Which stakeholder is MOST important to include when defining a risk profile during me selection process for a new third party application?
The third-party risk manager
The application vendor
The business process owner
The information security manager
A risk profile is a summary of the nature and level of risk that an organization faces. It includes information such as the sources, causes, and consequences of the risks, their likelihood and impact, their interrelationships and dependencies, and their alignment with the risk appetite and tolerance. A risk profile is influenced by various factors, such as the organization’s objectives, strategies, activities, processes, resources, capabilities, culture, etc. When defining a risk profile during the selection process for a new third party application, the stakeholder that is most important to include is the business process owner, who is the person who has the authority and responsibility for the design, execution, and performance of a business process. The business process owner can provide valuable input and insight into the requirements, expectations, and dependencies of the business process that will use the new third party application, and the potential risks and opportunities that may arise from the selection of the application. The business process owner can also help to prioritize and address the risks, and ensure that the risk profile is aligned with the business objectives and strategies. References = 5
When reviewing a report on the performance of control processes, it is MOST important to verify whether the:
business process objectives have been met.
control adheres to regulatory standards.
residual risk objectives have been achieved.
control process is designed effectively.
When reviewing a report on the performance of control processes, it is most important to verify whether the residual risk objectives have been achieved, as this indicates the extent to which the control processes have reduced the risk to an acceptable level. Residual risk is the risk that remains after the implementation of controls, and it should be aligned with the risk appetite and tolerance of the enterprise. Business process objectives, regulatory standards, and control process design are not the most important factors to verify,as they do not directly measure the effectiveness and efficiency of the control processes in managing the risk. References = CRISCPractice Quiz and Exam Prep; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 209.
Which of the following is the GREATEST concern when an organization uses a managed security service provider as a firewall administrator?
Exposure of log data
Lack of governance
Increased number of firewall rules
Lack of agreed-upon standards
A managed security service provider (MSSP) is a third-party entity that offers network security services to an organization, such as firewall operation, administration, monitoring, and maintenance1. A firewall is a device or software that controls the incoming and outgoing network traffic based on predefined rules2. A firewall administrator is a person or entity that manages and maintains the firewall configuration, rules, and policies3. When an organizationuses an MSSP as a firewall administrator, the greatest concern is the exposure of log data, because log data contains sensitive and valuable information about the organization’s network activity, such as source and destination IP addresses, ports, protocols, timestamps, and user identities4. If the log data is not protected properly by the MSSP, it could be accessed, modified, or stolen by unauthorized parties, such as hackers, competitors, or regulators, which could result in data breaches, compliance violations, reputational damage, or legal liabilities for the organization5. The other options are not as concerning as the exposure of log data, because they do not pose a direct and immediate threat to the organization’s data security and privacy, but rather affect the quality and efficiency of the firewall management, as explained below:
B. Lack of governance is a concern when an organization uses an MSSP as a firewall administrator, because it could lead to misalignment or inconsistency between the organization’s and the MSSP’s objectives, policies, and standards for firewall management. However, this concern can be mitigated by establishing a clear and comprehensive service level agreement (SLA) with the MSSP,which defines the roles, responsibilities, expectations, and performance indicators for the firewall management service6.
C. Increased number of firewall rules is a concern when an organization uses an MSSP as a firewall administrator, because it could create complexity, confusion, or duplication in the firewall configuration, which could affect the firewall performance and security. However, this concern can be mitigated by conducting regular firewall audits and reviews with the MSSP, which can help to rationalize, optimize, and update the firewall rules, and to ensure that they are relevant, effective, and efficient for the organization’s network environment.
D. Lack of agreed-upon standards is a concern when an organization uses an MSSP as a firewall administrator, because it could result in gaps or weaknesses in the firewall design and implementation, which could compromise the firewall functionality and security. However, this concern can be mitigated by adopting and following industry best practices, norms, and expectations for firewall management, such as the National Institute of Standards and Technology (NIST) guidelines, the Center for Internet Security (CIS) benchmarks, or the Payment Card Industry Data Security Standard (PCI DSS) requirements . References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 115. What Is A Managed Security Service Provider (MSSP)? - Fortinet, What is a Firewall? - Definition from Techopedia, Firewall Administrator Job Description - Betterteam, What is a Firewall Log? - Definition from Techopedia, Firewall Log Management: Why It’s Important and How to Do It Right, How to Write a Service Level Agreement (SLA) for an MSSP, [Firewall Auditing: BestPractices for Security and Compliance], [Guidelines on Firewalls and Firewall Policy | CSRC] , [CIS Firewall Benchmark - CIS], [PCI DSS and Firewalls - PCI Security Standards Council]
When assigning control ownership, it is MOST important to verify that the owner has accountability for:
Control effectiveness.
The budget for control implementation.
Assessment of control risk.
Internal control audits.
Control owners must be accountable for ensuring the effectiveness of the controls they manage. This accountability ensures the alignment of controls with risk objectives, as outlined inControl Governance and Ownership.
Which of the following can be interpreted from a single data point on a risk heat map?
Risk tolerance
Risk magnitude
Risk response
Risk appetite
A risk heat map is a kind of risk matrix where risks are ranked based on their potential impact and their likelihood of occurring, which allows you to prioritize the risks that pose the greatest threat. The severity of each risk is indicated by color, usually green for low risk, red for high risk, and yellow for medium risk. Therefore, from a single data point on a risk heat map, one can interpret the risk magnitude, which is the product of impact and likelihood. The other options are not directly related to a single data point on a risk heat map, but rather to the overall risk management strategy and context. References = Risk Assessment and Analysis Methods: Qualitative and Quantitative; What Is a Risk Heat Map, and How Can It Help Your Risk Management Strategy; CRISC Certified in Risk and Information Systems Control – Question599
Which of the following is MOST important to ensure when continuously monitoring the performance of a client-facing application?
Objectives are confirmed with the business owner.
Control owners approve control changes.
End-user acceptance testing has been conducted.
Performance information in the log is encrypted.
The performance of a client-facing application is the measure of how well the application meets the expectations and requirements of the clients who use it. The performance of a client-facing application can be affected by various factors, such as functionality, usability, reliability, availability, security, and scalability. Continuously monitoring the performance of a client-facing application is the process of collecting, analyzing, and reporting on the performance data and metrics of the application over time. Continuously monitoring the performance of a client-facing application can help identify and resolve issues, improve quality, optimize resources, and enhance client satisfaction. The most important thing to ensure when continuously monitoring the performance of a client-facing application is that the objectives are confirmed with the business owner. The business owner is the person or entity who has the authority and responsibility for the business value and outcomes of the application. The business owner defines the objectives, goals, and requirements of the application, and sets the performance criteria and targets. Confirming the objectives with the business owner can help ensure that the performance monitoring is aligned with the business needs and expectations, and that the performance data and metrics are relevant, accurate, and meaningful. References = Risk and Information SystemsControl Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.3: Continuous Monitoring, p. 203-205.
An organization’s expense claim system allows users to split large transactions into smaller ones to bypass limits. What should the risk practitioner do?
Conduct an audit to determine the frequency of occurrence
Update the probability in the risk register
Create a noncompliance risk scenario
Weigh compliance against the cost-benefit
This behavior representsintentional circumvention of control, requiring formal documentation and assessment as anoncompliance risk scenario.
CRISC principle:
“When control circumvention occurs, the risk practitioner should document the event as a noncompliance risk scenario to evaluate its impact and treatment.”
The other options—auditing, probability updates, or cost analysis—may follow, but the first step isformal recognitionof the risk within the risk register via a new scenario.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Scenario Development and Control Evaluation.
Which of the following approaches to bring your own device (BYOD) service delivery provides the BEST protection from data loss?
Enable data wipe capabilities
Penetration testing and session timeouts
Implement remote monitoring
Enforce strong passwords and data encryption
The best approach to bring your own device (BYOD) service delivery that provides the best protection from data loss is to enforce strong passwords and data encryption. BYOD is a service delivery model that allows the users to use their own personal devices, such as smartphones, tablets, or laptops, to access the enterprise’s network, applications, or data. BYOD can provide various benefits, such as increased productivity, flexibility, and satisfaction of the users, as well as reduced costs and maintenance of the enterprise. However, BYOD also poses various risks, such as data loss, data breach, malware infection, or unauthorized access, as the personal devices may not have the same level of security and control as the enterprise-owned devices. Enforcing strong passwords and data encryption is the best approach to protect the data on the personal devices, as it helps to prevent or limit the unauthorized access, disclosure, or theft of the data, especially if the devices are lost, stolen, or compromised. Enforcing strong passwords and data encryption also helps to comply with the legal and regulatory requirements for data protection and privacy. Enabling data wipe capabilities, penetration testing and session timeouts, and implementing remote monitoring are also useful approaches, but they are not as effective as enforcing strong passwords and data encryption, as they are either reactive or detective measures, rather than proactive or preventive measures. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
A recent big data project has resulted in the creation of an application used to support important investment decisions. Which of the following should be of GREATEST concern to the risk practitioner?
Data quality
Maintenance costs
Data redundancy
System integration
The greatest concern for the risk practitioner when a big data project has resulted in the creation of an application used to support important investment decisions is the data quality. Data quality is the degree to which the data is accurate, complete, consistent, reliable, relevant, and timely. Data quality is essential for the success of any big data project, as it affects the validity and reliability of the analysis and the outcomes. Poor data quality could lead to erroneous or misleading results, which could have negative consequences for the investment decisions and the organization’s performance and reputation. The other options are not as concerning as the data quality, although they may also pose some challenges or risks for the big data project. Maintenance costs, data redundancy, and system integration are all factors that could affect the efficiency and effectiveness of the big data project, but they do not directly affect the accuracy and reliability of the analysis and the outcomes. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.1, page 3-20.
Which of the following is the PRIMARY reason to ensure software engineers test patches before release to the production environment?
To detect incompatibilities that might disrupt the operation
To provide assurance that deployed patches have been properly authorized
To understand how long it will take to deploy the patch
To support availability by authorizing the release of the patch at the appropriate time
Pre-production compatibility testing ensures patches won’t break applications or services, protecting availability—a key control objective outlined in ISACA’s guidance on Change and Configuration Management.
After identifying new risk events during a project, the project manager s NEXT step should be to:
determine if the scenarios need 10 be accepted or responded to.
record the scenarios into the risk register.
continue with a qualitative risk analysis.
continue with a quantitative risk analysis.
After identifying new risk events during a project, the project manager’s next step should be to record the scenarios into the risk register, which is a document that records and tracks the identified risks, their causes, impacts, likelihood, responses, owners, and status. Recording the scenarios into the risk registerhelps to document and communicate the risks to the project team and stakeholders, and to facilitate the subsequent risk analysis and response processes. The other options are not the next steps, but rather the subsequent steps after recording the scenarios into the risk register. Determining if the scenarios need to be accepted or responded to is part of the risk evaluation and treatment process, which requires a prior risk analysis. Continuing with a qualitative or quantitative risk analysis is part of the risk assessment process, which requires a prior risk identification and documentation. References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana; Risk Identification in Project Management; 6.3. The 5 Steps of the Risk Management Process
Which of the following is the PRIMARY consideration when establishing an organization ' s risk management methodology?
Business context
Risk tolerance level
Resource requirements
Benchmarking information
The primary consideration when establishing an organization’s risk management methodology is the business context, which includes the internal and external factors that influence the organization’s objectives, strategies, scope, and boundaries. The business context helps to define the risk criteria, the risk appetite, the risk identification, the risk analysis, and the risk treatment. The other options are not the primary consideration, but rather the outcomes or inputs of the risk management methodology. References = ISO 31000 Risk Management – Principles andGuidelines; ISO 31000 Principles of Risk Management; The risk management process: What is the best structure and administration?
Which of the following would MOST likely result in agreement on accountability for risk scenarios?
Using a facilitated risk management workshop
Relying on generic risk scenarios
Relying on external IT risk professionals
Distributing predefined scenarios for review
The correct answer isAbecause afacilitated risk management workshopis most likely to result in agreement on accountability for risk scenarios. A workshop allows relevant stakeholders to discuss the scenarios together, align on business context, clarify roles, and agree on who owns the risk and who is responsible for treatment and escalation.
The other options are less effective:
B. Relying on generic risk scenariosreduces alignment with the specific business context and usually weakens ownership clarity.
C. Relying on external IT risk professionalsmay provide expertise, but accountability must be agreed internally by business stakeholders.
D. Distributing predefined scenarios for reviewis less effective than active facilitation because it does not create the same level of interaction and consensus.
Exact Extracts supporting the answer:
“An interdisciplinary team within the enterprise offers the best perspective on risk management to employees and stakeholders.”
“To ensure the overall effectiveness of a risk management program it is essential to have the participation of relevant stakeholders.”
“Clear detailed roles and responsibilities are MOST critical to ensure the three lines of defense work together effectively.”
“The BEST approach when developing risk scenarios for an enterprise is to use both the top-down and the bottom-up approach because they have different perspectives.”
“The management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
These extracts support that agreement on accountability is most likely when relevant stakeholders actively participate together in a structured discussion.
===========
Which of the following is the MOST important reason for a risk practitioner to continuously monitor a critical security transformation program?
To validate the quality of defined deliverables for the program
To detect increases in program costs
To ensure program risk events are mitigated in a timely manner
To provide timely reporting to the governance steering committee
Continuously monitoring a critical security transformation program is crucial for a risk practitioner primarily to ensure that any risk events are identified and mitigated promptly. This ensures that the security transformation remains on track and that potential risks do not escalate to a level that could compromise the program’s success.
Identifying and Mitigating Risks:
Risk Identification:Continuously monitoring the program helps in the early identification of risks. This is essential because unidentified risks can lead to unexpected issues that might derail the program.
Timely Mitigation:Once risks are identified, it is crucial to mitigate them as quickly as possible. Delays in mitigation can allow risks to grow in impact, making them harder and more expensive to address.
Ensuring Program Continuity:
Maintaining Momentum:Security transformation programs often involve significant changes and can be disruptive. By ensuring that risks are mitigated in a timely manner, the risk practitioner helps maintain the program’s momentum and keeps it on schedule.
Preventing Escalation:Timely risk mitigation prevents minor issues from escalating into major problems that could halt the program.
Aligning with Strategic Goals:
Strategic Alignment:Ensuring timely mitigation of risks helps in keeping the program aligned with the strategic goals of the organization. It ensures that the security objectives are met without significant delays or cost overruns.
Which of the following is the PRIMARY objective for automating controls?
Reducing the need for audit reviews
Facilitating continuous control monitoring
Improving control process efficiency
Complying with functional requirements
The primary objective of automating controls is to facilitate continuous control monitoring. Automation enables real-time or near-real-time oversight of control activities, allowing for prompt detection and response to control failures or anomalies. This continuous monitoring enhances the organization ' s ability to maintain compliance and manage risks effectively.
Which of the following is the BEST course of action to reduce risk impact?
Create an IT security policy.
Implement corrective measures.
Implement detective controls.
Leverage existing technology
To reduce risk impact, the best course of action is to implement corrective measures, which are actions taken to eliminate or minimize the negative effects of a risk event after it has occurred12.
Corrective measures can include restoring normal operations, repairing or replacing damaged assets, recovering lost data, compensating affected stakeholders, and implementing lessons learned12.
Corrective measures can reduce risk impact by minimizing the duration, severity, and scope of the consequences of a risk event, as well as preventing recurrence or escalation of similar risks in the future12.
The other options are not the best course of action to reduce risk impact, but rather different types of risk responses that may have different objectives and effects. For example:
Creating an IT security policy is an example of a preventive measure, which is an action taken to avoid or reduce the likelihood of a risk event before it occurs12. A preventive measure can reduce risk exposure, but not risk impact.
Implementing detective controls is an example of a monitoring measure, which is an action taken to identify and measure the occurrence or status of a risk event during or after it occurs12. A monitoring measure can provide timely information and feedback, but not reduce risk impact.
Leveraging existing technology is an example of a mitigation measure, which is an action taken to reduce the likelihood or impact of a risk event before it occurs12. A mitigation measure can reduce risk exposure, but not necessarily risk impact. References =
1: Risk Management Guide for Information Technology Systems, NIST Special Publication 800-30, July 2002
2: Project Risk Management Handbook, California Department of Transportation, June 2011
Which of the following BEST enables a risk practitioner to enhance understanding of risk among stakeholders?
Key risk indicators (KRIs)
Risk scenarios
Business impact analysis (BIA)
Threat analysis
Risk scenarios are descriptions of possible events or situations that could cause or affect a risk. Risk scenarios can help a risk practitioner to enhance understanding of risk among stakeholders, as they can illustrate the causes, consequences, and impacts of the risk in a clear and realistic way. Risk scenarios can also facilitate communication and collaboration among stakeholders, as they can provide a common language and framework for risk identification, analysis, and response. Risk scenarios can also support decision-making and prioritization, as they can show the likelihood and severity of the risk outcomes. References = Most Asked CRISC Exam Questions and Answers. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 237.
Which of the following is the PRIMARY benefit of implementing key control indicators (KCIs)?
Confirming the adequacy of recovery plans.
Improving compliance with control standards.
Providing early detection of control degradation.
Reducing the number of incidents.
Key Control Indicators (KCIs) are metrics used to monitor the performance of controls. Their primary benefit is the early detection of control degradation, allowing organizations to take corrective actions before issues escalate into significant problems.
Which of the following is the BEST source for identifying key control indicators (KCIs)?
Privileged user activity monitoring controls
Controls mapped to organizational risk scenarios
Recent audit findings of control weaknesses
A list of critical security processes
Key control indicators (KCIs) are metrics that provide information on the extent to which a given control is meeting its intended objectives in terms of loss prevention, reduction, etc. In order to provide such information, the control effectiveness indicator has to have an explicit relationship to both the specific control and to the specific risk against which the control has been implemented1. Therefore, the best source for identifying KCIs is to use controls mapped to organizational risk scenarios, which can help define the control objectives, the expectedoutcomes, and the relevant indicators for each risk scenario. This approach can also help align the KCIs with the organizational goals and strategy, and enable the monitoring and reporting of the control effectiveness23.
The other options are not the best sources for identifying KCIs, because:
Privileged user activity monitoring controls are specific types of controls that aim to prevent unauthorized access or misuse of sensitive data or systems by privileged users. They are not a sourcefor identifying KCIs, but rather a possible subject of KCIs. For example, a KCI for this type of control could be the number of privileged user accounts that have not been reviewed or revoked within a specified period4.
Recent audit findings of control weaknesses are useful for identifying the gaps or deficiencies in the existing control environment, and for recommending corrective actions or improvements. However, they are not a source for identifying KCIs, but rather an input for evaluating or revising the existing KCIs. For example, if an audit finding reveals that a control is not operating as intended, or that a KCI is not providing reliable or timely information, then the control or the KCI may need to be modified or replaced5.
A list of critical security processes is a high-level overview of the key activities or functions that are essential for maintaining the security of the organization’s assets and information. It is not a source for identifying KCIs, but rather a starting point for defining the control objectives and requirements. For example, a critical security process could be incident response, which requires a set of controls to ensure the timely and effective detection, containment, analysis, and recovery of security incidents. The KCIs for this process could be the number of incidents detected, the average time to resolve incidents, or the percentage of incidents that resulted in data breaches6.
References =
Key Control Indicator (KCI) - CIO Wiki
How to Develop Key Control Indicators to Improve Security Risk Monitoring - Gartner
Indicators - Program Evaluation - CDC
Privileged User Monitoring: What Is It and Why Is It Important? - LogRhythm
Internal Audit Key Performance Indicators (KPIs) - AuditBoard
Hierarchy of Controls - NIOSH - CDC
The risk appetite for an organization could be derived from which of the following?
Cost of controls
Annual loss expectancy (ALE)
Inherent risk
Residual risk
According to the CRISC Review Manual1, cost of controls is the amount of money or resources that an organization is willing to spend to implement and maintain risk responses. Cost of controls is one of the factors that influences the risk appetite of an organization, as it reflects thetrade-off between the benefits and costs of risk responses. Cost of controls helps to determine the optimal level of risk that an organization can accept in pursuit of its objectives, and to align the risk responses with the organization’s strategy, goals, and culture. References = CRISC Review Manual1, page 193.
An organization has allowed several employees to retire early in order to avoid layoffs Many of these employees have been subject matter experts for critical assets Which type of risk is MOST likely to materialize?
Confidentiality breach
Institutional knowledge loss
Intellectual property loss
Unauthorized access
The type of risk that is most likely to materialize as a result of allowing several employees to retire early in order to avoid layoffs is institutional knowledge loss, as it represents the loss of valuable information, experience, and expertise that the employees have accumulated over time, and that may not be easily transferred or replaced. Confidentiality breach, intellectual property loss, and unauthorized access are not the most likely types of risk, as they are more related to the security, ownership, or access of information, respectively, rather than the retention or transfer of knowledge. References = CRISC Review Manual, 7th Edition, page 100.
What is senior management ' s role in the RACI model when tasked with reviewing monthly status reports provided by risk owners?
Accountable
Informed
Responsible
Consulted
Senior management’s role in the RACI model when tasked with reviewing monthly status reports provided by risk owners is accountable, as it means that they have the ultimate authority and responsibility to approve or reject the risk management decisions and actions, and to oversee the risk management performance and outcomes. The other options are not the correct roles, as they imply different levels or types of involvement or participation in the risk management process, such as being informed, responsible, or consulted, respectively. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following is the PRIMARY reason for logging in a production database environment?
To provide evidence of activities
To prevent illicit actions of database administrators (DBAs)
To ensure that changes are authorized
To ensure that changes made are correctly applied
The primary reason for logging is to provide evidence of activities, ensuring accountability and traceability. This supports investigations, audits, and compliance requirements, aligning withControl Monitoring and Reportingstandards.
Which of the following is the MOST important objective of an enterprise risk management (ERM) program?
To create a complete repository of risk to the organization
To create a comprehensive view of critical risk to the organization
To provide a bottom-up view of the most significant risk scenarios
To optimize costs of managing risk scenarios in the organization
The most important objective of an enterprise risk management (ERM) program is to create a comprehensive view of critical risk to the organization, as it enables the organization to identify, assess, and prioritize the key risks that may affect its objectives and strategy, and to implement appropriate risk responses and controls. A comprehensive view of critical risk also helps the organization to align its risk appetite and tolerance with its business goals and value creation, and to enhance its risk culture and governance. A comprehensive view of critical risk can be achieved by integrating risk management across all levels and functions of the organization, and by using consistent and reliable risk information and reporting. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 242. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 242. CRISC Sample Questions 2024, Question 242.
Which of the following is the MOST important reason to restrict access to the risk register on a need-to-know basis?
It contains vulnerabilities and threats.
The risk methodology is intellectual property.
Contents may be used as auditable findings.
Risk scenarios may be misinterpreted.
Restricting access to the risk register on a need-to-know basis is important because it contains vulnerabilities and threats that could expose the organization to potential harm or loss if they are disclosed or exploited by unauthorized parties. The risk register is a tool that captures and documents the risk identification, analysis, evaluation, and treatment processes1. The risk register contains sensitive information such as the sources and causes of risk, the potential impacts and consequences of risk, the likelihood and frequency of risk occurrence, and the risk response actions and plans1. If this information is accessed by unauthorized parties, such as competitors, hackers, or malicious insiders, they could use it to launch attacks, sabotageoperations, or gain an unfair advantage over the organization. Therefore, access to the risk register should be limited to those who have a legitimate need and authorization to view, modify, or use the information, such as the risk owners, managers, or practitioners
Several network user accounts were recently created without the required management approvals. Which of the following would be the risk practitioner ' s BEST recommendation to address this situation?
Conduct a comprehensive compliance review.
Develop incident response procedures for noncompliance.
Investigate the root cause of noncompliance.
Declare a security breach and Inform management.
Several network user accounts were recently created without the required management approvals. This indicates that there is a risk of unauthorized access, use, disclosure, modification, or destruction of the network resources or data, which may affect the confidentiality, integrity, and availability of the network.
The best recommendation to address this situation is to investigate the root cause of noncompliance. This means that the risk practitioner should analyze the factors or reasons that led to the creation of the network user accounts without the required management approvals, such as human error, negligence, malice, system failure, process flaw, etc.
Investigating the root cause of noncompliance helps to identify and correct the source of the problem, prevent or reduce the recurrence of the problem, and improve the compliance and security of the network user accounts.
The other options are not the best recommendations to address this situation. They are either secondary or not effective for noncompliance.
The references for this answer are:
Risk IT Framework, page 31
Information Technology & Security, page 25
Risk Scenarios Starter Pack, page 23
A trusted third-party service provider has determined that the risk of a client ' s systems being hacked is low. Which of the following would be the client ' s BEST course of action?
Perform their own risk assessment
Implement additional controls to address the risk.
Accept the risk based on the third party ' s risk assessment
Perform an independent audit of the third party.
A risk assessment is a process that identifies, analyzes, and evaluates the risks that an organization faces in relation to its objectives, assets, and operations. A risk assessment helps to determine the likelihood and impact of potential threats, as well as the adequacy and effectiveness of existing controls. A risk assessment also provides the basis for risk treatment, which involves selecting and implementing the appropriate risk responses, such as avoiding,transferring, mitigating, or accepting the risk. The client’s best course of action in this scenario is to perform their own risk assessment, rather than relying on the third-party service provider’s risk assessment. This is because the third-party service provider may have different risk criteria, assumptions, methods, or perspectives than the client, and may not fully understand or address the client’s specific risk context, needs, and expectations. The third-party service provider’s risk assessment may also be biased, outdated, or inaccurate, and may not reflect the current or future risk environment. By performing their own risk assessment, the client can ensure that the risk of their systems being hacked is properly identified, measured, and managed, and that the risk level is acceptable and aligned with their risk appetite and tolerance. The other options are not the best courses of action for the client, as they may expose the client to unnecessary or unacceptable risk. Implementing additional controls to address the risk may be costly, ineffective, or redundant, and may not be justified by the actual risk level. Accepting the risk based on the third-party service provider’s risk assessment may be risky, as the client may not have a clear or accurate understanding of the risk exposure or consequences. Performing an independent audit of the third party may be useful, but it may not be sufficient or timely to assess and address the risk of the client’s systems being hacked. References = CRISC Review Manual, pages 38-391; CRISC Review Questions, Answers & Explanations Manual, page 792
What should be the PRIMARY objective for a risk practitioner performing a post-implementation review of an IT risk mitigation project?
Documenting project lessons learned
Validating the risk mitigation project has been completed
Confirming that the project budget was not exceeded
Verifying that the risk level has been lowered
A post-implementation review (PIR) is a process to evaluate whether the objectives of the project were met and whether the project delivered the expected benefits and outcomes1. The primary objective of a risk practitioner performing a PIR of an IT risk mitigation project is to verify that the risk level has been lowered as a result of the project implementation2. This can be done by comparing the actual risk level with theexpected risk level, assessing the effectiveness and efficiency of the risk mitigation controls, and identifying any residual or emergingrisks3. Documenting project lessons learned, validating the project completion, and confirming the project budget are important aspects of a PIR, but they are not the primary objective for a risk practitioner, as they do not directly measure the impact of the project on the risk level4. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk Response and Mitigation, Section 5.4: Post-Implementation Review, pp. 239-241.
An organization ' s IT infrastructure is running end-of-life software that is not allowed without exception approval. Which of the following would provide the MOST helpful information to justify investing in updated software?
The balanced scorecard
A cost-benefit analysis
The risk management frameworkD, A roadmap of IT strategic planning
A cost-benefit analysis is a tool that compares the costs and benefits of different alternatives, such as updating software or continuing to use end-of-life software. A cost-benefit analysis can provide the mosthelpful information to justify investing in updated software, as it can show the potential savings, benefits, and risks of each option, and help the decision-makers choose the best course of action. A cost-benefit analysis can also include qualitative factors, such as security, compliance, performance, and customer satisfaction, that may be affected by the software update. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 231. CRISC by Isaca Actual Free Exam Q & As, Question 8. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 231. CRISC Certified in Risk and Information Systems Control – Question231.
Which of the following is the MOST important reason for integrating IT risk management practices into enterprise risk management (ERM)?
To reduce conflicts of interest between IT and business units
To align ERM with regulatory requirements
To optimize enterprise-wide resource efficiency
To ensure IT risk scenarios are reflected in the corporate risk profile
IT risk is a subset of enterprise risk. Integration ensures IT risks arevisible and prioritizedalongside strategic and operational risks.
CRISC framework explains:
“Integration of IT risk management with ERM ensures that technology-related risks are appropriately represented in the overall corporate risk profile and reporting structure.”
Hence,Dis correct.
CRISC Reference:Domain 1 – IT Risk Governance, Topic: Enterprise and IT Risk Integration.
The PRIMARY benefit of selecting an appropriate set of key risk indicators (KRIs) is that they:
serve as a basis for measuring risk appetite.
align with the organization ' s risk profile.
provide a warning of emerging high-risk conditions.
provide data for updating the risk register.
According to the ISACA Risk and Information Systems Control study guide and handbook, the primary benefit of selecting an appropriate set of key risk indicators (KRIs) is that they provide a warning of emerging high-risk conditions. KRIs are metrics that monitor changes in the level of risk exposure and contribute to the early warning signs that enable organizations to report risks, prevent crises, and mitigate them in time. KRIs help risk managers to identify potential threats, assess their impact and likelihood, and take proactive measures to reduce the risk or seize the opportunity12
1: ISACA Risk and Information Systems Control Study Guide, 4th Edition, page 33 2: ISACA Risk and Information Systems Control Handbook, 1st Edition, page 25
Which of the following is the FIRST step when identifying risk items related to a new IT project?
Conduct a cost-benefit analysis.
Review the IT control environment.
Review the business case.
Conduct a gap analysis.
Which of the following changes would be reflected in an organization ' s risk profile after the failure of a critical patch implementation?
Risk tolerance is decreased.
Residual risk is increased.
Inherent risk is increased.
Risk appetite is decreased
A critical patch is a software update that fixes a security vulnerability or a bug that may affect the performance, functionality, or reliability of a system or a network. A critical patch implementation is a process that applies the software update to the system or network in a timely and effective manner. The failure of a critical patch implementation is a situation where the software update is not applied or not applied correctly, which may expose the system or networkto various threats, such as data theft, data corruption, data leakage, or denial of service. The failure of a critical patch implementation would be reflected in an organization’s risk profile by increasing the residual risk. Residual risk is the risk that remains after the risk response, which means the risk that is not avoided, transferred, or mitigated by the existing controls or measures. The failure of a critical patch implementation would increase the residual risk, as it would reduce the effectiveness or efficiency of the existing controls or measures that are supposed to address the security vulnerability or the bug. The failure of a critical patch implementation would also increase the likelihood or impact of the potential threats, as well as the exposure or consequences of the system or network. The other options are not the correct changes that would be reflected in an organization’s risk profile after the failure of a critical patch implementation, although they may be affected or related. Risk tolerance is the degree of variation from the risk appetite that the organization is not willing to accept. Risk tolerance may be decreased by the failure of a critical patch implementation, as the organization may become more cautious or conservative in accepting the risk, but it is not a direct or immediate change in the risk profile. Inherent risk is the risk that exists in the absence of any controls or measures, which means the risk that is inherent to the system or network or the environment. Inherent risk may be increased by the failure of a critical patch implementation, as the system or network may become more vulnerable or susceptible to the threats, but it is not a change in the risk profile, as the risk profile considers the existing controls or measures. Risk appetite is the amount and type of risk that the organization is willing to accept in pursuit of its objectives. Risk appetite may be decreasedby the failure of a critical patch implementation, as the organization may become less willing orable to accept the risk, but it is not a change in the risk profile, as the risk profile reflects the actual or current risk level, not the desired or expected risk level. References = CRISC Review Manual, pages 32-331; CRISC Review Questions, Answers & Explanations Manual, page 972; What is a Critical Patch? - Definition from Techopedia3; What is Residual Risk? - Definition from Techopedia4
During a recent security framework review, it was discovered that the marketing department implemented a non-fungible token asset program. This was done without following established risk procedures. Which of the following should the risk practitioner do FIRST?
Report the infraction.
Perform a risk assessment.
Conduct risk awareness training.
Discontinue the process.
Perform a Risk Assessment:
Immediate Action: The first step when discovering a non-compliant implementation is to understand the potential risks it poses to the organization. This involves identifying threats, vulnerabilities, and potential impacts of the non-fungible token (NFT) asset program.
Risk Identification and Evaluation: Assess the new program’s impact on the organization’s risk profile. Determine if it introduces significant security, compliance, or operational risks.
Documentation and Reporting: Document the findings and present them to senior management along with recommendations for mitigation or further action.
Comparison with Other Options:
Report the Infraction: Reporting is necessary but should follow the risk assessment to provide a clear understanding of the implications and necessary mitigations.
Conduct Risk Awareness Training: Training is preventive and should be part of a long-term strategy, not the immediate response to a specific incident.
Discontinue the Process: Discontinuing the process may be a necessary step after assessing the risk, but the assessment must come first to justify such an action.
Best Practices:
Comprehensive Risk Assessment: Ensure that the risk assessment covers all aspects, including financial, reputational, and regulatory risks.
Stakeholder Involvement: Involve relevant stakeholders in the assessment process to gather diverse perspectives and ensure a thorough evaluation.
Actionable Recommendations: Provide clear, actionable recommendations based on the risk assessment findings.
Which of the following BEST enables an organization to determine whether external emerging risk factors will impact the organization ' s risk profile?
Control identification and mitigation
Adoption of a compliance-based approach
Prevention and detection techniques
Scenario analysis and stress testing
Scenario analysis and stress testing are the best methods to enable an organization to determine whether external emerging risk factors will impact the organization’s risk profile, as they help to simulate and evaluate the potential outcomes and effects of various risk events and scenarios on the enterprise’s objectives and operations. Scenario analysis and stress testing can help to identify and assess the impact of external emerging risk factors, such as changes in the market, technology, regulation, or environment, and to measure the resilience and preparedness oftheenterprise to cope with these factors. Control identification and mitigation, adoption of a compliance-based approach, and prevention and detection techniques are not the best methods to enable an organization to determine whether external emerging risk factors will impact the organization’s risk profile, as they do not help to simulate and evaluate the potential outcomes and effects of various risk events and scenarios, but rather to manage and monitor the existing or known risks. References = CRISC: Certified in Risk & Information Systems Control Sample Questions, question 223.
An organization is outsourcing a key database to be hosted by an external service provider. Who is BEST suited to assess the impact of potential data loss?
Database manager
Public relations manager
Data privacy manager
Business manager
The business manager is best suited to assess the impact of potential data loss when outsourcing a key database to an external service provider.
