Refer to the exhibit.
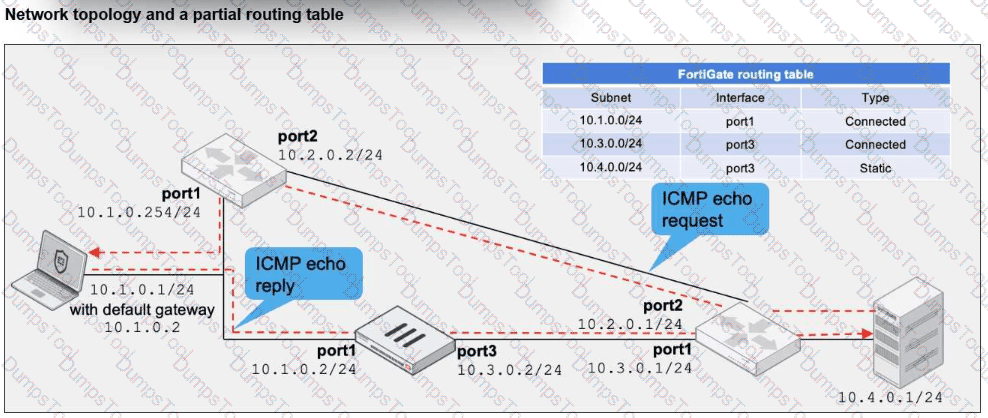
A network topology and a partial routing table are shown.
FortiGate has already been configured with a firewall policy that allows all ICMP traffic to flow from port1 to port3.
Which two changes can the administrator perform to ensure the server at 10.4.0.1/24 receives the ICMP echo reply from the laptop at 10.1.0.1/24? (Choose two.)
In a Security Fabric environment which three actions must you take to ensure successful communication among the nodes? (Choose three.)
Which three common FortiGate-to-collector-agent connectivity issues can you identify using the FSSO real-time debug? (Choose three.)
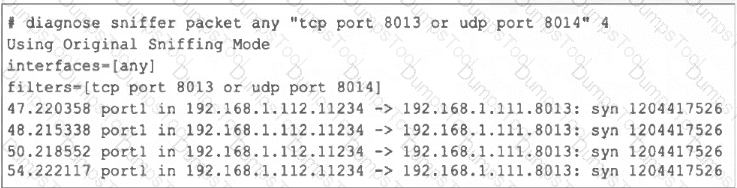
A FortiGate administrator is troubleshooting a VPN that is failing to establish.
As a first step, the administrator is attempting to sniff the traffic using the command:
# diagnose sniffer packet any ‘’udp port 500 or udp port 4500 or esp’’ 4
After several minutes there is still no output. What is the most Likely reason for this?
Refer to the exhibit.
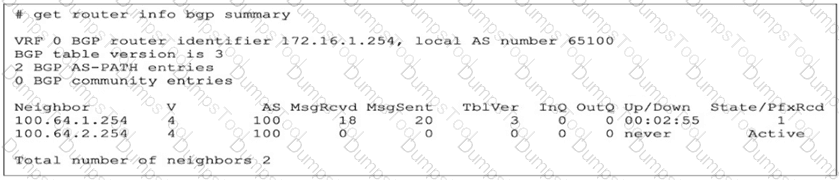
The output of the get router info bgp summary command is shown.
Which statement regarding adjacencies between the local router and its neighbors is correct?
Refer to the exhibit.
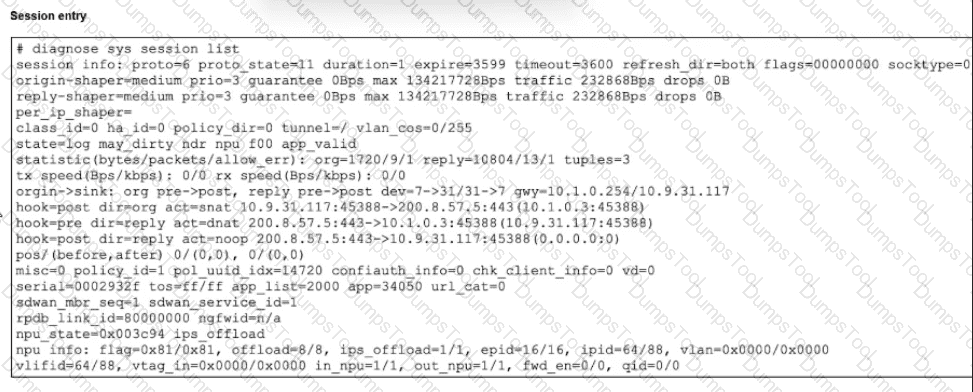
The exhibit shows a session entry. Which statement about this TCP session is true?
