A customer with a fully licensed Palo Alto Networks firewall is concerned about threats based on domain generation algorithms (DGAS).
Which Security profile is used to configure Domain Name Security (DNS) to Identity and block
previously unknown DGA-based threats in real time?
What are three key benefits of the Palo Alto Networks platform approach to security? (Choose three)
A customer is seeing an increase in the number of malicious files coming in from undetectable sources in their network. These files include doc and .pdf file types.
The customer uses a firewall with User-ID enabled
Which feature must also be enabled to prevent these attacks?
Select the BOM for the Prisma Access, to provide access for 5500 mobile users and 10 remote locations (100Mbps each) for one year, including Base Support and minimal logging. The customer already has 4x PA5220r 8x PA3220,1x Panorama VM for 25 devices.
A customer requires protections and verdicts for portable executable (PE) and executable and linkable format (ELF), as well as the ability to integrate with existing security tools.
Which Cloud-Delivered Security Service (CDSS) does Palo Alto Networks provide that will address this requirement?
A price-sensitive customer wants to prevent attacks on a Windows Virtual Server. The server will max out at 100Mbps but needs to have 45.000 sessions to connect to multiple hosts within a data center
Which VM instance should be used to secure the network by this customer?
When the Cortex Data Lake is sized for Traps Management Service, which two factors should be considered? (Choose two.)
The ability to prevent users from resolving internet protocol (IP) addresses to malicious, grayware, or newly registered domains is provided by which Security service?
A customer worried about unknown attacks is hesitant to enable SSL decryption due to privacy
and regulatory issues. How does the platform address the customer’s concern?
Which are the three mandatory components needed to run Cortex XDR? (Choose three.)
Which four steps of the cyberattack lifecycle does the Palo Alto Networks Security Operating Platform prevent? (Choose four.)
Which domain permissions are required by the User-ID Agent for WMI Authentication on a Windows Server? (Choose three.)
Which two new file types are supported on the WF-500 in PAN-OS 9? (Choose two)
Which three features are used to prevent abuse of stolen credentials? (Choose three.)
Which Security profile on the Next-Generation Firewall (NGFW) includes Signatures to protect against brute force attacks?
What two types of certificates are used to configure SSL Forward Proxy? (Сhoose two.)
A customer requires an analytics tool with the following attributes:
- Uses the logs on the firewall to detect actionable events on the network
- Automatically processes a series of related threat events that, when combines, indicate a likely comprised host on the network
- Pinpoints the area of risk and allows for assessment of the risk to action can be taken to prevent exploitation of network resources
Which feature of PAN-OS will address these requirements?
Which of the following statements is valid with regard to Domain Name System (DNS) sinkholing?
A customer is concerned about malicious activity occurring directly on their endpoints and will not be visible to their firewalls.
Which three actions does the Traps agent execute during a security event, beyond ensuring the prevention of this activity? (Choose three.)
What are two ways to manually add and remove members of dynamic user groups (DUGs)? (Choose two)
Which statement applies to Palo Alto Networks Single Pass Parallel Processing (SP3)?
Which two configuration elements can be used to prevent abuse of stolen credentials? (Choose two.)
The need for a file proxy solution, virus and spyware scanner, a vulnerability scanner, and HTTP decoder for URL filtering is handled by which component in the NGFW?
What are three sources of malware sample data for the Threat Intelligence Cloud? (Choose three)
What are two presales selling advantages of using Expedition? (Choose two.)
Which two configuration items are required when the NGFW needs to act as a decryption broker for multiple transparent bridge security chains? (Choose two.)
Which selection must be configured on PAN-OS External Dynamic Lists to support MineMeld indicators?
A customer has business-critical applications that rely on the general web-browsing application. Which security profile can help prevent drive-by-downloads while still allowing web-browsing traffic?
Which two steps are required to configure the Decryption Broker? (Choose two.)
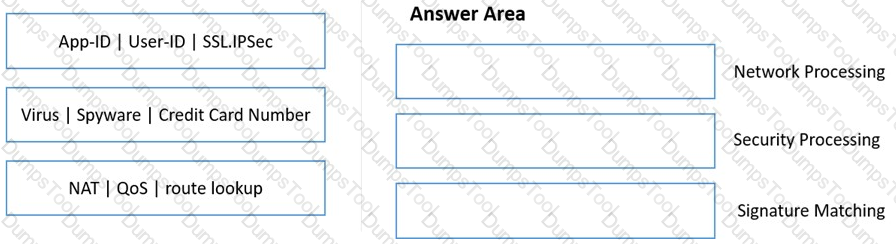
Match the functions to the appropriate processing engine within the dataplane.
Which is the smallest Panorama solution that can be used to manage up to 2500 Palo Alto Networks Next Generation firewalls?
Which two features are key in preventing unknown targeted attacks? (Choose two)
A Fortune 500 customer has expressed interest in purchasing WildFire; however, they do not want to send discovered malware outside of their network.
Which version of WildFire will meet this customer’s requirements?