Role of the Business Manager:
Understanding Business Impact:The business manager has a comprehensive understanding of the business processes, the criticality of the data, and the potential impact of data loss on business operations.
Decision Making:They are responsible for making decisions regarding risk tolerance, business continuity, and aligning the risk management practices with business objectives.
Assessment of Data Loss Impact:
Operational Impact:The business manager can evaluate how data loss would affect day-to-day operations and overall business continuity.
Financial and Reputational Impact:They can also assess the financial repercussions and potential damage to the organization’s reputation, providing a holistic view of the impact.
Which of the following would BEST help identify the owner for each risk scenario in a risk register?
Determining which departments contribute most to risk
Allocating responsibility for risk factors equally to asset owners
Mapping identified risk factors to specific business processes
Determining resource dependency of assets
A risk register is a tool that records and tracks the identified risks, their causes, impacts, likelihood, responses, and owners. The owner for each risk scenario is the person or group whohas the authority and accountability to manage the risk and its response. The best way to identify the owner for each risk scenario in a risk register is to map the identified risk factors tospecific business processes. Risk factors are the internal and external variables that influence the occurrence and impact of risks. Business processes are the activities that produce value for the enterprise, such as sales, marketing, production, or delivery. By mapping the risk factors to the business processes, the risk practitioner can determine which business process is affected by or contributes to the risk, and who is responsible for the business process. The owner for each risk scenario should be the person or group who is responsible for the business process that is associated with the risk. The other options are not the best way to identify the owner for each risk scenario, as they involve different criteria or methods:
Determining which departments contribute most to risk means that the risk practitioner evaluates the degree of involvement or exposure of each department to the risk. This may not be a reliable or consistent way to identify the owner for each risk scenario, as the risk may span across multiple departments, or the department may not have the authority or accountability to manage the risk.
Allocating responsibility for risk factors equally to asset owners means that the risk practitioner assigns the same level of responsibility to each person or group who owns an asset that is affected by or contributes to the risk. An asset is a resource that has value for the enterprise, such as hardware, software, data, or people. This may not be a fair or effective way to identify the owner for each risk scenario, as the asset owners may have different levels of involvement or exposure to the risk, or may not have the authority or accountability to manage the risk.
Determining resource dependency of assets means that the risk practitioner analyzes the relationship and interdependence of the assets that are affected by or contribute to the risk. This may help to identify the potential impact or likelihood of the risk, but it does not directly help to identify the owner for each risk scenario, as the resource dependency may not reflect the authority or accountability to manage the risk. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1.1, pp. 95-96.
Who is ULTIMATELY accountable for the confidentiality of data in the event of a data breach within a Software as a Service (SaaS) environment?
Vendor ' s information security officer
Customer ' s data privacy officer
Customer ' s data owner
Vendor ' s application owner
In a SaaS model, while the provider manages the infrastructure and application,data ownership and ultimate responsibilityfor its confidentiality remains with thecustomer ' s data owner, including due diligence and contractual safeguards.
Which of the following would be the GREATEST concern for an IT risk practitioner when an employees.....
The organization ' s structure has not been updated
Unnecessary access permissions have not been removed.
Company equipment has not been retained by IT
Job knowledge was not transferred to employees m the former department
The greatest concern for an IT risk practitioner when an employee transfers to another department is that unnecessary access permissions have not been removed. Unnecessary access permissions are the access rights or privileges that are no longer needed, relevant, or appropriate for the employee’s new role or responsibility. If these access permissions are not removed, they may pose a significant security risk, as the employee may be able to access, modify, or delete sensitive or critical data and systems that are not related to their current function. This may result in data leakage, fraud, sabotage, or compliance violations. The other options are not as concerning as unnecessary access permissions, as they are related to the organizational, operational, or knowledge aspects of the employee transfer, not the security or risk aspects of the employee transfer. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
Which of the following activities should only be performed by the third line of defense?
Operating controls for risk mitigation
Testing the effectiveness and efficiency of internal controls
Providing assurance on risk management processes
Recommending risk treatment options
Providing assurance on risk management processes is the activity that should only be performed by the third line of defense, because it is the role and responsibility of the independent andobjective assurance function, such as internal audit or external audit, to evaluate and report on the effectiveness and efficiency of the risk management processes and controls. The third line of defense is the last layer of the three lines of defense model, which is a framework that defines the roles and responsibilities of different functions and levels within the organization for risk management and control. The first line of defense is the operational management and staff, who are responsible for identifying, assessing, and managing the risks and controls within their areas of responsibility. The second line of defense is the oversight and support functions, such as risk management, compliance, or legal, who are responsible for establishing and monitoring the risk policies, standards, and frameworks, and providing guidance and advice to the first line of defense. The third line of defense is the assurance function, who are responsible for providing independent and objective assurance on the adequacy and effectiveness of the risk management processes and controls, and reporting to the senior management and the board of directors. Operating controls for risk mitigation, testing the effectiveness and efficiency of internal controls, and recommending risk treatment options are all activities that can be performed by the first or second line of defense, but not by the third line of defense, as they are not part of the assurance function. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.4.1, page 59
Which of the following would be MOST important for a risk practitioner to provide to the internal audit department during the audit planning process?
Closed management action plans from the previous audit
Annual risk assessment results
An updated vulnerability management report
A list of identified generic risk scenarios
The audit planning process is the process of defining and describing the scope, objectives, and approach of the internal audit that is performed to assess and evaluate the adequacy and effectiveness of the organization’s governance, risk management, and control functions. The audit planning process involves identifying and prioritizing the audit areas, topics, or issues, and allocating the audit resources, time, and budget.
The most important information for a risk practitioner to provide to the internal audit department during the audit planning process is the annual risk assessment results, which are the outcomes or outputs of the risk assessment process that measures and compares the likelihood and impact of various risk scenarios, and prioritizes them based on their significance and urgency. The annual risk assessment results can help the internal audit department to plan the audit by providing the following information:
The level and priority of the risks that may affect the organization’s objectives and operations, and the potential consequences or impacts that they may cause for the organization if they materialize.
The gap or difference between the current and desired level of risk, and the extent or degree to which the risk responses or controls contribute to or affect the gap or difference.
The cost-benefit or feasibility analysis of the possible actions or plans to address or correct the risks and their responses, and the expected or desired outcomes or benefits that they may provide for the organization.
The other options are not the most important information for a risk practitioner to provide to the internal audit department during the audit planning process, because they do not provide the same level of detail and insight that the annual risk assessment results provide, and they may not be relevant or actionable for the internal audit department.
Closed management action plans from the previous audit are the actions or plans that have been implemented or completed by the management to address or correct the findings or recommendations from the previous internal audit that was performed. Closed management action plans from the previous audit can provide useful information on the progress and performance of the management in improving and optimizing the organization’s governance, risk management, and control functions, but they are not the most important information for a risk practitioner to provide to the internal audit department during the audit planning process, because they do not indicate the current or accurate state and performance of the organization’s risk profile, and they may not cover all the relevant or emerging risks that may exist or arise.
An updated vulnerability management report is a report that provides the information and status of the vulnerabilities or weaknesses in the organization’s assets, processes, or systems that can be exploited or compromised by the threats or sources of harm that may affect the organization’s objectives or operations. An updated vulnerability management report can provide useful information on the existence and severity of the vulnerabilities, and the actions or plans to mitigate or prevent them, but it is not the most important information for a risk practitioner to provide to the internal audit department during the audit planning process, because it does not indicate the likelihood and impact of the risk scenarios that are associated with the vulnerabilities, and the potential consequences or impacts that they may cause for the organization.
A list of identified generic risk scenarios is a list that contains the descriptions or representations of the possible or hypothetical situations or events that may cause or result in a risk for the organization, without specifying the details or characteristics of the risk source, event, cause, orimpact. A list of identified generic risk scenarios can provide useful information on the types or categories of the risks that may affect the organization, but it is not the most important information for a risk practitioner to provide to the internal audit department during the audit planning process, because it does not indicate the level and priority of the risks, and the potential consequences or impacts that they may cause for the organization. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 188
CRISC Practice Quiz and Exam Prep
Ensure compliance with local legislation because it has a higher priority.
Conduct a risk assessment and develop mitigation options.
Terminate the current cloud contract and migrate to a local cloud provider.
Accept the risk because foreign legislation does not apply to the organization.
When regulatory conflicts arise, the best practice is to conduct a comprehensive risk assessment to understand the impact and develop appropriate mitigation strategies. Immediate termination may be premature without understanding options, and accepting risk without assessment may expose the organization to legal or compliance issues. Prioritizing compliance requires understanding the full scope of risks and controls necessary【5:35, 5:48†CRISC_SentenceinNOTE30.pptx】.
An organization has opened a subsidiary in a foreign country. Which of the following would be the BEST way to measure the effectiveness of the subsidiary ' s IT systems controls?
Implement IT systems in alignment with business objectives.
Review metrics and key performance indicators (KPIs).
Review design documentation of IT systems.
Evaluate compliance with legal and regulatory requirements.
The best way to measure the effectiveness of the subsidiary’s IT systems controls is to review metrics and key performance indicators (KPIs), as they provide quantitative and qualitative measures of the performance and outcomes of the IT systems and processes, and how well they meet the predefined standards and expectations. Metrics and KPIs can help to evaluate the efficiency, reliability, security, and quality of the IT systems and controls, and to identify any gaps, weaknesses, or issues that need to be addressed. Metrics and KPIs can also help to compare and benchmark the subsidiary’s IT systems and controls with those of the parent organization or other similar entities. The other options are not the best ways to measure the effectiveness of the subsidiary’s IT systems controls, although they may be useful or complementary methods. Implementing IT systems in alignment with business objectives is a good practice, but it does not measure the effectiveness of the IT systems controls, as it focuses on the alignment andintegration of the IT systems with the business strategy and goals. Reviewing design documentation of IT systems can provide some information on the specifications and requirements of the IT systems, but it does not measure the effectiveness of the IT systems controls, as it does not reflect the actual implementation and operation of the IT systems. Evaluating compliance with legal and regulatory requirements can ensure that the subsidiary’s IT systems and controls meet the minimum standards and obligations of the foreign country, but it does not measure the effectiveness of the IT systems controls, as it does not consider the performance and outcomes of the IT systems and processes. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk and Control Monitoring and Reporting, page 187.
Which of the following is the MOST efficient method for monitoring control effectiveness?
Conduct control self-assessments (CSAs)
Review system performance logs
Compare controls to business metrics
Perform independent periodic control testing
Control Self-Assessments (CSAs)provide an efficient way for process owners and staff to assess control effectiveness continuously. ISACA recognizes CSAs as a proactive approach that encourages accountability and early detection of control weaknesses, reducing the need for frequent external testing.
===========
A business impact analysis (BIA) enables an organization to determine appropriate IT risk mitigation actions by:
validating whether critical IT risk has been addressed.
assigning accountability for IT risk to business functions.
identifying IT assets that support key business processes.
defining the requirements for an IT risk-aware culture
Business Impact Analysis (BIA):
Objective: The primary objective of a BIA is to identify and evaluate the effects of disruptions on business operations. This includes determining the criticality of IT assets that support key business processes.
Risk Mitigation: By identifying critical IT assets, organizations can prioritize risk mitigation efforts to ensure that key business processes remain operational during and after disruptions.
Appropriate IT Risk Mitigation:
Critical Asset Identification: Knowing which IT assets are essential allows for targeted risk mitigation strategies. This ensures resources are allocated efficiently to protect the most important systems.
Impact Assessment: Understanding the impact of potential disruptions on critical IT assets helps in developing effective disaster recovery and continuity plans.
Comparison with Other Options:
Validating Critical IT Risk: While important, this is typically part of a broader BIA process rather than its primary objective.
Assigning Accountability for IT Risk: This is crucial for governance but does not directly enable risk mitigation actions.
Defining IT Risk-aware Culture: Important for overall risk management but does not directly influence specific mitigation actions.
Best Practices:
Detailed Asset Inventory: Maintain an up-to-date inventory of IT assets and their dependencies on business processes.
Regular Updates and Reviews: Continuously update the BIA to reflect changes in the IT environment and business processes.
Which of the following is a drawback in the use of quantitative risk analysis?
It assigns numeric values to exposures of assets.
It requires more resources than other methods
It produces the results in numeric form.
It is based on impact analysis of information assets.
The drawback in the use of quantitative risk analysis is that it requires more resources than other methods. Quantitative risk analysis is a method of risk analysis that assigns numeric values to the exposures of assets, the impact and likelihood of risk events, and the cost and benefit of risk responses. Quantitative risk analysis can provide more precise and objective results, and support the risk-based decision making process. However, quantitative risk analysis also requires more resources than other methods, such as data, time, expertise, and tools, to collect, validate, and analyze the quantitative information, and to perform the complex calculations and simulations. Quantitative risk analysis may also be limited by the availability, reliability, and accuracy of thedata, and the assumptions and models used. Assigning numeric values to exposures of assets, producing the results in numeric form, and being based on impact analysis of information assets are not drawbacks, but characteristics of quantitative risk analysis. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 49.
The BEST key performance indicator (KPI) for monitoring adherence to an organization ' s user accounts provisioning practices is the percentage of:
accounts without documented approval
user accounts with default passwords
active accounts belonging to former personnel
accounts with dormant activity.
User accounts provisioning is the process of creating, managing, and modifying user accounts within a system or an application, based on the user’s roles, responsibilities, and requirements. User accounts provisioning is an essential part of identity and access management (IAM), which aims to ensure the confidentiality, integrity, and availability of the system or the application, and the information or resources that it handles or supports1.
The best key performance indicator (KPI) for monitoring adherence to an organization’s user accounts provisioning practices is the percentage of accounts without documented approval, because it can help to measure how well the organization follows the policies, standards, and procedures for user accounts provisioning, and how effectively the organization controls andaudits the user accounts provisioning activities. The percentage of accounts without documented approval can indicate:
The level of compliance and accountability of the user accounts provisioning process, and the extent to which the user accounts provisioning requests and actions are authorized and verified by the appropriate parties, such as managers, IT staff, or security officers
The level of risk and exposure of the user accounts provisioning process, and the likelihood and impact of unauthorized or inappropriate user accounts provisioning, such as granting excessive or unnecessary access privileges, creating duplicate or fraudulent accounts, or violating legal or regulatory requirements
The level of quality and efficiency of the user accounts provisioning process, and the ability and capacity of the organization to manage and maintain the user accounts provisioning records and documents, such as forms, logs, or reports23
The other options are not the best KPIs for monitoring adherence to an organization’s user accounts provisioning practices, but rather some of the factors or outcomes of it. User accountswith default passwords are user accounts that have not changed their passwords from the initial or default values that are assigned by the system or the application. User accounts with default passwords are a factor that can increase the risk of unauthorized or malicious access to the system or the application, as the default passwords may be easily guessed or compromised by attackers. Active accounts belonging to former personnel are user accounts that have not been deactivated or deleted after the users have left the organization. Active accounts belonging to former personnel are an outcome of ineffective or inefficient user accounts deprovisioning, which is the process of revoking or removing the user accounts and access privileges when they are no longer needed or valid. Accounts with dormant activity are user accounts that have not been used or accessed for a long period of time. Accounts with dormant activity are an outcome of poor or inconsistent user accounts management, which is the process of updating or modifying the user accounts and access privileges according to the changes or needs of the users or the organization4. References =
User Provisioning for SaaS Apps: Top 10 Best Practices | Resmo
Top Identity and Access Management Metrics
KPI-driven approach to Identity & Access Management - Elimity
[CRISC Review Manual, 7th Edition]
Which of the following has the MOST validity for conducting risk assessments?
Internal control effectiveness measured through inference from external assessment
Control effectiveness determined through subject matter expertise estimation
Inferences of internal control effectiveness from peer reports
Internal control effectiveness measured through direct testing
The correct answer isDbecauseinternal control effectiveness measured through direct testingprovides the most valid basis for conducting risk assessments. Direct testing produces objective evidence about whether controls are designed appropriately and operating effectively. It is stronger and more reliable than estimates, external inference, or peer-based assumptions because it evaluates the actual control environment of the organization.
The other options are less valid:
A. Internal control effectiveness measured through inference from external assessmentmay provide useful insight, but it is indirect and may not reflect the organization’s actual internal control performance.
B. Control effectiveness determined through subject matter expertise estimationcan support assessment, but it remains judgment-based rather than evidence-based.
C. Inferences of internal control effectiveness from peer reportsare indirect and may not be relevant to the organization’s own environment, systems, or risk exposure.
Exact Extracts supporting the answer:
“To best identify information systems control deficiencies gap analysis is used. It highlights the discrepancies between desired control objectives and actual control design and operational effectiveness.”
“The MOST important criterion when reviewing information security controls is ensuring that the controls are effectively addressing risk.”
“The BEST way to ensure that an information systems control is appropriate and effective is to verify that the risk associated with the control is mitigated.”
“To determine control effectiveness it ' s essential to verify that the control meets the test results of intended objectives.”
“Testing the control to ensure that the risk has been adequately mitigated is the best action to take once a new control has been implemented validating that the control effectively addresses the identified risk.”
These extracts support that the most valid evidence of control effectiveness comes from actual verification and testing, not from assumptions or indirect sources. Therefore,direct testingprovides the strongest validity for risk assessments.
===========
Which of the following is MOST helpful in identifying new risk exposures due to changes in the business environment?
Standard operating procedures
SWOT analysis
Industry benchmarking
Control gap analysis
New risk exposures due to changes in the business environment are the possibilities and impacts of new or emerging threats or opportunities that may affect the organization’s objectives, performance, or value creation, as a result of changes in the internal or external factors that influence the organization’s operations, such as technology, competition, regulation, or customer behavior12.
The most helpful tool in identifying new risk exposures due to changes in the business environment is a SWOT analysis, which is a technique that involves identifying and analyzing the strengths, weaknesses, opportunities, and threats (SWOT) that are relevant to the organization’s situation, goals, and capabilities34.
A SWOT analysis is the most helpful tool because it helps the organization to scan and assess the business environment, and to identify and prioritize the new or emerging risk exposures that may arise from the changes in the environment34.
A SWOT analysis is also the most helpful tool because it helps the organization to align and adapt its strategy and actions to the changes in the environment, and to leverage its strengths and opportunities, and mitigate its weaknesses and threats34.
The other options are not the most helpful tools, but rather possible sources or inputs that may be used in a SWOT analysis. For example:
Standard operating procedures are documents that describe the routine tasks and processes that are performed by the organization, and the policies and standards that govern them56. However, these documents are not the most helpful tools because they may not reflect or capture the changes in the business environment, and they may need to be revised or updated to address the new or emerging risk exposures56.
Industry benchmarking is a technique that involves comparing and contrasting the performance and practices of the organization with those of the similar or leadingorganizations in the same or related industry, and identifying the gaps or opportunities for improvement78. However, this technique is not the most helpful tool because it may not provide a comprehensive or holistic view of the business environment, and it may not align with the organization’s specific situation, goals, or capabilities78.
Control gap analysis is a technique that involves assessing and evaluating the adequacy and effectiveness of the controls that are designed and implemented to mitigate the risks, and identifying and addressing the areas or aspects that need to be improved or added . However, this technique is not the most helpful tool because it is reactive rather than proactive, and it may not identify or anticipate the new or emerging risk exposures that may result from the changes in the business environment . References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
3: SWOT Analysis - ISACA1
4: SWOT Analysis: What It Is and When to Use It2
5: Standard Operating Procedure - Wikipedia3
6: How to Write Effective Standard Operating Procedures (SOP)4
7: Benchmarking - Wikipedia5
8: Benchmarking: Definition, Types, Process, Advantages & Examples6
Control Gap Analysis - ISACA7
Control Gap Analysis: A Step-by-Step Guide8
Which of the following is the PRIMARY reason to adopt key control indicators (KCIs) in the risk monitoring and reporting process?
To provide data for establishing the risk profile
To provide assurance of adherence to risk management policies
To provide measurements on the potential for risk to occur
To provide assessments of mitigation effectiveness
Key control indicators (KCIs) are metrics that measure the performance and effectiveness of the controls that are implemented to mitigate the risks. KCIs can help to monitor the status and health of the controls, as well as to identify any issues or gaps that need to be addressed. The primary reason to adopt KCIs in the risk monitoring and reporting process is to provideassessments of mitigation effectiveness, meaning that they can help to evaluate how well the controls are reducing the risk exposure and achieving the desired outcomes. KCIs can also help to support the risk management decision making and improvement actions, as well as to demonstrate the value and benefits of the controls. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.1.2, p. 115-116
An organization recently implemented a cybersecurity awareness program that includes phishing simul-ation exercises for all employees. What type of control is being utilized?
Deterrent
Preventive
Compensating
Detective
Phishing simulation exercises are designed to educate users and reduce the likelihood of them falling for real phishing attacks. This is considered apreventive control, as it aims to stop incidents before they occur by changing behavior.
Which of the following BEST enables an organization to address risk associated with technical complexity?
Documenting system hardening requirements
Minimizing dependency on technology
Aligning with a security architecture
Establishing configuration guidelines
Addressing Technical Complexity:
Security Architecture Alignment: Aligning with a security architecture helps manage the complexity by providing a structured framework for implementing and managing security controls.
Comprehensive Framework: A security architecture ensures that all security controls are integrated and aligned with the organization’s overall security strategy, reducing the risk associated with technical complexity.
Steps Involved:
Develop or Adopt a Security Architecture: Use established frameworks such as SABSA, TOGAF, or Zachman.
Implementation: Apply the security architecture across all systems and processes to ensure consistency and integration.
Monitoring and Maintenance: Continuously monitor the security architecture and update it as necessary to address new threats and technologies.
Comparison with Other Options:
Documenting System Hardening Requirements: Important but does not address the overall complexity.
Minimizing Dependency on Technology: Not always feasible and does not fully address the inherent complexity.
Establishing Configuration Guidelines: Helpful but should be part of the broader security architecture.
Best Practices:
Continuous Improvement: Regularly update and improve the security architecture to adapt to evolving threats and technologies.
Training and Awareness: Ensure that all relevant personnel understand the security architecture and their role in maintaining it.
A PRIMARY function of the risk register is to provide supporting information for the development of an organization ' s risk:
strategy.
profile.
process.
map.
A primary function of the risk register is to provide supporting information for the development of an organization’s risk profile, which is a comprehensive and structured representation of therisks that the organization faces. The risk profile helps the organization to understand its risk exposure, appetite, and tolerance, and to align its risk management strategy with its business objectives and context. The risk register is a document that records and tracks the identified risks, their causes, impacts, likelihood, responses, owners, and status. The risk register is anessential input for creating and updating the risk profile, as it provides the data and analysis of the risks that need to be prioritized and addressed. The other options are not the primary function of the risk register, although they may be related to it. The risk strategy is the plan and approach for managing the risks, and it is based on the risk profile. The risk process is the set of activities and tasks for identifying, assessing, responding, and monitoring the risks, and it is facilitated by the risk register. The risk map is a graphical tool for displaying the risks based on their impact and likelihood, and it is derived from the risk register. References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana; Purpose of a risk register: Here’s what a risk register is used for; Risk Register: Definition, Importance, and Elements! - Bit Blog; What is a Risk Register? A Complete Guide | Capterra; Risk Registers: What Are They, When Should You Use Them, and Why?
Which of the following is of GREATEST concern when uncontrolled changes are made to the control environment?
A decrease in control layering effectiveness
An increase in inherent risk
An increase in control vulnerabilities
An increase in the level of residual risk
The control environment is the set of internal and external factors and conditions that influence and shape the organization’s governance, risk management, and control functions. It includes the organization’s culture, values, ethics, structure, roles, responsibilities, policies, standards, etc.
Uncontrolled changes are changes or modifications to the control environment that are not planned, authorized, documented, or monitored, and that may have unintended or adverse consequences for the organization. Uncontrolled changes may be caused by various drivers or events, such as technological innovations, market trends, regulatory changes, customer preferences, competitor actions, environmental issues, etc.
The greatest concern when uncontrolled changes are made to the control environment is an increase in the level of residual risk, which is the amount and type of risk that remains after the implementation and execution of the risk responses or controls. An increase in the level of residual risk means that the risk responses or controls are not effective or sufficient to mitigate or prevent the risks, and that the organization may face unacceptable or intolerable consequences if the risks materialize.
An increase in the level of residual risk is the greatest concern when uncontrolled changes are made to the control environment, because it indicates that the organization’s risk profile and performance have deteriorated, and that the organization may not be able to achieve its objectives or protect its value. It also indicates that the organization’s risk appetite and tolerance have been violated, and that the organization may need to take corrective or compensating actions to restore the balance between risk and return.
The other options are not the greatest concerns when uncontrolled changes are made to the control environment, because they do not indicate the actual or potential impact or outcome of the risks, and they may not be relevant or actionable for the organization.
A decrease in control layering effectiveness means a decrease in the extent or degree to which the organization uses multiple or overlapping controls to address the same or related risks, and to provide redundancy or backup in case of failure or compromise of one or more controls. A decrease in control layering effectiveness may indicate a weakness or gap in the organization’s control design or implementation, but it does not indicate the actual or potential impact oroutcome of the risks, and it may not be relevant or actionable for the organization, unless the control layering is required or recommended by the organization’s policies or standards.
An increase in inherent risk means an increase in the amount and type of risk that exists in the absence of any risk responses or controls, and that is inherent to the nature or characteristics of the risk source, event, cause, or impact. An increase in inherent risk may indicate a change or variation in the organization’s risk exposure or level, but it does not indicate the actual or potential impact or outcome of the risks, and it may not be relevant or actionable for the organization, unless the inherent risk exceeds the organization’s risk appetite or tolerance.
An increase in control vulnerabilities means an increase in the number or severity of the weaknesses or flaws in the organization’s risk responses or controls that can be exploited or compromised by the threats or sources of harm that may affect the organization’s objectives or operations. An increase in control vulnerabilities may indicate a weakness or gap in the organization’s control design or implementation, but it does not indicate the actual or potential impact or outcome of the risks, and it may not be relevant or actionable for the organization, unless the control vulnerabilities are exploited or compromised by the threats or sources of harm. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 174
CRISC Practice Quiz and Exam Prep
An organization has established a single enterprise-wide risk register that records high-level risk scenarios. The IT risk department has created its own register to record more granular scenarios applicable to IT. Which of the following is the BEST way to ensure alignment between these two registers?
Map the granular risk scenarios to the high-level risk register items.
List application and server vulnerabilities in the IT risk register.
Identify overlapping risk scenarios between the two registers.
Maintain both high-level and granular risk scenarios in a single register.
Mapping granular scenarios to high-level register items ensures consistency and alignment across different levels of risk management. This approach supportsIntegrated Risk Management Frameworks.
Which stakeholders are PRIMARILY responsible for determining enterprise IT risk appetite?
Audit and compliance management
The chief information officer (CIO) and the chief financial officer (CFO)
Enterprise risk management and business process owners
Executive management and the board of directors
The stakeholders who are PRIMARILY responsible for determining enterprise IT risk appetite are the executive management and the board of directors, because they are the ones who set thestrategic direction and objectives of the enterprise, and who define the acceptable level of risk exposure and tolerance for achieving those objectives. The other options are not the primary stakeholders, because:
Option A: Audit and compliance management are responsible for providing assurance and oversight on the effectiveness of the risk management process and the compliance with internal and external requirements, but they do not determine the enterprise IT risk appetite.
Option B: The CIO and the CFO are responsible for managing the IT resources and the financial resources of the enterprise, respectively, but they do not determine the enterprise IT risk appetite.
Option C: Enterprise risk management and business process owners are responsible for identifying, assessing, and responding to the risks that affect their domains, but they do not determine the enterprise IT risk appetite. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 83.
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor ' s control environment?
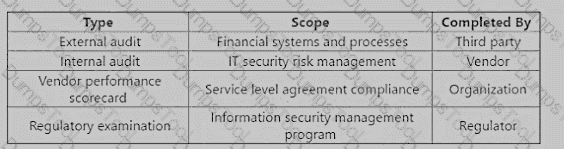
External audit
Internal audit
Vendor performance scorecard
Regulatory examination
An external audit is the most reliable input to evaluate residual risk in the vendor’s control environment, as it provides an independent and objective assessment of the vendor’s financial systems and processes. An external audit is conducted by a third party, such as a certified public accountant (CPA) or a professional auditing firm, that follows the generally accepted auditing standards (GAAS) and the generally accepted accounting principles (GAAP). An external audit can help to verify the accuracy and completeness of the vendor’s financial statements, identify any material misstatements or errors, and evaluate the effectiveness and efficiency of the vendor’s internal controls. An external audit can also provide assurance and confidence to the organization and other stakeholders that the vendor is complying with the relevant laws, regulations, and contractual obligations.
The other options are not the most reliable inputs to evaluate residual risk in the vendor’s control environment. An internal audit is conducted by the vendor itself, which may introduce bias or conflict of interest. An internal audit may also have a different scope, methodology, or quality than an external audit. A vendor performance scorecard is completed by the organization, which may not have the sufficient access, expertise, or authority to assess the vendor’s control environment. A vendor performance scorecard may also focus more on the service level agreement (SLA) compliance, rather than the financial systems and processes. A regulatory examination is conducted by a regulator, such as a government agency or a standard-settingbody, which may have a different purpose, criteria, or perspective than the organization. A regulatory examination may also have a limited scope, frequency, or transparency. References = Guide to VendorRisk Assessment | Smartsheet, Understanding Inherent Vs. Residual Risk Assessments - Resolver, Assessing Internal Controls over Compliance - HCCA Official Site
Which of the following methods would BEST contribute to identifying obscure risk scenarios?
Brainstorming sessions
Control self-assessments
Vulnerability analysis
Monte Carlo analysis
Brainstorming sessions would best contribute to identifying obscure risk scenarios, as they allow participants to generate and share ideas without being constrained by conventional thinking or assumptions. Brainstorming sessions can help to identify risks that are not obvious, not well understood, or not covered by existing controls. Control self-assessments, vulnerability analysis, and Monte Carlo analysis are useful methods for evaluating and quantifying risks, but they are not designed to identify obscure risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 59.
Which of the following would provide the MOST objective assessment of the effectiveness of an organization ' s security controls?
An internal audit
Security operations center review
Internal penetration testing
A third-party audit
According to the CRISC Review Manual1, a third-party audit is an independent and objective examination of an organization’s security controls by an external auditor or organization. A third-party audit provides the most objective assessment of the effectiveness of an organization’s security controls, as it helps to avoid any conflicts of interest, biases, or assumptions that may affect the internal audit, review, or testing. A third-party audit also helps to ensure that the security controls comply with the relevant standards, regulations, and best practices, and that they meet the expectations and requirements of the stakeholders, such as customers, partners, or regulators. References = CRISC Review Manual1, page 224.
Which of the following BEST helps to identify significant events that could impact an organization?
Vulnerability analysis
Control analysis
Scenario analysis
Heat map analysis
Which of the following is the PRIMARY objective of maintaining an information asset inventory?
To provide input to business impact analyses (BIAs)
To protect information assets
To facilitate risk assessments
To manage information asset licensing
An information asset inventory is a list of all the information assets that an organization owns or uses. It includes information such as the asset name, description, owner, location, classification,value, and dependencies. The primary objective of maintaining an information asset inventory is to provide input to business impact analyses (BIAs), which are used to identify the criticality and recovery priorities of information assets in the event of a disruption. By having an updated and accurate information asset inventory, an organization can ensure that the BIAs reflect the current state and needs of the business processes that rely on the information assets. References = CRISC Review Manual, 7th Edition, page 74.
A risk practitioner notices a trend of noncompliance with an IT-related control. Which of the following would BEST assist in making a recommendation to management?
Assessing the degree to which the control hinders business objectives
Reviewing the IT policy with the risk owner
Reviewing the roles and responsibilities of control process owners
Assessing noncompliance with control best practices
A risk practitioner notices a trend of noncompliance with an IT-related control. This indicates that there is a risk of ineffective or inefficient implementation or operation of the control, which may expose the organization to potential threats or losses.
The best way to assist in making a recommendation to management is to assess the degree to which the control hinders business objectives. This means that the risk practitioner should analyze the impact of the control on the performance, productivity, quality, or customer satisfaction of the business processes or functions that are affected by the control.
Assessing the degree to which the control hinders business objectives helps to identify the root causes of noncompliance, the costs and benefits of compliance, and the potential alternatives or improvements for the control. It also helps to communicate the value and importance of the control to the management and the stakeholders, and to obtain their support and commitment for the control compliance.
The other options are not the best ways to assist in making a recommendation to management. They are either secondary or not essential for control compliance.
The references for this answer are:
Risk IT Framework, page 19
Information Technology & Security, page 13
Risk Scenarios Starter Pack, page 11
An organization is increasingly concerned about loss of sensitive data and asks the risk practitioner to assess the current risk level. Which of the following should the risk practitioner do FIRST?
Identify staff members who have access to the organization ' s sensitive data.
Identify locations where the organization ' s sensitive data is stored.
Identify risk scenarios and owners associated with possible data loss vectors.
Identify existing data loss controls and their levels of effectiveness.
The first step in assessing the current risk level of data loss is to identify where the sensitive data is stored, such as servers, databases, laptops, mobile devices, etc. This will help to determine the scope and boundaries of the risk assessment, as well as the potential exposure and impact of data loss. Identifying staff members who have access to the data, risk scenarios and owners, and existing controls are important steps, but they should be done after identifying the data locations. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1.1, page 51.
Which of the following sources is MOST relevant to reference when updating security awareness training materials?
Risk management framework
Risk register
Global security standards
Recent security incidents reported by competitors
The most relevant source to reference when updating security awareness training materials is the recent security incidents reported by competitors. This can help to illustrate the real-world threats and consequences of poor security practices, and to motivate the employees to follow the security policies and procedures. Risk management framework, risk register, and global security standards are other sources that may be useful, but they are not as relevant as the recent security incidents. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 9; CRISC Review Manual, 6th Edition, page 214.
When reviewing a business continuity plan (BCP). which of the following would be the MOST significant deficiency?
BCP testing is net in conjunction with the disaster recovery plan (DRP)
Recovery time objectives (RTOs) do not meet business requirements.
BCP is often tested using the walk-through method.
Each business location has separate, inconsistent BCPs.
