A security policy requires that a user account be created for auditing purposes. This user should only view configuration and operational data without making any changes. Which predefined login class would satisfy this requirement?
operator
unauthorized
read-only
super-user
Junos OS provides several predefined login classes to implement Role-Based Access Control (RBAC) efficiently. For an auditor who needs to verify the current state of the device without the risk of altering it, the read-only class is the ideal choice.
The read-only class allows a user to log in and execute show commands to view the running configuration and operational statistics. However, it strictly prohibits the user from entering configuration mode (using the configure command) or executing any " impactful " operational commands that could reset counters, clear log files, or affect traffic flow.
It is important to distinguish this from the operator class. While the operator class also cannot change the configuration, it does have permissions to clear interface statistics, reset routing protocol neighbors, and perform other " clear " or " reset " actions. For a pure auditing role where even resetting a counter would be considered a breach of policy, read-only provides the necessary " look but don ' t touch " environment. The super-user class, conversely, has full unrestricted access, and unauthorized is not a standard functional class. Using the read-only class ensures compliance with security best practices by granting the minimum necessary privileges required for the auditing task.
You manage a Junos device with 20 interfaces. Each interface requires the same description and MTU setting. Which configuration approach would reduce repetitive commands and ensure consistency?
Use the wildcard delete command to remove duplicate settings.
Configure each interface individually.
Use a configuration group.
Use search and replace to apply settings across interfaces.
In the Junos OS architecture, configuration groups (defined under the [edit groups] hierarchy) provide a powerful mechanism for template-based management. This approach is specifically designed to handle scenarios where multiple configuration objects, such as twenty different Ethernet interfaces, require identical parameters like a specific description or MTU value. By defining these common settings once within a group, an administrator can then apply that group to multiple interfaces using the apply-groups statement.
This methodology drastically reduces the number of repetitive commands required and, more importantly, ensures strict consistency across the device. If the MTU needs to be adjusted in the future, the change is made in a single location—within the configuration group—and is automatically inherited by all interfaces to which the group is applied. This inheritance model prevents " configuration drift " where individual interfaces might otherwise end up with mismatched settings due to manual entry errors. Using configuration groups is considered a best practice for Senior Architects managing high-density platforms, as it simplifies the candidate configuration file and makes the management of bulk interface settings both scalable and error-resistant.
According to HPE Juniper Networking, what are two recommended tasks you should perform before upgrading Junos OS on a device? (Choose two.)
Delete all rollback configurations.
Verify available storage space using the show system storage command.
Disable all interfaces to prevent traffic during the upgrade.
Back up the active current configuration.
Upgrading the Junos OS is a high-impact operation that requires thorough preparation to minimize risk and potential downtime. According to Juniper ' s best practices, one of the most critical preliminary steps is to verify that the device has sufficient available storage space. Using the show system storage command, an administrator can inspect the /var partition, which is the primary directory where software packages are temporarily stored and expanded during the installation process. If the storage is nearly full, the upgrade may fail midway, potentially leaving the device in an inconsistent state or requiring manual intervention via the boot loader.
The second mandatory task is to back up the active configuration . While Junos automatically maintains rollback files locally, these could be lost if the storage media fails or if a " clean install " (format install) becomes necessary. Having an external backup on a remote server or a local workstation ensures that the device ' s identity, policies, and interface settings can be restored quickly regardless of the upgrade outcome. Other tasks, such as creating a rescue configuration or performing a file system cleanup, are also highly recommended to ensure the " last known good " state is preserved. Disabling interfaces is generally unnecessary as Junos manages the transition gracefully, and deleting rollbacks would counterproductively remove historical recovery points. Ensuring these two pillars—storage availability and off-box backups—provides the safest foundation for a successful software lifecycle management event.
