350-201 Question Includes: Single Choice Questions: 118, Multiple Choice Questions: 8, Drag Drop: 13,
Refer to the exhibit.
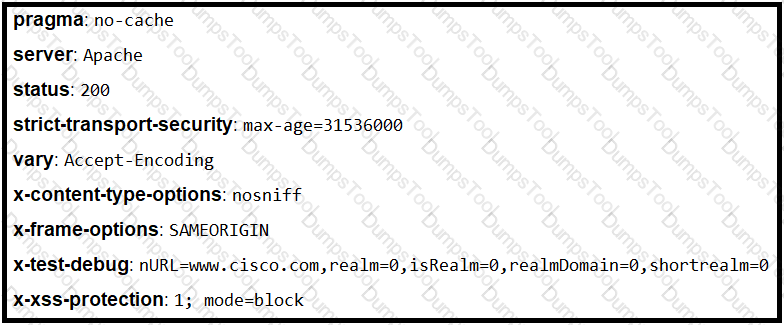
Where is the MIME type that should be followed indicated?
Refer to the exhibit.
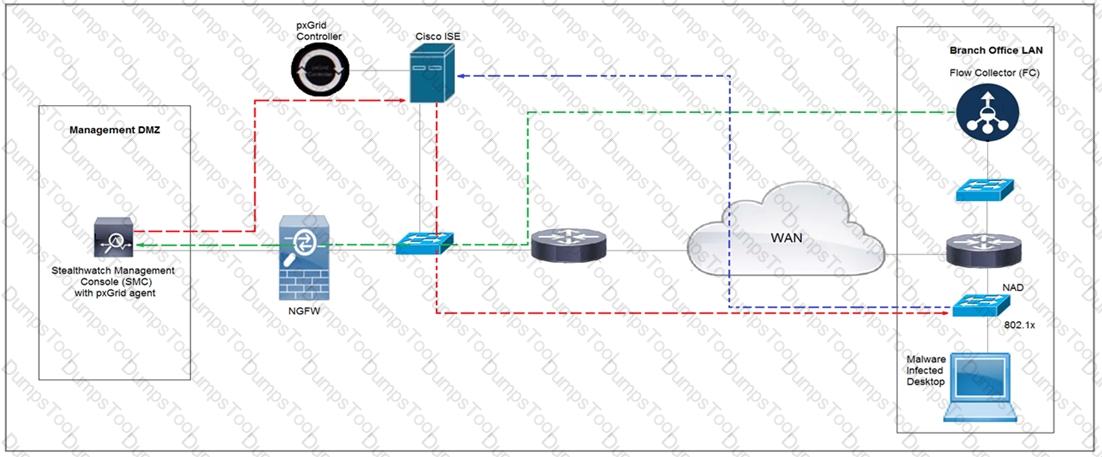
Rapid Threat Containment using Cisco Secure Network Analytics (Stealthwatch) and ISE detects the threat of malware-infected 802.1x authenticated endpoints and places that endpoint into a quarantine VLAN using Adaptive Network Control policy. Which method was used to signal ISE to quarantine the endpoints?
An audit is assessing a small business that is selling automotive parts and diagnostic services. Due to increased customer demands, the company recently started to accept credit card payments and acquired a POS terminal. Which compliance regulations must the audit apply to the company?
A company recently completed an internal audit and discovered that there is CSRF vulnerability in 20 of its hosted applications. Based on the audit, which recommendation should an engineer make for patching?
Refer to the exhibit.
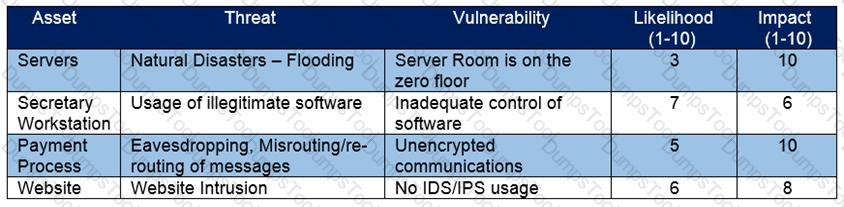
Which asset has the highest risk value?
Customers Passed
Cisco 350-201
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted Cisco Exam 350-201 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
Cisco CyberOps Professional 350-201 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing Cisco CyberOps Professional 350-201 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool 350-201 Performing CyberOps Using Core Security Technologies (CBRCOR) Practice Questions is enormous and unmatched!
The Cisco 350-201 exam, also known as “Performing CyberOps Using Core Security Technologies (CBRCOR),” tests your knowledge and skills related to core cybersecurity operations.
The Cisco 350-201 exam is ideal for security professionals, network administrators, and IT specialists seeking to enhance their cybersecurity expertise and gain a deeper understanding of Cisco's security solutions. It's particularly relevant for those aspiring to enter the Security Operations Center (SOC) field.
The Cisco 350-201 exam covers core cybersecurity operations, including fundamentals, techniques, processes and automation.
Successful completion of Cisco 350-201 exam leads to the Cisco Certified CyberOps Professional certification.
The Cisco 350-201 exam consists of 139 questions.
The Cisco 350-201 exam duration is 120 minutes.
Cisco 300-215 (CBRFIR) and Cisco 350-201 (CBRCOR) are both part of the Cisco CyberOps Professional certification track, but they focus on different areas of cybersecurity operations.
Dumpstool offers a range of 350-201 study materials to boost your exam preparation, including:
Yes, Dumpstool provides a money-back guarantee on our Cisco 350-201 exam preparation materials. If you do not pass the exam after using our 350-201 questions answers material, you can request a refund based on our terms and conditions. This guarantee ensures that you can prepare with confidence.