According to the CRISC Review Manual, recovery time objectives (RTOs) are the maximum acceptable time that an IT system can be inoperable without causing significant damage to the business operations and objectives. RTOs are determined by the business impact analysis (BIA) and are used to define the recovery strategies and priorities. Therefore, if the RTOs do not meet the business requirements, it would be themost significant deficiency in the BCP, as it would imply that the recovery plan is not aligned with the business needs and expectations. The other options are not the most significant deficiencies, as they do not directly affect the recovery time and the business continuity. BCP testing is not necessarily done in conjunction with the DRP, as they have different scopes and objectives. BCP testing can use different methods, such as walk-through, simulation, or full interruption, depending on the purpose and scope of the test. Each business location can have separate BCPs, as long as they are consistent with the enterprise-wide BCP and the business requirements. References = CRISC Review Manual, 7th Edition, Chapter 5, Section 5.2.2, page 240.
Numerous media reports indicate a recently discovered technical vulnerability is being actively exploited. Which of the following would be the BEST response to this scenario?
Assess the vulnerability management process.
Conduct a control serf-assessment.
Conduct a vulnerability assessment.
Reassess the inherent risk of the target.
A technical vulnerability is a weakness or flaw in the design or implementation of an information system or resource that can be exploited or compromised by a threat or source of harm that may affect the organization’s objectives or operations. A technical vulnerability may be caused byvarious factors, such as human error, system failure, process inefficiency, resource limitation, etc.
A vulnerability assessment is a process of identifying and evaluating the technical vulnerabilities that exist or may arise in the organization’s information systems or resources, and determining their severity and impact. A vulnerability assessment can help the organization to assess and prioritize the risks, and to design and implement appropriate controls or countermeasures to mitigate or prevent the risks.
The best response to the scenario of a recently discovered technical vulnerability being actively exploited is to conduct a vulnerability assessment, because it can help the organization to address the following questions:
What is the nature and extent of the technical vulnerability, and how does it affect the functionality or security of the information system or resource?
How is the technical vulnerability being exploited or compromised, and by whom or what?
What are the potential consequences or impacts of the exploitation or compromise of the technical vulnerability for the organization and its stakeholders?
How can the technical vulnerability be detected and reported, and what are the available or feasible options or solutions to address or correct it?
Conducting a vulnerability assessment can help the organization to improve and optimize the information system or resource quality and performance, and to reduce or eliminate the technicalvulnerability. It can also help the organization to align the information system or resource with the organization’s objectives and requirements, and to comply with the organization’s policies and standards.
The other options are not the best responses to the scenario of a recently discovered technical vulnerability being actively exploited, because they do not address the main purpose and benefit of conducting a vulnerability assessment, which is to identify and evaluate the technical vulnerability, and to determine its severity and impact.
Assessing the vulnerability management process is a process of evaluating and verifying the adequacy and effectiveness of the process that is used to identify, analyze, evaluate, and communicate the technical vulnerabilities, and to align them with the organization’s objectives and requirements. Assessing the vulnerability management process can help the organization to improve and optimize the process, and to reduce or eliminate the gaps or weaknesses in the process, but it is not the best response to the scenario, because it does not indicate the nature and extent of the technical vulnerability, and how it affects the organization and its stakeholders.
Conducting a control self-assessment is a process of evaluating and verifying the adequacy and effectiveness of the controls that are intended to ensure the confidentiality, integrity, availability, and reliability of the information systems and resources, using the input and feedback from the individuals or groups that are involved or responsible for the information systems activities or functions. Conducting a control self-assessment can help the organization to identify and document the control deficiencies, and to align them with the organization’s objectives and requirements, but it is not the best response to the scenario, because it does not indicate thenature and extent of the technical vulnerability, and how it affects the organization and its stakeholders.
Reassessing the inherent risk of the target is a process of reevaluating and recalculating the amount and type of risk that exists in the absence of any controls, and that is inherent to the nature or characteristics of the target, which is the information system or resource that is affected by the technical vulnerability. Reassessing the inherent risk of the target can help the organization to understand and document the risk exposure or level, and to align it with the organization’s risk appetite and tolerance, but it is not the best response to the scenario, because it does not indicate the nature and extent of the technical vulnerability, and how it affects the organization and its stakeholders. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 195
CRISC Practice Quiz and Exam Prep
The BEST way to obtain senior management support for investment in a control implementation would be to articulate the reduction in:
detected incidents.
residual risk.
vulnerabilities.
inherent risk.
Residual risk is the risk that remains after applying risk responses, such as avoidance, mitigation, transfer, or acceptance. It represents the level of exposure that the organisation is willing to tolerate or assume. Residual risk should be aligned with the organisation’s risk appetite and risk tolerance, which are determined by senior management. Therefore, the best way to obtain senior management support for investment in a control implementation would be to articulate the reduction in residual risk that the control would achieve. This would demonstrate how the control would help the organisation meet its riskobjectives and reduce the likelihood or impact of adverse events. References = ISACA CRISC Review Manual, 7th Edition, Chapter 1, Section 1.3.2, page 25.
Which of the following presents the GREATEST security risk associated with Internet of Things (IoT) technology?
The inability to monitor via network management solutions
The lack of relevant IoT security frameworks to guide the risk assessment process
The heightened level of IoT threats via the widespread use of smart devices
The lack of updates for vulnerable firmware
Vulnerable firmware that lacks updates is a significant security risk, as it can be exploited by attackers. Addressing this issue aligns withSecure IoT Deployment Practicesto reduce exposure.
Which of the following poses the GREATEST risk to an organization ' s operations during a major it transformation?
Lack of robust awareness programs
infrequent risk assessments of key controls
Rapid changes in IT procedures
Unavailability of critical IT systems
Unavailability of critical IT systems poses the greatest risk to an organization’s operations during a major IT transformation, because it can disrupt the business continuity, productivity, and performance of the organization. Unavailability of critical IT systems can also cause financial, reputational, or legal damages to the organization, and affect the quality and delivery of products or services to the customers. The other options are not the greatest risks, although they may also pose some challenges or threats to the organization during a major IT transformation. Lack of robust awareness programs, infrequent risk assessments of key controls, and rapid changes in IT procedures are examples of management or process risks that can affect the planning, execution,or monitoring of the IT transformation, but they do not have the same impact or severity as the unavailability of critical IT systems. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Which of the following should be done FIRST when information is no longer required to support business objectives?
Archive the information to a backup database.
Protect the information according to the classification policy.
Assess the information against the retention policy.
Securely and permanently erase the information
A retention policy is a set of rules and guidelines that define how long and under what conditions the information should be kept or disposed of by the organization, based on its value, sensitivity, and legal or regulatory requirements.
When information is no longer required to support business objectives, the first thing that should be done is to assess the information against the retention policy. This means that the information should be reviewed and evaluated to determine if it should be retained or deleted, and for how long and by whom.
Assessing the information against the retention policy helps to ensure that the information is managed and disposed of in a consistent and compliant manner, that the information is protected from unauthorized access, use, disclosure, modification, or destruction, and that the information is available for future reference or audit purposes if needed.
The other options are not the first things that should be done when information is no longer required to support business objectives. They are either secondary or not essential for information management.
The references for this answer are:
Risk IT Framework, page 28
Information Technology & Security, page 22
Risk Scenarios Starter Pack, page 20
Which of the following statements BEST describes risk appetite?
The amount of risk an organization is willing to accept
The effective management of risk and internal control environments
Acceptable variation between risk thresholds and business objectives
The acceptable variation relative to the achievement of objectives
Risk appetite is defined as " the amount of risk that an organization is willing to accept in pursuit of its objectives, before action is deemed necessary to reduce the risk. " 1 It represents a balance between the potential benefits of innovation and the threats that change inevitably brings. Risk appetite reflects the organization’s risk attitude and its willingness to accept risk in specific scenarios, with a governance model in place for risk oversight. Risk appetite helps to guide the organization’s approach to risk and risk management, and to align its risk decisions with its business objectives and context. The other options are not the best descriptions of risk appetite, as they are either too vague (the effective management of risk and internal control environments), too narrow (acceptable variation between risk thresholds and business objectives), or confusing (the acceptable variation relative to the achievement of objectives). References = Risk Appetite vs. Risk Tolerance: What is the Difference?
Which of the following should be included in a risk assessment report to BEST facilitate senior management ' s understanding of the results?
Benchmarking parameters likely to affect the results
Tools and techniques used by risk owners to perform the assessments
A risk heat map with a summary of risk identified and assessed
The possible impact of internal and external risk factors on the assessment results
A risk heat map is a graphical tool that displays the level of risk for each risk area based on the impact and likelihood of occurrence. It also provides a summary of the risk assessment results, such as the number and severity of risks, the risk appetite and tolerance, and the risk response strategies. A risk heat map can help senior management to understand the risk profile of the organization, prioritize the risks that need attention, and allocate resources accordingly. A risk heat map is more effective than the other options because it can communicate complex information in a simple and visual way, and it can highlight the key risk areas and trends. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.2, page 97.
Which of the following should be considered FIRST when creating a comprehensive IT risk register?
Risk management budget
Risk mitigation policies
Risk appetite
Risk analysis techniques
Risk appetite is the most important factor to consider first when creating a comprehensive IT risk register, as it defines the amount and type of risk that the organization is willing to accept in pursuit of its objectives, and guides the identification, assessment, response, and monitoring of the IT risks. The other options are not the most important factors, as they are more related to theresources, actions, or methods of the IT risk management, respectively, rather than the strategy or direction of the IT risk management. References = CRISC Review Manual, 7th Edition, page 109.
A technology company is developing a strategic artificial intelligence (Al)-driven application that has high potential business value. At what point should the enterprise risk profile be updated?
After user acceptance testing (UAT)
Upon approval of the business case
When user stories are developed
During post-implementation review
A risk owner should be the person accountable for:
the risk management process
managing controls.
implementing actions.
the business process.
A risk owner should be the person accountable for the business process that is affected by the risk, as they have the authority, responsibility, and knowledge to manage the risk effectively. The risk owner should collaborate with the risk practitioner, who facilitates the risk management process, and the risk action owners, who implement the risk response actions. The risk owner should also ensure that the controls are adequate and functioning properly to mitigate the risk. The other options are not the best description of what a risk owner should be accountable for, as they are either too broad (the risk management process), too narrow (managing controls or implementing actions), or not directly related to the risk (the businessprocess). References = Why Assigning a Risk Owner is Important and How to Do It Right; Definition of Risk Owner; What Is a Risk Owner in Project Management?
Which of the following should be used as the PRIMARY basis for evaluating the state of an organization ' s cloud computing environment against leading practices?
The cloud environment ' s capability maturity model
The cloud environment ' s risk register
The cloud computing architecture
The organization ' s strategic plans for cloud computing
Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources that can be rapidly provisioned and released with minimal management effort or service provider interaction. The cloud computing architecture is the structure and design of the cloud environment, which includes the components, services, interfaces, standards, and configurations. The cloud computing architecture should be used as the primary basis for evaluating the state of an organization’s cloud computing environment against leading practices, as it determines the performance, security, reliability, scalability, and interoperability of the cloud services. By comparing the cloud computing architecture with the best practices and benchmarks in the industry, an organization can identify the gaps and weaknesses in the cloud environment and implement the necessary improvements and controls. References = CRISC Review Manual, 7th Edition, page 156.
Which of the following is the MOST important information to cover in a business continuity awareness training program for all employees of the organization?
Recovery time objectives (RTOs)
Communication plan
Critical asset inventory
Separation of duties
Which key performance efficiency IKPI) BEST measures the effectiveness of an organization ' s disaster recovery program?
Number of service level agreement (SLA) violations
Percentage of recovery issues identified during the exercise
Number of total systems recovered within tie recovery point objective (RPO)
Percentage of critical systems recovered within tie recovery time objective (RTO)
The key performance indicator (KPI) that best measures the effectiveness of an organization’s disaster recovery program is the percentage of critical systems recovered within the recovery time objective (RTO). The RTO is the acceptable timeframe within which a business process or system must be restored after a disruption. The percentage of critical systems recovered within the RTO indicates how well the disaster recovery program can meet the business continuity requirements and minimize the impact of the disruption. The other options are not as good as the percentage of critical systems recovered within the RTO, as they are related to the efficiency, quality, or scope of the disaster recovery program, not the effectiveness of the disaster recovery program. References = Risk and Information Systems Control StudyManual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Key Performance Indicators, page 183.
Which of the following is the PRIMARY reason to engage business unit managers in risk management processes ' ?
Improved alignment will technical risk
Better-informed business decisions
Enhanced understanding of enterprise architecture (EA)
Improved business operations efficiency
Risk management is the process of identifying, analyzing, evaluating, treating, monitoring, and communicating the risks that may affect the achievement of an organization’s objectives. Risk management helps to optimize the risk exposure and performance of the organization, and support the business objectives and strategies. The primary reason to engage business unit managers in risk management processes is to enable better-informed business decisions, which are the decisions that incorporate the risk information and analysis into the strategic and operational choices of the organization. By engaging business unit managers in risk management processes, the organization can ensure that the business unit managers have the insight andunderstanding of the current and potential risks, their likelihood and impact, their interrelationships and dependencies, and their alignment with the risk appetiteand tolerance. This can help the business unit managers to prioritize the risks, allocate the resources, select the risk responses, monitor the risk performance, and evaluate the risk outcomes. References = 5
Which of the following is MOST important for the organization to consider before implementing a new in-house developed artificial intelligence (Al) solution?
Industry trends in Al
Expected algorithm outputs
Data feeds
Alert functionality
The most important factor for the organization to consider before implementing a new in-house developed artificial intelligence (AI) solution is the expected algorithm outputs, as they define the desired outcomes and objectives of the AI solution, and guide the design, testing, and validation of the AI algorithm. The other options are not the most important factors, as they are more related to the research, input, or monitoring of the AI solution, respectively, rather than the output of the AI solution. References = CRISC Review Manual, 7th Edition, page 153.
Which of the following is the BEST risk management approach for the strategic IT planning process?
Key performance indicators (KPIs) are established to track IT strategic initiatives.
The IT strategic plan is reviewed by the chief information security officer (CISO) and enterprise risk management (ERM).
The IT strategic plan is developed from the organization-wide risk management plan.
Risk scenarios associated with IT strategic initiatives are identified and assessed.
Identifying and assessing the risk scenarios associated with IT strategic initiatives is the best risk management approach for the strategic IT planning process, because it helps to understand and evaluate the potential or actual threats or opportunities that may affect the achievement or implementation of the IT strategic initiatives, and to determine the appropriate risk responses and controls. A risk scenario is a hypothetical situation or event that describes the source, cause, consequence, and impact of a risk. A risk scenario can be positive or negative, depending on whether it represents an opportunity or a threat. An IT strategic initiative is a project or program that supports or enables the IT strategy, which is a plan that defines how IT supports and aligns with the organization’s vision, mission, and strategy. The strategic IT planning process is a process of developing, implementing, and monitoring the IT strategy and its associated IT strategic initiatives. Identifying and assessing the risk scenarios is the best risk management approach, as it helps to anticipate and prepare for the potential or actual outcomes of the IT strategic initiatives, and to optimize the risk-reward balance and the value delivery of IT. Establishing key performance indicators (KPIs) to track IT strategic initiatives, reviewing the IT strategic plan by the chief information security officer (CISO) and enterprise risk management (ERM), and developing the IT strategic plan from the organization-wide risk management plan are all possible risk management approaches for the strategic IT planning process, but they are not the best approach, as they do not directly address the identification and assessment of the risk scenarios associated with IT strategic initiatives. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.1.1, page 37
Quantifying the value of a single asset helps the organization to understand the:
overall effectiveness of risk management
consequences of risk materializing
necessity of developing a risk strategy,
organization s risk threshold.
Quantifying the value of a single asset helps the organization to understand the consequences of risk materializing, as it indicates how much impact or loss the organization would suffer if the asset is compromised, damaged, or destroyed by a threat. The value of an asset can be determined by various methods, such as the cost of acquisition, replacement, or restoration, the market value, the income or revenue generated, or the impact on the business objectives or reputation. The other options are not the best description of what quantifying the value of a single asset helps the organization to understand, as they are either too broad (overall effectiveness of risk management, necessity of developing a risk strategy) or not directly related to the asset value (organization’s risk threshold). References = IT Asset Valuation, Risk Assessment and Control Implementation Model; How to quantify assets?; Asset Valuation - Definition, Methods, and Importance
Which of the following should a risk practitioner do FIRST when an organization decides to use a cloud service?
Review the vendor selection process and vetting criteria.
Assess whether use of service falls within risk tolerance thresholds.
Establish service level agreements (SLAs) with the vendor.
Check the contract for appropriate security risk and control provisions.
According to the CRISC EXAM TOPIC 2 LONG Flashcards, the first thing that a risk practitioner should do when an organization decides to use a cloud service is to review the vendor selection process and vetting criteria. This is because the vendor selection process and vetting criteria are essential steps to ensure that the cloud service provider meets the organization’s requirements and expectations, and that the risks associated with the cloud service are identified and managed. By reviewing the vendor selection process and vetting criteria, the risk practitioner can evaluate the quality, reliability, security, and compliance of the cloud service provider, and determine if the cloud service is suitable and beneficial for the organization. The risk practitioner can also identify any gaps or weaknesses in the vendor selection process and vetting criteria, and recommend improvements or alternatives accordingly. References = CRISC EXAM TOPIC 2 LONG Flashcards
Which of the following is MOST important to include in a risk assessment of an emerging technology?
Risk response plans
Risk and control ownership
Key controls
Impact and likelihood ratings
The most important thing to include in a risk assessment of an emerging technology is the impact and likelihood ratings of the risks associated with the technology. Impact and likelihood ratings are the measures of the potential consequences and probabilities of the risk events that could affect the achievement of the enterprise’s objectives. Impact and likelihood ratings can help to evaluate the level andnature of the risk exposure, and to prioritize the risks for further analysis and response. Impact and likelihood ratings can also help to communicate the risk profile and appetite of the enterprise, and to support the risk-based decision making. Risk response plans, risk and control ownership, and key controls are not as important as impact and likelihood ratings, as they are the outputs or outcomes of the risk assessment process, and not the inputs or components of the risk assessment process. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 49.
Which of the following BEST ensures that the data feeds used by an organization are complete and accurate?
Data is inspected and accepted by owners
Best-in-class data mining technology is used
Sources of data and attributes are known
The project is run by an experienced team
Whendata owners inspect and approveincoming data, it provides assurance of its completeness and accuracy, as they are accountable for the integrity of the data under their ownership.
An organization has four different projects competing for funding to reduce overall IT risk. Which project should management defer?
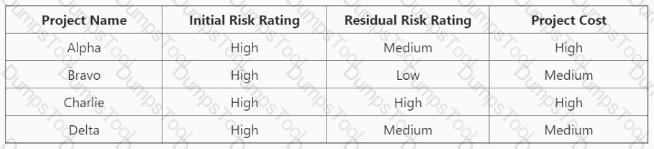
Project Charlie
Project Bravo
Project Alpha
Project Delta
Project Delta should be deferred by management, as it has the lowest return on investment (ROI) among the four competing projects. ROI is a measure of the profitability or efficiency of a project, calculated by dividing the net benefits by the total costs. Project Delta has a net benefit of $100,000 and a total cost of $200,000, resulting in an ROI of 0.5. The other projects have higher ROIs: Project Alpha has an ROI of 1.0, Project Bravo has an ROI of 0.8, and Project Charlie has an ROI of 0.6. Therefore, Project Delta is the least attractive option for reducingoverall IT risk, and management should prioritize the other projects instead. References = How to Manage Project Risk: A 5-Step Guide; Matching the right projects with the right resources; Risk Types in Project Management
Which of the following resources is MOST helpful when creating a manageable set of IT risk scenarios?
Results of current and past risk assessments
Organizational strategy and objectives
Lessons learned from materialized risk scenarios
Internal and external audit findings
According to the CRISC Review Manual1, lessons learned from materialized risk scenarios are the insights and knowledge gained from analyzing the causes, impacts, and responses of actual risk events that occurred in the past. Lessons learned from materialized risk scenarios are the most helpful resource when creating a manageable set of IT risk scenarios, as they help to identify and prioritize the most relevant and realistic risks that could affect the organization’s objectives, processes, and resources. Lessons learned from materialized risk scenarios also helpto improve the risk management practices and capabilities, and to avoid repeating the same mistakes or gaps in the future. References = CRISC Review Manual1, page 206.
An organization has an internal control that requires all access for employees be removed within 15 days of their termination date. Which of the following should the risk practitioner use to monitor
adherence to the 15-day threshold?
Operation level agreement (OLA)
Service level agreement (SLA)
Key performance indicator (KPI)
Key risk indicator (KRI)
A key performance indicator (KPI) is a metric that measures the achievement of a specific goal or objective. A KPI for the internal control that requires all access for employees be removed within 15 days of their termination date could be the percentage of employees whose access was removed within the specified time frame. This KPI would help the risk practitioner to monitor the compliance and effectiveness of the control and identify any deviations or issues.
References
•Key Performance Indicators (KPIs) - ISACA
•How to Improve Risk Awareness in the Workplace [+ Template] - AlertMedia
•[SITXWHS
Which of the following is the GREATEST benefit of using IT risk scenarios?
They support compliance with regulations.
They provide evidence of risk assessment.
They facilitate communication of risk.
They enable the use of key risk indicators (KRls)
The greatest benefit of using IT risk scenarios is that they facilitate communication of risk, as they provide a clear and realistic description of the risk sources, events, impacts, and responses, and enable the stakeholders to understand and appreciate the risk exposure and appetite of the organization. Supporting compliance with regulations, providing evidence of risk assessment, and enabling the use of key risk indicators (KRIs) are also benefits of using IT risk scenarios, but they are not the greatest benefit, as they are more related to the outcomes or consequences of risk communication, rather than the process or value of risk communication. References = CRISC Review Manual, 7th Edition, page 100.
Which of the following analyses is MOST useful for prioritizing risk scenarios associated with loss of IT assets?
SWOT analysis
Business impact analysis (BIA)
Cost-benefit analysis
Root cause analysis
Business impact analysis (BIA) is the most useful analysis for prioritizing risk scenarios associated with loss of IT assets, because it evaluates the potential consequences of disruption tocritical business functions and processes. BIA helps to identify the most significant risks and the most urgent recovery needs. SWOT analysis, cost-benefit analysis, and root cause analysis are all useful tools for different purposes, but they do not directly address the impact of risk scenarios on business continuity and resilience. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 143
A payroll manager discovers that fields in certain payroll reports have been modified without authorization. Which of the following control weaknesses could have contributed MOST to this problem?
The user requirements were not documented.
Payroll files were not under the control of a librarian.
The programmer had access to the production programs.
The programmer did not involve the user in testing.
A payroll manager discovers that fields in certain payroll reports have been modified without authorization. This indicates that there is a risk of unauthorized access, use, disclosure, modification, or destruction of sensitive data, such as employee information, payroll records, tax returns, etc.
A control weakness that could have contributed most to this problem is that the programmer had access to the production programs. This means that the programmer could potentially alter the source code or configuration of the payroll software without proper authorization or approval.
The other options are not control weaknesses that could have contributed most to this problem. They are either irrelevant or less likely to cause unauthorized changes in the payroll software.
The references for this answer are:
Risk IT Framework, page 12
Information Technology & Security, page 6
Risk Scenarios Starter Pack, page 4
Which of the following is the MAIN benefit to an organization using key risk indicators (KRIs)?
KRIs provide an early warning that a risk threshold is about to be reached.
KRIs signal that a change in the control environment has occurred.
KRIs provide a basis to set the risk appetite for an organization.
KRIs assist in the preparation of the organization ' s risk profile.
The main benefit of using key risk indicators (KRIs) for an organization is that they provide an early warning that a risk threshold is about to be reached. KRIs are metrics that measure the likelihood and impact of risks, and help monitor and prioritize the most critical risks. KRIs also help to trigger timely and appropriate risk responses, before the risk becomes unmanageable orunacceptable. The other options are not the main benefit of using KRIs, although they may be secondary benefits or outcomes. KRIs signal that a change in the control environment has occurred, provide a basis to set the risk appetite for an organization, and assist in the preparation of the organization’s risk profile. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.1, page 4-36.
Which of the following would BEST help an enterprise define and communicate its risk appetite?
Gap analysis
Risk assessment
Heat map
Risk register
The best way to help an enterprise define and communicate its risk appetite is to use a risk register, which is a document that records and summarizes the key information and data about the identified risks and the risk responses1. A risk register can help to:
Define the risk appetite, which is the amount and type of risk that the enterprise is willing to accept or pursue in order to achieve its objectives2. The risk register can include the risk appetite statement, which is a clear and concise expression of the enterprise’s risk preferences and boundaries3.
Communicate the risk appetite, which is the process of sharing and informing the risk appetite to the relevant stakeholders, such as the board, the management, the employees, or the customers4. The risk register can be used as a communication tool, which can provide a consistent and transparent view of the enterprise’s risk profile and performance5.
The other options are not the best ways to help an enterprise define and communicate its risk appetite, because:
Gap analysis is a technique that compares the current state and the desired state of a process, system, or organization, and identifies the gaps or differences between them6. Gap analysis can help to assess the alignment or misalignment of the enterprise’s risk appetite with its risk level, but it does not help to define or communicate the risk appetite itself.
Risk assessment is a process that estimates the probability and impact of the risks, and prioritizes the risks based on their significance and urgency. Risk assessment can help to identify andanalyze the risks that may affect the enterprise’s objectives, but it does not help to define or communicate the risk appetite itself.
Heat map is a graphical representation that uses colors to indicate the level or intensity of a variable, such as risk. Heat map can help to visualize and compare the risks based on their probability and impact, but it does not help to define or communicate the risk appetite itself.
References =
Risk Register - CIO Wiki
Risk Appetite - CIO Wiki
Risk Appetite Statement - CIO Wiki
Risk Communication - CIO Wiki
Risk Reporting - CIO Wiki
Gap Analysis - CIO Wiki
[Risk Assessment - CIO Wiki]
[Heat Map - CIO Wiki]
[Risk and Information Systems Control documents and learning resources by ISACA]
An organization has determined that risk is not being adequately tracked and
managed due to a distributed operating model. Which of the following is the
BEST way to address this issue?
Increase the frequency of risk assessments.
Revalidate the organization ' s risk appetite
Create a centralized portfolio of risk scenarios.
Create dashboards for risk metrics.
Which of the following is the MOST important benefit of key risk indicators (KRIs) '
Assisting in continually optimizing risk governance
Enabling the documentation and analysis of trends
Ensuring compliance with regulatory requirements
Providing an early warning to take proactive actions
The most important benefit of key risk indicators (KRIs) is providing an early warning to take proactive actions, because this helps organizations to prevent or mitigate potential risks that may impact their operations, objectives, or performance. KRIs are specific metrics that measure the level and impact of risks, and provide timely signals that something may be going wrong or needs urgent attention. By monitoring and analyzing KRIs, organizations can identify and assess emerging or existing risks, and initiate appropriate risk responses before the risks escalate intosignificant issues. This can enhance the organization’s resilience, competitiveness, and value creation. The other options are less important benefits of KRIs. Assisting in continually optimizing risk governance is a benefit of KRIs, but it is not the most important one. Risk governance is the framework and process that defines how an organization manages its risks, including the roles, responsibilities, policies, and standards. KRIs can help to evaluate and improve the effectiveness and efficiency of risk governance, but they are not the only factor that influences it. Enabling the documentation and analysis of trends is a benefit of KRIs, but it is not the most important one. Documenting and analyzingtrends can help organizations to understand the patterns, causes, and consequences of risks, and to learn from their experiences. However, this benefit is more relevant for historical or retrospective analysis, rather than for proactive action. Ensuring compliance with regulatory requirements is a benefit of KRIs, but it is not the most important one. Compliance is the adherence to the laws, regulations, and standards that apply to an organization’s activities and operations. KRIs can help to monitor and demonstrate compliance, but they are not the only tool or objective for doing so. References = Why Key Risk Indicators Are Important for Risk Management 1
An organization has implemented a policy requiring staff members to take a minimum of five consecutive days ' leave per year to mitigate the risk of malicious insider activities. Which of the following is the BEST key performance indicator (KPI) of the effectiveness of this policy?
Percentage of staff turnover following five consecutive days of leave
Average number of consecutive days of leave per staff member
Number of suspected malicious activities reported since policy implementation
Financial loss incurred due to malicious activities since policy implementation
The number of suspected malicious activities reported since the policy ' s implementation directly measures thepolicy ' s effectiveness in identifying and mitigating insider threats. This aligns withKey Performance Indicators (KPIs)used to evaluate control outcomes.
The MAIN reason for prioritizing IT risk responses is to enable an organization to:
determine the risk appetite.
determine the budget.
define key performance indicators (KPIs).
optimize resource utilization.
Optimizing resource utilization is the main reason for prioritizing IT risk responses, as it helps to allocate resources to the most critical and urgent risks. The other options are not the main reasons for prioritizing IT risk responses, although they may be related to the process.
Which of the following is the MOST effective key performance indicator (KPI) for change management?
Percentage of changes with a fallback plan
Number of changes implemented
Percentage of successful changes
Average time required to implement a change
According to the CRISC Review Manual (Digital Version), the percentage of successful changes is the most effective key performance indicator (KPI) for change management, as it measures thequality and effectiveness of the change management process and its alignment with the organization’s objectives and requirements. The percentage of successful changes helps to:
Evaluate the extent to which the changes have met the expected outcomes and benefits
Identify and analyze the root causes of any failed or problematic changes and implement corrective actions or improvement measures
Monitor and report the performance and progress of the change management process and its impact on the organization
Enhance the confidence and satisfaction of the stakeholders and customers with the change management process and its results
References = CRISC Review Manual (Digital Version), Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Scenarios, pp. 107-1081
An organization is considering outsourcing user administration controls tor a critical system. The potential vendor has offered to perform quarterly sett-audits of its controls instead of having annual independent audits. Which of the following should be of GREATEST concern to me risk practitioner?
The controls may not be properly tested
The vendor will not ensure against control failure
The vendor will not achieve best practices
Lack of a risk-based approach to access control
The greatest concern for the risk practitioner when the potential vendor has offered to perform quarterly self-audits of its controls instead of having annual independent audits is that the controls may not be properly tested. Self-audits are audits that are performed by the vendor itself, without the involvement of an external or independent party. Self-audits may not be reliable, objective, or consistent, as the vendor may have biases, conflicts of interest, or lack of expertise in auditing its own controls. Self-audits may also not follow the same standards, criteria, or methodologies as independent audits, and may not provide sufficient assurance or evidence of the effectiveness of the controls. The other options are not as concerning as the possibility of improper testing of the controls, as they are related to the outcomes, expectations, or approaches of the controls, not the quality or validity of the controls. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: IT Control Assessment, page 6
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
Creating metrics to track remote connections
Updating remote desktop software
Implementing multi-factor authentication (MFA)
Updating the organizational policy for remote access
Implementing multi-factor authentication (MFA) directly reduces the likelihood of unauthorized access by adding an extra layer of verification to remote network access. ISACA and CRISC materials emphasize that technical controls (e.g., MFA) meaningfully reduce the probability of threat scenarios involving remote access
What information is MOST helpful to asset owners when classifying organizational assets for risk assessment?
Potential loss to tie business due to non-performance of the asset
Known emerging environmental threats
Known vulnerabilities published by the asset developer
Cost of replacing the asset with a new asset providing similar services
The potential loss to the business due to non-performance of the asset is the most helpful information for asset owners when classifying organizational assets for risk assessment, because it reflects the value and criticality of the asset to the business objectives and processes. The potential loss can be measured in terms of financial, operational, reputational, or legal impacts.The known emerging environmental threats are not relevant for asset classification, because they are external factors that affect the risk level, not the asset value. The known vulnerabilities published by the asset developer are not relevant for asset classification, because they are internal factors that affect the risk level, not the asset value. The cost of replacing theasset with a new asset providing similar services is not relevant for asset classification, because it does not reflect the business impact of losing the asset functionality or availability. References = CRISC Sample Questions 2024
The cost of maintaining a control has grown to exceed the potential loss. Which of the following BEST describes this situation?
Insufficient risk tolerance
Optimized control management
Effective risk management
Over-controlled environment
The situation where the cost of maintaining a control has grown to exceed the potential loss is best described as an over-controlled environment, as it indicates that the control is not cost-effective and may be unnecessary or excessive. Insufficient risk tolerance, optimized control management, and effective risk management are not the best descriptions, as they do not reflect the imbalance between the control cost and the potential loss. References = CRISC Review Manual, 7th Edition, page 149.
The PRIMARY reason for periodically monitoring key risk indicators (KRIs) is to:
rectify errors in results of KRIs.
detect changes in the risk profile.
reduce costs of risk mitigation controls.
continually improve risk assessments.
The primary reason for periodically monitoring key risk indicators (KRIs) is to detect changes in the risk profile of the enterprise. KRIs are metrics that provide information on the level of exposure to a specific risk or a group of risks. By monitoring KRIs, the enterprise can identifyany deviations from the expected risk level, and take appropriate actions to adjust the risk response or the risk appetite. Monitoring KRIs also helps to validate the effectiveness of risk mitigation controls and the accuracy of risk assessments. Rectifying errors in results of KRIs, reducing costs of risk mitigation controls, and continually improving risk assessments are possible benefits of monitoring KRIs, but they are not the primary reason. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.1.1.2, page 175.
Which of the following provides the BEST evidence that robust risk management practices are in place within an organization?
A management-approved risk dashboard
A current control framework
A regularly updated risk register
Regularly updated risk management procedures
Importance of a Risk Register:
A risk register is a critical tool for documenting, tracking, and managing risks within an organization. It serves as a central repository for all identified risks, detailing their status, impact, likelihood, and the actions taken to mitigate them.
A regularly updated risk register demonstrates an active and ongoing risk management process, reflecting the organization ' s commitment to identifying and addressing risks promptly.
Evidence of Robust Risk Management:
The risk register shows the organization ' s proactive approach to risk management by continuously monitoring and updating risks.
It provides transparency and accountability, allowing stakeholders to see how risks are being managed and mitigated over time.
Regular updates ensure that new risks are identified and existing risks are reassessed, indicating a dynamic and responsive risk management practice.
Comparing Other Options:
Management-Approved Risk Dashboard:While useful for summarizing risk information, a dashboard does not provide the detailed, ongoing updates and comprehensive tracking found in a risk register.
Current Control Framework:A control framework outlines the controls in place but does not detail specific risks or their management.
Regularly Updated Risk Management Procedures:Procedures are important but do not provide the same level of detailed risk tracking and management as a risk register.
References:
The CRISC Review Manual emphasizes the importance of a risk register in consolidating and tracking risk data, making it an essential component of robust risk management practices (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.6 Risk Register) .
Which of the following is MOST important for a risk practitioner to verify when periodically reviewing risk response action plans?
