300-215 Question Includes: Single Choice Questions: 102, Multiple Choice Questions: 26, Drag Drop: 3,
A network host is infected with malware by an attacker who uses the host to make calls for files and shuttle traffic to bots. This attack went undetected and resulted in a significant loss. The organization wants to ensure this does not happen in the future and needs a security solution that will generate alerts when command and control communication from an infected device is detected. Which network security solution should be recommended?
Refer to the exhibit.
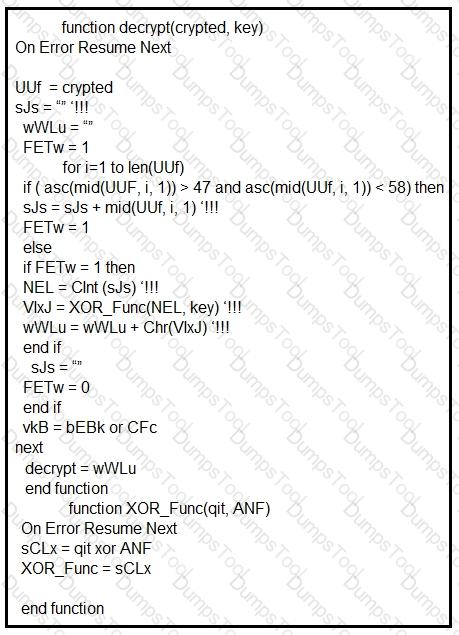
Which type of code created the snippet?
A cybersecurity analyst is analyzing a complex set of threat intelligence data from internal and external sources. Among the data, they discover a series of indicators, including patterns of unusual network traffic, a sudden increase in failed login attempts, and multiple instances of suspicious file access on the company's internal servers. Additionally, an external threat feed highlights that threat actors are actively targeting organizations in the same industry using ransomware. Which action should the analyst recommend?
What is a concern for gathering forensics evidence in public cloud environments?
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?
Customers Passed
Cisco 300-215
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted Cisco Exam 300-215 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
Cisco CyberOps Professional 300-215 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing Cisco CyberOps Professional 300-215 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool 300-215 Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) Practice Questions is enormous and unmatched!
DumpsTool products focus each and every aspect of the 300-215 certification exam. You’ll find them absolutely relevant to your needs.
DumpsTool’s products are absolutely exam-oriented. They contain 300-215 study material that is Q&As based and comprises only the information that can be asked in actual exam. The information is abridged and up to the task, devoid of all irrelevant and unnecessary detail. This outstanding content is easy to learn and memorize.
DumpsTool offers a variety of products to its clients to cater to their individual needs. DumpsTool Study Guides, 300-215 Exam Dumps, Practice Questions answers in pdf and Testing Engine are the products that have been created by the best industry professionals.
The money back guarantee is the best proof of our most relevant and rewarding products. DumpsTool’s claim is the 100% success of its clients. If they don’t succeed, they can take back their money.
DumpsTool 300-215 Testing Engine delivers you practice tests that have been made to introduce you to the real exam format. Taking these tests also helps you to revise the syllabus and maximize your success prospects.
Yes. DumpsTool’s concentration is to provide you with the state of the art products at affordable prices. Round the year, special packages and discounted prices are also introduced.