Refer to the exhibit, which shows a partial output of a real-time LDAP debug.
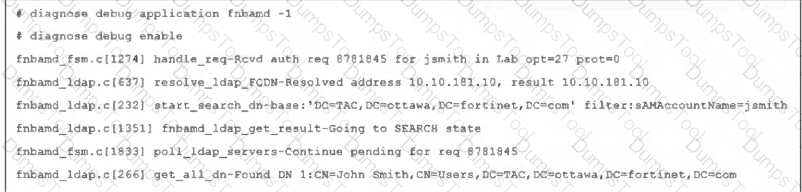
What two conclusions can you draw from the output? (Choose two.)
Which two statements are true regarding heartbeat messages sent from an FSSO collector agent to FortiGate? (Choose two.)
Refer to the exhibit, which shows one way communication of the downstream FortiGate with the upstream FortiGate within a Security Fabric.
What three actions must you take to ensure successful communication? (Choose three.)
Refer to the exhibit, which shows partial outputs from two routing debug commands.
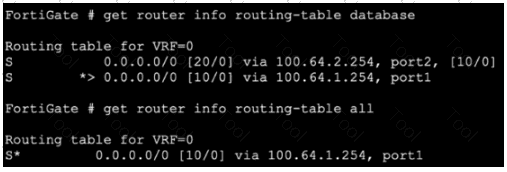
Why is the port2 default route not in the second command output?
Refer to the exhibit.
Which two observations can you make about the web filter traffic captured using the flow tool? (Choose two.)
Refer to the exhibit, which shows the partial output of FortiOS kernel slabs.
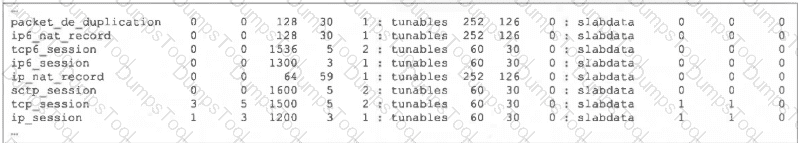
Which statement is true?
Refer to the exhibits.
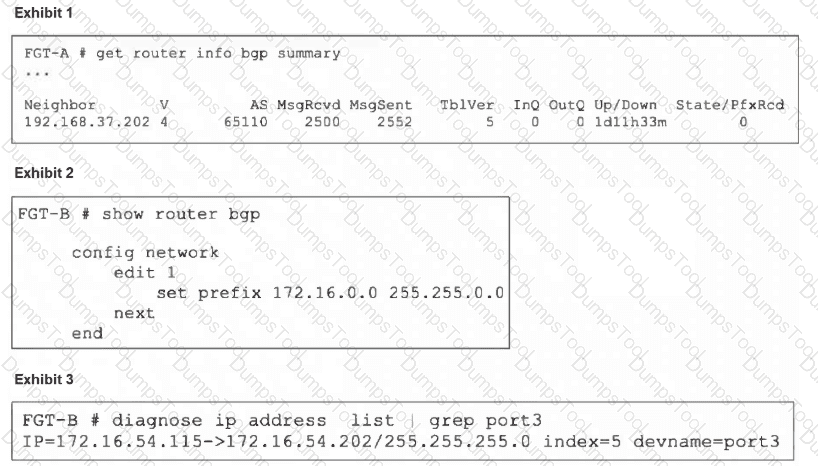
An administrator is attempting to advertise the network configured on port3. However, FGT-A is not receiving the prefix.
Which two actions can the administrator take to fix this problem? (Choose two.)