The action plans have documented schedules
The action plans treat the corresponding risk
Budget has been allocated for the action plans
Key risk indicators (KRIs) are defined in the action plans
Which of the following indicators measures the performance of IT configuration management?
Number of devices reviewed for compliance
Number of devices adhering to baseline settings
Number of devices exceeding minimum configuration
Number of devices not reporting configuration data
The correct answer isBbecause the most meaningful indicator ofIT configuration management performanceis thenumber of devices adhering to baseline settings. Configuration management performance is best measured by how many devices are actually in compliance with established baseline configurations.
The other options are less effective indicators:
A. Number of devices reviewed for compliancemeasures activity, not actual performance or outcome.
C. Number of devices exceeding minimum configurationdoes not necessarily reflect compliance with approved baselines.
D. Number of devices not reporting configuration datamay indicate a monitoring issue, but it does not directly measure configuration management performance.
Exact Extracts supporting the answer:
“The control practice related to information systems architecture that includes establishing and maintaining baselines for internally developed systems is Configuration management.”
“The MOST appropriate metric to measure how well the information security function is managing the administration of user access is percent of accounts with configurations in compliance.”
“Including thresholds that identify when controls no longer provide the intended value is essential when developing metrics to monitor the control life cycle.”
“The use of key performance indicators for management of technology controls is BEST related to the measurement of control effectiveness to determine that business requirements are being met.”
These extracts support that configuration management should be measured againstbaseline compliance, makingdevices adhering to baseline settingsthe best indicator.
===========
Which of the following would BEST assist in reconstructing the sequence of events following a security incident across multiple IT systems in the organization ' s network?
Network monitoring infrastructure
Centralized vulnerability management
Incident management process
Centralized log management
According to the CRISC Review Manual, centralized log management is the best way to assist in reconstructing the sequence of events following a security incident across multiple IT systems in the organization’s network, because it enables the collection, correlation, analysis, and retention of log data from various sources. Centralized log management can provide a comprehensive and consistent view of the activities and transactions that occurred before, during, and after the incident, and can facilitate the identification of the root cause, impact, and scope of the incident. The other options are not the best ways to assist in reconstructing the sequence of events, because they do not provide the same level of detail and accuracy as centralized log management. Network monitoring infrastructure is a tool that helps to monitor the performance and availability of the network, but it does not capture the log data from the IT systems. Centralized vulnerability management is a process that helps to identify and remediate the vulnerabilities in the IT systems, but it does not record the events and transactions that occurred on the systems. Incident management process is a process that helps to respond to and resolve the incidents, but it does not provide the log data from the IT systems. References = CRISC Review Manual, 7th Edition, Chapter 5, Section 5.3.2, page 263.
Which of the following is the MOST appropriate key risk indicator (KRI) for backup media that is recycled monthly?
Time required for backup restoration testing
Change in size of data backed up
Successful completion of backup operations
Percentage of failed restore tests
The most appropriate key risk indicator (KRI) for backup media that is recycled monthly is the percentage of failed restore tests. A KRI is a metric that measures the likelihood or impact of a risk, and provides an early warning signal of a potential risk event. The percentage of failed restore tests is a KRI that reflects the quality and reliability of the backup media, and indicates the possibility of data loss or corruption. A high percentage of failed restore tests would suggest that the backup media is not functioning properly, and that the risk of data unavailability is increasing. Therefore, this KRI would help the risk practitioner to monitor the risk and take corrective actions as needed. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.2.2, page 235.
Which of the following is the MOST important consideration for effectively maintaining a risk register?
An IT owner is assigned for each risk scenario.
The register is updated frequently.
The register is shared with executive management.
Compensating controls are identified.
A risk register is a tool that records and tracks the information about the identified risks, such as the risk description, category, owner, probability, impact, response strategy, status, and action plan. The most important consideration for effectively maintaining a risk register is to update it frequently, as the risk environment is dynamic and subject to change. By updating the risk register regularly, an organization can ensure that the risk information is current, accurate, and relevant, and that the risk responses are timely, appropriate, and effective. References = CRISC Review Manual, 7th Edition, page 99.
It was discovered that a service provider ' s administrator was accessing sensitive information without the approval of the customer in an Infrastructure as a Service (laaS) model. Which of the following would BEST protect against a future recurrence?
Data encryption
Intrusion prevention system (IPS)
Two-factor authentication
Contractual requirements
The best option to protect against a future recurrence of unauthorized access by a service provider’s administrator is D. Contractual requirements. Data encryption, intrusion prevention system, and two-factor authentication are all technical measures that can enhance the security of the data stored in the Infrastructure as a Service (IaaS) model, but they do not prevent the service provider’s administrator from accessing the data if they have the necessary credentials, keys, or permissions. Contractual requirements, on the other hand, are legal obligations that bind the service provider to respect the customer’s privacy and confidentiality, and to limit the access tothe data to only authorized and necessary personnel. Contractual requirements can also specify the penalties or remedies for any breach of contract, which can deter the service provider’s administrator from violating the terms of the agreement. Therefore, contractual requirements are the most effective way to protect against a future recurrence of unauthorized access by a service provider’s administrator12
1: What is Data Encryption? | Forcepoint 2: The elements of a contract: understanding contract requirements - Juro
Which of the following is the MOST effective way to minimize the impact associated with the loss of key employees?
Maintain and publish a RACI chart.
Promote incentive programs.
Perform succession planning.
Develop a robust onboarding program.
The correct answer isCbecausesuccession planningis the most effective way to minimize the impact of losing key employees. The main objective is not only to document roles, but to ensure continuity of critical knowledge, responsibilities, and decision-making capability when essential personnel leave the organization. Succession planning prepares the enterprise in advance by identifying backups, developing internal talent, and reducing dependency on specific individuals.
The other options are less effective:
A. Maintain and publish a RACI charthelps clarify responsibilities, but it does not ensure a replacement is ready for key personnel loss.
B. Promote incentive programsmay help retention, but it does not directly minimize the impact if employees do leave.
D. Develop a robust onboarding programhelps new employees become productive, but it is reactive and does not specifically address continuity for loss of key staff.
Exact Extracts supporting the answer:
“Clear detailed roles and responsibilities are MOST critical to ensure the three lines of defense work together effectively.”
“The management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“The primary goal of an enterprise’s IT risk management process is to protect the enterprise and its ability to perform its mission.”
“The main outcome of a business impact analysis (BIA) is the criticality of business processes.”
These extracts support the principle that the organization must preserve continuity of critical responsibilities and business processes. Succession planning best achieves that objective and therefore is the most effective way to minimize the impact associated with the loss of key employees.
===========
The BEST metric to demonstrate that servers are configured securely is the total number of servers:
exceeding availability thresholds
experiencing hardware failures
exceeding current patching standards.
meeting the baseline for hardening.
The best metric to demonstrate that servers are configured securely is the total number of servers meeting the baseline for hardening. Hardening is the process of applying security configurations and settings to servers to reduce their attack surface and vulnerability. A baseline is a standard or benchmark that defines the minimum level of security required for servers. By measuring the number of servers that meet the baseline, the organization can assess the effectiveness of its hardening efforts and identify any gaps or deviations. The other metrics, such as exceeding availability thresholds, experiencing hardware failures, or exceeding current patching standards, are not directly related to the security configuration of servers, but rather to their performance, reliability, or maintenance. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.2, page 2-25.
Which of the following is the PRIMARY consideration when determining the impact to an organization after the discovery of malware on an endpoint device?
Availability of patches and security updates.
Asset criticality and sensitivity.
Currency of the incident response plan.
Currency of anti-malware signatures.
The BEST answer is B because impact is determined by what the affected asset means to the organization. If the endpoint stores sensitive information, supports a critical business process, or has privileged access, the organizational impact is higher. The uploaded CRISC notes support this by stating that the criticality of business processes is a main outcome of business impact analysis, risk assessments identify risk with the highest business impact, and infrastructure criticality can be quantified based on dependencies.
ISACA’s risk assessment guidance states that asset criticality should be determined in terms of impact on business or system objectives, and that impact is the magnitude of harm from a risk scenario affecting confidentiality, integrity, or availability.
A and D relate to vulnerability remediation and preventive/detective control strength, not the primary impact determination. C affects response readiness, but the impact depends first on the criticality and sensitivity of the compromised endpoint and its data.
===========
Which of the following would MOST effectively reduce risk associated with an increase of online transactions on a retailer website?
Scalable infrastructure
A hot backup site
Transaction limits
Website activity monitoring
The most effective way to reduce risk associated with an increase of online transactions on a retailer website is to implement website activity monitoring. Website activity monitoring can help to detect and prevent fraudulent transactions, unauthorized access, data breaches, and other cyber threats that may compromise the security and integrity of the website and its data. Scalable infrastructure, a hot backup site, and transaction limits are other possible ways to reduce risk, but they are not as effective as website activity monitoring. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Which of the following is MOST important to review when an organization needs to transition the majority of its employees to remote work during a crisis?
Customer notification plans
Capacity management
Access management
Impacts on IT project delivery
Capacity management is crucial when transitioning employees to remote work during a crisis. It involves ensuring that the IT infrastructure can handle increased loads and that resources are available to support remote operations effectively.
Which of the following is the GREATEST concern when establishing key risk indicators (KRIs)?
High percentage of lagging indicators
Nonexistent benchmark analysis
Incomplete documentation for KRI monitoring
Ineffective methods to assess risk
The greatest concern when establishing key risk indicators (KRIs) is using ineffective methods to assess risk. KRIs are metrics that measure the likelihood and impact of risks, and help monitor and prioritize the most critical risks. To establish effective KRIs, the risk assessment methods should be reliable, valid, consistent, and timely. Ineffective methods to assess risk could lead to inaccurate or misleading KRIs, which could result in poor risk management decisions and outcomes. The other options are not as significant as using ineffective methods to assess risk, although they may also affect the quality and usefulness of KRIs. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.1, page 4-36.
Which of the following is the MOST important consideration for protecting data assets m a Business application system?
Application controls are aligned with data classification lutes
Application users are periodically trained on proper data handling practices
Encrypted communication is established between applications and data servers
Offsite encrypted backups are automatically created by the application
The most important consideration for protecting data assets in a business application system is to ensure that the application controls are aligned with the data classification rules. Data classification rules define the level of sensitivity, confidentiality, and criticality of the data, andthe corresponding security requirements and controls. Application controls are the policies, procedures, and technical measures that are implemented at the application level to ensure the security, integrity, and availability of the data. Application controls should be designed and configured to match the data classification rules, so that the data is protected according to its value and risk. For example, if the data is classified as highly confidential, the application controls should enforce strong authentication, encryption, access control, logging, and auditing mechanisms. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 214.
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
The organization has not adopted Infrastructure as a Service (IaaS) for its operations
The organization has incorporated blockchain technology in its operations
The organization has implemented heuristics on its network firewall
The organization has not reviewed its encryption standards
Quantum computing threatens outdated algorithms and key lengths. The biggest concern is stale encryption standards—they directly relate to cryptographic resilience. ISACA materials underscore that encryption evaluation is foundational in emerging-threat risk assessments.
The design of procedures to prevent fraudulent transactions within an enterprise resource planning (ERP) system should be based on:
stakeholder risk tolerance.
benchmarking criteria.
suppliers used by the organization.
the control environment.
Fraudulent transactions are those that involve deception, manipulation, or misrepresentation of information or data to obtain an unauthorized or improper benefit or advantage1. Fraudulenttransactions can pose significant risks and losses for an organization, such as financial damages, legal liabilities, reputational damages, or operational disruptions2.
Enterprise resource planning (ERP) systems are integrated software applications that support the core business processes and functions of an organization, such as accounting, finance, human resources, supply chain, inventory, or customer relationship management3. ERP systems can facilitate the efficiency, accuracy, and security of business transactions, but they can also be vulnerable to fraudulent transactions, such as:
Creating fake vendors or customers and processing false invoices or payments
Manipulating or falsifying financial or accounting data or reports
Changing or deleting critical or sensitive information or records
Abusing or misusing access privileges or credentials
Bypassing or compromising the system controls or security measures4
The design of procedures to prevent fraudulent transactions within an ERP system should be based on the control environment. The control environment is the set of standards, processes, and structures that provide the basis for carrying out internal control across the organization. The control environment comprises the following elements:
The tone at the top, which reflects the leadership’s commitment and attitude towards internal control and ethical conduct
The organizational structure, which defines the roles and responsibilities, reporting lines, and authority levels for internal control
The human resource policies and practices, which ensure that the staff have the appropriate skills, competencies, and incentives for internal control
The risk assessment process, which identifies and evaluates the potential risks and threats to the organization’s objectives and transactions
The control activities, which are the specific policies, procedures, and mechanisms that prevent, detect, or correct errors or fraud in transactions
The information and communication systems, which provide reliable and timely data and information for internal control and decision-making
The monitoring and evaluation activities, which measure and report the performance and effectiveness of internal control and ensure continuous improvement
By basing the design of procedures to prevent fraudulent transactions within an ERP system on the control environment, the organization can:
Ensure that the procedures are aligned with the organization’s objectives, values, and expectations regarding internal control and fraud prevention
Provide clear and consistent guidance and instructions for the staff and stakeholders involved in the transactions and the ERP system
Implement adequate and appropriate controls and safeguards to mitigate the risks and vulnerabilities of the transactions and the ERP system
Monitor and evaluate the compliance and effectiveness of the procedures and the ERP system, and identify and address any issues or gaps
References = What is Fraud?, Fraud Risk Management - AICPA, What is ERP?, ERP Fraud: How to Prevent It - ERP Focus, [COSO – Control Environment - Deloitte], [How to use COSO to assess IT controls - Journal of Accountancy]
In which of the following scenarios would a risk practitioner be required to provide the MOST justification for a risk assessment?
Modeling a threat-based risk event
Calculating mean time between failures (MTBF)
Using a semi-quantitative approach
Calculating adjusted loss expectancy (ALE)
Threat-based risk event modeling often involves significant expert judgment: choosing plausible threats, estimating their capability, attack paths, and motivations, and modeling multi-step attack scenarios. According to CRISC, such modeling demands strong justification and documented rationale because assumptions and inputs may be challenged by stakeholders and auditors. Semi-quantitative approaches and ALE calculations also require explanation, but they are generally based on standardized scales, historical data, or accepted formulas. MTBF is an engineering reliability metric, usually based on vendor data or operational history, requiring limited justification from a risk perspective. Threat-based modeling, however, drives critical decisions about controls and investment, and because it can be sensitive to subjective inputs, risk practitioners must carefully justify scenario selection, likelihood estimates, and impact assumptions to maintain credibility and enable informed governance decisions.
Which of the following is the PRIMARY reason for conducting peer reviews of risk analysis?
To enhance compliance with standards
To minimize subjectivity of assessments
To increase consensus among peers
To provide assessments for benchmarking
According to the CRISC Review Manual1, peer reviews are the process of evaluating the quality and validity of risk analysis by independent experts or colleagues. Peer reviews are conducted to ensure that the risk analysis is consistent, objective, and reliable, and that it follows the established standards and methods. The primary reason for conducting peer reviews of risk analysis is to minimize subjectivity of assessments, as peer reviews can help to reduce personal biases, preferences, and assumptions that may affect the risk analysis outcomes. Peer reviews can also help to identify and correct any errors, gaps, or inconsistencies in the risk analysis, and to improve the risk analysis skills and knowledge of the reviewers and the reviewees. References = CRISC Review Manual1, page 209.
An organization ' s IT team has proposed the adoption of cloud computing as a cost-saving measure for the business. Which of the following should be of GREATEST concern to the risk practitioner?
Due diligence for the recommended cloud vendor has not been performed.
The business can introduce new Software as a Service (SaaS) solutions without IT approval.
The maintenance of IT infrastructure has been outsourced to an Infrastructure as a Service (laaS) provider.
Architecture responsibilities may not be clearly defined.
The lack of due diligence for the recommended cloud vendor should be of greatest concern to the risk practitioner, because it exposes the organization to potential risks and issues related to the security, reliability, performance, and compliance of the cloud service provider. Due diligence is a process of conducting a thorough investigation and evaluation of a potential vendor or partnerbefore entering into a contractual relationship. Due diligence helps to verify the vendor’s credentials, capabilities, reputation, and track record, and to identify any red flags or gaps that may affect the quality or suitability of the service. Cloud computing is a model of delivering IT services over the internet, where the service provider owns and manages the IT infrastructure, platforms, or applications, and the customer pays only for the resources or functions they use. Cloud computing can offer cost savings, scalability, and flexibility for the business, but it also introduces new risks and challenges, such as data privacy, security breaches, vendor lock-in, service outages, or regulatory compliance. Therefore, performing due diligence for the recommended cloud vendor is essential to ensure that the organization’s expectations and requirements are met, and that the risks and issues are identified and addressed. The business introducing new SaaS solutions without IT approval, the maintenance of IT infrastructure being outsourced to an IaaS provider, and the architecture responsibilities not being clearly defined are all possible concerns for the risk practitioner, but they are not the greatest concern, as they can bemitigated or resolved with appropriate controls, policies, or agreements. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.1, page 183
Which of the following provides the MOST useful information to assess the magnitude of identified deficiencies in the IT control environment?
Peer benchmarks
Internal audit reports
Business impact analysis (BIA) results
Threat analysis results
Internal audit reports provide the most useful information to assess the magnitude of identified deficiencies in the IT control environment. Internal audit reports are independent and objective evaluations of the design and operating effectiveness of the IT controls, as well as the compliance with policies, standards, and regulations. Internal audit reports also provide recommendations for improvement and follow-up actions for the control deficiencies. Internal audit reports can help measure the impact and severity of the control deficiencies, and prioritize the remediation efforts. Peer benchmarks, business impact analysis (BIA) results, and threat analysis results are not as directly related to the assessment of the control deficiencies, although they may provide some contextual or comparative information. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.4.1, page 1-19.
To help ensure the success of a major IT project, it is MOST important to:
obtain the appropriate stakeholders ' commitment.
align the project with the IT risk framework.
obtain approval from business process owners.
update the risk register on a regular basis.
Which of the following is the MOST important course of action to foster an ethical, risk-aware culture?
Implement a fraud detection and prevention framework.
Ensure the alignment of the organization ' s policies and standards to the defined risk appetite.
Establish an enterprise-wide ethics training and awareness program.
Perform a comprehensive review of all applicable legislative frameworks and requirements.
According to the CRISC Review Manual, an enterprise-wide ethics training and awareness program is one of the key elements of a strong risk culture, as it helps to promote ethical behavior, raise awareness of risk management principles and practices, and foster a culture of accountability and transparency2
1: Developing Collective Risk Leadership Through CRISC - ISACA 2: CRISC Review Manual, 7th Edition, page 23
Which of the following is MOST important when considering risk in an enterprise risk management (ERM) process?
Financial risk is given a higher priority.
Risk with strategic impact is included.
Security strategy is given a higher priority.
Risk identified by industry benchmarking is included.
According to the ISACA CRISC Review Manual, an enterprise risk management (ERM) process is a holistic approach to identifying, analyzing, responding to, and monitoring all types of risk that affect the achievement of the enterprise’s objectives. The ERM process should consider all types of risk, including strategic, operational, financial, compliance, and reputational risks. Among these, strategic risks are the most important, as they have the potential to affect the enterprise’s mission, vision, and goals. Therefore, risk with strategic impact should be includedin the ERM process. References = ISACA CRISC Review Manual, 7th Edition, Chapter 1, Section 1.2.1, page 17.
Which of the following BEST indicates the risk appetite and tolerance level (or the risk associated with business interruption caused by IT system failures?
Mean time to recover (MTTR)
IT system criticality classification
Incident management service level agreement (SLA)
Recovery time objective (RTO)
The best indicator of the risk appetite and tolerance level for the risk associated with business interruption caused by IT system failures is the recovery time objective (RTO). The RTO is the maximum acceptable time or duration that a business process or an IT system can be disrupted or interrupted before it causes unacceptable impact or harm to the business. The RTO reflects the risk appetite and tolerance level for thebusiness interruption risk, as it indicates how much disruption or interruption the business can tolerate or accept, and how quickly the business needs to resume or recover the business process or the IT system. The RTO also helps to determine the priorities and requirements for the business continuity and recovery planning, and to select and implement the appropriate continuity and recovery strategies and solutions. Mean time to recover(MTTR), IT system criticality classification, and incident management service level agreement (SLA) are not the best indicators of the risk appetite and tolerance level for the business interruption risk, as they are either the measures or the outcomes of the business continuity and recovery performance, and they do not directly indicate how much disruption or interruption the business can tolerate or accept. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 50
An organization has asked an IT risk practitioner to conduct an operational risk assessment on an initiative to outsource the organization ' s customer service operations overseas. Which of the following would MOST significantly impact management ' s decision?
Time zone difference of the outsourcing location
Ongoing financial viability of the outsourcing company
Cross-border information transfer restrictions in the outsourcing country
Historical network latency between the organization and outsourcing location
The most significant factor that would impact management’s decision when conducting an operational risk assessment on an initiative to outsource the organization’s customer service operations overseas is the cross-border information transfer restrictions in the outsourcing country. Cross-border information transfer restrictions are the laws, regulations, standards, or contracts that govern the collection, processing, storage, or transmission of information across national or regional boundaries. Cross-border information transfer restrictions may affect the organization’s outsourcing initiative, because they may impose limitations, obligations, or penalties on the organization or the outsourcing company, such as requiring consent, notification, or authorization, or prohibiting or restricting certain types or categories of information. Cross-border information transfer restrictions may also create challenges or risks for the organization’s outsourcing initiative, such as compliance, legal, reputational, or operational risks, or conflicts orinconsistencies with the organization’s own policies, regulations, standards, or contracts. The other options are not as significant as the cross-border information transfer restrictions, although they may also pose some difficulties or limitations for the organization’s outsourcing initiative. Time zone difference of the outsourcing location, ongoing financial viability of the outsourcing company, and historical network latency between the organization and outsourcing location are all factors that could affect the efficiency and effectiveness of the outsourcing initiative, but they do not directly affect the legality or security of the outsourcing initiative. References = 3
Which of the following is the MOST important update for keeping the risk register current?
Modifying organizational structures when lines of business merge
Adding new risk assessment results annually
Retiring risk scenarios that have been avoided
Changing risk owners due to employee turnover
Understanding the Question:
The question asks what the most important update for keeping the risk register current is.
Analyzing the Options:
A. Modifying organizational structures when lines of business merge:Reflects significant changes in the organization that impact risk profiles.
B. Adding new risk assessment results annually:Important but periodic.
C. Retiring risk scenarios that have been avoided:Necessary but not as impactful as major organizational changes.
D. Changing risk owners due to employee turnover:Important but secondary to major structural changes.
Organizational Changes:When lines of business merge, it can significantly alter the risk landscape, introducing new risks and changing the impact and likelihood of existing ones. Updating the risk register to reflect these changes is crucial for accurate risk management.
Impact on Risk Profiles:Mergers and acquisitions can affect every aspect of an organization, from operational processes to regulatory compliance, making it essential to update the risk register accordingly.
Which of the following should be the PRIMARY consideration when assessing the automation of control monitoring?
impact due to failure of control
Frequency of failure of control
Contingency plan for residual risk
Cost-benefit analysis of automation
Automation of control monitoring is the application of technology to allow continuous or high-frequency, automated monitoring of controls to validate the effectiveness of controls designed to mitigate risk1.
Automation of control monitoring can provide benefits such as increased test coverage, improved timeliness, reduced risk velocity, greater visibility, improved consistency, and the ability to identify trends23.
However, automation of control monitoring also involves costs such as the acquisition, implementation, maintenance, and updating of the technology, as well as the training and support of the staff who use it45.
Therefore, the primary consideration when assessing the automation of control monitoring is the cost-benefit analysis of automation, which compares the expected benefits and costs of automation and determines whether the benefits outweigh the costs or vice versa45.
The other options are not the primary consideration, but rather secondary or tertiary factors that may influence the decision to automate or not. For example, the impact due to failure of controland the frequency of failure of control are aspects of the risk assessment that may indicatethe need for automation, but they do not provide the basis for evaluating the feasibility and desirability of automation45. Similarly, the contingency plan for residual risk is a component of the risk response that may include automation as a risk mitigation strategy, but it does not measure the effectiveness and efficiency of automation45. References =
2: A Practical Approach to Continuous Control Monitoring, ISACA Journal, Volume 2, 2015
3: Continuous Controls Monitoring: The Next Generation Of Controls Testing, Forbes Technology Council, June 2, 2022
1: Making Continuous Controls Monitoring Work for Everyone, ISACA Now Blog, June 13, 2022
4: Controls Automation - Monitoring vs. Operation - Part 3, Turnkey Consulting, July 29, 2021
5: What’s Continuous Control Monitoring and Why Is It Important?, MetricStream Blog, October 15, 2019
When processing personal information which of the following BEST helps to mitigate privacy risk while still enabling testing?
Data classification
Data sanitization
Data encryption
Data anonymization
The correct answer is D because data anonymization best mitigates privacy risk while still enabling testing. It allows the organization to use realistic data sets for development or testing purposes without exposing identifiable personal information. This supports business needs while reducing the chance of privacy violations.
The other options are less effective for this specific purpose:
A. Data classification helps determine protection requirements, but it does not by itself make the data safe for testing.
B. Data sanitization can remove sensitive data, but anonymization is the more direct privacy-preserving method for retaining usable test data.
C. Data encryption protects data from unauthorized access, but the data remains personal information once decrypted for testing.
Exact Extracts supporting the answer:
“A privacy impact assessment can help enterprises weigh the benefits of their data processing activities against risk to determine the appropriate response.”
“The MAIN benefit of information classification is that it helps select security measures proportional to risk.”
“To determine the level of protection required for securing personally identifiable information a risk practitioner should PRIMARILY consider the sensitivity property of the information.”
“The MOST important principle of data protection that a risk practitioner should advocate for is that data should be accurate.”
These extracts support that personal information should be processed in a way that reduces privacy risk while preserving appropriate business use. For testing, data anonymization is the best answer.
===========
QUESTION NO: 101 [Risk Assessment]
Which of the following is the FIRST step in a risk assessment process?
A. Identifying risk owners
B. Documenting vulnerabilities
C. Assessing the likelihood of threats
D. Identifying assets
Answer: D
The correct answer is D because the first step in a risk assessment process is identifying assets . Before vulnerabilities can be documented, threats assessed, or owners assigned, the organization must first know what systems, data, applications, infrastructure, or business resources are in scope for the assessment.
The other options come later in the process:
A. Identifying risk owners follows once the assets, processes, and risks are understood.
B. Documenting vulnerabilities requires prior understanding of the assets being assessed.
C. Assessing the likelihood of threats also occurs after assets and scenarios have been identified.
Exact Extracts supporting the answer:
“The FIRST step in identifying and assessing IT risk is to gather information on the current and future environment.”
“The PRIMARY reason for determining the security boundary prior to conducting a risk assessment is to identify the scope of the risk assessment.”
“Understanding the system and its subsystems is the MOST effective method to conduct a risk assessment on an internal system in an enterprise.”
“Risk assessment is the risk management activity that initially identifies critical business functions and key business risk.”
These extracts support that risk assessment begins with understanding the environment and scope, which in this question is best represented by identifying assets .
===========
QUESTION NO: 102 [Risk Assessment]
A risk assessment has determined that an organization is highly susceptible to a vulnerability in its IT infrastructure. Which of the following is MOST important to communicate to the board?
A. Results of the most recent penetration test
B. Impact to the organization if the vulnerability is exploited
C. Results of a root cause analysis of the vulnerability
D. Open source intelligence reports on successful attacks
Answer: B
The correct answer is B because the board needs to understand the business impact to the organization if the vulnerability is exploited. The board’s focus is strategic oversight, organizational exposure, and the effect on mission, operations, and enterprise objectives rather than detailed technical findings.
The other options are less appropriate for the board:
A. Results of the most recent penetration test are useful technical evidence, but they are not the most important board-level message.
C. Results of a root cause analysis of the vulnerability are more useful for management and remediation teams.
D. Open source intelligence reports on successful attacks may provide context, but the key issue for the board is business impact.
Exact Extracts supporting the answer:
“IT risk is measured by its impact on business operations.”
“The primary reason risk professionals conduct risk assessments is to identify risk with the highest business impact.”
“The board of directors is accountable for overall enterprise strategy for risk governance.”
“Dashboards are MOST suitable for reporting IT-related business risk to senior management.”
These extracts support that board communication should focus on business impact. Therefore, the most important thing to communicate is the impact to the organization if the vulnerability is exploited .
===========
QUESTION NO: 103 [Governance]
Which of the following is MOST important for ensuring anonymous reporting of non-compliant activity?
A. Establishing an employee feedback channel
B. Establishing a dedicated compliance function
C. Implementing an incentive program
D. Implementing homomorphic encryption
Answer: A
The correct answer is A because the most important factor for ensuring anonymous reporting of non-compliant activity is a trusted employee feedback/reporting channel . Anonymous reporting depends on having a practical and secure method for individuals to raise concerns without exposing their identity.
The other options are less suitable:
B. Establishing a dedicated compliance function may support oversight, but does not by itself enable anonymous reporting.
C. Implementing an incentive program may encourage reporting, but it does not ensure anonymity.
D. Implementing homomorphic encryption is not the practical organizational control needed for anonymous misconduct reporting.
Exact Extracts supporting the answer:
“The greatest benefit of a risk-aware culture is that issues are escalated when suspicious activity is noticed.”
“The best proactive approach for practicing professional ethics within an enterprise is to provide ethics awareness training.”
“The most effective way to support adherence to an enterprise ' s code of ethics is by ensuring periodic training evaluation and attestation of employees.”
“Developing and practicing ethical behavior within an enterprise contributes the most to building the risk culture.”
These extracts support that issues should be escalated and reported. The most important mechanism for anonymous reporting is establishing an employee feedback channel .
===========
QUESTION NO: 104 [Risk Response and Mitigation]
Which of the following is MOST important to document when accepting risk?
A. Risk owner
B. Risk identification date
C. Risk mitigation date
D. Risk impact level
Answer: A
The correct answer is A because when accepting risk, the most important item to document is the risk owner . Risk acceptance must be tied to clear accountability. The organization must know who has the authority to accept the risk and who remains accountable for monitoring and managing it afterward.
The other options are important supporting details, but not the most important:
B. Risk identification date is useful for tracking, but not as critical as accountability.
C. Risk mitigation date may not apply if the risk is being accepted rather than mitigated.
D. Risk impact level is important to understand the risk, but acceptance must ultimately be assigned to an accountable owner.
Exact Extracts supporting the answer:
“Accountability for a risk treatment plan lies with the risk owner.”
“The PRIMARY objective of risk reporting is to provide the risk owner with information to initiate risk response.”
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“During the risk assessment process it is most important to establish a clear line of accountability to ensure that risk ownership is assigned to the appropriate level.”
These extracts directly support that risk acceptance must be tied to documented accountability. Therefore, the most important item to document is the risk owner .
===========
QUESTION NO: 105 [Risk and Control Monitoring and Reporting]
Which of the following is the MOST effective way for an organization to track emerging risk?
A. Conduct peer benchmarking
B. Adjust the risk taxonomy
C. Capture it in the risk register
D. Re-perform relevant risk assessments
Answer: C
The correct answer is C because the most effective way to track emerging risk is to capture it in the risk register . The risk register is the primary enterprise tool for documenting identified risks, their status, ownership, mitigation actions, and ongoing changes over time. Once an emerging risk is identified, placing it in the risk register ensures it can be monitored, communicated, prioritized, and acted upon.
The other options are less effective as the primary tracking mechanism:
A. Conduct peer benchmarking may provide context, but it does not serve as the formal internal tracking tool.
B. Adjust the risk taxonomy may help classification, but not active tracking of a specific emerging risk.
D. Re-perform relevant risk assessments may be necessary later, but the first and most effective way to track the risk is to record it formally.
Exact Extracts supporting the answer:
“The risk register is the best tool for identifying changes in an enterprise’s risk profile.”
“The MAIN reason an enterprise maintains a risk register is to act as a repository of identified risk for decision-making.”
“The BEST tool for documenting the status of risk mitigation and risk ownership at the enterprise level is the risk register.”
“An emerging risk should be added to the risk register by the risk practitioner when the activity that triggers the risk initiates.”
“An updated risk register ensures effective prioritization and treatment of risk.”
These extracts directly support that emerging risk should be formally documented and tracked through the risk register .
Which of the following techniques is MOST helpful when quantifying the potential loss impact of cyber risk?
Cost-benefit analysis
Penetration testing
Business impact analysis (BIA)
Security assessment
Understanding Business Impact Analysis (BIA):
BIA is a process used to identify and evaluate the potential effects (impact) of interruptions to critical business operations as a result of a disaster, accident, or emergency.
It helps quantify the potential loss impact of cyber risks by assessing the financial and operational consequences of disruptions.
Quantifying Loss Impact:
BIA involves determining the value of business processes and the impact of their loss. This includes evaluating factors such as revenue loss, additional operational costs, legal penalties, and reputational damage.
By analyzing the criticality of business functions and their dependencies, BIA provides a detailed understanding of potential impacts, aiding in the development of risk mitigation strategies.
Comparing Other Techniques:
Cost-Benefit Analysis:Useful for evaluating the cost-effectiveness of controls but does not provide a comprehensive assessment of potential loss impacts.
Penetration Testing:Identifies vulnerabilities but does not quantify the business impact of exploiting those vulnerabilities.
Security Assessment:Evaluates security controls but is not focused on the broader business impact of potential disruptions.
References:
The CRISC Review Manual emphasizes the role of BIA in assessing the impact of risks on business operations and quantifying potential losses (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.7 Business Impact Analysis).
Which of me following is MOST helpful to mitigate the risk associated with an application under development not meeting business objectives?
Identifying tweets that may compromise enterprise architecture (EA)
Including diverse Business scenarios in user acceptance testing (UAT)
Performing risk assessments during the business case development stage
Including key stakeholders in review of user requirements
The most helpful way to mitigate the risk associated with an application under development not meeting business objectives is to include key stakeholders in the review of user requirements, because this ensures that the application is designed and developed according to the needs and expectations of the end users and the business owners. Including key stakeholders in the review of user requirements also helps to avoid scope creep, requirement changes, or miscommunication that may affect the quality, functionality, or usability of the application. The other options are not the most helpful ways to mitigate the risk, although they may also be useful in reducing the likelihood or impact of the risk. Identifying threats that may compromise enterprise architecture (EA), including diverse business scenarios in user acceptance testing (UAT), and performing risk assessments during the business case development stage are examples of preventive or detective controls that aim to identify and address the potential issues or problems that may arise during the application development process, but they do not address the alignment of the applicationwith the business objectives. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Which of the following is the MOST important information to be communicated during security awareness training?