You must view the forwarding table on your Junos device to troubleshoot a packet forwarding issue. In this scenario, which command would display the forwarding table?
show route table
show route forwarding-table
show ip forwarding
show forwarding-options
To effectively troubleshoot packet forwarding in a Junos environment, an architect must distinguish between the control plane ' s Routing Information Base (RIB) and the data plane ' s Forwarding Information Base (FIB). While the command show route displays the RIB (the master routing table maintained by the Routing Engine), it does not necessarily reflect the actual instructions being executed by the hardware. The definitive command for viewing the data plane ' s active path selection is show route forwarding-table.
Executing this command reveals the contents of the FIB as it has been pushed from the Routing Engine to the Packet Forwarding Engine (PFE). The output provides critical diagnostic data, including the destination prefix, the specific next-hop IP address, the interface through which the packet will egress, and the type of route (such as unicast or broadcast). This is the " ground truth " for packet movement; if a route exists in the RIB but is missing from the forwarding table, it indicates a failure in the communication between the RE and PFE. Utilizing this command is the primary method for identifying black holes, incorrect next-hop resolution, or issues with hardware-level filter applications that might be impacting transit traffic flow at wire speed.
What are two characteristics of transit traffic in Junos OS? (Choose two.)
It includes routing protocol packets.
It is traffic destined for the Routing Engine.
It does not require control plane processing.
It is forwarded by the Packet Forwarding Engine.
Transit traffic represents the primary " workload " of a Junos device; it is the data that enters one network interface and exits another, destined for a remote host. Unlike exception traffic, transit traffic is forwarded exclusively by the Packet Forwarding Engine (PFE) . The PFE uses specialized Application-Specific Integrated Circuits (ASICs) or programmable NPUs to perform lookups in the hardware-based forwarding table (FIB) at wire speed.
A defining characteristic of transit traffic is that it does not require control plane processing . Once the Routing Engine (RE) has populated the PFE with the necessary forwarding instructions, the RE steps out of the way. The packets pass through the PFE ' s ingress processing, lookups, and egress queuing without ever consuming CPU cycles on the Routing Engine. This bypass is what allows Junos devices to maintain massive throughput and low latency, even if the RE is busy recalculating a complex BGP table. Routing protocol packets (like OSPF updates) and traffic destined for the router ' s own management IP address are explicitly not transit traffic; they are control plane traffic because they terminate at the device ' s " brain. " Transit traffic is strictly " pass-through " data.
Which two characteristics apply to TCP? (Choose two.)
TCP guarantees fixed latency for application flows.
TCP broadcasts datagrams by default on Ethernet.
TCP uses a three-way handshake to establish a connection.
TCP provides reliable, ordered delivery using sequence numbers.
Comprehensive and Detailed 150 to 250 words of Explanation From: The Transmission Control Protocol (TCP) is a core transport-layer protocol within the TCP/IP suite designed to provide a highly reliable, connection-oriented service. Unlike the User Datagram Protocol (UDP), which is connectionless and best-effort, TCP ensures that data is delivered accurately and in the correct order. A defining characteristic of TCP is its use of a three-way handshake to establish a session. This process involves the exchange of SYN, SYN-ACK, and ACK segments, which synchronizes sequence numbers between the two endpoints and ensures both hosts are ready for data transfer.
Furthermore, TCP provides reliable, ordered delivery by utilizing sequence numbers and acknowledgments. Each data segment is assigned a sequence number; the receiving host uses these numbers to reassemble the data in its original order, even if segments arrive out of sequence due to network jitter or multiple paths. If a segment is lost, the lack of a timely acknowledgment triggers a retransmission, guaranteeing that the application receives all data. TCP does not provide fixed latency guarantees, as its error-recovery mechanisms can introduce delays. Additionally, TCP is a unicast-only protocol and does not support broadcasting on Ethernet. Reference: Networking Fundamentals, Transport Layer Protocols, TCP vs. UDP.
==========
Which two statements are correct about a Routing Engine? (Choose two.)
It processes management traffic.
It processes CoS marked traffic.
It forwards transit traffic.
It maintains routing tables.