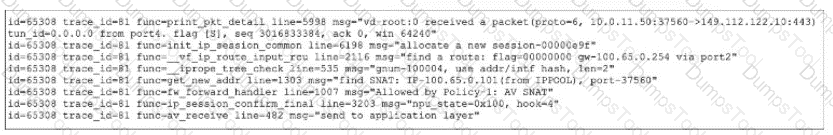
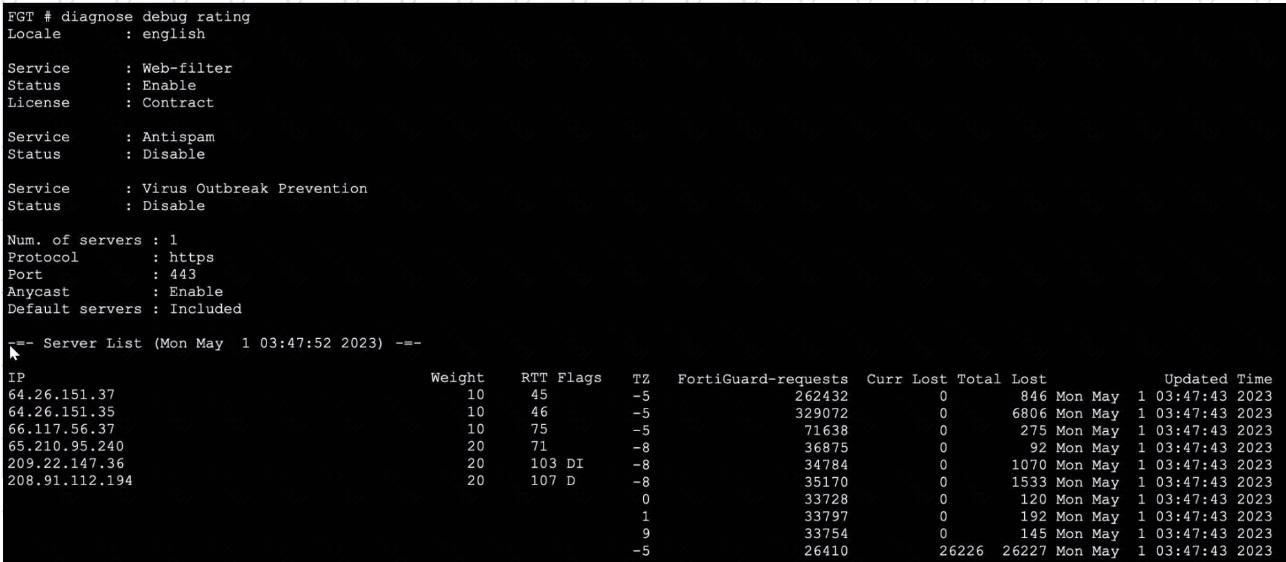
Refer to the exhibit, which shows the output of a debug command.
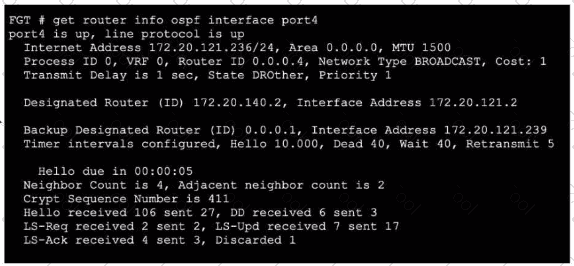
Which two statements about the output are true? (Choose two.)
Refer to the exhibit.
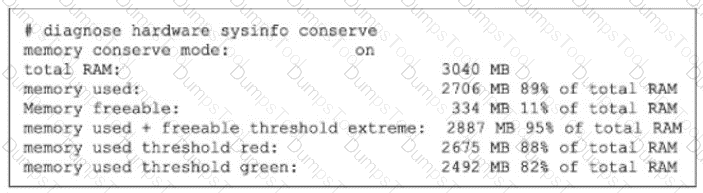
If the default settings are m place, what can you conclude about the conserve mode shown in the exhibit?
Refer to the exhibit.
The exhibit shows the output from using the command diagnose debug application samld -1 to diagnose a SAML connection.

Based on this output, what can you conclude?
Refer to the exhibit, which shows the output o! the BGP database.
Which two statements are correct? (Choose two.)
Refer to the exhibit, which shows the output of get router info bgp summary.
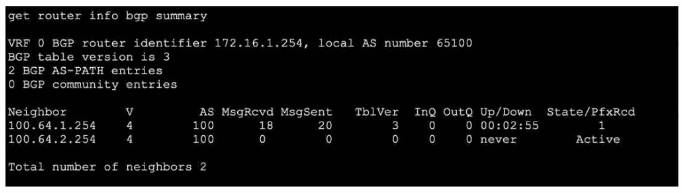
Which two statements are true? (Choose two.)
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate.
Which action will FortiGate take when using the default settings for SSL certificate inspection?
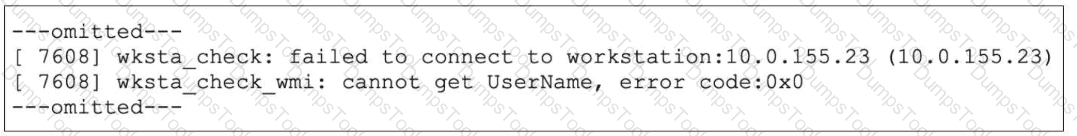
Refer to the exhibit showing a debug output.