Management ' s expectations
Corporate risk profile
Recent security incidents
The current risk management capability
The most important information to be communicated during security awareness training is management’s expectations. This will help to establish the security culture and behavior of the enterprise, and to align the staff’s actions with the enterprise’s objectives, policies, and standards. Management’s expectations also provide the basis for measuring and evaluating the effectiveness of the security awareness program. Corporate risk profile, recent security incidents, and the current risk management capability are also important information to be communicated during security awareness training, but they are not as important as management’s expectations. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.1.1.2, page 2291
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 642.
Which of the following is the result of a realized risk scenario?
Technical event
Threat event
Vulnerability event
Loss event
The result of a realized risk scenario is a loss event. A loss event is an occurrence that causes harm or damage to the organization’s assets, resources, or reputation. A loss event is also known as an incident or a breach. A loss event is the outcome of a risk scenario, which is a description of a possible situation or event that could affect the organization’s objectives or operations. A risk scenario consists of three elements: a threat, a vulnerability, and an impact. A threat is a potential source of harm or damage. A vulnerability is a weakness or flaw that could be exploited by a threat. An impact is the consequence or effect of a threat exploiting a vulnerability. A risk scenario is realized when a threat exploits a vulnerability and causes an impact, which results in a loss event. The other options are not the result of a realized risk scenario, although they may be part of a risk scenario. A technical event, a threat event, and a vulnerability event are all types of events that could occur in a risk scenario, but they are not the final outcome or result of a risk scenario. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
Which of the following should be the risk practitioner s FIRST course of action when an organization has decided to expand into new product areas?
Identify any new business objectives with stakeholders.
Present a business case for new controls to stakeholders.
Revise the organization ' s risk and control policy.
Review existing risk scenarios with stakeholders.
The first course of action for the risk practitioner when an organization has decided to expand into new product areas is to identify any new business objectives with stakeholders. Business objectives are the specific, measurable, achievable, relevant, and time-bound (SMART) goals that the organization aims to accomplish through its products and services. Stakeholders are the parties who have an interest or influence in the organization and its products and services, such as customers, employees, shareholders, suppliers, regulators, or competitors. Identifying any new business objectives with stakeholders is the first course of action, because it helps to understand and define the purpose, scope, and criteria of the new product areas, and to align them with the organization’s vision, mission, and strategy. Identifying any new business objectives with stakeholders also helps to establish the expectations, needs, and requirements of the stakeholders, and to ensure their engagement and support for the new product areas. Identifying any newbusiness objectives with stakeholders is the basis for the subsequent risk management activities, such as identifying, analyzing, evaluating, and responding to the risks associated with the new product areas. The other options are not the first course of action, although they may be related or subsequent steps in the risk management process. Presenting a business case for new controls to stakeholders is a part of the risk response process, which involves selecting and executing the appropriate actions to reduce, avoid, share, or exploit the risks associated with the new product areas. Presenting a business case for new controls to stakeholders can help to justify and communicate the value and impact of the new controls, and to obtain the approval and resources for implementing them. However, this is not the first course of action, as it depends on the identification and prioritization of the business objectives and the risks. Revising the organization’s risk and control policy is a part of the risk governance process, which involves defining and updating the rules and guidelines for managing the risks and the controls associatedwith the new product areas. Revising the organization’s risk and control policy can help to ensure the consistency and effectiveness of the risk management process, and to comply with the relevant laws and regulations. However, this is not the first course of action, as it follows the identification and assessment of the business objectives and the risks. Reviewing existing risk scenarios with stakeholders is a part of the risk monitoring and review process, which involves evaluating and improving the performance and outcomes of the risk management process for the new product areas. Reviewing existing risk scenarios with stakeholders can help to identify and address any changes or issues in the risk levels or the risk responses, and to provide feedback and learning for the risk management process. However, this is not the first course of action, as it requires the identification and analysis of the business objectives and the risks. References = Risk Scenarios Toolkit - ISACA, How to Write Strong Risk Scenarios and Statements - ISACA, The Role of Executive Management in ERM - Corporate Compliance Insights
To enable effective integration of IT risk scenarios and ERM, it is MOST important to have a consistent approach to reporting:
Risk impact and likelihood
Risk velocity
Key risk indicators (KRIs)
Risk response plans and owners
Aconsistent approach to reporting risk impact and likelihoodis essential for integrating IT risk into the broader enterprise risk management (ERM) framework. It allows for proper aggregation and alignment, ensuring IT risks are understood in context with overall enterprise risk.
===========
Which of the following BEST indicates the effective implementation of a risk treatment plan?
Inherent risk is managed within an acceptable level.
Residual risk is managed within appetite and tolerance.
Risk treatments are aligned with industry peers.
Key controls are identified and documented.
The effective implementation of a risk treatment plan is best indicated by managing residual risk within the organization’s appetite and tolerance levels. Residual risk is the remaining risk aftercontrols have been applied, and ensuring it is within acceptable levels demonstrates that the risk treatment plan is effective.
Managing Residual Risk within Appetite and Tolerance (Answer B):
Definition: Residual risk is the risk remaining after risk treatment measures have been implemented.
Significance: Managing residual risk within the set appetite and tolerance levels shows that the implemented controls are effective and aligned with the organization’s risk management objectives.
Outcome: It ensures that the organization ' s risk exposure is kept within acceptable boundaries, thereby protecting its assets and operations.
Comparison with Other Options:
A. Inherent risk is managed within an acceptable level:
Definition: Inherent risk is the risk before any controls are applied.
Limitation: The focus should be on residual risk post-treatment.
C. Risk treatments are aligned with industry peers:
Purpose: While benchmarking is useful, it does not directly indicate the effectiveness of risk treatment.
D. Key controls are identified and documented:
Purpose: Identifying and documenting controls is necessary, but effectiveness is shown by managing residual risk.
Which of the following is the BEST indication that an organization ' s risk management program has not reached the desired maturity level?
Significant increases in risk mitigation budgets
Large fluctuations in risk ratings between assessments
A steady increase in the time to recover from incidents
A large number of control exceptions
A risk management program is a set of processes, policies, and tools that enable an enterprise to identify, analyze, evaluate, treat, monitor, and communicate its risks. The maturity level of a risk management program indicates how well the program is integrated, standardized, and aligned with the enterprise’s objectives, culture, and values. The best indication that an organization’s risk management program has not reached the desired maturity level is large fluctuations in risk ratings between assessments. Risk ratings are the measures of the impact and likelihood of the risks, and they should be consistent and comparable across the enterprise and over time. Large fluctuations in risk ratings between assessments suggest that the risk management program is not stable, reliable, or effective, and that the risk identification and analysis methods are not robust, accurate, or transparent. The other options are not as indicative of the maturity level of the riskmanagement program, as they involve different aspects or outcomes of the risk management program:
Significant increases in risk mitigation budgets means that the enterprise is spending more resources on implementing risk responses, such as controls, policies, or procedures. This may indicate that the enterprise is facing more or higher risks, or that the risk responses are more costly or complex, but it does not necessarily reflect the maturity level of the risk management program, as it may also depend on the enterprise’s risk appetite, tolerance, and strategy.
A steady increase in the time to recover from incidents means that the enterprise is taking longer to restore its normal operations after a disruption or a loss. This may indicate that the enterprise is not prepared or resilient enough to deal with the incidents, or that the incidents are more frequent or severe, but it does not necessarily reflect the maturity level of the risk management program, as it may also depend on the nature and source of the incidents, or the availability and effectiveness of the recovery plans.
A large number of control exceptions means that the enterprise is deviating from the established controls, policies, or procedures, either intentionally or unintentionally. This may indicate that the enterprise is not complying with the risk management program, or that the controls are not adequate or appropriate for the enterprise’s needs, but it does not necessarily reflect the maturity level of the risk management program, as it may also depend on the reasons and justifications for the exceptions, or the approval and monitoring processes for the exceptions. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.1.3.1, pp. 14-15.
When a risk practitioner is determining a system ' s criticality. it is MOST helpful to review the associated:
process flow.
business impact analysis (BIA).
service level agreement (SLA).
system architecture.
The most helpful information to review when determining a system’s criticality is the associated business impact analysis (BIA). A BIA is a process of identifying and evaluating the potential effects of disruptions to the organization’s critical business functions and processes. A BIA can help to determine the system’s criticality by assessing its impact on the organization’s objectives, performance, and value. Process flow, service level agreement (SLA), and system architecture are other possible information sources, but they are not as helpful as the BIA. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 4; CRISC Review Manual, 6th Edition, page 153.
From a risk management perspective, which of the following is the PRIMARY benefit of using automated system configuration validation tools?
Residual risk is reduced.
Staff costs are reduced.
Operational costs are reduced.
Inherent risk is reduced.
From a risk management perspective, the primary benefit of using automated system configuration validation tools is that they reduce the inherent risk, which is the risk that exists before any controls are applied. Automated system configuration validation tools can help to ensure that the system settings are consistent, compliant, and secure, and that they match the predefined standards and policies. This can reduce the likelihood and impact of errors, misconfigurations, vulnerabilities, or deviations that may compromise the system’s functionality, performance, or integrity. The other options are not the primary benefits of using automated system configuration validation tools, although they may be secondary benefits or outcomes of doing so. Residual risk is the risk that remains after the controls are applied, and it may not be directly affected by the automated system configuration validation tools. Staff costs and operational costs are related to the efficiency and economy of the system configuration process, but they are not the main risk management objectives. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk Response, page 150.
An insurance company handling sensitive and personal information from its customers receives a large volume of telephone requests and electronic communications daily. Which of the following
is MOST important to include in a risk awareness training session for the customer service department?
Archiving sensitive information
Understanding the incident management process
Identifying social engineering attacks
Understanding the importance of using a secure password
Social engineering attacks are attempts to manipulate or deceive people into revealing confidential or personal information, such as passwords, account numbers, or security codes. Customer service representatives are often targeted by social engineering attacks, as they have access to sensitive customer data and may be pressured to provide quick and satisfactory service. Therefore, it is most important to include in a risk awareness training session for the customer service department how to identify and prevent social engineering attacks, such as phishing, vishing, baiting, or impersonation.
References
•The role of customer service in cybersecurity - Security Intelligence
•How to Improve Risk Awareness in the Workplace [+ Template] - AlertMedia
•Top 4 Risks For Customer Service Teams | Resolver
Determining if organizational risk is tolerable requires:
mapping residual risk with cost of controls
comparing against regulatory requirements
comparing industry risk appetite with the organizations.
understanding the organization ' s risk appetite.
Determining if organizational risk is tolerable requires understanding the organization’s risk appetite, which is the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives1. Understanding the organization’s risk appetite can help to:
Define and communicate the risk tolerance, which is the acceptable or unacceptable level of risk for each risk category or scenario2.
Guide and align the risk identification, analysis, evaluation, and treatment processes, and ensure that the risks are consistent and proportional to the risk appetite3.
Measure and monitor the risk performance and outcome, and ensure that the residual risk (the risk that remains after the risk responses) is within the risk appetite, or take corrective actions if needed4.
The other options are not the best ways to determine if organizational risk is tolerable, because:
Mapping residual risk with cost of controls is a useful but not sufficient way to determine if organizational risk is tolerable, as it provides a quantitative analysis of the trade-off between the risk level and the risk response cost5. However, mapping residual risk with cost of controls does not consider the qualitative aspects of the risk, such as the impact on the organization’s strategy, culture, or reputation.
Comparing against regulatory requirements is a necessary but not sufficient way to determine if organizational risk is tolerable, as it ensures that the organization complies with the applicable laws, rules, or standards that govern its activities and operations6. However, comparing against regulatory requirements does not guarantee that the organization meets its own objectives and expectations, which may be higher or lower than the regulatory requirements.
Comparing industry risk appetite with the organization’s risk appetite is a helpful but not sufficient way to determine if organizational risk is tolerable, as it provides a reference or a standard for benchmarking the organization’s risk level and performance with its peers or competitors7. However, comparing industry risk appetite with the organization’s risk appetitedoes not ensure that the organization addresses its specific or unique risks, which may differ from the industry risks.
References =
Risk Appetite - CIO Wiki
Risk Tolerance - CIO Wiki
Risk Management Process - CIO Wiki
Risk Monitoring - CIO Wiki
Residual Risk - CIO Wiki
Regulatory Compliance - CIO Wiki
Benchmarking - CIO Wiki
Risk and Information Systems Control documents and learning resources by ISACA
Which of the following BEST represents a critical threshold value for a key control indicator (KCI)?
The value at which control effectiveness would fail
Thresholds benchmarked to peer organizations
A typical operational value
A value that represents the intended control state
A critical threshold value for a key control indicator (KCI) is the value that indicates that the control is no longer performing its intended function of mitigating a risk. If the KCI reaches or exceeds this value, it means that the control effectiveness has failed and corrective actions are needed. The other options are not the best representations of a critical threshold value for a KCI, because they do not reflect the actual performance or outcome of the control. Thresholds benchmarked to peer organizations, a typical operational value, and a value that represents the intended control state are examples of target or acceptable values for a KCI, not critical or unacceptable values. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
A risk owner has accepted a high-impact risk because the control was adversely affecting process efficiency. Before updating the risk register, it is MOST important for the risk practitioner to:
ensure suitable insurance coverage is purchased.
negotiate with the risk owner on control efficiency.
reassess the risk to confirm the impact.
obtain approval from senior management.
A risk owner is the individual who is accountable for the management of a specific risk. A risk owner can decide to accept a high-impact risk if the control that mitigates the risk is adversely affecting the process efficiency. However, before updating the risk register, which is a document that records and tracks the identified risks and their responses, it is most important for the risk practitioner to obtain approval from senior management. Senior management is the group of executives who have the authority and responsibility for the strategic direction and performance of the organization. Obtaining approval from senior management can help ensure that the risk acceptance decision is aligned with the organization’s risk appetite and policies, and that the potential consequences of the high-impact risk are understood and accepted by the top-level decision makers. Obtaining approval from senior management can also help communicate and justify the risk acceptance decision to other stakeholders, such as regulators, auditors, customers, etc., and avoid any conflicts or misunderstandings that may arise from the risk acceptance decision. References = Why Assigning a Risk Owner is Important and How to Do It Right, Risk Ownership: A brief guide, Creating a Risk Register: All You Need to Know.
Which of the following is the MOST appropriate key performance indicator (KPI) to measure change management performance?
Percentage of changes implemented successfully
Percentage of rejected change requests
Number of after-hours emergency changes
Number of change control requests
Thepercentage of successfully implemented changesdirectly reflects the effectiveness and stability of the change management process. It measures whether changes achieve intended results without disruption.
To ensure key risk indicators (KRIs) are effective and meaningful, the KRIs should be aligned to:
A control framework
Industry standards
Capability maturity targets
Business processes
KRIs must be aligned to business processes to ensure they reflect actual risk conditions affecting critical operations. Misalignment can lead to inaccurate monitoring and ineffective response.
If concurrent update transactions to an account are not processed properly, which of the following will MOST likely be affected?
Confidentiality
Accountability
Availability
Integrity
Integrity is the property of data that ensures its accuracy, completeness, and consistency2. If concurrent update transactions to an account are not processed properly, the integrity of the data may be compromised, as it may lead to concurrency problems such as lost update, unrepeatable read, or phantom read3. These problems can cause the data to be incorrect, incomplete, or inconsistent, which may affect the reliability and validity of the data. Therefore, option D is the correct answer, as it reflects the impact of improper concurrent update transactions on the data integrity. The other options are not correct, as they do not directly relate to the effect of concurrent update transactions on the data. Option A, confidentiality, is the property of data that ensures its protection from unauthorized access or disclosure2. Concurrent update transactions do not necessarily affect the confidentiality of the data, as they do not involve exposing the data to unauthorized parties. Option B, accountability, is the property of data that ensures its traceability and auditability2. Concurrent update transactions do not necessarily affect the accountability of the data, as they do not involve losing the records or logs of the data transactions. Option C, availability, is the property of data that ensures its accessibility and usability2. Concurrent update transactions do not necessarily affect the availability of the data, as they do not involve preventing the access or use of the data.
An organization recently implemented an automated interface for uploading payment files to its banking system to replace manual processing. Which of the following elements of the risk register is MOST appropriate for the risk practitioner to update to reflect the improved control?
Risk scenarios
Risk ownership
Risk impact
Risk likelihood
Updating the risk likelihood in the risk register is appropriate when an improved control, such as an automated interface, is implemented. This change affects the probability of the risk occurring, thus reflecting the enhanced control environment.
Which of the following is the BEST approach when a risk practitioner has been asked by a business unit manager for special consideration during a risk assessment of a system?
Conduct an abbreviated version of the assessment.
Report the business unit manager for a possible ethics violation.
Perform the assessment as it would normally be done.
Recommend an internal auditor perform the review.
According to the CRISC Review Manual, performing the assessment as it would normally be done is the best approach when a risk practitioner has been asked by a business unit manager for special consideration during a risk assessment of a system, because it ensures that the risk practitioner maintains their objectivity, integrity, and professionalism. The risk practitioner should not compromise the quality or accuracy of the risk assessment, regardless of any external pressure or influence. The risk practitioner should follow the established risk assessment methodology and standards, and report the risk results and recommendations based on the facts and evidence. The other options are not the best approaches, because they may affect the credibility or reliability of the risk assessment. Conducting an abbreviated version of the assessment may result in incomplete or insufficient risk information, which may lead to poor riskdecisions or actions. Reporting the business unit manager for a possible ethics violation may escalate the situation or create a conflict of interest, which may hinder the risk assessment process or outcome. Recommending an internal auditor perform the review may transfer the responsibility or accountability of the risk practitioner, which may undermine their role or authority. References = CRISC Review Manual, 7th Edition, Chapter 2, Section 2.2.1, page 74.
A risk heat map is MOST commonly used as part of an IT risk analysis to facilitate risk:
communication
identification.
treatment.
assessment.
A risk heat map is a tool that shows the likelihood and impact of different risks on a matrix, using colors to indicate the level of risk. A risk heat map is most commonly used as part of an IT risk analysis to facilitate risk assessment, which is the process of estimating the probability and consequences of the risks, and comparing them against the risk criteria1. A risk heat map can help to visualize, communicate, and prioritize the risks, as well as to evaluate the effectiveness of the risk response actions2. The other options are not the best choices for describing the purpose of a risk heat map, as they are either less specific or less relevant than risk assessment. Risk communication is the process of sharing and exchanging information about the risks among the stakeholders3. A risk heat map can support risk communication by providing a clear and concise representation of the risks, but it is not the main objective of the tool. Riskidentification is the process of finding, recognizing, and describing the risks that may affect the organization4. A risk heat map can help to identify the risks by categorizing them into different domains or sources, but it is not the primary function of the tool. Risk treatment is the process of selecting and implementing the appropriate measures to modify the risk5. A risk heat map can help to guide the risk treatment by showing the risk ratings and thresholds, but it is not the core purpose of the tool. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1, Page 47.
An organization allows programmers to change production systems in emergency situations. Which of the following is the BEST control?
Implementing an emergency change authorization process
Periodically reviewing operator logs
Limiting the number of super users
Reviewing the programmers ' emergency change reports
Implementing an emergency change authorization process is the best control for an organization that allows programmers to change production systems in emergency situations, because it helps to ensure that the changes are justified, approved, documented, and tested before they are implemented, and that they are monitored and reviewed after they are implemented. An emergency change is a change that is required to resolve or prevent a critical issue or incident that may affect the availability, performance, or security of the production systems. A production system is a system that is used to support or enable the operational or business functions or processes of the organization. An emergency change authorization process is a process that defines the roles and responsibilities, criteria and procedures, and tools and techniques for managing and controlling the emergency changes. Implementing an emergency change authorization process is the best control, as it helps to minimize the risks and impacts of theemergency changes, and to maintain the integrity and reliability of the production systems. Periodically reviewing operator logs, limiting the number of super users, and reviewing the programmers’ emergency change reports are all possible controls for an organization that allows programmers to change production systems in emergency situations, but they are not the best control, as they do not provide a comprehensive and consistent approach to the emergency change management. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.4.1, page 208
The effectiveness of a control has decreased. What is the MOST likely effect on the associated risk?
The risk impact changes.
The risk classification changes.
The inherent risk changes.
The residual risk changes.
The most likely effect on the associated risk when the effectiveness of a control has decreased is that the residual risk changes. Residual risk is the risk that remains after the implementation of risk responses or controls. If the control becomes less effective, the residual risk will increase, as the risk exposure and impact will be higher than expected. The risk impact, the risk classification, and the inherent risk are not likely to change when the effectiveness of a control has decreased, as they are more related to the nature and characteristics of the risk, rather than the control performance. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1.4, page 541
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 652.
Which of the following is MOST important to add to the risk register for a remediated risk scenario?
Notification to technical teams of implementation schedules
Sign-off by senior executives
Evidence of successfully implemented controls
Minutes from control design meetings
For closed risks, documented proof that controls are in place and working (e.g., logs, test results) is vital. ISACA’s CRISC Manual emphasizes that evidence is required to validate control effectiveness and support audit requirements
A recent regulatory requirement has the potential to affect an organization ' s use of a third party to supply outsourced business services. Which of the following is the BEST course of action?
Conduct a gap analysis.
Terminate the outsourcing agreement.
Identify compensating controls.
Transfer risk to the third party.
The best course of action when a recent regulatory requirement has the potential to affect an organization’s use of a third party to supply outsourced business services is to conduct a gap analysis, as it involves comparing the current and desired states of compliance, and identifying any gaps or discrepancies that need to be addressed. Terminating the outsourcing agreement, identifying compensating controls, and transferring risk to the third party are not the best courses of action, as they may not be feasible, effective, or appropriate, respectively, and may require the prior knowledge of the compliance gaps and risks. References = CRISC Review Manual, 7th Edition, page 111.
Which of the following is MOST important to the successful development of IT risk scenarios?
Cost-benefit analysis
Internal and external audit reports
Threat and vulnerability analysis
Control effectiveness assessment
IT risk scenarios are hypothetical situations that describe how IT-related risks can affect the organization’s objectives, operations, or assets1. IT risk scenarios help to make IT risk more concrete and tangible, and to enable proper risk analysis and assessment2. IT risk scenarios are developed after IT risks are identified, and are used as inputs for risk analysis, where the frequency and impact of the scenarios are estimated3.
The most important factor to the successful development of IT risk scenarios is threat and vulnerability analysis. Threat and vulnerability analysis is the process of identifying and evaluating the potential sources and causes of IT risks, such as malicious actors, natural disasters, human errors, or technical failures4. Threat and vulnerability analysis can help to:
Define the scope and boundaries of the IT risk scenarios, and ensure that they are relevant and realistic
Identify the critical assets, processes, or functions that are exposed or affected by the IT risks, and assess their value and importance to the organization
Determine the likelihood and methods of the threat events, and the existing or potential weaknesses or gaps in the IT control environment
Estimate the potential consequences and impacts of the IT risks, such as financial losses, operational disruptions, reputational damages, or compliance violations5
References = IT Scenario Analysis in Enterprise Risk Management - ISACA, IT Risk Scenarios - Morland-Austin, Threat and Vulnerability Analysis - Wikipedia, Threat and Vulnerability Analysis - ISACA
Which of the following is the MOST effective way 10 identify an application backdoor prior to implementation ' ?
User acceptance testing (UAT)
Database activity monitoring
Source code review
Vulnerability analysis
A source code review is the process of examining and analyzing the source code of an application to identify any vulnerabilities, errors, or flaws that may compromise the security, functionality, or performance of the application. A source code review is the most effective way to identify an application backdoor prior to implementation, as it can detect any hidden or unauthorized code that may allow unauthorized access, bypass security controls, or execute malicious commands. A source code review can also help to improvethe quality and reliability of the application, and ensure compliance with the coding standards and best practices. References = CRISC Review Manual, 7th Edition, page 181.
Which of the following is MOST important for developing effective key risk indicators (KRIs)?
Engaging sponsorship by senior management
Utilizing data and resources internal to the organization
Including input from risk and business unit management
Developing in collaboration with internal audit
Key risk indicators (KRIs) are metrics used by organizations to monitor and assess potential risks that may impact their objectives and performance. KRIs also provide early warning signals that help organizations identify, analyze, and address risks before they escalate into significant issues1. Effective KRIs are thosethat are relevant, measurable, predictable, comparable, and informational2. The most important factor for developing effective KRIs is including input from risk and business unit management, as they are the persons who have the best understanding of the risk environment, the risk appetite and tolerance, and the risk factors and impacts of the organization. By including input from risk and business unit management, the organization can ensure that the KRIs are aligned with the organization’s strategy, vision, and mission, and that they reflect the current and emerging risks and their potential consequences. Engaging sponsorship by senior management, utilizing data and resources internal to the organization, and developing in collaboration with internal audit are not the most important factors for developing effective KRIs, as they do not provide the same level of insight and relevance as including input from risk and business unit management. Engaging sponsorship by senior management is a factor that involves obtaining the support and approval of the senior leaders who have the authority and accountability for the organization’s performance and governance. Engaging sponsorship by senior management can help to promote the importance and value of KRIs, and to ensure their communication and implementation across the organization, but it does not ensure that the KRIs are appropriate and accurate for the organization’s risk profile. Utilizing data and resources internal to the organization is a factor that involves using the information and assets that are available within the organization to support or enable the development of KRIs. Utilizing data and resources internal to the organization can help to enhance the quality and reliability of KRIs, and to reduce the cost and complexity of obtaining external data and resources, but it does not ensure that the KRIs are comprehensive and consistent with the organization’s risk environment. Developing in collaboration with internal audit is a factor that involves working with the internal audit function that provides independent and objective assurance and advice on the adequacy and effectiveness of the organization’s risk management. Developing in collaboration with internal audit can help to improve the validity and compliance of KRIs, and to provide feedback and recommendations for improvement, but it does not ensure that the KRIs are relevant and realistic for the organization’s risk objectives and strategies. References = 1: Key Risk Indicators: A Practical Guide | SafetyCulture2: KRI Framework for Operational Risk Management | Workiva3: [Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.1: Key Risk Indicators, pp. 181-185.]
A third-party vendor has offered to perform user access provisioning and termination. Which of the following control accountabilities is BEST retained within the organization?
Reviewing access control lists
Authorizing user access requests
Performing user access recertification
Terminating inactive user access
According to the CRISC Review Manual1, authorizing user access requests is the process of granting or denying access to IT resources based on the user’s role, responsibilities, and business needs. Authorizing user access requests is a key control accountability that should be retained within the organization, as it helps to ensure that the principle of least privilege is applied, and that the access rights are aligned with the organization’s policies, standards, and risk appetite. Authorizing user access requests also helps to prevent unauthorized access, data leakage, fraud, and other potential risks associated with user access provisioning and termination. Therefore, the best control accountability to retain within the organizationwhen a third-party vendor offers to perform user access provisioning and termination is authorizing user access requests. References = CRISC Review Manual1, page 240.
During the creation of an organization ' s IT risk management program, the BEST time to identify key risk indicators (KRIs) is while:
Interviewing data owners
Reviewing risk response plans with internal audit
Developing a risk monitoring process
Reviewing an external risk assessment
KRIs should be identified during the development of a risk monitoring process to ensure alignment with organizational objectives and effective risk tracking. This reflectsProactive Risk Monitoring.
Which of the following would BEST help to ensure that identified risk is efficiently managed?
Reviewing the maturity of the control environment
Regularly monitoring the project plan
Maintaining a key risk indicator for each asset in the risk register
Periodically reviewing controls per the risk treatment plan
According to the CRISC Review Manual (Digital Version), periodically reviewing controls per the risk treatment plan would best help to ensure that identified risk is efficiently managed, as it involves verifying the effectiveness and efficiency of the implemented risk response actions and identifying any gaps or changes in the risk profile. Periodically reviewing controls per the risk treatment plan helps to:
Confirm that the controls are operating as intended and producing the desired outcomes
Detect any deviations, errors, or weaknesses in the controls and their performance
Evaluate the adequacy and appropriateness of the controls in relation to the current risk environment and the organization’s risk appetite and risk tolerance
Recommend and implement corrective actions or improvement measures to address any issues or deficiencies in the controls
Update the risk register and the risk treatment plan to reflect the current risk status and the residual risk levels
References = CRISC Review Manual (Digital Version), Chapter 4: IT Risk Monitoring and Reporting, Section 4.1: IT Risk Monitoring, pp. 215-2161
Which of the following provides the MOST helpful information in identifying risk in an organization?
Risk registers
Risk analysis
Risk scenarios
Risk responses
Risk scenarios provide the MOST helpful information in identifying risk in an organization, because they describe the possible events, causes, effects, and impacts of a risk on the organization’s objectives and processes. Risk scenarios help to identify the sources, drivers, and indicators of risk, as well as the potential consequences and likelihood of occurrence. The other options are not as helpful as risk scenarios, because:
Option A: Risk registers are tools to document and track the identified risks, their characteristics, and their status, but they do not provide information on how to identify risks in the first place.
Option B: Risk analysis is a process to assess the likelihood and impact of the identified risks, and to prioritize them based on their severity, but it does not provide information on how to identify risks in the first place.
Option D: Risk responses are actions to address the identified risks, either by reducing, transferring, avoiding, or accepting them, but they do not provide information on how to identify risks in the first place. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 105.
Which of the following is the BEST approach for a risk practitioner to use for identifying the level of technical debt in an organization?
Review business cases for large organizational projects.
Measure the alignment of technical standards with information security policies.
Analyze trends in technology investments over time.
Compare the current state to the target enterprise architecture (EA).
Technical debt is best understood by identifying the gap between current capabilities and the desired future-state architecture. CRISC states that this is done most effectively bycomparing the current environment to the target enterprise architecture (EA). This comparison identifies outdated technologies, unsupported platforms, integration issues, and areas requiring modernization. Reviewing business cases or investment trends provides financial insights but does not quantify technical debt. Comparing standards with policies highlights compliance issues, not architectural deficiencies. EA comparison allows organizations to quantify how far they are from the strategic architectural roadmap, making it the most accurate method.
External auditors have found that management has not effectively monitored key security technologies that support regulatory objectives. Which type of indicator would BEST enable the organization to identify and correct this situation?
Key Performance Indicator (KPI)
Key Management Indicator (KMI)
Key Risk Indicator (KRI)
Key Control Indicator (KCI)
Key Control Indicators (KCIs) measure the performance and effectiveness of controls. When regulatory objectives are tied to technical controls (like firewalls or SIEM), KCIs can detect when those controls are failing or operating outside of thresholds. This allows proactive remediation before compliance violations occur.
Which of the following would be- MOST helpful to understand the impact of a new technology system on an organization ' s current risk profile?
Hire consultants specializing m the new technology.
Review existing risk mitigation controls.
Conduct a gap analysis.
Perform a risk assessment.
A risk assessment is a process of measuring and comparing the likelihood and impact of various risk scenarios, and prioritizing them based on their significance and urgency. A risk assessmentcan help the organization to understand and document the risks that may affect its objectives and operations, and to support the decision making and planning for the risk management.
Performing a risk assessment would be the most helpful to understand the impact of a new technology system on an organization’s current risk profile, because it can help the organization to address the following questions:
What are the potential benefits and challenges of implementing the new technology system, and how do they align with the organization’s objectives and needs?
What are the existing or emerging risks that may affect the new technology system, and how do they relate to the organization’s current risk profile?
How likely and severe are the risks that may affect the new technology system, and what are the possible consequences or impacts for the organization and its stakeholders?
How can the risks that may affect the new technology system be mitigated or prevented, and what are the available or feasible options or solutions?
Performing a risk assessment can help the organization to understand the impact of the new technology system on its current risk profile by providing the following benefits:
It can enable the comparison and evaluation of the current and desired state and performance of the organization’s risk management function, and to identify and quantify the gaps or opportunities for improvement.
It can provide useful references and benchmarks for the alignment and integration of the new technology system with the organization’s risk management function, and for the compliance with the organization’s risk policies and standards.
It can support the implementation and monitoring of the new technology system, and for the allocation and optimization of the resources, time, and budget for the new technology system.
The other options are not the most helpful to understand the impact of a new technology system on an organization’s current risk profile, because they do not provide the same level of detail and insight that performing a risk assessment provides, and they may not be specific or applicable to the organization’s objectives and needs.
Hiring consultants specializing in the new technology means engaging or contracting external experts or professionals that have the skills and knowledge on the new technology system, and that can provide advice or guidance on the implementation and management of the new technology system. Hiring consultants specializing in the new technology can help the organization to enhance its competence and performance on the new technology system, but it is not the most helpful, because it does not measure and compare the likelihood and impact of the risks that may affect the new technology system, and it may not be relevant or appropriate for the organization’s current risk profile.
Reviewing existing risk mitigation controls means examining and evaluating the adequacy and effectiveness of the controls or countermeasures that are intended to reduce or eliminate the risksthat may affect the organization’s objectives and operations. Reviewing existing risk mitigation controls can help the organization to improve and optimize its risk management function, but it is not the most helpful, because it does not identify and prioritize the risks that may affect the newtechnology system, and it may not cover all the relevant or significant risks that may affect the new technology system.
Conducting a gap analysis means comparing and contrasting the current and desired state and performance of the organization’s objectives and operations, and identifying and quantifying the gaps or differences that need to be addressed or corrected. Conducting a gap analysis can help the organization to identify and document its improvement needs and opportunities, but it is not the most helpful, because it does not measure and compare the likelihood and impact of the risks that may affect the new technology system, and it may not be aligned or integrated with the organization’s current risk profile. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 208
CRISC Practice Quiz and Exam Prep
An organization has an approved bring your own device (BYOD) policy. Which of the following would BEST mitigate the security risk associated with the inappropriate use of enterprise applications on the devices?
Periodically review application on BYOD devices
Include BYOD in organizational awareness programs
Implement BYOD mobile device management (MDM) controls.
Enable a remote wee capability for BYOD devices
The best way to mitigate the security risk associated with the inappropriate use of enterprise applications on the BYOD devices is to implement BYOD mobile device management (MDM) controls. MDM controls are software tools or services that allow the organization to remotely manage, monitor, and secure the BYOD devices and the enterprise applications and data on them. MDM controls can help to enforce security policies, restrict unauthorized access, encrypt sensitive data, wipe data in case of loss or theft, and update or patch applications. The other options are not as effective as implementing MDM controls, as they are related to the review, awareness, or recovery of the BYOD devices and applications, not the prevention or protection of the security risk. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
Which of the following BEST facilitates the development of relevant risk scenarios?
Perform quantitative risk analysis of historical data.
Adopt an industry-recognized risk framework.