The architecture of a Junos device is bifurcated into two primary functional planes: the Control Plane, managed by the Routing Engine (RE), and the Data Plane, managed by the Packet Forwarding Engine (PFE). The Routing Engine serves as the " brain " of the device. One of its primary responsibilities is the processing of management traffic, which includes handling CLI sessions (SSH, Telnet), SNMP requests, and system logging. Because the RE runs the Junos OS kernel, it provides the environment for all administrative tasks and system management utilities.
Additionally, the Routing Engine is responsible for the intelligence of the network, which involves running routing protocols (such as OSPF, BGP, or IS-IS) and maintaining the master routing tables. It populates the Routing Information Base (RIB) with all learned paths and then calculates the best paths to build the Forwarding Information Base (FIB). This FIB is then pushed to the PFE for hardware-level packet switching. It is a common misconception that the RE handles transit traffic; however, the RE only handles " exception traffic " or traffic destined for the device itself. This separation ensures that the control plane remains stable and responsive even during periods of heavy transit load on the forwarding plane. Reference: Junos OS Fundamentals, Architectural Overview, Control Plane vs. Forwarding Plane.
What is the main function of the forwarding table on a Junos device?
It contains only active routes used to forward packets through the PFE.
It advertises routes to neighboring routers.
It stores all learned routes from routing protocols.
It determines the best route based on route preference.
The architecture of Junos OS is designed with a strict functional separation between the control plane and the data plane. The Routing Engine (RE) maintains the master Routing Information Base (RIB), which acts as a comprehensive database storing all potential paths learned from various routing protocols, static configurations, and direct connections. However, to achieve wire-speed performance, the device does not consult the RIB for every packet. Instead, the RE identifies the " active " or best routes for each destination based on route preference and metrics.
Once these active routes are selected, the RE distills them into a streamlined Forwarding Information Base (FIB), commonly referred to as the forwarding table, and pushes this table to the Packet Forwarding Engine (PFE). The main function of the forwarding table is to provide a high-speed, local lookup mechanism that allows the PFE to forward transit traffic across the switch fabric with minimal latency. This table contains only the specific exit interface and Layer 2 next-hop information required for packet delivery. By isolating the PFE from the overhead of complex routing protocol state machines and all inactive redundant paths, Junos OS ensures that forwarding performance remains consistent even during control plane re-convergence. Reference: Junos OS Fundamentals, Control Plane and Forwarding Plane functions.
==========
Which protocol is used to discover the Layer 2 (MAC) address of a next hop for IPv6 hosts?
DHCP
ARP
NDP
DNS
In the IPv6 protocol suite, the traditional Address Resolution Protocol (ARP) used in IPv4 has been deprecated and replaced by the Neighbor Discovery Protocol (NDP). NDP is a multifaceted protocol built upon the Internet Control Message Protocol version 6 (ICMPv6). Its primary purpose is to allow a host or router to determine the Layer 2 hardware (MAC) address of a neighbor on the same local link when only the neighbor ' s IPv6 address is known.
This specific process is known as Neighbor Solicitation and Neighbor Advertisement. When a Junos device needs to resolve a MAC address for an IPv6 next hop, it sends a Neighbor Solicitation (ICMPv6 Type 135) message to the solicited-node multicast address. The target host responds with a Neighbor Advertisement (ICMPv6 Type 136) containing its physical MAC address. Beyond address resolution, NDP also handles Router Discovery, Prefix Discovery, and Duplicate Address Detection (DAD). Unlike ARP, which relies on broadcasts that can impact all hosts on a segment, NDP utilizes efficient multicast communication. Understanding NDP is critical for Junos architects, as it is the foundational mechanism that facilitates logical-to-physical address mapping in modern IPv6 environments, ensuring that the Packet Forwarding Engine can properly encapsulate frames for local delivery.
Which statement describes the primary purpose of a routing policy in Junos OS?
It controls which routes are accepted or advertised by a routing protocol. B. It determines the physical interface used for forwarding traffic. C. It sets the maximum number of routes in the routing table. D. It enables automatic rollback of routing changes.