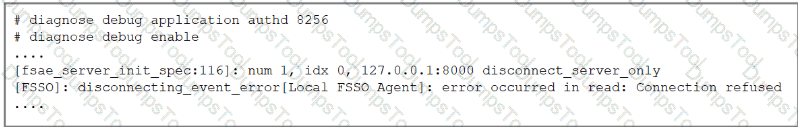
An administrator deployed FSSO in DC Agent Mode but FSSO is failing on FortiGate. Pinging FortiGate from where the collector agent is deployed is successful.
The administrator then produces the debug output shown in the exhibit.
What could be causing this error message?
While troubleshooting a FortiGate web filter issue, users report that they cannot access any websites, even though those sites are not explicitly blocked by any web filter profiles that are applied to firewall policies.
What are the three most likely reasons for this behavior? (Choose three answers)
A VPN tunnel is up. To monitor traffic flow, the administrator enters the following CLI commands on an SSH session on FortiGate:
# diagnose debug enable
# diagnose sniffer packet any ' udp and port 500 ' 4
However, the sniffer does not show any output. Assuming default configuration values, what are two possible reasons there is no output? (Choose two answers)
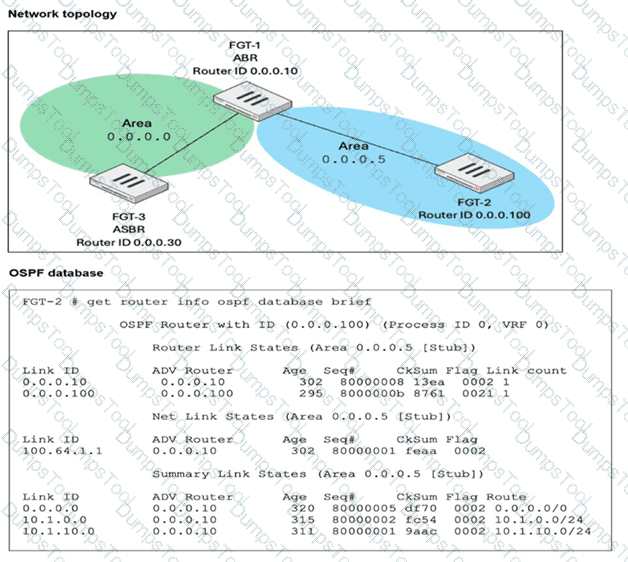
What are two reasons that an OSPF router does not have any type 5 tank-state advertisements (LSAs) In its link-stale database (LSD6)? (Choose two.)
Exhibit.
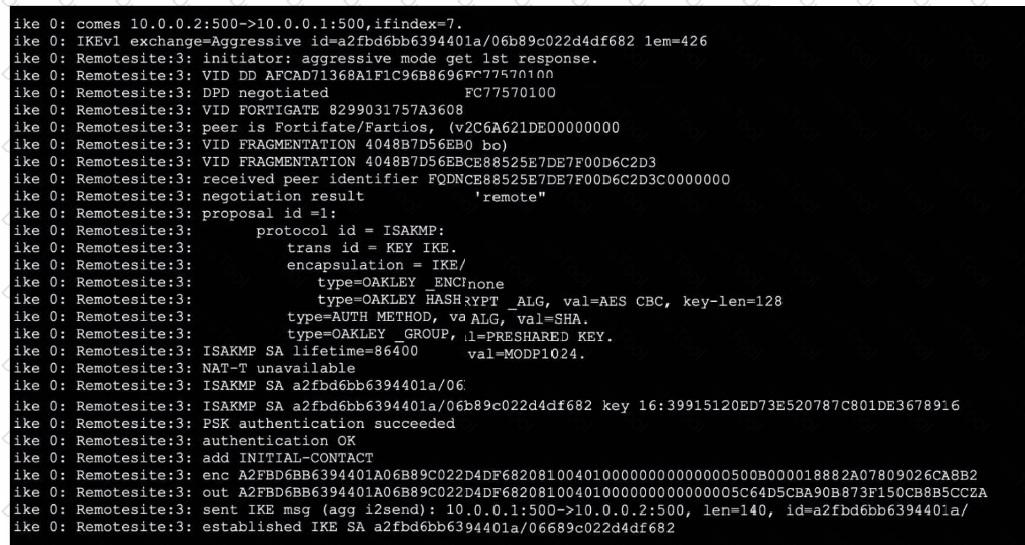
Refer to the exhibit, which contains partial output from an IKE real-time debug.