Use qualitative risk assessment methodologies.
Conduct brainstorming sessions with key stakeholders.
Brainstorming sessions with key stakeholders are the best way to facilitate the development of relevant risk scenarios, as they can generate diverse and creative ideas, perspectives, and insights about the potential risks and their impact on the organization’s objectives and operations. Brainstorming sessions can also foster collaboration, communication, and engagement among the stakeholders, and help to identify and prioritize the most significant and realistic risk scenarios. Brainstorming sessions can be guided by an industry-recognized risk framework, such as ISACA’s Risk IT, and supported by qualitative or quantitative risk assessment methodologies, but they are not sufficient by themselves to develop relevant risk scenarios.
Which of the following should be the FIRST step when a company is made aware of new regulatory requirements impacting IT?
Perform a gap analysis.
Prioritize impact to the business units.
Perform a risk assessment.
Review the risk tolerance and appetite.
New regulatory requirements impacting IT are those that impose new obligations, restrictions, or standards on how an organization uses, manages, or secures its IT systems, data, or services1. Examples of such regulations include the GDPR, the CCPA, the HIPAA, or the PCI-DSS2. New regulatory requirements impacting IT can pose significant challenges and risks for an organization, such as:
Compliance costs and efforts, such as updating policies, procedures, and systems, training staff, or hiring experts
Noncompliance penalties and consequences, such as fines, lawsuits, sanctions, or reputational damages
Operational disruptions or inefficiencies, such as system changes, data migrations, or service interruptions
Competitive disadvantages or opportunities, such as losing or gaining customers, partners, or markets3
The first step that should be done when a company is made aware of new regulatory requirements impacting IT is to review the risk tolerance and appetite. Risk tolerance is the acceptable level of variation that an organization is willing to accept around its risk appetite. Risk appetite is the amount and type of risk that an organization is willing to take in order to meet its strategic objectives. By reviewing the risk tolerance and appetite, the company can:
Establish a clear and consistent understanding of the organization’s goals, values, and expectations regarding the new regulatory requirements impacting IT
Assess the current and potential impacts of the new regulatory requirements impacting IT on the organization’s performance, operations, or assets
Determine the level of risk exposure and acceptance that the organization is comfortable with, and identify the risk thresholds or limits that should not be exceeded
Align the risk management strategies and actions with the organization’s risk tolerance and appetite, and prioritize the most critical and urgent risks to be addressed
Communicate and report the risk tolerance and appetite to the stakeholders and regulators, and ensure transparency and accountability
References = Regulating emerging technology | Deloitte Insights, Ten Key Regulatory Challenges of 2024 - kpmg.com, The Risks of Non-Compliance with Data Protection Laws, [Risk Tolerance - COSO], [Risk Appetite - COSO] , [Risk Appetite and Tolerance - IRM]
A risk practitioner has become aware of production data being used in a test environment. Which of the following should be the practitioner ' s PRIMARY concern?
Sensitivity of the data
Readability of test data
Security of the test environment
Availability of data to authorized staff
Production data is the data that is used in the actual operation of a system or application, such as customer information, financial records, transactions, etc.
Test data is the data that is used in the testing or development of a system or application, such as dummy data, sample data, simulated data, etc.
A risk practitioner has become aware of production data being used in a test environment. This indicates that there is a risk of unauthorized access, use, disclosure, modification, or destruction of the production data, which may affect the confidentiality, integrity, and availability of the data.
The primary concern of the risk practitioner in this situation is the sensitivity of the data. This means that the risk practitioner should assess how valuable, critical, or confidential the data is, and what would be the impact or consequence if the data is compromised or lost.
The sensitivity of the data helps to determine the level of protection and control that is needed to safeguard the data, and the priority and urgency of the risk response actions.
The other options are not the primary concerns of the risk practitioner in this situation. They are either secondary or not essential for data protection.
The references for this answer are:
Risk IT Framework, page 32
Information Technology & Security, page 26
Risk Scenarios Starter Pack, page 24
The BEST way to mitigate the high cost of retrieving electronic evidence associated with potential litigation is to implement policies and procedures for:
data classification and labeling.
data logging and monitoring.
data retention and destruction.
data mining and analytics.
Which of the following is the BEST indicator of the effectiveness of a control monitoring program?
Time between control failure and failure detection
Number of key controls as a percentage of total control count
Time spent on internal control assessment reviews
Number of internal control failures within the measurement period
The effectiveness of a control monitoring program can be measured by how quickly it can detect and correct any control failures that may compromise the achievement of the organization’s objectives. A shorter time between control failure and failure detection means that the control monitoring program is able to identify and report the issues promptly, and initiate the remediation actions accordingly. This can reduce the impact and likelihood of the risks associated with the control failures, and enhance the performance and reliability of the controls. The other options are not as good indicators of the effectiveness of a control monitoring program, because they do not reflect the timeliness and responsiveness of the program, but rather the scope, effort, or frequency of the program. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.3, page 130.
Which of the following is the MOST effective way to help ensure future risk levels do not exceed the organization ' s risk appetite?
Developing contingency plans for key processes
Implementing key performance indicators (KPIs)
Adding risk triggers to entries in the risk register
Establishing a series of key risk indicators (KRIs)
Key Risk Indicators (KRIs)are metrics used to monitor changes in risk exposure, enabling proactive adjustments to keep risks within appetite. They provide early warnings of potential breaches in risk thresholds.
An organization operates in an environment where reduced time-to-market for new software products is a top business priority. Which of the following should be the risk practitioner ' s GREATEST concern?
Sufficient resources are not assigned to IT development projects.
Customer support help desk staff does not have adequate training.
Email infrastructure does not have proper rollback plans.
The corporate email system does not identify and store phishing emails.
In an environment where reduced time-to-market for new software products is a top business priority, the risk practitioner’s greatest concern should be whether sufficient resources are assigned to IT development projects. Resources include human, financial, technical, and physical assets that are needed to plan, design, develop, test, and deliver high-quality software products in a timely manner. If the IT development projects are under-resourced, they may face challenges such as delays, errors, defects, rework, scope creep, or failure to meet customer expectations or requirements. These challenges can increase the risk of losing competitive advantage, market share, customer satisfaction, or reputation. The other options are less critical, as they are not directly related to the core business priority of reducing time-to-market for new softwareproducts. Customer support help desk staff training, email infrastructure rollback plans, and corporate email system phishing detection are important aspects of information security and customer service, but they are not the primary drivers of software product development anddelivery. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.2: Risk Response Options, p. 115-116.
The purpose of requiring source code escrow in a contractual agreement is to:
ensure that the source code is valid and exists.
ensure that the source code is available if the vendor ceases to exist.
review the source code for adequacy of controls.
ensure the source code is available when bugs occur.
According to the How Important Is Source Code Escrow - ISACA article, the purpose of requiring source code escrow in a contractual agreement is to ensure that the source code isavailable if the vendor ceases to exist. Source code escrow is the deposit of the source code of software with a third-party escrow agent, who releases it to the licensee only if certain conditions are met, such as the bankruptcy, merger, or acquisition of the licensor. This arrangement protects the licensee from losing access to the software support and maintenance, and allows them to continue using and modifying the software as needed. Therefore, the answer is B. ensure that the source code is available if the vendor ceases to exist. References = How Important Is Source Code Escrow - ISACA
An organization wants to assess the maturity of its internal control environment. The FIRST step should be to:
validate control process execution.
determine if controls are effective.
identify key process owners.
conduct a baseline assessment.
A baseline assessment is the first step in assessing the maturity of an organization’s internal control environment. A baseline assessment is a comprehensive evaluation of the current state of the internal control structure, processes, and activities across the organization. A baseline assessment helps to identify the strengths and weaknesses of the existing internal controls, as well as the gaps and opportunities for improvement. A baseline assessment also provides a reference point for measuring the progress and effectiveness of the internal control improvement initiatives. The other options are not the first steps in assessing the maturity of an internal control environment, although they may be part of the subsequent steps. Validating control process execution is a technique to verify that the internal control activities are performed as designed and intended. Determining if controls are effective is a process to evaluate the adequacy and efficiency of the internal controls in achieving the desired outcomes and mitigating the risks. Identifying key process owners is a task to assign the roles and responsibilities for the internal control design, implementation, and monitoring to the appropriate individuals or groupswithin theorganization. References = CRISC Review Manual, pages 153-1541; CRISC Review Questions, Answers & Explanations Manual, page 742
Management has noticed storage costs have increased exponentially over the last 10 years because most users do not delete their emails. Which of the following can BEST alleviate this issue while not sacrificing security?
Implementing record retention tools and techniques
Establishing e-discovery and data loss prevention (DLP)
Sending notifications when near storage quota
Implementing a bring your own device 1BVOD) policy
According to the Risk and Information Systems Control documents, implementing record retention tools and techniques is the best solution in this scenario. Record retention involves managing the lifecycle of records, including their creation, usage, storage, and disposal. By implementing record retention policies, organizations can define how long emails and other data should be retained before being deleted. This helps in efficiently managing storage space and reducing unnecessary storage costs.
Establishing e-discovery and data loss prevention (DLP) (Option B) focuses more on legal and compliance aspects and may not directly address the issue of reducing storage costs. Sending notifications when near storage quota (Option C) is a reactive approach and may not prevent the exponential increase in storage costs. Implementing a bring your own device (BYOD) policy (Option D) is unrelated to the issue of email storage costs.
References = Risk and Information Systems Control Study Manual
Legal and regulatory risk associated with business conducted over the Internet is driven by:
the jurisdiction in which an organization has its principal headquarters
international law and a uniform set of regulations.
the laws and regulations of each individual country
international standard-setting bodies.
The legal and regulatory risk associated with business conducted over the Internet is driven by the laws and regulations of each individual country. Legal and regulatory risk is the risk of non-compliance or violation of the applicable laws and regulations that govern the business activities, operations, or transactions. Business conducted over the Internet involves the use of the global network of interconnected computers and devices to exchange information, goods, or services across the geographic boundaries. Business conducted over the Internet may expose the enterprise to various legal and regulatory risks, such as data protection, privacy, security, intellectual property, consumer protection, taxation, or jurisdiction issues. The legal and regulatory risk associated with business conducted over the Internet is driven by the laws and regulations of each individual country, as each country may have different or conflicting laws and regulations that apply to the business conducted over the Internet, and that may change or vary over time. The laws and regulations of each individual country may also impose different or additional obligations, requirements, or restrictions on the enterprise, and may subject the enterprise to different or multiple enforcement actions, penalties, or disputes. The jurisdiction inwhich an organization has its principal headquarters, international law and a uniform set of regulations, and international standard-setting bodies are not the drivers of the legal and regulatory risk associated with business conducted over the Internet, as they do not reflect the diversity and complexity of the legal and regulatory landscape that the enterprise may face when conducting business over the Internet. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
Which of the following is MOST important when defining controls?
Identifying monitoring mechanisms
Including them in the risk register
Aligning them with business objectives
Prototyping compensating controls
According to the CRISC Review Manual1, controls are the policies, procedures, practices, and organizational structures that are designed and implemented to manage risk. The most important factor when defining controls is to align them with the business objectives, as this helps to ensure that the controls support the achievement of the organization’s strategy, goals, and values. Aligning controls with business objectives also helps to optimize the benefits and costs of controls, and to prioritize and allocate resources for control implementation and maintenance. References = CRISC Review Manual1, page 202.
A risk practitioner is developing a set of bottom-up IT risk scenarios. The MOST important time to involve business stakeholders is when:
updating the risk register
documenting the risk scenarios.
validating the risk scenarios
identifying risk mitigation controls.
Validating the risk scenarios is the most important time to involve business stakeholders, as they can provide feedback on the relevance, completeness, and accuracy of the scenarios. They can also help to ensure that the scenarios are aligned with the business objectives, context, and risk appetite. By involving business stakeholders in the validation process, the risk practitioner can increase the credibility and acceptance of the risk scenarios.
Updating the risk register, documenting the risk scenarios, and identifying risk mitigation controls are all important steps in the risk scenario development process, but they are not the most important time to involve business stakeholders. These steps can be performed by the risk practitioner with input from othersources, such as subject matter experts, historical data, industry standards, etc. References = CRISC Review Manual, 7th Edition, ISACA, 2020, page 47-481
Which of the following is accountable for the management of IT risk within an organization?
Senior management
Business process owners
Second line
Internal audit
The correct answer isBbecausebusiness process ownersare accountable for the management of IT risk within the organization. In CRISC, risk accountability rests with those who own the business activities and processes affected by the risk. They are responsible for ensuring that risk is identified, assessed, treated, and monitored in a way that supports business objectives.
The other options are not the best answer:
A. Senior managementapproves risk appetite, provides oversight, and signs off on plans, but accountability for specific business risk resides with the owners of the business processes and services.
C. Second lineprovides oversight, guidance, framework support, and monitoring, but does not own the risk.
D. Internal auditis independent and provides assurance; it does not manage or own IT risk.
Exact Extracts supporting the answer:
“Accountability for business risk related to IT primarily lies with users of IT services.”
“For an IT system supporting a critical business process senior managers should be accountable for the risk.”
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“Risk owner is a risk management role that is part of the first line of defense.”
“Operational management is the function that manages risk according to the three lines of defense model.”
Taken together, these extracts show that accountability for IT risk is assigned to the first line, meaning business and operational owners, not assurance or oversight functions. Therefore,business process ownersare accountable for management of IT risk within the organization.
===========
Which of the following is the MOST important consideration when determining whether to accept residual risk after security controls have been implemented on a critical system?
Cost versus benefit of additional mitigating controls
Annualized loss expectancy (ALE) for the system
Frequency of business impact
Cost of the Information control system
Residual risk is the risk that remains after security controls have been implemented on a system. Residual risk can be accepted, transferred, avoided, or further mitigated. The most important consideration when deciding whether to accept residual risk is the cost versus benefit of additional mitigating controls. This means comparing the potential impact of the residual risk with the cost and effectiveness of implementing more controls to reduce it. If the cost of additional controls outweighs the benefit of reducing the residual risk, then it may be acceptableto accept the residual risk. However, if the benefit of additional controls exceeds the cost, then it may be advisable to implement more controls to lower the residual risk to an acceptable level. References = Risk and Information Systems Control Study Manual, Chapter 3: Risk Response and Mitigation, Section 3.4: Risk Response Selection, p. 156-157.
Which of the following would provide the MOST useful information to a risk owner when reviewing the progress of risk mitigation?
Key audit findings
Treatment plan status
Performance indicators
Risk scenario results
A treatment plan status is a report that shows the current status and progress of the risk mitigation actions and activities that are implemented to reduce the risk exposure of the organization. A treatment plan status would provide the most useful information to a risk owner when reviewing the progress of risk mitigation, as it can help to monitor and evaluate the performance and effectiveness of the risk controls, and to identify and address any issues or gaps that may arise during the implementation. A treatment plan status can also provide feedback and information to the risk owners and stakeholders, and enable them to adjust the risk strategy and response actions accordingly. References = CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 257. CRISC Sample Questions 2024, Question 257. ISACACertified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 257. CRISC by Isaca Actual Free Exam Q & As, Question 9.
Which of the following situations would cause the GREATEST concern around the integrity of application logs?
Weak privileged access management controls
Lack of a security information and event management (SIEM) system
Lack of data classification policies
Use of hashing algorithms
The PRIMARY goal of a risk management program is to:
facilitate resource availability.
help ensure objectives are met.
safeguard corporate assets.
help prevent operational losses.
According to the What Is Risk Management & Why Is It Important? article, risk management is the systematic process of identifying, assessing, and mitigating threats or uncertainties that can affect your organization. The primary goal of a risk management program is to help ensure objectives are met, by aligning the risk management process with the organization’s strategy, vision, mission, values, and objectives. By having a risk management program, an organization can identify potential problems before they occur and have a plan for addressing them, as well as monitor and report on the effectiveness of the risk responses. This can help the organization to achieve its desired outcomes and create value for its stakeholders. References = What Is Risk Management & Why Is It Important?
Which of the following BEST enables risk mitigation associated with software licensing noncompliance?
Document IT inventory management procedures.
Conduct annual reviews of license expiration dates.
Perform automated vulnerability scans.
Implement automated IT asset management controls.
Automated IT asset management ensures real-time visibility and tracking of software usage, licensing, and compliance. It minimizes human error, improves audit readiness, and proactively addresses noncompliance risks.
Which of the following will BEST help to ensure implementation of corrective action plans?
Contracting to third parties
Establishing employee awareness training
Setting target dates to complete actions
Assigning accountability to risk owners
Assigning accountability to risk owners is the best way to ensure implementation of corrective action plans, because it clarifies the roles and responsibilities of those who are in charge of managing and mitigating the risks. Contracting to third parties, establishing employee awareness training, and setting target dates tocomplete actions are all helpful measures, but they do not guarantee the implementation of corrective action plans without accountability. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.3, page 105
An organization is unable to implement a multi-factor authentication requirement until the next fiscal year due to budget constraints. Consequently, a policy exception must be submitted. Which of the following is MOST important to include in the analysis of the exception?
Sections of the policy that may justify not implementing the requirement
Risk associated with the inability to implement the requirement
Budget justification to implement the new requirement during the current year
Industry best practices with respect to implementation of the proposed control
The most important factor to include in the analysis of the policy exception is the risk associated with the inability to implement the multi-factor authentication requirement. A policy exception is a temporary orpermanent deviation from the established policies or standards of the organization, due to various reasons, such as budget constraints, technical limitations, or business needs. A policy exception must be submitted and approved by the appropriate authority, and it must include a clear and comprehensive analysis of the rationale, impact, and mitigation of the exception. The risk associated with the inability to implement the multi-factor authentication requirement is the most important factor to include in the analysis, because it evaluates the probability and severity of potential threats or incidents that could exploit the lack of multi-factor authentication, such as unauthorized access, data breach, or identity theft. The risk analysis also helps to justify the need and urgency of the policy exception, and to propose alternative or compensating controls to reduce or transfer the risk, such as password policies, access restrictions, or encryption. The other options are not the most important factor, although they may be relevant or supportive to the policy exception analysis. Sections of the policy that may justify not implementing the requirement are the clauses or provisions in the policy that allow or enable the policy exception, such as exemptions, waivers, or variances. These sections can help to validate the legitimacy and feasibility of the policy exception, but they do not assess the risk or the impact of the exception. Budget justification to implement the new requirement during the current year is the explanation and evidence of the financial resources and constraints that affect the implementation of the multi-factor authentication requirement. This justification can help to demonstrate the cost-benefit and return on investment of the requirement, but it does not measure the risk or the mitigation of the exception. Industry best practices with respect to implementation of the proposed control are the proven methods and standards that are adopted by the leading organizations in a specific field or sector for implementing the multi-factor authentication requirement. These best practices can help to benchmark and improve the quality and effectiveness of the requirement, but they do not quantify the risk or the impact of the exception. References = Policy Exception Management - ISACA, Multi-Factor Authentication Policy - University of Arkansas, Common Conditional Access policy: Require MFA for all users
After mapping generic risk scenarios to organizational security policies, the NEXT course of action should be to:
record risk scenarios in the risk register for analysis.
validate the risk scenarios for business applicability.
reduce the number of risk scenarios to a manageable set.
perform a risk analysis on the risk scenarios.
According to the LDR514: Security Strategic Planning, Policy, and Leadership Course, after mapping generic risk scenarios to organizational security policies, the next course of action should be to validate the risk scenarios for business applicability. This is because generic risk scenarios are not specific to the organization’s context, objectives, and environment, and they may not capture the unique threats, vulnerabilities, and impacts that the organization faces. Therefore, validating the risk scenarios for business applicability will help to ensure that the risk scenarios are relevant, realistic, and consistent with the organization’s security policies. Validating the risk scenarios will also help to identify any gaps, overlaps, or conflicts between the risk scenarios and the security policies, and to resolve themaccordingly. References = LDR514: Security Strategic Planning, Policy, and Leadership Course, Risk Assessment and Analysis Methods: Qualitative and Quantitative
Which of the following is the BEST control to detect an advanced persistent threat (APT)?
Utilizing antivirus systems and firewalls
Conducting regular penetration tests
Monitoring social media activities
Implementing automated log monitoring
Implementing automated log monitoring is the best control to detect an advanced persistent threat (APT), which is a stealthy and continuous attack on a target network or system. Automated log monitoring can help to identify anomalous or suspicious activities, such as unusual network traffic, unauthorized access attempts, or data exfiltration, that may indicate the presence of an APT. Utilizing antivirus systems and firewalls, conducting regular penetration tests, and monitoring social media activities are controls that help to prevent or mitigate APTs, but not to detect them. References = Most Asked CRISC Exam Questions and Answers - The Knowledge Academy, question 200.
Which of the following would be a risk practitioner’s BEST recommendation upon learning of an updated cybersecurity regulation that could impact the organization?
Perform a gap analysis
Conduct system testing
Implement compensating controls
Update security policies
Performing a gap analysis is the best recommendation for a risk practitioner upon learning of an updated cybersecurity regulation that could impact the organization. A gap analysis can help identify the current state of compliance, the desired state of compliance, and the actions needed to achieve compliance. Conducting system testing, implementing compensating controls, and updating security policies are possible actions that may result from the gap analysis, but they arenot the best initial recommendation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 1; CRISC Review Manual, 6th Edition, page 143.
Which of the following will BEST help to ensure key risk indicators (KRIs) provide value to risk owners?
Ongoing training
Timely notification
Return on investment (ROI)
Cost minimization
The best way to ensure key risk indicators (KRIs) provide value to risk owners is to provide timely notification of the changes in the risk exposure. KRIs are metrics that provide an early warning of increasing risk exposure in various areas of the organization. By providing timely notification of the KRI values, the risk owners can be alerted of the risk situation and take appropriate actions to manage the risk. Ongoing training, return on investment (ROI), and cost minimization are other possible ways to ensure KRIs provide value, but they are not as effective as timely notification. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 10; CRISC Review Manual, 6th Edition, page 140.
Which of the following provides the BEST evidence that risk mitigation plans have been implemented effectively?
Self-assessments by process owners
Mitigation plan progress reports
Risk owner attestation
Change in the level of residual risk
Residual risk is the risk that remains after the risk mitigation plans have been implemented. Residual risk reflects the effectiveness of the risk response in reducing the likelihood or impact of the risk. The best evidence that risk mitigation plans have been implemented effectively is the change in the level of residual risk. A change in the level of residual risk can be measured by comparing the risk level before and after the risk mitigation plans have been executed. A change in the level of residual risk can also be evaluated by comparing the actual residual risk with the target or acceptable residual risk. A change in the level of residual risk can demonstrate how well the risk mitigation plans have achieved the risk objectives and met the risk criteria. A change in the level of residual risk can also provide feedback and lessons learned for future risk management activities. References = Residual Risk: Definition, Formula & Management, Residual Risk: What It Is and How to Manage It, Residual Risk: How to Calculate and Manage It.
Which of the following scenarios presents the GREATEST risk of noncompliance with data privacy best practices?
Making data available to a larger audience of customers
Data not being disposed according to the retention policy
Personal data not being de-identified properly
Data being used for purposes the data subjects have not opted into
Data Privacy Principles:
Consent and Purpose Limitation: According to data privacy regulations like GDPR, data subjects must provide explicit consent for specific purposes. Using data for purposes beyond what was consented to violates these principles, posing significant compliance risks.
Transparency and Accountability: Organizations must be transparent about how they use personal data and ensure accountability in data processing. Using data without consent undermines this transparency and accountability.
Greatest Risk of Noncompliance:
Legal and Regulatory Risks: Using personal data without consent can lead to severe penalties under laws like GDPR and CPRA. These laws impose heavy fines for noncompliance, making this scenario the highest risk.
Reputational Damage: Unauthorized use of personal data can severely damage an organization’s reputation, leading to loss of customer trust and potential financial losses.
Operational Impact: Ensuring compliance with consent requirements is fundamental to an organization ' s data processing activities. Failure to do so can disrupt business operations and necessitate significant remediation efforts.
Comparison with Other Options:
Making Data Available to a Larger Audience of Customers: While potentially risky, this does not inherently violate data privacy principles if done within consented uses.
Data Not Being Disposed According to the Retention Policy: This poses risks related to data minimization and retention principles but is less severe than unauthorized data use.
Personal Data Not Being De-identified Properly: This is a significant risk but typically involves fewer direct legal and regulatory implications compared to using data without consent.
The BEST key performance indicator (KPI) to measure the effectiveness of a backup process would be the number of:
resources to monitor backups
restoration monitoring reports
backup recovery requests
recurring restore failures
The number of recurring restore failures is the best key performance indicator (KPI) to measure the effectiveness of a backup process, as it helps to evaluate the reliability and quality of the backup data and the backup system. A backup process is a process of creating and storing copies of data or systems to enable recovery in case of data loss, corruption, or disaster. A restore process is a process of retrieving and restoring the backup data or systems to the original or alternative location or state. A restore failure is an event that occurs when the restore processfails to complete successfully or correctly, due to various reasons, such as corrupted or missing backup data, incompatible or outdated backup system, or insufficient or unavailable resources. A recurring restore failure is a restore failure that happens repeatedly or frequently, indicating a persistent or systemic problem with the backup process.
The number of recurring restore failures helps to measure the effectiveness of the backup process by providing the following benefits:
It indicates the extent and magnitude of the backup process performance and quality issues, and the impact and severity of the backup process failures on the data or system availability and integrity.
It identifies and analyzes the root causes and contributing factors of the backup process failures, and the gaps or weaknesses in the backup process design, implementation, operation, or monitoring.
It provides feedback and learning opportunities for the backup process improvement and enhancement, and guides the development and implementation of corrective or preventive actions.
It communicates and reports the backup process status and results to the relevant stakeholders, and supports the alignment of the backup process with the organizational strategy and objectives.
The other options are not the best key performance indicators (KPIs) to measure the effectiveness of a backup process. The number of resources to monitor backups is a measure of the inputs or costs of the backup process, but it does not indicate the outputs or benefits of the backup process. The number of restoration monitoring reports is a measure of the documentation or communication of the backup process, but it does not reflect the actual or potential performance or quality of the backup process. The number of backup recovery requests is a measure of the demand or frequency of the backup process, but it does not evaluate the reliability or quality of the backup process. References = 12 Process KPIs to Monitor Process Performance in 2024 - AIMultiple, IT Risk Resources | ISACA, Mastering RTO and RPO in Backup Strategies: A Key to Data Recovery Success
Which of the following will BEST help to improve an organization ' s risk culture?
Maintaining a documented risk register
Establishing a risk awareness program
Rewarding employees for reporting security incidents
Allocating resources for risk remediation
A risk awareness program is a set of activities that aim to educate and inform employees about the organization’s risk culture, policies, and procedures. A risk awareness program can help improve an organization’s risk culture by enhancing the employees’ understanding of risk, their roles and responsibilities in risk management, and the benefits of risk mitigation. A risk awareness program can also foster a culture of openness, trust, and collaboration among employees, managers, and stakeholders, which can improve the organization’s risk performance and resilience.
Maintaining a documented risk register, rewarding employees for reporting security incidents, and allocating resources for risk remediation are also important aspects of risk management, but they do not directly address the organization’s risk culture, which is the shared values, beliefs, and attitudes that influence how risk is perceived and handled within the organization.
Which of the following would be MOST helpful in assessing the risk associated with data loss due to human vulnerabilities?
Reviewing password change history
Performing periodic access recertification
Conducting social engineering exercises
Reviewing the results of security awareness surveys
Social engineering exercises are simulations of real-world attacks that exploit human vulnerabilities, such as phishing, baiting, pretexting, or quid pro quo. Conducting social engineering exercises can help assess the risk associated with data loss due to human vulnerabilities by measuring the employees’ susceptibility to such attacks, their awareness of security policies and procedures, and their response to incidents. Reviewing password change history, performing periodic access recertifications, and reviewing the results of security awareness surveys are also useful, but they do not directly test the employees’ behavior and resilience in the face of social engineering attacks.
Which of the following is MOST important for an organization to consider when developing its IT strategy?
IT goals and objectives
Organizational goals and objectives
The organization ' s risk appetite statement
Legal and regulatory requirements
The most important factor for an organization to consider when developing its IT strategy is the organizational goals and objectives. The organizational goals and objectives are the statements that define the purpose, direction, and desired outcomes of the organization. The organizational goals and objectives help to align the IT strategy with the organization’s mission, vision, values, and strategy, and to ensure that the IT strategy supports and enables the organization’s performance and improvement. The organizational goals and objectives also help to communicate and coordinate the IT strategy with the organization’s stakeholders, such as the board, management, business units, and IT functions, and to facilitate the IT decision-making and reporting processes. The other options are not as important as the organizational goals and objectives, although they may be related to the IT strategy. IT goals and objectives, the organization’s risk appetite statement, and legal and regulatory requirements are all factors that could affect the feasibility and sustainability of the IT strategy, but they do not necessarily reflect or influence the organization’s purpose, direction, and desired outcomes. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.2.1, page 1-9.
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
IT infrastructure manager
Chief Risk Officer (CRO)
Business continuity manager
Business application owner
The business application owner is responsible for the operation and risk decisions related to the application. Since the loss of failover may impact business continuity, their approval is essential.
Which of the following is the PRIMARY factor in determining a recovery time objective (RTO)?
Cost of offsite backup premises
Cost of downtime due to a disaster
Cost of testing the business continuity plan
Response time of the emergency action plan
A recovery time objective (RTO) is the maximum acceptable time or duration that a business process or function can be disrupted or unavailable due to a disaster or incident, before it causes unacceptable or intolerable consequences for the organization. It is usually expressed in hours, days, or weeks, and it is aligned with the organization’s business continuity and disaster recovery objectives and requirements.
The primary factor in determining a RTO is the cost of downtime due to a disaster, which is the estimated loss or damage that the organization may suffer if a business process or function is disrupted or unavailable for a certain period of time. The cost of downtime can be expressed in terms of financial, operational, reputational, or legal consequences, and it can help the organization to assess the impact and urgency of the disaster, and to decide on the appropriate recovery strategy and resources.
The other options are not the primary factors in determining a RTO, because they do not address the fundamental question of how long the organization can tolerate the disruption or unavailability of a business process or function.
The cost of offsite backup premises is the cost of acquiring, maintaining, or using an alternative or secondary location or facility that can be used to resume or continue the business process or function in case of a disaster or incident. The cost of offsite backup premises is important to consider when selecting or implementing a recovery strategy, but it is not the primary factor in determining a RTO, because it does not indicate the impact or urgency of the disaster, and it may not reflect the organization’s business continuity and disaster recovery objectives and requirements.
The cost of testing the business continuity plan is the cost of conducting, evaluating, or improving the tests or exercises that are performed to verify or validate the effectiveness and efficiency of the business continuity plan, which is the document that describes the actions and procedures that the organization will take to recover or restore the business process or function in case of a disaster or incident. The cost of testing the business continuity plan is important to consider when developing or updating the business continuity plan, but it is not the primary factor in determining a RTO, because it does not indicate the impact or urgency of the disaster, and it may not reflect the organization’s business continuity and disaster recovery objectives and requirements.
The response time of the emergency action plan is the time or duration that it takes for the organization to initiate or execute the emergency action plan, which is the document that describes the immediate actions and procedures that the organization will take to protect the life, health, and safety of the people, and to minimize the damage or loss of the assets,in case of adisaster or incident. The response time of the emergency action plan is important to consider when preparing or reviewing the emergency action plan, but it is not the primary factor in determining a RTO, because it does not indicate the impact or urgency of the disaster, and it may not reflect the organization’s business continuity and disaster recovery objectives and requirements. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 62-63, 66-67, 70-71, 74-75, 78-79
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 165
CRISC Practice Quiz and Exam Prep
Management has determined that it will take significant time to remediate exposures in the current IT control environment. Which of the following is the BEST course of action?
Implement control monitoring.
Improve project management methodology.
Reassess the risk periodically.
Identify compensating controls.
When remediation is delayed, compensating controls provide interim protection by reducing risk to acceptable levels.
Which of The following is the MOST comprehensive input to the risk assessment process specific to the effects of system downtime?
Business continuity plan (BCP) testing results
Recovery lime objective (RTO)
Business impact analysis (BIA)
results Recovery point objective (RPO)
The most comprehensive input to the risk assessment process specific to the effects of system downtime is the business impact analysis (BIA). The BIA is a process of analyzing the potential impacts of disruptive events on the business processes, functions, and resources. The BIA identifies the criticality, dependencies, recovery priorities, and recovery objectives of the business processes, and quantifies the financial and non-financial impacts of system downtime. The BIA provides valuable information for the risk assessment process, as it helps to evaluate the likelihood and impact of the risks, and to determine the appropriate risk responses. Business continuity plan (BCP) testing results, recovery time objective (RTO), and recovery point objective (RPO) are not as comprehensive as the BIA, as they are derived from the BIA and focus on specific aspects of the business continuity and recovery strategies. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 130.
An IT risk threat analysis is BEST used to establish
risk scenarios
risk maps
risk appetite
risk ownership.
An IT risk threat analysis is best used to establish risk scenarios. A risk scenario is a description of a possible event or situation that may affect the achievement of the IT objectives. A riskscenario consists of three elements: a threat, a vulnerability, and an impact. A threat is a potential cause of an unwanted incident. A vulnerability is a weakness or flaw that can be exploited by a threat. An impact is the consequence or effect of the incident on the IT objectives. An IT risk threat analysis is a technique that identifies and evaluates the threats that may pose a risk to the IT assets and processes. An IT risk threat analysis can help to establish risk scenarios by providing the information and context for the threat element of the risk scenario. The other options are not as directly related to an IT risk threat analysis, as they are related to the outcomes, measures, or responsibilities of the IT risk management process, not the inputs or sources of the IT risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.3: IT Risk Scenarios, page 23.
Which of the following is the BEST indication that an organization ' s IT asset life cycle is poorly managed?
Increased hardware maintenance costs
Sensitive data found on discarded devices
Lack of asset labeling
Inadequate employee training
The correct answer isBbecause findingsensitive data on discarded devicesis the clearest indication that the IT asset life cycle is poorly managed. This points to failure in end-of-life handling, media sanitization, disposal controls, ownership accountability, and policy enforcement. It is a direct indicator of life cycle control breakdown with significant security and compliance consequences.
The other options are less conclusive:
A. Increased hardware maintenance costsmay indicate inefficiency, but not necessarily poor life cycle control.
C. Lack of asset labelingis a weakness, but less severe and less direct than improper disposal of sensitive data.
D. Inadequate employee trainingmay contribute to problems, but it is not the strongest indicator by itself.
Exact Extracts supporting the answer:
“When data are no longer needed by a particular process they should be handled according to policy.”