In Junos OS, a routing policy is a powerful tool used to manage the flow of routing information between the Routing Information Base (RIB) and routing protocols. Unlike forwarding decisions, which are handled by the Packet Forwarding Engine, routing policies function within the control plane on the Routing Engine. Their primary purpose is to define specific criteria for importing routes into the routing table from neighbors or exporting routes from the routing table to neighbors.
Routing policies consist of terms containing from (match) and then (action) statements. They allow administrators to filter prefixes (e.g., denying specific BGP routes), modify route attributes (e.g., changing OSPF metrics or BGP communities), and manipulate path selection behavior. For example, an export policy might be used to ensure that only specific internal subnets are advertised to an ISP via BGP, preventing the accidental leakage of private infrastructure addresses. By default, Junos applies " default policies " for each protocol (such as OSPF accepting all OSPF routes), but custom policies allow for granular control over how the device interacts with the rest of the network. This ensures that the routing table contains only the desired paths for optimal traffic engineering.
Which routing table is used for IPv6 unicast routes by default?
inet.0
inet.6
inet.1
inet6.0
In Junos OS, routing information is meticulously organized into separate databases known as routing tables, each identified by a specific name corresponding to an address family and its intended operational purpose. The master routing table for IPv4 unicast information is inet.0 . For the IPv6 address family, Junos OS utilizes inet6.0 as the default master routing table for all unicast reachability information. This table stores all IPv6 prefixes learned from directly connected interfaces, static configurations, and dynamic routing protocols such as OSPFv3, IS-IS, or BGP.
It is a core architectural principle in Junos to isolate these families to ensure management clarity and prevent address space collisions. While the system utilizes other specialized tables for specific functions—such as inet.3 for MPLS path information or inet.1 for multicast forwarding caches— inet6.0 remains the primary repository for IPv6-based forwarding decisions. When a Junos device receives an IPv6 packet, the Packet Forwarding Engine (PFE) performs a lookup against the entries derived from this table to determine the appropriate egress interface and next-hop address. Understanding this default table structure is essential for network architects when troubleshooting dual-stack environments or configuring protocol-specific import and export policies.
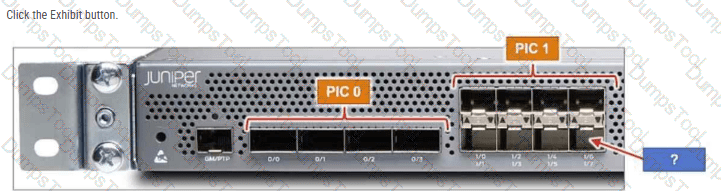
The MX204 has 12 built-in ports. Referring to the exhibit, to which interface does the arrow point?
хе-0/2/7
хе-0/0/7
хе-0/1/7
хе-0/1/6
The Juniper MX204 is a fixed-configuration router that utilizes a specific hierarchical naming convention for its physical interfaces: type-fpc/pic/port. In the MX204 architecture, there is a single built-in Flexible PIC Concentrator (FPC), which is always designated as FPC 0 . This FPC is subdivided into two logical Physical Interface Cards (PICs): PIC 0 and PIC 1 .
As shown in the exhibit, PIC 0 contains four high-speed ports (labeled 0/0 through 0/3) that typically support 40GbE or 100GbE speeds. PIC 1 contains eight ports (labeled 1/0 through 1/7) designed for 1GbE or 10GbE connectivity. These ports are arranged in a stacked, $2 \times 4$ grid. The labeling system on the chassis indicates the port numbers for each column. In the fourth column of the PIC 1 block, the top port is identified as 1/6 and the bottom port as 1/7 .
The blue arrow in the exhibit points directly to the bottom-right interface in the PIC 1 section. Correlating this physical location with the chassis labels confirms that the port number is 7. When combined with the FPC and PIC identifiers, the full interface name is xe-0/1/7 (assuming a 10GbE transceiver is installed). Understanding this physical-to-logical mapping is essential for accurate cabling and configuration within the Junos OS, ensuring that administrators apply the correct logical unit and protocol settings to the intended physical hardware.
