JN0-335 Question Includes: Single Choice Questions: 40, Multiple Choice Questions: 58,
You are experiencing excessive packet loss on one of your two WAN links route traffic from the degraded link to the working link
Which AppSecure component would you use to accomplish this task?
Which two statements about SRX chassis clustering are correct? (Choose two.)
Regarding static attack object groups, which two statements are true? (Choose two.)
How does the SSL proxy detect if encryption is being used?
Exhibit
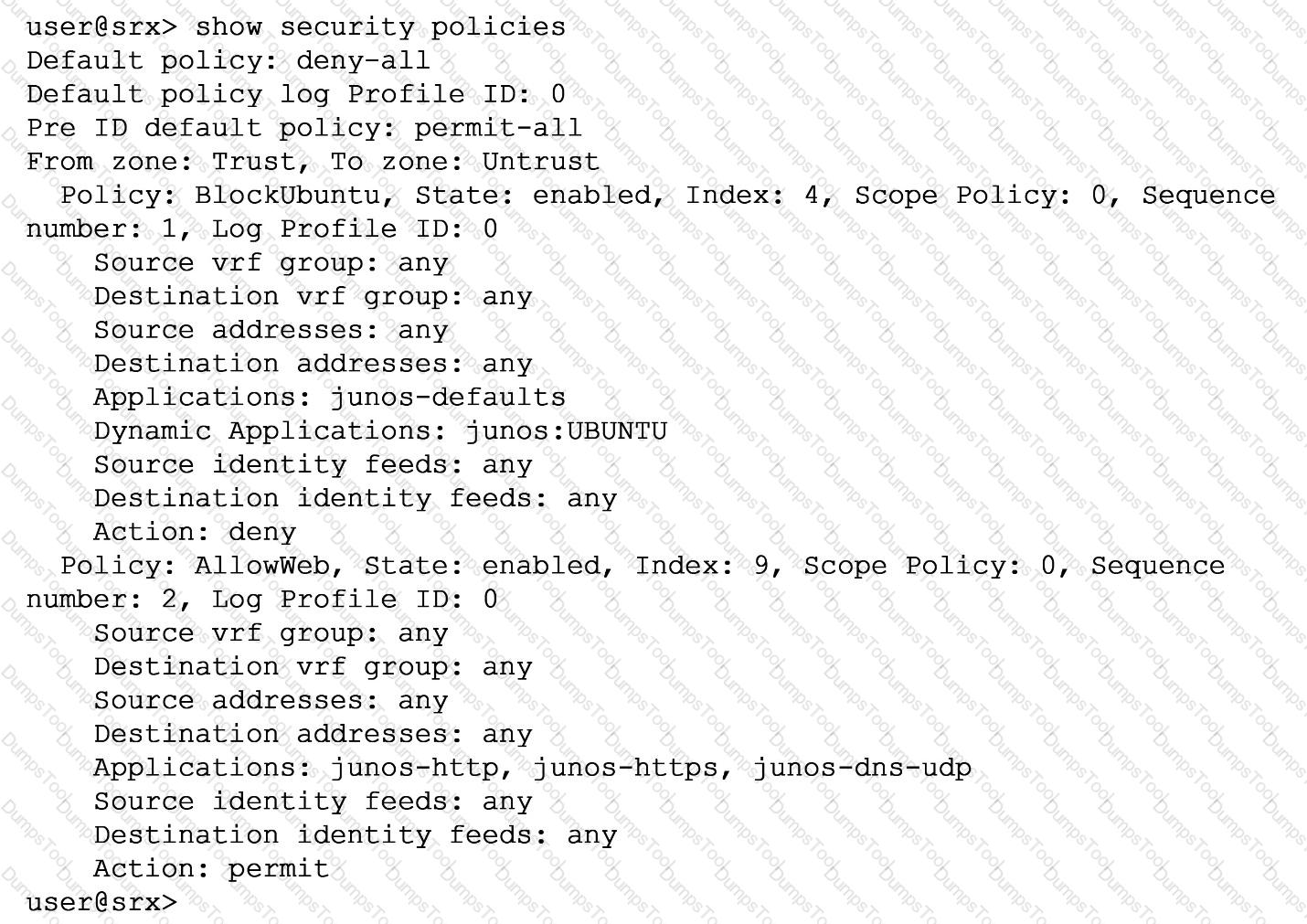
You are asked to ensure that servers running the Ubuntu OS will not be able to update automatically by blocking their access at the SRX firewall. You have configured a unified security policy named Blockuburrtu, but it is not blocking the updates to the OS.
Referring to the exhibit which statement will block the Ubuntu OS updates?
Customers Passed
Juniper JN0-335
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted Juniper Exam JN0-335 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
Juniper JNCIS-SEC JN0-335 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing Juniper JNCIS-SEC JN0-335 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool JN0-335 Security, Specialist (JNCIS-SEC) Practice Questions is enormous and unmatched!
The Juniper JN0-335 Exam, also known as the JNCIS-SEC (Juniper Networks Certified Specialist Security), is a certification exam designed to validate a candidate's knowledge of security technologies and Junos OS for SRX Series devices.
The exam is intended for networking professionals with intermediate knowledge of Junos OS and security technologies. Candidates must first pass the JNCIA-SEC certification as a prerequisite.
The JN0-335 exam covers the following key topics:
The passing score for the Juniper JN0-335 Exam (Security, Specialist - JNCIS-SEC) is 70%.
The cost of the Juniper JN0-335 Exam (Security, Specialist - JNCIS-SEC) is typically $300 USD. However, prices may vary depending on your region and any ongoing promotions or discounts offered by Juniper Networks.
JNCIS-SEC certification focuses on intermediate-level knowledge of Junos OS security features and technologies. While the JNCIP-DC certification is for advanced-level professionals specializing in data center technologies.
Preparation involves studying the JN0-335 exam syllabus, practicing with real questions, and using resources like JN0-335 study guide pdf, practice questions, and practice exams available on Dumpstool.com.
Yes, Dumpstool provides JN0-335 practice tests that closely resemble the actual exam, helping candidates familiarize themselves with the JN0-335 exam format.
At Dumpstool, we update our JN0-335 exam dumps and practice questions regularly to ensure that they reflect the most current exam trends and content. This helps you prepare with the most relevant and accurate material, improving your chances of success.