“Information that is no longer required to support the main purpose of the enterprise from an information security perspective should be managed under the retention policy.”
“The data security control that BEST protects the confidentiality of data stored on backup media in transit to a third-party storage facility is encryption.”
“The BEST safeguard against a data breach is security awareness training.”
These extracts support that assets and the data on them must be handled according to policy throughout the life cycle, especially when no longer needed. Sensitive data remaining on discarded devices is therefore the strongest indication of poor asset life cycle management.
===========
Which of the following should be the MAIN consideration when validating an organization ' s risk appetite?
Comparison against regulations
Maturity of the risk culture
Capacity to withstand loss
Cost of risk mitigation options
According to the Gaining the competitive edge – measuring and assessing an organization’s risk culture article, risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite should be aligned with the organization’s strategy, goals, and values, and should reflect the organization’s risk culture and capabilities. One of the main considerations when validating an organization’s risk appetite is the capacity to withstand loss, which is the ability of the organization to absorb the impact of adverse events without jeopardizing its viability or reputation. The capacity to withstand loss depends on various factors, such as the financial strength, the operational resilience, the governance structure, and the stakeholder expectations of the organization. By assessing the capacity to withstand loss, the organization can determine if its risk appetite is realistic and appropriate, or if it needs to be adjusted to match its risk profile and environment. References = Gaining the competitive edge – measuring and assessing an organization’s risk culture
In the design phase.
During pre-production testing.
Once in the production environment.
Throughout development.
Automated code reviews are most effective when integrated throughout the development lifecycle. Continuous reviews allow early detection and remediation of vulnerabilities, preventing security issues from propagating into later stages such as testing or production. Performing code reviews only at the end or once in production is less effective as vulnerabilities may already be embedded. The proactive approach in development reduces risk significantly
The BEST way to demonstrate alignment of the risk profile with business objectives is through:
risk scenarios.
risk tolerance.
risk policy.
risk appetite.
The BEST way to demonstrate alignment of the risk profile with business objectives is through risk scenarios, because they are the descriptions and illustrations of the potential events or situations that may affect the achievement of the business objectives and processes. Risk scenarios can help to demonstrate how the risk profile, which is the summary and representation of the identified and assessed risks, is relatedand relevant to the business objectives and processes, and how the risk responses and controls are designed and implemented to support and enable the business objectives and processes. The other options are not the best way, because:
Option B: Risk tolerance is the level of variation or deviation from the expected or desired outcome that the organization is willing to accept or endure, but it does not demonstrate alignment of the risk profile with business objectives, which is the process of ensuring that the risk profile and the business objectives are consistent and compatible with each other.
Option C: Risk policy is the document that defines the principles, guidelines, and requirements for the risk management process and activities in the organization, but it does not demonstrate alignment of the risk profile with business objectives, which is the process of showing and proving that the risk profile and the business objectives are coherent and integrated with each other.
Option D: Risk appetite is the amount and type of risk that the organization is willing to take or pursue in order to achieve its objectives and goals, but it does not demonstrate alignment of the risk profile with business objectives, which is the process of establishing and maintaining that the risk profile and the business objectives are aligned and balanced with each other. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 104.
Which of The following should be of GREATEST concern for an organization considering the adoption of a bring your own device (BYOD) initiative?
Device corruption
Data loss
Malicious users
User support
A bring your own device (BYOD) initiative allows employees to use their personal devices, such as smartphones, tablets, or laptops, for work purposes. This can provide benefits such as increased productivity, flexibility, and employee satisfaction. However, it also introducessignificant risks, such as data loss, data leakage, malware infection, unauthorized access, and compliance violations. Among these risks, data loss is of greatest concern for an organization, as it can have severe consequences, such as reputational damage, legal liability, financial loss, and competitive disadvantage. Data loss can occur due to various reasons, such as device theft, loss, damage, or disposal, accidental deletion, unauthorized transfer, or malicious attack. Therefore, an organization considering the adoption of a BYOD initiative should implement appropriate controls, such as encryption, authentication, remote wipe, backup, and data classification, to protect the data stored or accessed on the personal devices. References = Bring Your Own Device (BYOD) Policy: What You Need to Know, BYOD Risks: What You Need to Know, BYOD Security: 8 Risks and How to Mitigate Them
Which of the following would BEST mitigate the ongoing risk associated with operating system (OS) vulnerabilities?
Temporarily mitigate the OS vulnerabilities
Document and implement a patching process
Evaluate permanent fixes such as patches and upgrades
Identify the vulnerabilities and applicable OS patches
The best way to mitigate the ongoing risk associated with operating system (OS) vulnerabilities is to document and implement a patching process. A patching process is a set of procedures and guidelines that define how to identify, evaluate, test, apply, and monitor patches for the OS. Patches are updates or fixes that address the known vulnerabilities or bugs in the OS. By documenting and implementing a patching process, the organization can ensure that the OS is regularly updated and protected from the potential exploits or attacks that may exploit the vulnerabilities. The other options are not as effective as documenting and implementing a patching process, as they are related to the temporary, partial, or reactive measures to deal with the OS vulnerabilities, not the proactive and continuous measures to prevent or reduce the OS vulnerabilities. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
Which of the following would provide the MOST helpful input to develop risk scenarios associated with hosting an organization ' s key IT applications in a cloud environment?
Reviewing the results of independent audits
Performing a site visit to the cloud provider ' s data center
Performing a due diligence review
Conducting a risk workshop with key stakeholders
The most helpful input to develop risk scenarios associated with hosting an organization’s key IT applications in a cloud environment is conducting a risk workshop with key stakeholders. A risk workshop is a facilitated session that involves brainstorming, discussing, and analyzing the potential risks and opportunities related to a specific topic or project. A risk workshop helps to identify and prioritize the most relevant and significant risk scenarios, as well as to explore the possible causes, impacts, and responses. A risk workshop also helps to engage and align the key stakeholders, such as the business owners, IT managers, cloud providers, and risk experts, and to leverage their knowledge, experience, and perspectives. The other options are not as helpful as conducting a risk workshop, although they may provide some inputor information for the risk scenario development. Reviewing the results of independent audits, performing a site visit to the cloud provider’s data center, and performing a due diligence review are all activities that can help to assess the current state and performance of the cloud environment, but they do not necessarily generate or evaluate the risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
Which of the following BEST mitigates the risk of sensitive personal data leakage from a software development environment?
Tokenized personal data only in test environments
Data loss prevention tools (DLP) installed in passive mode
Anonymized personal data in non-production environments
Multi-factor authentication for access to non-production environments
Anonymizing personal data in non-production environments means replacing the real data with fictitious but realistic data that does not allow identification of the individuals. This is a good way to mitigate the risk of sensitive personal data leakage from a software development environment, as it reduces the exposure of the data to unauthorized access or misuse. Tokenizing personal data only in test environments is not sufficient, as the data may still be exposed in other non-production environments, such as development or staging. Data loss prevention tools (DLP) installed in passive mode may detect and report data leakage incidents, but they do not prevent them from happening. Multi-factor authentication for access to non-production environments may enhance the security of the access, but it does not protect the data from being leaked by authorized users or compromised by other means. References = CRISC Review Manual (Digital Version), page 226; CRISC Review Questions, Answers & Explanations Database, question 195.
Which of the following should be of GREATEST concern to a risk practitioner when determining the effectiveness of IT controls?
Configuration updates do not follow formal change control.
Operational staff perform control self-assessments.
Controls are selected without a formal cost-benefit
analysis-Management reviews security policies once every two years.
Configuration updates are changes made to the settings, parameters, or components of an IT system or network. Configuration updates can affect the functionality, performance, security, and reliability of the system or network. Therefore, configuration updates should follow formal change control, which is a process that ensures that changes are authorized, documented, tested, and implemented in a controlled manner. Formal change control can help prevent errors, conflicts, disruptions, and vulnerabilities that may arise from configuration updates. Configuration updates that do not follow formal change control should be of greatest concern to a risk practitioner when determining the effectiveness of IT controls, as they can introduce newrisks or compromise existing controls. References = Risk and Information Systems Control Study Manual, Chapter 3: Risk Response and Mitigation, Section 3.5: Control Monitoring and Reporting, p. 161-162.
Which of the following would MOST likely require a risk practitioner to update the risk register?
An alert being reported by the security operations center.
Development of a project schedule for implementing a risk response
Completion of a project for implementing a new control
Engagement of a third party to conduct a vulnerability scan
The completion of a project for implementing a new control would most likely require a risk practitioner to update the risk register. The risk register is a document that records the identified risks, their analysis, and their responses. The completion of a project for implementing a new control means that a risk response has been executed and a new control has been established. This may affect the likelihood and/or impact of the related risks, and the residual risk level. Therefore, the risk practitioner should update the risk register to reflect the current status and outcome of the risk response and the new control. The other options are not as likely to require a risk practitioner to update the risk register, as they are related to the reporting, planning, or assessment of the risks or the controls, not the implementation or completion of the risk response or the new control. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Response, page 87.
A company has located its computer center on a moderate earthquake fault. Which of the following is the MOST important consideration when establishing a contingency plan and an alternate processing site?
The alternative site is a hot site with equipment ready to resume processing immediately.
The contingency plan provides for backup media to be taken to the alternative site.
The contingency plan for high priority applications does not involve a shared cold site.
The alternative site does not reside on the same fault to matter how the distance apart.
A contingency plan is a set of actions and procedures that aim to ensure the continuity of critical business functions in the event of a disruption or disaster. An alternate processing site is a location where the organization can resume its information systems operations in case the primary site is unavailable or damaged. The most important consideration when establishing a contingency plan and an alternate processing site for a company located on a moderate earthquake fault is to ensure that the alternative site does not reside on the same fault, no matter how far apart they are. This is because an earthquake can affect a large area along the fault line, and potentially damage both the primary and the alternative site, rendering them unusable. By choosing an alternative site that is not on the same fault, the company can reduce the risk of losing both sites, and increase the likelihood of restoring its operations quickly and effectively. The other options are not as important as the alternative site location, because they do not address the main threat of an earthquake, but rather focus on specific or partial aspects of the contingency plan, as explained below:
A. The alternative site is a hot site with equipment ready to resume processing immediately is a consideration that relates to the availability and readiness of the alternative site, but it does not ensure that the site is safe and secure from an earthquake. A hot site is a type of alternative site that has the necessary hardware, software, and network components to resume the information systems operations with minimal or no downtime. However, if the hot site is on the same fault asthe primary site, it may not be accessible or functional after an earthquake, and the company may lose both sites and the data stored on them.
B. The contingency plan provides for backup media to be taken to the alternative site is a consideration that relates to the integrity and recoverability of the data, but it does not ensure that the site is safe and secure from an earthquake. Backup media are devices or systems that store copies of the data and information that are essential for the organization’s operations. Taking backup media to the alternative site can help the company to restore its data and resume its operations in case the primary site is damaged or destroyed. However, if the alternative site is on the same fault as the primary site, it may not be accessible or functional after an earthquake, and the company may lose both sites and the backup media.
C. The contingency plan for high priority applications does not involve a shared cold site is a consideration that relates to the performance and reliability of the alternative site, but it does not ensure that the site is safe and secure from an earthquake. A shared cold site is a type of alternative site that has the necessary space and infrastructure to accommodate the information systems operations, but does not have the hardware, software, or network components installed. A shared cold site is shared by multiple organizations, and may not be available or suitable for the company’s high priority applications, which require more resources and customization. However, if the alternative site is on the same fault as the primary site, it may not be accessible or functional after an earthquake, and the company may lose both sites and the ability to resume its high priority applications. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 115. How to conduct a contingency planning process - IFRC, CP-4(2): Alternate Processing Site - CSF Tools - Identity Digital, Information System Contingency Planning Guidance - ISACA
A user has contacted the risk practitioner regarding malware spreading laterally across the organization ' s corporate network. Which of the following is the risk practitioner’s BEST course of action?
Review all log files generated during the period of malicious activity.
Perform a root cause analysis.
Notify the cybersecurity incident response team.
Update the risk register.
Notifying the incident response team ensures immediate action to contain and remediate the malware spread, limiting further impact. This aligns withIncident Response and Containmentprotocols under risk management.
A risk practitioner has been notified of a social engineering attack using artificial intelligence (AI) technology to impersonate senior management personnel. Which of the following would BEST mitigate the impact of such attacks?
Subscription to data breach monitoring sites
Suspension and takedown of malicious domains or accounts
Increased monitoring of executive accounts
Training and awareness of employees for increased vigilance
Training employees to recognize and respond to social engineering tactics is the most effective way to mitigate these attacks. It empowers staff to act as the first line of defense, aligning withRisk Awareness and Organizational Trainingpractices.
An organization has decided to implement an emerging technology and incorporate the new capabilities into its strategic business plan. Business operations for the technology will be outsourced. What will be the risk practitioner ' s PRIMARY role during the change?
Managing third-party risk
Developing risk scenarios
Managing the threat landscape
Updating risk appetite
The risk practitioner’s primary role during the change is to manage the third-party risk, as this involves identifying, assessing, and mitigating the risks associated with outsourcing the business operations for the emerging technology. The risk practitioner should ensure that the third-party provider has the necessary capabilities, security, and compliance to deliver the expected outcomes and meet the contractual obligations. The risk practitioner should also monitor the performance and service levels of the third-party provider and report any issues or incidents. Developing risk scenarios, managing the threat landscape, and updating risk appetite are all important activities for the risk practitioner, but they are not the primary role during the change. Developing risk scenarios is a technique for identifying and analyzing potential risk events and their impacts. Managing the threat landscape is a process of identifying and responding to the external and internal threats that may affect the organization. Updating risk appetite is a decision that reflects the organization’s willingness to accept or avoid risk in pursuit of its objectives. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 48.
Which of the following BEST mitigates reputational risk associated with disinformation campaigns against an organization?
Monitoring digital platforms that disseminate inaccurate or misleading news stories
Engaging public relations personnel to debunk false stories and publications
Restricting the use of social media on corporate networks during specific hours
Providing awareness training to understand and manage these types of attacks
Understanding Reputational Risk:
Reputational risk arises from negative public perception, which can be fueled by disinformation campaigns. These campaigns spread false or misleading information about an organization, potentially damaging its reputation.
Mitigating Reputational Risk:
The best way to mitigate this risk is to actively counteract false information and restore public trust. This involves debunking false stories and correcting misinformation promptly and effectively.
Role of Public Relations:
Engaging public relations (PR) personnel is crucial in managing the organization ' s reputation. PR professionals are skilled in crafting messages, dealing with media, and using communication strategies to address and correct false narratives.
PR personnel can issue press releases, organize press conferences, and leverage social media to reach a wide audience, ensuring the correct information is disseminated.
Monitoring and Awareness Training:
While monitoring digital platforms and providing awareness training are important, they are more preventive measures. Monitoring helps in early detection, and training aids in internalmanagement of such risks. However, they do not actively counteract the false information once it is in the public domain.
Restricting Social Media:
Restricting social media usage on corporate networks does not address the core issue of disinformation campaigns. It may reduce internal risks but does not mitigate external reputational damage.
References:
The CRISC Review Manual discusses strategies for managing reputational risk and highlights the importance of proactive communication and public relations efforts (CRISC Review Manual, Chapter 1: Governance, Section 1.3.4 The Value of Risk Communication).
Which of the following is a KEY consideration for a risk practitioner to communicate to senior management evaluating the introduction of artificial intelligence (Al) solutions into the organization?
Al requires entirely new risk management processes.
Al potentially introduces new types of risk.
Al will result in changes to business processes.
Third-party Al solutions increase regulatory obligations.
Artificial intelligence (AI) solutions can offer significant benefits to an organization, such as improved efficiency, accuracy, and innovation. However, AI also poses new challenges and risks that need to be considered and addressed by senior management. Some of these risks include:
Ethical and social risks: AI solutions may have unintended or undesirable impacts on human values, rights, and behaviors, such as privacy, fairness, accountability, and transparency. For example, AI systems may exhibit bias, discrimination, or manipulation, or may infringe on personal data or autonomy.
Technical and operational risks: AI solutions may have vulnerabilities, errors, or failures that affect their performance, reliability, or security. For example, AI systems may be subject to hacking, tampering, or misuse, or may malfunction or produce inaccurate or harmful outcomes.
Legal and regulatory risks: AI solutions may have unclear or conflicting legal or regulatory implications or obligations, such as liability, compliance, or governance. For example, AI systems may raise questions about ownership, responsibility, or accountability, or may violate existing laws or regulations, or create new ones.
Therefore, a risk practitioner should communicate to senior management that AI potentially introduces new types of risk that need to be identified, assessed, and managed in alignment with the organization’s objectives, values, and risk appetite. References = ISACA CRISC Review Manual, 7th Edition, Chapter 3, Section 3.2.2, page 113.
A rule-based data loss prevention {DLP) tool has recently been implemented to reduce the risk of sensitive data leakage. Which of the following is MOST likely to change as a result of this implementation?
Risk likelihood
Risk velocity
Risk appetite
Risk impact
A rule-based data loss prevention (DLP) tool is a software solution that identifies and helps prevent unsafe or inappropriate sharing, transfer, or use of sensitive data. It can help an organization monitor and protect sensitive information across on-premises systems, cloud-based locations, and endpoint devices. It can also help an organization comply with regulations such as the Health Insurance Portability and Accountability Act (HIPAA) and General Data Protection Regulation (GDPR). A rule-based DLP tool works by comparing content to the organization’s DLP policy, which defines how the organization labels, shares, and protects data without exposing it to unauthorized users. The tool can then apply protective actions such as encryption, access restrictions, and alerts. As a result of implementing a rule-based DLP tool, the most likely change is the reduction of risk likelihood, which is the probability of a risk event occurring. By detecting and preventing data breaches, exfiltration, or unwanted destruction of sensitive data, a rule-based DLP tool can lower the chance of such incidents happening and thus decrease the risk likelihood. The other options are less likely to change as a result of implementing a rule-based DLP tool. Risk velocity is the speed at which a risk event impacts an organization, which depends on factors such as the nature of the threat, the response time, and the recovery process. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives, which depends on factors such as the organization’s culture, strategy, and stakeholder expectations. Risk impact is the potential loss or damage that a risk event can cause to an organization, which depends on factors such as the severity of the incident, the extent of theexposure, andthe resilience of the organization. While a rule-based DLP tool may have some influence on these factors, it is not the primary driver of change for them. References = Risk IT Framework, ISACA, 2022, p. 13
A new international data privacy regulation requires personal data to be
disposed after the specified retention period, which is different from the local
regulatory requirement. Which of the following is the risk practitioner ' s
BEST course of action?
The application code has not been version controlled.
Knowledge of the applications is limited to few employees.
An IT project manager is not assigned to oversee development.
Controls are not applied to the applications.
Which of the following is the PRIMARY purpose of periodically reviewing an organization ' s risk profile?
Align business objectives with risk appetite.
Enable risk-based decision making.
Design and implement risk response action plans.
Update risk responses in the risk register
According to the CRISC Review Manual, the primary purpose of periodically reviewing an organization’s risk profile is to enable risk-based decision making, because it helps to ensure thatthe risk information is current, relevant, and accurate. The risk profile is a snapshot of the organization’s risk exposure at a given point in time, based on the risk identification, analysis, and evaluation processes. Periodically reviewing the risk profile allows the organization tomonitor the changes in the risk environment, the effectiveness of the risk responses, and the impact of the risk events. This enables the organization to make informed decisions about the risk management strategies and priorities. The other options are not the primary purpose of periodically reviewing the risk profile, as they are related to other aspects of the risk management process. Aligning business objectives with risk appetite is the purpose of establishing the risk context, which defines the scope and boundaries of the risk management activities. Designing and implementing risk response action plans is the purpose of the risk response process, which involves selecting and executing the appropriate risk responses. Updating risk responses in the risk register is the outcome of the risk monitoring and reporting process, which involves tracking the risk performance and communicating the risk information to the stakeholders. References = CRISC Review Manual, 7th Edition, Chapter 2, Section 2.2.4, page 86.
When communicating changes in the IT risk profile, which of the following should be included to BEST enable stakeholder decision making?
List of recent incidents affecting industry peers
Results of external attacks and related compensating controls
Gaps between current and desired states of the control environment
Review of leading IT risk management practices within the industry
The best thing to include when communicating changes in the IT risk profile is the gaps between the current and desired states of the control environment, as this shows the stakeholders the extent and impact of the changes, and the actions and resources needed to address them. The control environment is the set of policies, processes, and systems that provide reasonableassurance that the IT risks are identified, assessed, and treated effectively and efficiently. The current state of the control environment reflects the existing level and performance of the controls, and the residual risk that remains after the controls are applied. The desired state of the control environment reflects the target level and performance of the controls, and the risk appetite and tolerance of the organization. The gaps between the current and desired states of the control environment indicate the areas of improvement or enhancement for the IT risk management process, and the priorities and strategies for risk response. The other options are not the best things to include when communicating changes in the IT risk profile, although they may be useful or relevant information. A list of recent incidents affecting industry peers can provide some context and comparison for the IT risk profile, but it does not measure or explain the changes in the IT risk level or the control environment. Results of external attacks and related compensating controls can demonstrate the security and resilience of the IT systems and networks, but they do not cover the entire scope or spectrum of the IT risk profile or the control environment. A review of leading IT risk management practices within the industry can provide some insights and benchmarks for the IT risk management process, but it does not reflect thespecific situation or needs of the organization or the stakeholders. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk and Control Monitoring and Reporting, page 181.
Which of the following is the MOST important consideration when sharing risk management updates with executive management?
Using an aggregated view of organizational risk
Ensuring relevance to organizational goals
Relying on key risk indicator (KRI) data Including
Trend analysis of risk metrics
According to the CRISC Review Manual (Digital Version), the most important consideration when sharing risk management updates with executive management is ensuring relevance toorganizational goals, as this helps to align risk management with business strategy and performance. The risk management updates should:
Highlight the key risks that may affect the achievement of the organizational goals and objectives
Demonstrate the value and benefits of risk management in supporting decision making and enhancing business resilience
Provide clear and concise information on the current risk profile, risk appetite, risk tolerance and risk exposure of the organization
Recommend appropriate risk response actions and resource allocation to address the identified risks
Communicate the roles and responsibilities of executive management in overseeing and governing risk management
References = CRISC Review Manual (Digital Version), Chapter 4: IT Risk Monitoring and Reporting, Section 4.2: IT Risk Reporting, pp. 221-2221
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of IT policies? The number of:
IT policy exceptions granted.
Senior management approvals.
Key technology controls covered by IT policies.
Processes covered by IT policies.
Which of the following is the MOST important consideration when developing risk strategies?
Organization ' s industry sector
Long-term organizational goals
Concerns of the business process owners
History of risk events
Risk strategies are the plans and actions that an organization adopts to manage its risks and to achieve its objectives. Risk strategies should be aligned with the organization’s vision, mission, values, and culture, as well as its internal and external environment. The most important consideration when developing risk strategies is the long-term organizational goals, meaning that the risk strategies should support and enable the organization to pursue and attain its desired future state and outcomes. The long-term organizational goals should guide the risk identification, assessment, response, and monitoring processes, as well as the risk appetite and tolerance levels. The long-term organizational goals should also be communicated and cascaded throughout the organization to ensure the risk awareness and engagement of all stakeholders. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.2, p. 27-28
During the control evaluation phase of a risk assessment, it is noted that multiple controls are ineffective. Which of the following should be the risk practitioner ' s FIRST course of action?
Recommend risk remediation of the ineffective controls.
Compare the residual risk to the current risk appetite.
Determine the root cause of the control failures.
Escalate the control failures to senior management.
The control evaluation phase of a risk assessment is the phase where the risk practitioner evaluates the effectiveness and efficiency of the existing or planned controls that mitigate the identified risks. Controls are the actions or measures that reduce the likelihood or impact of the risks to an acceptable level. The control evaluation phase involves testing, reviewing, and auditing the controls, and identifying any gaps or weaknesses that need to be addressed. If the control evaluation phase reveals that multiple controls are ineffective, the risk practitioner’s first course of action should be to determine the root cause of the control failures. The root cause is the underlying or fundamental reason that leads to the problem or issue, such as the controlfailure. By determining the root cause of the control failures, the risk practitioner can understand why the controls are not working as intended, and what factors or variables are influencing the control performance. This will help the risk practitioner to identify and implement the most appropriate and effective risk response strategy and actions, such as recommending risk remediation, comparing the residual risk, or escalating the control failures. The other options are not the first course of action, as they involve different steps or outcomes of the risk management process:
Recommend risk remediation of the ineffective controls means that the risk practitioner suggests the actions or measures that can improve or restore the effectiveness of the controls, such as by modifying, replacing, or adding the controls. This may be a useful step in the risk management process, but it is not the first course of action, as it may not address the root cause of the control failures, or may not be feasible or efficient for the enterprise’s needs.
Compare the residual risk to the current risk appetite means that the risk practitioner evaluates the level of risk that remains after considering the existing or planned controls, and compares it with the amount and type of risk that the enterprise is willing to accept in pursuit of its objectives. This may be a helpful step in the risk management process, but it is not the first course of action, as it may not reflect the true or current level of risk exposure, or may not account for the uncertainties or complexities of the risks or the controls.
Escalate the control failures to senior management means that the risk practitioner communicates the control failures to the senior leaders of the enterprise, who oversee the enterprise-wide risk management program, and provide guidance and direction to the risk owners and practitioners. This may be a necessary step in the risk management process, but it is not the first course of action, as it may not provide sufficient or timely information or action to address the control failures, or may not reflect the urgency or priority of the control failures. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.3.3.1, pp. 62-63.
Which of the following BEST indicates the efficiency of a process for granting access privileges?
Average time to grant access privileges
Number of changes in access granted to users
Average number of access privilege exceptions
Number and type of locked obsolete accounts
According to the CRISC Review Manual, the average time to grant access privileges is the best indicator of the efficiency of a process for granting access privileges, because it measures how quickly and effectively the process can respond to the access requests and meet the business needs. The average time to grant access privileges can be calculated by dividing the total time spent on granting access privileges by the number of access requests processed. The other options are not the best indicators of the efficiency of the process, because they measure other aspects of the process, such as the quality, the security, or the maintenance. The number of changes in access granted to users measures the quality of the process, as it indicates how wellthe process can align the access rights with the user roles and functions. The average number of access privilege exceptions measures the security of the process, as it indicates how often theprocess deviates from the established policies and standards. The number and type of locked obsolete accounts measures the maintenance of the process, as it indicates how well the process can remove the unnecessary or outdated accounts. References = CRISC Review Manual, 7th Edition, Chapter 4, Section 4.1.2, page 163
Which of the following should management consider when selecting a risk mitigation option?
Maturity of the enterprise architecture
Cost of control implementation
Reliability of key performance indicators (KPIs)
Reliability of key risk indicators (KPIs)
When selecting a risk mitigation option, management should consider the cost of control implementation, as well as the benefits and residual risks. The cost of control implementation includes the direct costs of acquiring, installing, and maintaining the control, as well as the indirect costs of potential side effects, suchas reduced performance, increased complexity, or decreased user satisfaction. The cost of control implementation should be balanced with theexpected reduction in risk exposure and the alignment with the enterprise’s risk appetite and tolerance. The maturity of the enterprise architecture, the reliability of key performance indicators (KPIs), and the reliability of key risk indicators (KRIs) are relevant factors for risk identification and assessment, but not for risk response selection. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk Response, page 149.
Which of the following is the MOST important consideration when identifying stakeholders to review risk scenarios developed by a risk analyst? The reviewers are:
accountable for the affected processes.
members of senior management.
authorized to select risk mitigation options.
independent from the business operations.
The most important consideration when identifying stakeholders to review risk scenarios developed by a risk analyst is that the reviewers are accountable for the affected processes. This is because the reviewers need to have a clear understanding of the business processes that are exposed to the risks, and the potential impact and consequences of the risk scenarios. The reviewers also need to have the authority and responsibility to implement the risk responses and monitor the risk performance. By involving the stakeholders who are accountable for the affected processes, the risk analyst can ensure that the risk scenarios are realistic, relevant, and comprehensive, and that the risk management process is aligned with the business objectives and expectations. The other options are not as important as the accountability for the affected processes, because they do not guarantee that the reviewers have the necessary knowledge, experience, and involvement in the risk management process, as explained below:
B. Members of senior management are not the most important consideration, because they may not have the detailed or operational knowledge of the business processes that are exposed to the risks, or the technical or practical aspects of the risk scenarios. Senior management may also have different or conflicting priorities or perspectives on the risk management process, which may affect the quality and validity of the review.
C. Authorized to select risk mitigation options are not the most important consideration, because they may not have the direct or regular involvement in the business processes that are exposed to the risks, or the specific or contextual understanding of the risk scenarios. The authority to select risk mitigation options may also depend on other factors, such as the risk appetite, the budget, or the organizational structure, which may limit or influence the review.
D. Independent from the business operations are not the most important consideration, because they may not have the sufficient or relevant knowledge of the business processes that are exposed to the risks, or the potential or actual impact and consequences of the risk scenarios. The independence from the business operations may also create a gap or disconnect between the risk management process and the business objectives and expectations, which may affect the effectiveness and efficiency of the review. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 45. A Stakeholder Approach to Risk Management, Module 2. Project risk management: stakeholders’ risks and the project manager’s role, What Is Risk Management Scenario Analysis?
Which of the following is a PRIMARY benefit of engaging the risk owner during the risk assessment process?
Identification of controls gaps that may lead to noncompliance
Prioritization of risk action plans across departments
Early detection of emerging threats
Accurate measurement of loss impact
A primary benefit of engaging the risk owner during the risk assessment process is prioritization of risk action plans across departments, because this helps to ensure that the most critical and relevant risks are addressed first, and that the resources and efforts are allocated and coordinated efficiently and effectively. A risk owner is the person or group who is responsible for the day-to-day management and mitigation of a specific risk, and who has the authority and accountability to make risk-related decisions. A risk assessment is the process of identifying, analyzing, and evaluating the risks that may affect the organization’s objectives, performance, or value. A risk action plan is the set of actions and tasks that are designed and implemented to reduce the likelihood and impact of a risk, or to exploit the opportunities that a risk may create. By engaging the risk owner during the risk assessment process, the organization can benefit from the following advantages:
The risk owner can provide valuable input and feedback on the risk identification, analysis, and evaluation, based on their knowledge, experience, and perspective of the risk and its context.
The risk owner can help to develop and implement the risk action plan, based on their understanding of the risk objectives, expectations, and outcomes, and their ability to influence and control the risk factors and sources.
The risk owner can help to prioritize the risk action plan, based on their assessment of the risk severity, urgency, and importance, and their consideration of the costs, benefits, and feasibility of the risk actions.
The risk owner can help to coordinate the risk action plan across departments, by communicating and collaborating with other risk owners, stakeholders, and resources, and by aligning and integrating the risk actions with the organization’s strategy, processes, and culture. References = Risk Owners — What Do They Do1
The BEST metric to monitor the risk associated with changes deployed to production is the percentage of:
changes due to emergencies.
changes that cause incidents.
changes not requiring user acceptance testing.
personnel that have rights to make changes in production.
Changes deployed to production are those that affect the functionality, performance, or security of the system in a way that is visible or accessible to the end users1. These changes can introduce new risks or vulnerabilities, such as errors, bugs, compatibility issues, or unauthorized access2. Therefore, it is important to monitor the risk associated with these changes and measure how often they cause incidents in production.
One metric that can be used to monitor this risk is the percentage of changes that cause incidents in production. This metric indicates how effective the change management process is and how well the organization can prevent or mitigate potential problems caused by changes3. A high percentage of incidents indicates a high level of risk and a need for improvement in the change management process.
References = IT Change Management for SOC: Process and Best Practices, Determining and Managing Risk when Deploying Code, 6 Deployment Risks and How To Mitigate Them
An application runs a scheduled job that compiles financial data from multiple business systems and updates the financial reporting system. If this job runs too long, it can delay financial reporting. Which of the following is the risk practitioner ' s BEST recommendation?
Implement database activity and capacity monitoring.
Ensure the business is aware of the risk.
Ensure the enterprise has a process to detect such situations.
Consider providing additional system resources to this job.
The risk practitioner’s best recommendation is to consider providing additional system resources to this job, as this would help to reduce the likelihood and impact of the risk of delaying financial reporting. Providing additional system resources, such as memory, CPU, disk space, or bandwidth, can improve the performance and efficiency of the application and the scheduled job. This can also help to avoid potential errors, failures, or interruptions that could affect the quality and timeliness of the financial data and reporting.
The other options are not the best recommendations for this situation. Implementing database activity and capacity monitoring is a good practice to identify and analyze the root causes of performance issues, but it does not directly address the risk of delaying financial reporting. Ensuring the business is aware of the risk is an important step to communicate and escalate the risk, but it does not provide a solution or mitigation strategy. Ensuring the enterprise has a process to detect such situations is a preventive measure to avoid or minimize the occurrence ofthe risk, but it does not eliminate or reduce the risk. References = Practical Recommendations for Better Enterprise Risk Management - ISACA, HR Risk Management: A Practitioner’s Guide - AIHR, Isaca CRISC today updated questions - Verified by Isaca Experts
An organization has allowed its cyber risk insurance to lapse while seeking a new insurance provider. The risk practitioner should report to management that the risk has been:
transferred
mitigated.
accepted
avoided
Cyber risk insurance is a type of insurance policy that provides coverage against losses and damages caused by cyber incidents such as data breaches, hacking, and other cyber attacks. When an organization decides to purchase cyber risk insurance, it transfers the risk of financial loss due to a cyber incident to the insurance company. In the scenario described in the question, the organization allowed its cyber risk insurance to lapse while seeking a new insurance provider. This means that the organization is currently not covered by any cyber risk insurance policy and is therefore exposed to financial losses due to cyber incidents. The risk practitioner should report to management that the risk has been accepted. Accepting risk means that the organization is aware of the potential consequences of the risk and has decided not to take any action to mitigate, transfer, or avoid it. The other options are not correct because they do not reflect the current situation of the organization. The organization has not transferred the risk to another party, as it has no cyber risk insurance policy in place. The organization has not mitigated the risk, as it has not implemented anycontrols or measures to reduce the likelihood or impact of the risk. The organization has not avoided the risk, as it has not eliminated the source or cause of the risk or changed its activities to prevent the risk from occurring. References = CRISC Review Manual, pages 32-331; CRISC Review Questions, Answers & Explanations Manual, page 752
Which of the following MUST be assessed before considering risk treatment options for a scenario with significant impact?