Which two statements about route preference in Junos are correct? (Choose two.)
Both direct and static routes have the same preference.
Both direct and local routes have the same preference.
Both OSPF internal and OSPF AS external routes have the same preference.
Both EBGP and IBGP routes have the same preference.
Route preference is the quantitative value Junos OS uses to rank the trustworthiness of different routing sources when multiple protocols provide a path to the same destination. A critical architectural distinction in Junos is that both direct and local routes share the same default preference value of 0. Direct routes represent subnets physically connected to an interface, while local routes represent the specific IP address assigned to the device interface itself. Because a value of 0 is the lowest possible numerical value, these routes are always preferred over any learned via dynamic protocols or static configuration.
Additionally, Junos OS treats External BGP (EBGP) and Internal BGP (IBGP) differently than other vendors by assigning both an identical default preference of 170. This means that if the same prefix is learned via both EBGP and IBGP, the preference value alone will not determine the active route; the system must instead proceed to the standard BGP path selection algorithm (evaluating attributes like Local Preference, AS Path, and Origin) to break the tie. In contrast, OSPF distinguishes between its route types, assigning a preference of 10 to internal routes and 150 to AS external routes. Understanding these default values—specifically the parity between direct/local and the unified preference for BGP variants—is foundational for predicting how the Routing Engine populates the forwarding table. Reference: Routing Fundamentals, Default Route Preference Values.
==========
What does the user@router > clear log ospf-trace command accomplish?
The ospf-trace file is deleted.
Trace parameters are removed from the OSPF protocol configuration.
Logging data into ospf-trace is stopped.
Data in the ospf-trace file is removed and logging continues.
The clear log command is a vital operational utility within the Junos OS used to manage the size and relevance of log files without interrupting the system ' s logging processes. When a Senior Architect executes the clear log ospf-trace command, the Junos kernel truncates the specified file, effectively removing all existing text and resetting the file size to zero bytes. Crucially, the file itself is not deleted from the /var/log directory, nor is the underlying traceoptions configuration modified in any way.
Because tracing is often used for real-time debugging of protocol behaviors like OSPF, trace files can rapidly grow to several megabytes, making it difficult to find specific events. By clearing the log, the administrator ensures that any subsequent OSPF events—such as adjacency changes, LSA flooding, or SPF calculations—are recorded at the very beginning of the file, free from historical clutter. The OSPF process (rpd) continues to write to the file immediately after the truncation occurs. This operational behavior distinguishes the clear command from the file delete command, which would remove the file entirely, or the set protocols ospf traceoptions configuration command, which defines which specific events the device should record. Utilizing clear log is a standard best practice during intensive troubleshooting sessions to maintain a clean and chronologically relevant diagnostic environment.
An administrator wants to set up a remote user authentication service for the many users that access a Juniper security device. In this scenario, what are two supported authentication protocols? (Choose two.)
RADIUS
TACACS+
SHA
IPsec
For managing high volumes of administrative users, Junos OS supports externalizing the authentication, authorization, and accounting (AAA) process. The two primary industry-standard protocols supported for this purpose are RADIUS (Remote Authentication Dial-In User Service) and TACACS+ (Terminal Access Controller Access-Control System Plus).
Using these protocols allows an architect to maintain a centralized user database on an external server (like Cisco ACS, FreeRADIUS, or Microsoft NPS) rather than configuring every individual user account locally on every Junos device. When a user attempts to log in via SSH or the console, the Junos device acts as a client, forwarding the credentials to the remote server. RADIUS is often preferred for its broad compatibility and efficiency, while TACACS+ is frequently chosen for its ability to separate authentication from authorization and its support for granular command-level accounting. SHA (Secure Hash Algorithm) is a cryptographic hash function used within these processes but is not an authentication protocol itself. Similarly, IPsec is a suite for securing IP communications (VPNs) and is unrelated to the administrative login AAA sequence.
According to HPE Juniper Networking, when should you use the replace pattern command instead of the rename command?