Which two statements about this debug output are correct? (Choose two.)
Refer to the exhibit.
The output from a collector agent log is shown. The collector agent is showing the status of a workstation as Not Verified . What are two common causes for this message? (Choose two.)
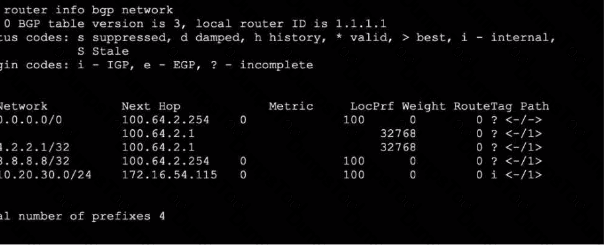
Refer to the exhibits.
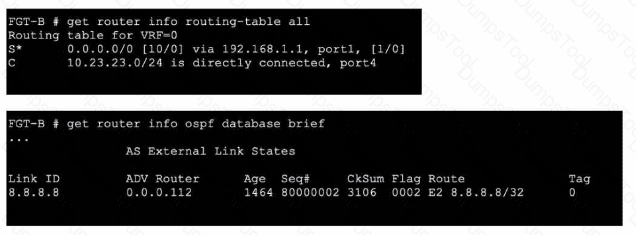
An administrator Is expecting to receive advertised route 8.8.8.8/32 from FGT-A. On FGT-B, they confirm that the route is being advertised and received, however, the route is not being injected into the routing table. What is the most likely cause of this issue?
During which phase of IKEv2 does the Diffie-Helman key exchange take place?
Refer to the exhibit, which shows the output of a real-time debug. Which statement about this output is true? (Choose one answer)
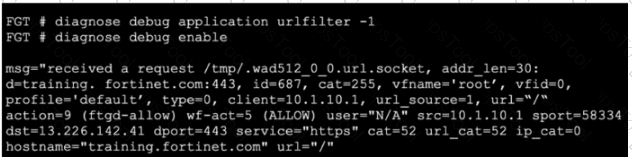
Exhibit.
Refer to the exhibit, which shows the output of a diagnose command.
What can you conclude about the debug output in this scenario?
Which three conditions are required for two FortiGate devices to form an OSPF adjacency? (Choose three answers)
Exhibit 1.
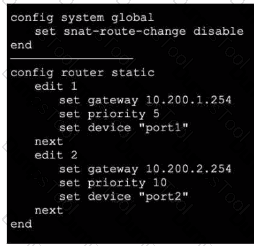
Exhibit 2.
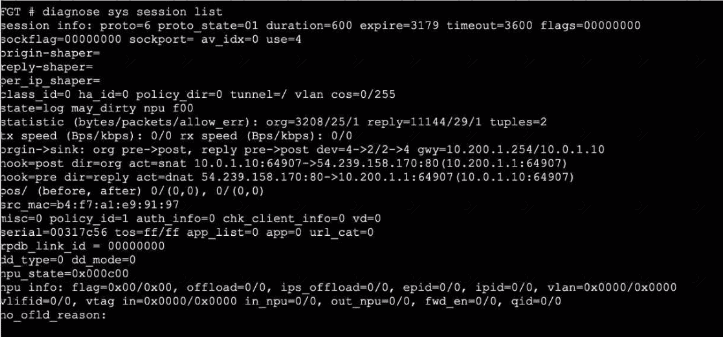
Refer to the exhibits, which show the configuration on FortiGate and partial internet session information from a user on the internal network.
An administrator would like to lest session failover between the two service provider connections.
Which two changes must the administrator make to force this existing session to immediately start using the other interface? (Choose two.)
Refer to the exhibit.
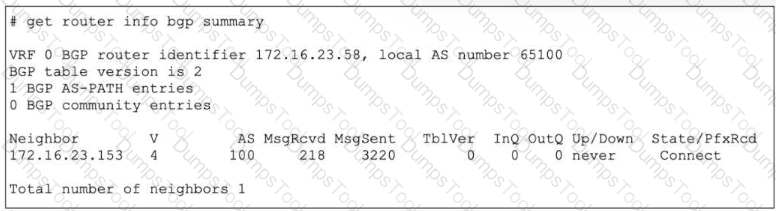
The output of a BGP debug command is shown.
Why has the local router at 172.16.23.58 been unable to establish adjacency with its only neighbor?
When FortiGate enters conserve mode because of memory pressure, which action can FortiGate perform to preserve memory?