You want to create a private candidate configuration.
You want to disable a physical interface.
You need to edit a single component name in the configuration.
You want to globally replace all occurrences of a specific string.
In Junos OS configuration management, the rename and replace pattern commands serve distinct roles for modifying the candidate configuration. The rename command is used when an administrator needs to change the identifier of a specific, single configuration object—such as changing an interface name or a policy-term name—while keeping the underlying properties of that object intact. In contrast, the replace pattern command is a powerful utility designed for bulk modifications across the configuration hierarchy. It utilizes string matching or regular expressions to find every occurrence of a specific text string and substitute it with another.
This is particularly useful in scenarios involving mass updates, such as migrating an entire subnet across multiple interface descriptions, firewall filters, and routing policy terms simultaneously. While rename acts locally on a specific path, replace pattern can be applied globally from the root of the configuration or constrained to a specific sub-hierarchy. As a Senior Architect, it is critical to understand that replace pattern does not just change names; it can modify any part of the statement text, making it an essential tool for efficient large-scale configuration refactoring without the need for manual, line-by-line edits. Reference: Configuration Basics, Modifying Configuration, Command Line Editing.
Exhibit:
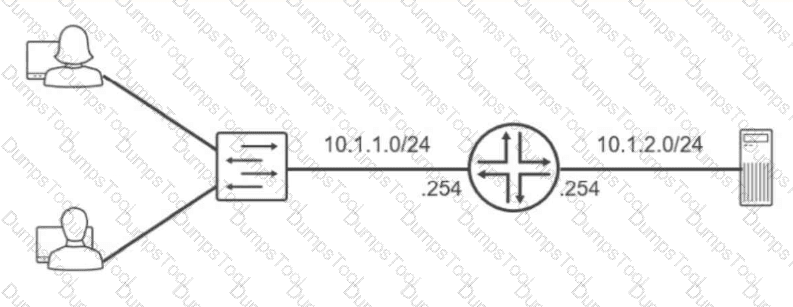
Referring to the exhibit, which routing configuration is required for these two users to access the remote server?
Users and the server require a default gateway.
Trunk ports must be enabled on the switch.
Users must connect directly to the router.
A routing protocol must be enabled on the router.
The network topology illustrates two distinct IP subnets, 10.1.1.0/24 and 10.1.2.0/24 , separated by a Layer 3 router. For hosts on the first subnet to communicate with the server on the second subnet, an intermediary device must perform inter-subnet routing. The router acts as the exit point for each local segment, utilizing its interfaces assigned with the .254 host address as the logical path to external networks.
The fundamental requirement for this communication is the configuration of a default gateway on all end-nodes. When the users (on 10.1.1.0/24 ) attempt to send data to the server (on 10.1.2.0/24 ), their local TCP/IP stack recognizes the destination is not on the local wire. Without a defined default gateway, the hosts would simply drop the traffic as unroutable. By setting the default gateway to 10.1.1.254 for users and 10.1.2.254 for the server, the hosts are instructed to forward all off-net traffic to the router. The router then consults its routing table—which contains these directly connected routes—and forwards the packets to the appropriate egress interface. While VLAN tagging or routing protocols could exist in more complex environments, the primary necessity for basic reachability between these two specific segments is a correctly configured gateway on the terminal devices. Reference: Networking Fundamentals, IP Routing Basics, Default Gateway Configuration.
==========
You successfully committed a configuration change. You now realize an issue exists and must revert back to the previous configuration. Which command entered in configuration mode will accomplish this task when committed?
show | compare
save config
rollback 0
rollback 1
Junos OS features a sophisticated configuration management system that automatically creates a snapshot of the active configuration every time a commit is successfully performed. These snapshots are stored as rollback files in a historical archive. Within the configuration mode hierarchy, the rollback command allows an administrator to discard current candidate changes and load a previously committed configuration into the candidate buffer.
The numbering of these rollback files is sequential and follows a specific logic: rollback 0 represents the configuration that is currently active and running on the system. To revert to the state that existed immediately prior to the most recent commit, the administrator must use rollback 1. This command overwrites the current candidate configuration with the previous operational state. It is important to note that executing rollback 1 does not immediately impact the running system; it merely populates the candidate database. The changes must still be verified—often using show | compare—and then finalized by executing the commit command. By default, Junos maintains up to 50 of these rollback configurations (and up to 100 on certain platforms/versions), providing a robust safety net for operational recovery and auditing. Reference: Configuration Basics, Managing Configurations, Rollback configurations.
Exhibit:
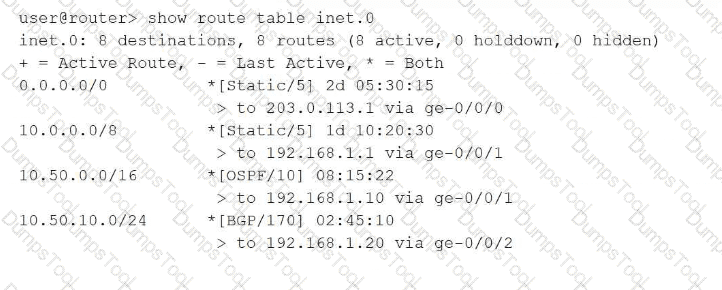
Referring to the exhibit, which route will be selected for a packet destined to IP address 10.50.10.55?
Route 0.0.0.0/0 will be selected using next hop 203.0.113.1 because the default route matches all destinations and has been active the longest.
Route 10.50.0.0/16 will be selected using next hop 192.168.1.10 because OSPF has a better preference value than BGP.
Route 10.50.10.0/24 will be selected using next hop 192.168.1.20 because it has the longest prefix match for the destination address.
Route 10.0.0.0/8 will be selected using next hop 192.168.1.1 because it was learned from the static routing protocol which has the lowest preference value.
In Junos OS, the Routing Information Base (RIB) selection process follows a strict hierarchy where the Longest Prefix Match (LPM) is the absolute primary tie-breaker. When a packet is destined for 10.50.10.55 , the Routing Engine searches the inet.0 table for all matching entries. In this exhibit, four routes match: the default route ( 0.0.0.0/0 ), a general static route ( 10.0.0.0/8 ), an OSPF route ( 10.50.0.0/16 ), and a BGP route ( 10.50.10.0/24 ).
The LPM rule dictates that the router must select the most specific route available, which is defined as the entry with the highest number of matching bits in the subnet mask. The 10.50.10.0/24 route matches 24 bits of the destination address, making it more specific than the 16-bit, 8-bit, or 0-bit alternatives. It is critical to understand that route preference (e.g., Static at 5, OSPF at 10, or BGP at 170) is only evaluated if there are multiple paths to the exact same prefix and length. Because these prefixes vary in length, the length takes precedence over the protocol preference. Therefore, the BGP-learned route via 192.168.1.20 is selected as the active path, ensuring traffic follows the most granular routing information provided to the device. Reference: Routing Fundamentals, Routing Table Selection, Longest Prefix Match.
==========
You committed a new configuration on a Junos router, but users report connectivity issues. You must quickly restore the previous working configuration without manually editing the candidate configuration. Which command should you use to load the required configuration into the candidate configuration?
rollback 0
show | compare rollback
rollback 1
load override
In Junos OS, the configuration database is designed with a robust versioning system that facilitates rapid recovery from administrative errors. Every time a commit command is successfully executed, the system automatically archives the previous active configuration and assigns it a " rollback " index. The rollback command is used within configuration mode to revert the candidate configuration to a previously saved state.
The indices are zero-based, where rollback 0 represents the currently active configuration that was just committed. To restore the configuration that was functional immediately before the most recent, problematic commit, the administrator must use rollback 1. This command replaces the current candidate configuration with the contents of the last known working state. It is important to note that executing rollback 1 only populates the candidate buffer; to make this previous configuration active and restore connectivity, the administrator must subsequently issue the commit command. This mechanism is a cornerstone of Junos OS ' s commitment to high availability and operational resilience, allowing for nearly instantaneous restoration of services without the need for manual line-by-line configuration edits during a network outage.
What is the purpose of an ARP packet?
to determine the MPLS label of a given IP address
to determine the IP address of a given URL
to determine the MAC address of a given IP address
to determine the IP address of a given MAC address
The Address Resolution Protocol (ARP) is a fundamental Layer 2 utility used within the IPv4 suite to resolve a known network-layer (Layer 3) address to its corresponding physical media access control (MAC) or hardware address (Layer 2). In a typical Ethernet environment, when a Junos device needs to forward a packet to a next-hop on a local subnet, the Packet Forwarding Engine (PFE) requires the destination MAC address to properly encapsulate the frame.
The process begins with an ARP Request, which is broadcast to all hosts on the segment asking, " Who owns this IP address? " The host assigned that specific IP responds with an ARP Reply containing its MAC address. The Junos device then stores this mapping in its ARP cache (viewable via the show arp command) to avoid repeated broadcasts for subsequent packets. This resolution is essential because while IP addresses facilitate end-to-end logical routing, the actual delivery of data across a physical wire or switch fabric relies entirely on hardware addresses. Without successful ARP resolution, the device cannot complete the Layer 2 header, and the traffic will be dropped as " encapsulation failed. "
Which two statements are correct about Junos OS? (Choose two.)
Junos OS provides the ability to run unsigned third-party binaries.
Junos OS provides modularization of software processes.
Junos OS combines security and routing policies.
Junos OS separates the control plane and the forwarding plane.
Junos OS is built upon a highly stable and secure architecture that distinguishes it from many legacy network operating systems. Two of its most defining characteristics are software modularization and the separation of the control and forwarding planes .
Modularization means that Junos OS runs each major function—such as the routing protocol process (rpd), the management process (mgd), and the interface process (dcd)—as an independent software daemon in its own protected memory space. This ensures that if a single process crashes or needs to be restarted, it does not bring down the entire system or interrupt traffic forwarding.
Furthermore, the physical and logical separation of the Control Plane (Routing Engine) and the Forwarding Plane (Packet Forwarding Engine) is a cornerstone of Junos design. The Routing Engine handles complex intelligence, protocol calculations, and management, while the Packet Forwarding Engine performs high-speed packet switching in hardware. This ensures that a heavy management load or a complex routing recalculation won ' t cause " jitter " or packet loss for transit traffic. Conversely, Junos strictly prohibits unsigned third-party binaries to maintain system integrity, and it maintains a clear functional distinction between routing policies (path selection) and security policies (traffic permit/deny).
Which two operational mode commands would you use to verify CPU and memory utilization on a Junos device? (Choose two.)
show chassis routing-engine
show chassis environment
show system processes extensive
show system resource-monitor summary
In the Junos OS architecture, maintaining visibility into the health of the Routing Engine (RE) is paramount for ensuring control plane stability. The command show chassis routing-engine is the primary tool for a high-level hardware status overview. It provides critical telemetry regarding the RE ' s current CPU utilization (broken down by user, background, and kernel tasks), memory usage statistics, and uptime. This command is essential for identifying if the device ' s " brain " is under significant stress due to heavy protocol processing or management tasks.
For a more granular, process-specific analysis, the show system processes extensive command is utilized. Similar to the ' top ' utility in Unix-based systems, it lists all active software daemons (such as rpd for routing, dcd for interfaces, and mgd for management) and ranks them by their real-time CPU and memory consumption. This allows an architect to pinpoint exactly which process might be causing a performance bottleneck. While show chassis environment focuses on physical hardware health like temperatures and fan speeds, and resource-monitor provides summary data, the combination of show chassis routing-engine and show system processes extensive offers the most comprehensive diagnostic view of the device ' s internal computational resources. Reference: Operational Monitoring and Maintenance, System Health Monitoring.
==========

TESTED 09 May 2026
Copyright © 2014-2026 DumpsTool. All Rights Reserved