Risk magnitude
Incident probability
Risk appetite
Cost-benefit analysis
According to the Risk Assessment and Management: A Complete Guide, risk magnitude is the product of the likelihood and impact of a risk scenario. Risk magnitude is an important factor to consider before choosing risk treatment options, as it indicates the level of exposure andpotential harm that the organization faces from the risk scenario. Risk treatment options should be selected based on the risk magnitude, as well as the risk appetite and tolerance of the organization. For a scenario with significant impact, the risk magnitude is likely to be high, and therefore the risk treatment options should aim to reduce the likelihood and/or impact of the risk scenario as much as possible, or to transfer or avoid the risk altogether. References = Risk Assessment and Management: A Complete Guide, ISO 27001 Risk Assessment & Risk Treatment: The Complete Guide
A key risk indicator (KRI) is reported to senior management on a periodic basis as exceeding thresholds, but each time senior management has decided to take no action to reduce the risk. Which of the following is the MOST likely reason for senior management ' s response?
The underlying data source for the KRI is using inaccurate data and needs to be corrected.
The KRI is not providing useful information and should be removed from the KRI inventory.
The KRI threshold needs to be revised to better align with the organization s risk appetite
Senior management does not understand the KRI and should undergo risk training.
A key risk indicator (KRI) is a metric that measures the level and trend of a risk that may affect the organization’s objectives, operations, or performance1. A KRI threshold is a predefined value or range that indicates the acceptable or tolerable level of risk for the organization2. Theorganization’s risk appetite is the amount and type of risk that it is willing to take in order to meet its strategic goals3. Therefore, the most likely reason for senior management’s response is that the KRI threshold needs to be revised to better align with the organization’s risk appetite. This means that the current threshold is either too low or too high, resulting in false alarms or missed signals. By adjusting the threshold to reflect the organization’s risk appetite, senior management can ensure that the KRI provides relevant and actionable information for risk management and decision making. The other options are not the most likely reasons for senior management’s response, as they imply that the KRI is faulty, irrelevant, or misunderstood. The underlying data source for the KRI is using inaccurate data and needs to be corrected. This option assumes that the KRI is based on erroneous or unreliable data, which would affect its validity and reliability. However, this is not the most likely reason, as senior management would be expected to verify the data quality and accuracy before using the KRI for risk monitoring and reporting. The KRI is not providing useful information and shouldbe removed from the KRI inventory. This option assumes that the KRI is not aligned with the organization’s objectives, strategies, or risk profile, which would affect its usefulness and value. However, this is not the most likely reason, as senior management would be expected to review and update the KRI inventory periodically to ensure that the KRIs are relevant and meaningful for risk management. Senior management does not understand the KRI and should undergo risk training. This option assumes that senior management lacks the knowledge or skills to interpret and use the KRI for risk management, which would affect their competence and confidence. However, this is not the most likely reason, as senior management would be expected to have sufficient risk awareness and education to understand and apply the KRI for risk management. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.4, Page 53.
A new policy has been published to forbid copying of data onto removable media. Which type of control has been implemented?
Preventive
Detective
Directive
Deterrent
A preventive control is a type of control that aims to avoid or reduce the occurrence of an undesirable event or risk. A preventive control can be implemented through technical, administrative, or physical means. A new policy that forbids copying of data onto removablemedia is an example of a preventive control, because it prevents unauthorized data exfiltration or leakage through removable devices, such as flash drives or external hard disk drives. A preventive control is different from the other types of controls, as explained below:
A detective control is a type of control that aims to discover or identify the occurrence of an undesirable event or risk. A detective control can be implemented through monitoring, auditing, or reporting activities. An example of a detective control is a log analysis tool that detects any unauthorized access or modification of data on a system.
A directive control is a type of control that aims to guide or instruct the behavior or actions of individuals or groups. A directive control can be implemented through policies, procedures, standards, or rules. An example of a directive control is a training program that teaches employees how to handle sensitive data securely and appropriately.
A deterrent control is a type of control that aims to discourage or dissuade individuals or groups from performing an undesirable event or risk. A deterrent control can be implemented throughsanctions, penalties, or consequences. An example of a deterrent control is a warning message that informs users of the legal implications of copying data onto removable media without authorization. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, page 38.
Who should be responsible for approving the cost of controls to be implemented for mitigating risk?
Risk practitioner
Risk owner
Control owner
Control implementer
A MAJOR advantage of using key risk indicators (KRIs) is that they:
Identify scenarios that exceed defined risk appetite.
Help with internal control assessments concerning risk appetite.
Assess risk scenarios that exceed defined thresholds.
Identify when risk exceeds defined thresholds.
KRIs provide measurable indicators that flag when risks exceed predefined thresholds, enabling swift and effective risk response. This supports theMonitoring and Reportingfunction in risk management, ensuring risks are managed proactively.
During an internal IT audit, an active network account belonging to a former employee was identified. Which of the following is the BEST way to prevent future occurrences?
Conduct a comprehensive review of access management processes.
Declare a security incident and engage the incident response team.
Conduct a comprehensive awareness session for system administrators.
Evaluate system administrators ' technical skills to identify if training is required.
The best way to prevent future occurrences of active network accounts belonging to former employees is to conduct a comprehensive review of access management processes. This review should include verifying that the access rights of all employees are updated regularly, especially when they change roles or leave the organization. The review should also ensure that there are clear policies and procedures for granting, modifying, and revoking access rights, and that these are followed consistently and documented properly. The review should also identify and address any gaps or weaknesses in the access management processes that could lead to unauthorized orinappropriate access. By conducting a comprehensive review of access management processes, the organization can improve its security posture and reduce the risk of data breaches or misuse of resources. References = IT audit: The ultimate guide [with checklist] | Zapier, IT auditing and controls – planning the IT audit [updated 2021]
When developing a risk awareness training program, which of the following training topics would BEST facilitate a thorough understanding of risk scenarios?
Mapping threats to organizational objectives
Reviewing past audits
Analyzing key risk indicators (KRIs)
Identifying potential sources of risk
Identifying potential sources of risk is the first step in the risk identification process, which is essential for developing a thorough understanding of risk scenarios. Sources of risk can be internal or external, and can include factors such as people, processes, technology, environment, regulations, and events. Identifying potential sources of risk can help to generate a comprehensive list of risk scenarios that can affect the organization’s objectives and operations. Identifying potential sources of risk can also help to raise risk awareness among the employees and to foster a risk culture within the organization. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, p. 66-67
A risk practitioner learns of an urgent threat intelligence alert to patch a critical vulnerability identified in the organization ' s operating system. Which of the following should the risk practitioner do FIRST?
Patch the operating system immediately
Determine whether any active attacks are exploiting the vulnerability
Invoke the organization ' s incident response plan
Evaluate the threat in the context of the organization ' s IT environment
Before acting, the risk practitioner mustevaluate the threat in the organizational context. This includes checking system exposure, current mitigations, and potential business impact. Only then can an informed decision (such as patching or mitigation) be made.
An organization has recently updated its disaster recovery plan (DRP). Which of the following would be the GREATEST risk if the new plan is not tested?
External resources may need to be involved.
Data privacy regulations may be violated.
Recovery costs may increase significantly.
Service interruptions may be longer than anticipated.
Testing a disaster recovery plan is essential to ensure its effectiveness and identify any gaps or weaknesses that might hinder the recovery process. Without testing, the organization may face longer service interruptions than anticipated, which could result in loss of revenue, customer dissatisfaction, reputational damage, and regulatory penalties. Some of the best practices for disaster recovery testing are1:
Test many scenarios
Test regularly
Document everything
Keep everyone updated
Define metrics
Evaluate the results
Test your disaster recovery plan
References = Best Practices For Disaster Recovery Testing | Snyk
Which of the following is MOST important to identify when developing top-down risk scenarios?
Key procedure control gaps
Business objectives
Senior management ' s risk appetite
Hypothetical scenarios
The most important factor to identify when developing top-down risk scenarios is B. Business objectives12
Top-down risk scenarios are based on the organization’s strategic goals, objectives, and key performance indicators (KPIs), and they aim to identify the potential events or situations that could prevent or hinder the achievement of those goals and objectives12
By identifying the business objectives, the risk practitioner can align the risk scenarios with the organization’s mission, vision, and values, and ensure that the risk scenarios are relevant, realistic, and meaningful for the senior management and other stakeholders12
The other factors are not as important as the business objectives when developing top-down risk scenarios, because they are either more relevant for bottom-up risk scenarios (A and D), or they are derived from the business objectives and the risk scenarios ©12
Which of the following is MOST helpful to review when identifying risk scenarios associated with the adoption of Internet of Things (loT) technology in an organization?
The business case for the use of loT
The loT threat landscape
Policy development for loT
The network that loT devices can access
Risk scenarios: Narratives that describe potential risk events, their causes, consequences, and likelihood1.
Internet of Things (IoT): A network of interconnected devices, software, sensors, and other things that communicate and exchange data without human intervention2.
IoT threat landscape: The range and types of threats and attacks that target IoT devices, systems, and networks3.
The most helpful thing to review when identifying risk scenarios associated with the adoption of IoT technology in an organization is the IoT threat landscape. The IoT threat landscape provides a comprehensive and current overview of the potential sources, methods, and impacts of cyberattacks on IoT devices, systems, and networks. Reviewing the IoT threat landscape can help an organization to:
Identify the most relevant and prevalent threats and vulnerabilities that affect IoT technology, such as weak passwords, insecure interfaces, insufficient data protection, poor device management, or lack of encryption4.
Assess the likelihood and impact of different types of attacks, such as malware infections, denial-of-service attacks, data breaches, unauthorized access, or sabotage4.
Prioritize the most critical and urgent risks that need to be addressed and mitigated.
Develop realistic and plausible risk scenarios that reflect the actual IoT threat environment and the organization’s specific context and objectives.
The other options are not as helpful as the IoT threat landscape when identifying risk scenarios associated with the adoption of IoT technology in an organization, because they do not provide a comprehensive and current view of the potential threats and attacks that target IoT technology. The business case for the use of IoT, which is the justification and rationale for adopting IoT technology based on the expected benefits, costs, and risks, may help to understand the value and purpose of IoT technology for the organization, but it does not provide detailed information on the specific threats and vulnerabilities that affect IoT technology. Policy development for IoT, which is the process of creating and implementing rules and guidelines for the governance, management, and security of IoT technology, may help to establish the standards and expectations for IoT technology within the organization, but it does not provide an overview of the external threats and attacks that target IoT technology. The network that IoT devices can access, which is the infrastructure and system that enables the connectivity and communicationof IoT devices, may help to identify the potential entry points and attack vectors for IoT threats, but it does not provide a complete picture of the types and impacts of IoT threats.
References = Risk Scenarios Toolkit, What is the Internet of Things (IoT)? With Examples | Coursera, Top IoT security issues and challenges (2022) – Thales, 8 Internet of Things Threats and Security Risks - SecurityScorecard
Who is the MOST appropriate owner for newly identified IT risk?
The manager responsible for IT operations that will support the risk mitigation efforts
The individual with authority to commit organizational resources to mitigate the risk
A project manager capable of prioritizing the risk remediation efforts
The individual with the most IT risk-related subject matter knowledge
According to the CRISC Review Manual, the risk owner is the person who has the authority and accountability to manage a specific risk and its associated controls1. The risk owner is also responsible for ensuring that the risk is within the acceptable level and that the risk response is effective and efficient2. Therefore, the most appropriate owner for a newly identified IT risk is the individual who has the authority to commit organizational resources to mitigate the risk, asthey have the most interest and influence on the risk and its impact on the business objectives. The other options are not the most appropriate owners for a newly identified IT risk, as they may not have the authority or the accountability to manage the risk. The manager responsible for IT operations that will support the risk mitigation efforts may have the operational responsibility or the oversight of the risk management activities, but they may not have the authority to allocate the resources or approve the risk response. A project manager capable of prioritizing the risk remediation efforts may have the project management skills or the knowledge of the risk management process, but they may not have the accountability or the ownership of the risk or its outcomes. The individual with the most IT risk-related subject matter knowledge may have the technical expertise or the understanding of the risk and its causes, but they may not have the decision-making power or the responsibility to manage the risk or its controls. References = CRISC Review Manual, pages 32-331; CRISC Review Questions, Answers & Explanations Manual, page 822
Which of the following is MOST helpful in identifying gaps between the current and desired state of the IT risk environment?
Analyzing risk appetite and tolerance levels
Assessing identified risk and recording results in the risk register
Evaluating risk scenarios and assessing current controls
Reviewing guidance from industry best practices and standards
Evaluating risk scenarios and assessing current controls is the most helpful in identifying gaps between the current and desired state of the IT risk environment, because it allows the risk practitioner to compare the actual and expected outcomes of the IT processes and activities under different situations. A risk scenario is a hypothetical situation that describes a possible event or sequence of events that may affect the IT objectives and performance. A risk scenario can be based on various factors, such as the sources of risk, the risk drivers, the risk events, the risk impacts, and the risk responses. A risk scenario can also include the likelihood and severity of the risk, as well as the assumptions and uncertainties involved. Evaluating risk scenarios helps the risk practitioner to understand the nature and extent of the IT risks, as well as the potential consequences and opportunities that may arise from them. Assessing current controls is the process of examining and testing the existing controls that are implemented to manage the IT risks. A control is a measure or action that reduces the likelihood or impact of a risk, or enhances the benefits or opportunities of a risk. Assessing current controls helps the risk practitioner to determine the effectiveness and efficiency of the controls, as well as their alignment with the IT objectives and requirements. By evaluating risk scenarios and assessing current controls, the risk practitioner can identify the gaps between the current and desired state of the IT risk environment. The gaps can be related to the following aspects: - The IT objectives and performance: The gaps can indicate the difference between the actual and expected results of theIT processes and activities, as well as the deviation from the IT goals and targets. - The IT risk exposure and appetite: The gaps can indicate the difference between the actualand acceptable level of risk that the organization faces or is willing to take in pursuit of the IT objectives. - The IT risk management process and practices: The gaps can indicate the difference between the actual and expected performance of the IT risk management process, as well as the compliance with the IT risk management policies and standards. - The IT risk culture and awareness: The gaps can indicate the difference between the actual and desired level of risk awareness,understanding, and communication among the IT stakeholders, as well as the alignment with the organizational values and culture. Identifying the gaps between the current and desired state of the IT risk environment is important for the risk practitioner, as it can help to prioritize and address the IT risks, as well as to improve and optimize the IT risk management process and practices. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: Risk Scenarios, pp. 63-681
Which of the following is the GREATEST benefit of identifying appropriate risk owners?
Accountability is established for risk treatment decisions
Stakeholders are consulted about risk treatment options
Risk owners are informed of risk treatment options
Responsibility is established for risk treatment decisions.
The greatest benefit of identifying appropriate risk owners is that accountability is established for risk treatment decisions. Risk owners are the individuals or groups who are responsible and accountable formanaging a specific risk and its associated actions and outcomes. By identifying appropriate risk owners, the organization can ensure that the risk treatment decisions are made by the people who have the authority, knowledge, and interest in the risk. Stakeholders beingconsulted, risk owners being informed, and responsibility being established are other possible benefits, but they are not as great as accountability being established. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
A risk practitioner is reviewing the status of an action plan to mitigate an emerging IT risk and finds the risk level has increased. The BEST course of action would be to:
implement the planned controls and accept the remaining risk.
suspend the current action plan in order to reassess the risk.
revise the action plan to include additional mitigating controls.
evaluate whether selected controls are still appropriate.
The best course of action when a risk practitioner finds that the risk level of an emerging IT risk has increased, despite having an action plan to mitigate it, is to evaluate whether the selected controls are still appropriate. This is because the increase in the risk level may indicate that the current controls are not effective or sufficient to reduce the impact or likelihood of the risk, or that the risk environment has changed and new threats or vulnerabilities have emerged. By evaluating the appropriateness of the selected controls, the risk practitioner can identify the gaps or weaknesses in the control design or implementation, and determine the need for corrective actions or improvements. The other options are not the best course of action, because they do not address the root cause of the problem, but rather assume or ignore the effectiveness of the controls, as explained below:
A. Implement the planned controls and accept the remaining risk is not the best course of action, because it assumes that the planned controls are adequate and aligned with the organization’s risk appetite, which may not be the case if the risk level has increased. Implementing the planned controls without evaluating their appropriateness may result in wasting resources, exposing the organization to more risk, or missing opportunities to enhance the risk mitigation effectiveness.
B. Suspend the current action plan in order to reassess the risk is not the best course of action, because it ignores the effectiveness of the current controls, which may still provide some level ofrisk mitigation, even if they are not optimal. Suspending the current action plan may also delay the risk response and increase the risk exposure, especially if the risk is time-sensitive or dynamic. Reassessing the risk without evaluating the appropriateness of the current controls may also lead to inaccurate or incomplete risk information and analysis.
C. Revise the action plan to include additional mitigating controls is not the best course of action, because it assumes that the current controls are ineffective or insufficient, which may not be the case if the risk level has increased due to other factors, such as changes in the risk environment or the organization’s objectives. Revising the action plan without evaluating the appropriateness of the current controls may result in overcompensating, duplicating, or conflicting the controls, which may affect the risk mitigation efficiency and performance. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.3, page 130. How to Mitigate Emerging Technology Risk - ISACA, Risk Mitigation Strategies: Types & Examples (+ Free Template), 5 Key Risk Mitigation Strategies (With Examples) | Indeed.com
An organization’s board of directors is concerned about recent data breaches in the news and wants to assess its exposure to similar scenarios. Which of the following is the BEST course of action?
Evaluate the organization ' s existing data protection controls.
Reassess the risk appetite and tolerance levels of the business.
Evaluate the sensitivity of data that the business needs to handle.
Review the organization’s data retention policy and regulatory requirements.
Data Protection Controls:
Evaluating existing data protection controls involves reviewing and assessing the measures in place to protect sensitive data from breaches.
This includes technical, administrative, and physical controls designed to prevent unauthorized access, use, disclosure, disruption, modification, or destruction of data.
Steps in Evaluation:
Review Current Controls:Assess the effectiveness of encryption, access controls, data masking, and other security measures.
Identify Gaps:Determine if there are any weaknesses or vulnerabilities in the current controls.
Recommend Improvements:Suggest enhancements or additional controls to address identified gaps.
Importance of Evaluation:
Provides the board with a clear understanding of the organization’s current security posture and exposure to data breaches.
Helps in identifying areas where additional controls or improvements are needed to mitigate risks effectively.
Comparing Other Actions:
Reassess Risk Appetite and Tolerance Levels:Important but secondary to understanding current controls.
Evaluate Data Sensitivity:Useful but should be part of a broader assessment of existing controls.
Review Data Retention Policy:Relevant for compliance but not directly addressing the immediate concern of data breaches.
References:
The CRISC Review Manual discusses the importance of evaluating data protection controls to understand and mitigate risks (CRISC Review Manual, Chapter 4: Information Technology and Security, Section 4.4 Data Protection and Privacy).
Which of the following observations should be of GREATEST concern to a risk practitioner assessing a third-party service provider for privacy risk?
Appropriate privacy training and awareness campaigns are not conducted for employees
The provider subcontracts part of the service to a fourth party
Contractual language for handling personally identifiable information (PII) is not defined.
The roles and responsibilities associated with data governance are not well defined
The correct answer is C because undefined contractual language for handling personally identifiable information (PII) is the greatest concern in a third-party privacy risk assessment. Contract terms establish the provider’s legal and operational obligations for collection, use, protection, sharing, retention, breach notification, and disposal of personal data. If these obligations are not clearly defined, the organization may be unable to enforce privacy requirements or demonstrate adequate governance over outsourced processing.
The other options are important, but not as critical as missing contractual obligations:
A. Appropriate privacy training and awareness campaigns are not conducted for employees is a control weakness, but contractual requirements come first.
B. The provider subcontracts part of the service to a fourth party is a significant concern, but it can be governed through contract language and oversight.
D. The roles and responsibilities associated with data governance are not well defined is also important, but contractual clarity over PII handling is more fundamental.
Exact Extracts supporting the answer:
“To safeguard an enterprise from issues like unbacked-up emails the best approach would be validating the company policies to the provider’s contract.”
“The most important part of any outsourcing contract is provisions to assess the compliance of the provider.”
“The most important consideration for an enterprise structuring a contract with a third party is the inclusion of a confidentiality clause.”
“The first step for a risk practitioner when an enterprise has decided to outsource all IT services and support to a third party is to ensure that security requirements are addressed in all contracts and agreements.”
“The MOST important consideration when transmitting personal information across networks is ensuring the privacy of the personal information.”
These extracts support that privacy and security obligations must be clearly established in contracts. Therefore, the greatest concern is that contractual language for handling PII is not defined .
===========
QUESTION NO: 96 [Risk Assessment]
Which of the following groups would provide the MOST relevant perspective when reporting loss exposure based on a risk analysis exercise?
A. Internal auditors
B. Senior management
C. Process owners
D. Independent risk consultants
Answer: C
The correct answer is C because process owners provide the most relevant perspective when reporting loss exposure . They understand the business process, operational dependencies, impact of disruptions, and real consequences if the risk materializes. Since loss exposure is closely tied to business impact, the people accountable for and closest to the process provide the most meaningful input.
The other options are less appropriate:
A. Internal auditors provide independent assurance, but they are not the primary source of business-impact perspective.
B. Senior management provides strategic oversight, but process owners offer more detailed and direct exposure insight.
D. Independent risk consultants may add external expertise, but not the same operational understanding of the specific process.
Exact Extracts supporting the answer:
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“For an IT system supporting a critical business process senior managers should be accountable for the risk.”
“The main outcome of a business impact analysis (BIA) is the criticality of business processes.”
“IT risk is measured by its impact on business operations.”
“The primary reason risk professionals conduct risk assessments is to identify risk with the highest business impact.”
These extracts support that loss exposure is best understood through the business process context, making process owners the most relevant group.
===========
QUESTION NO: 97 [Risk Response and Mitigation]
Which of the following processes is MOST helpful in proactively identifying non-compliant baseline images prior to implementing IT systems?
A. Patch management
B. Configuration management
C. Vulnerability management
D. Change management
Answer: B
The correct answer is B because configuration management is the process most directly concerned with establishing, maintaining, and validating system baselines. If the goal is to identify non-compliant baseline images before implementation, configuration management is the most helpful process because it governs approved configurations and compares actual builds to required baselines.
The other options are less appropriate:
A. Patch management focuses on updates and fixes, not full baseline compliance.
C. Vulnerability management identifies known weaknesses, but not baseline-image compliance as directly as configuration management.
D. Change management governs approval of changes, but it does not primarily validate baseline images.
Exact Extracts supporting the answer:
“The control practice related to information systems architecture that includes establishing and maintaining baselines for internally developed systems is Configuration management.”
“The MOST appropriate metric to measure how well the information security function is managing the administration of user access is percent of accounts with configurations in compliance.”
“Including thresholds that identify when controls no longer provide the intended value is essential when developing metrics to monitor the control life cycle.”
“The BEST way to identify IS control deficiencies is through defined control objectives.”
These extracts support that baseline definition and compliance checking are core configuration management activities. Therefore, the best answer is configuration management .
===========
QUESTION NO: 98 [Governance]
A risk practitioner notes that the number of unauthorized disclosures of confidential data has been increasing. Which of the following is MOST important to examine for determining the root cause?
A. Completeness of data classification schema
B. Updated regulations related to data protection
C. The volume of data loss prevention (DLP) alerts
D. Scope of security awareness training
Answer: A
The correct answer is A because the completeness of the data classification schema is the most important area to examine when determining the root cause of increasing unauthorized disclosures of confidential data. If data is not classified correctly or completely, the organization may fail to apply the right handling requirements, access restrictions, monitoring, retention, and protection controls. Classification is the foundation for protecting confidential information.
The other options are less important for root cause determination:
B. Updated regulations related to data protection may change compliance obligations, but they are not the most likely direct root cause of increased disclosures.
C. The volume of DLP alerts may reflect symptoms or detection levels, but it does not explain the underlying cause.
D. Scope of security awareness training may contribute, but it is secondary to correctly identifying and labeling sensitive data.
Exact Extracts supporting the answer:
“The PRIMARY responsibility for data classification rests with the data owner.”
“The FIRST policy that governs how information is to be protected from within the enterprise especially for a breakthrough technology is the data classification policy.”
“The MAIN benefit of information classification is that it helps select security measures proportional to risk.”
“To determine the level of protection required for securing personally identifiable information a risk practitioner should PRIMARILY consider the sensitivity property of the information.”
“The person responsible for ensuring that information is classified is the data owner.”
These extracts directly support that classification drives protection requirements. Therefore, the most important area to examine is the completeness of the data classification schema .
===========
QUESTION NO: 99 [Governance]
Which of the following BEST enables the classification of controls in a risk taxonomy?
A. Hiring external consultants
B. Adopting standards and frameworks
C. Reviewing security policies periodically
D. Performing internal and external audits
Answer: B
The correct answer is B because adopting standards and frameworks best enables the classification of controls in a risk taxonomy. Standards and frameworks provide structured categories, common terminology, and organized control domains that make it possible to classify controls consistently across the enterprise.
The other options are less appropriate:
A. Hiring external consultants may help with implementation, but does not itself provide the classification structure.
C. Reviewing security policies periodically supports maintenance, but not the foundational taxonomy.
D. Performing internal and external audits evaluates controls, but does not define their classification model.
Exact Extracts supporting the answer:
“To best support IT in fulfilling business requirements an internal control system or framework is essential.”
“An enterprise-wide risk management framework is adopted to enable a consistent approach to risk response throughout the enterprise.”
“When many corporate IT standards are outdated the best course of action is to review the standards against current requirements and determine their adequacy.”
“The BEST way to identify IS control deficiencies is through defined control objectives.”
These extracts support that frameworks and standards provide the necessary structure and consistency for organizing and classifying controls. Therefore, the best answer is adopting standards and frameworks .
Which of the following should be the GREATEST concern to a risk practitioner when process documentation is incomplete?
Inability to allocate resources efficiently
Inability to identify the risk owner
Inability to complete the risk register
Inability to identify process experts
The greatest concern for a risk practitioner when process documentation is incomplete is the inability to identify the risk owner. The risk owner is the person or entity that has the authority and responsibility to manage a specific risk or a group of related risks. The risk owner helps to identify, assess, and respond to the risks, and to monitor and report on the risk performance and improvement. The risk owner also helps to communicate and coordinate the risk management activities with the relevant stakeholders, such as the board, management, business units, and IT functions. The risk owner is usually identified in the process documentation, which describes the roles, responsibilities, procedures, and resources for each process. The inability to identify the risk owner is a major concern for the risk practitioner, because it may affect the accountability, transparency, and effectiveness of the risk management process, and may lead to confusion, conflicts, or gaps in the risk management activities. The other options are not as concerning as the inability to identify the risk owner, although they may also pose some difficulties or limitations for the risk management process. Inability to allocate resources efficiently, inability to complete the risk register, and inability to identify process experts are all factors that could affect the quality and timeliness of the risk management process, but they do not necessarily affect the authority and responsibility of the risk management process. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, page 2-11.
Which of the following is MOST important to enable well-informed cybersecurity risk decisions?
Determine and understand the risk rating of scenarios.
Conduct risk assessment peer reviews.
Identify roles and responsibilities for security controls.
Engage a third party to perform a risk assessment.
To make well-informed cybersecurity risk decisions, it is most important to determine and understand the risk rating of scenarios. A risk rating is a measure of the severity and priority of a risk, based on the combination of its impact and likelihood. A risk scenario is a description of a potential event or situation that could adversely affect the organization’s objectives, assets, or processes. By determining and understanding the risk rating of scenarios, the organization can identify the most critical and urgent risks, and select the appropriate risk response strategies accordingly. The other options are not as important as determining and understanding the risk rating of scenarios, because they do not provide a clear and comprehensive view of the risk, butrather focus on specific or partial aspects of the risk management process. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 45.
Which of the following is the ULTIMATE goal of conducting a privacy impact analysis (PIA)?
To identify gaps in data protection controls
To develop a customer notification plan
To identify personally identifiable information (Pll)
To determine gaps in data identification processes
The ultimate goal of conducting a privacy impact analysis (PIA) is to identify gaps in data protection controls, as it involves assessing the privacy risks and impacts of collecting, using, storing, and disclosing personally identifiable information (PII), and determining the adequacy and effectiveness of the existing or proposed controls to mitigate those risks and impacts. Developing a customer notification plan, identifying PII, and determining gaps in data identification processes are possible steps or outcomes of conducting a PIA, but they are not the ultimate goal, as they do not address the root cause or solution of the privacy issues. References = CRISC Review Manual, 7th Edition, page 155.
An organization is implementing internet of Things (loT) technology to control temperature and lighting in its headquarters. Which of the following should be of GREATEST concern?
Insufficient network isolation
impact on network performance
insecure data transmission protocols
Lack of interoperability between sensors
Insecure data transmission protocols should be of greatest concern when an organization is implementing internet of Things (IoT) technology to control temperature and lighting in its headquarters, because they can expose the IoT devices and data to unauthorized access,interception, or manipulation. Insecure data transmission protocols can also compromise the confidentiality, integrity, and availability of the IoT system and the information it collects and transmits. The other options are not the greatest concerns, although they may also pose some challenges or risks to the IoT implementation. Insufficient network isolation, impact on networkperformance, and lack of interoperability between sensors are examples of technical or operational issues that can affect the functionality, efficiency, or compatibility of the IoT system, but they do not have the same severity or impact as insecure data transmission protocols. References = CRISC Sample Questions 2024
Which of the following is MOST useful for measuring the existing risk management process against a desired state?
Balanced scorecard
Risk management framework
Capability maturity model
Risk scenario analysis
The most useful tool for measuring the existing risk management process against a desired state is the capability maturity model, as it provides a structured and standardized way to assess the current and target levels of maturity, performance, and effectiveness of the risk management process, and to identify the gaps and improvement opportunities. The balanced scorecard, the risk management framework, and the risk scenario analysis are not the most useful tools, as they are more related to the evaluation, design, or identification of the risk management process, respectively, rather than the measurement of the risk management process. References = CRISC Review Manual, 7th Edition, page 154.
During a review of the asset life cycle process, a risk practitioner identified several unreturned and unencrypted laptops belonging to former employees. Which of the following is the GREATEST concern with this finding?
Insufficient laptops for existing employees
Abuse of leavers ' account privileges
Unauthorized access to organizational data
Financial cost of replacing the laptops
The greatest concern with finding unreturned and unencrypted laptops belonging to former employees is the risk of unauthorized access to organizational data. The laptops may containsensitive or confidential information that could be compromised if they fall into the wrong hands. This could result in data breaches, reputational damage, legal liabilities, or regulatory penalties for the organization. Therefore, it is important to have proper controls in place to ensure that the laptops are returned, wiped, or encrypted when the employees leave the organization.
An organization ' s finance team is proposing the adoption of a blockchain technology to provide a secure method for moving funds. Which of the following should the risk practitioner do FIRST?
Recommend permissionless blockchain.
Perform a risk assessment.
Perform a business impact analysis (BIA).
Recommend permissioned blockchain.
Before selecting technologies or deployment models, a risk assessment should be conducted to evaluate potential threats, vulnerabilities, and controls. This ensures the technology aligns with the risk appetite and regulatory requirements of the organization.
An organization ' s business gap analysis reveals the need for a robust IT risk strategy. Which of the following should be the risk practitioner ' s PRIMARY consideration when participating in development of the new strategy?
Scale of technology
Risk indicators
Risk culture
Proposed risk budget
The risk practitioner’s primary consideration when participating in development of a new IT risk strategy should be the risk culture of the organization. Risk culture is the set of values, beliefs, attitudes, and behaviors that shape how the organization perceives, manages, and responds to risks. Risk culture influences the organization’s risk appetite, risk objectives, risk policies, risk processes, and risk performance. The risk practitioner should consider the risk culture whendeveloping a new IT risk strategy, because it helps to align the IT risk strategy with the organization’s mission, vision, values, and strategy, and to ensure that the IT risk strategy is supported and accepted by the organization’s stakeholders, such as the board, management, employees, customers, regulators, etc. The risk practitioner should also consider the risk culture when developing a new IT risk strategy, because it helps to identify and addressany gaps, issues, or challenges that may affect the implementation and effectiveness of the IT risk strategy, such as lack of awareness, communication, coordination, or accountability. The other options are not the primary consideration for the risk practitioner, although they may be related to the IT risk strategy. Scale of technology, risk indicators, and proposed risk budget are all factors that could affect the feasibility and sustainability of the IT risk strategy, but they do not necessarily reflector influence the organization’s risk culture. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.2.1, page 1-9.
Which of the following should be an element of the risk appetite of an organization?
The effectiveness of compensating controls
The enterprise ' s capacity to absorb loss
The residual risk affected by preventive controls
The amount of inherent risk considered appropriate
Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. One of the elements of risk appetite is the enterprise’s capacity to absorb loss, which is the maximum amount of loss that an organization can withstand without jeopardizing its existence or strategic objectives. The effectiveness of compensating controls, the residual risk affected by preventive controls, and the amount of inherent risk considered appropriate are not elements of risk appetite, but rather factors that influence the risk assessment and responseprocesses. References = [CRISC Review Manual (Digital Version)], page 41; CRISC Review Questions, Answers & Explanations Database, question 196.
Which of the following is the PRIMARY reason for a risk practitioner to use global standards related to risk management?
To build an organizational risk-aware culture
To continuously improve risk management processes
To comply with legal and regulatory requirements
To identify gaps in risk management practices
Global standards related to risk management are documents that provide the principles, guidelines, and best practices for managing risk in a consistent, effective, and efficient manner across different organizations, sectors, and regions12.
The primary reason for a risk practitioner to use global standards related to risk management is to continuously improve risk management processes, which are the activities and tasks that enable the organization to identify, analyze, evaluate, treat, monitor, and communicate the risks that may affect its objectives, performance, and value creation34.
Continuously improving risk management processes is the primary reason because it helps the organization to enhance its risk management capabilities and maturity, and to adapt to the changing risk environment and stakeholder expectations34.
Continuously improving risk management processes is also the primary reason because it supports the achievement of the organization’s goals and the delivery of value to the stakeholders, which are the ultimate purpose and outcome of risk management34.
The other options are not the primary reason, but rather possible benefits or objectives that may result from using global standards related to risk management. For example:
Building an organizational risk-aware culture is a benefit of using global standards related to risk management that involves creating and maintaining a shared understanding, attitude, and behavior towards risk among the organization’s employees and leaders, and fostering a culture of accountability, transparency, and learning34. However, this benefit is not the primary reason because it is an enabler and a consequence of continuously improving risk management processes, rather than a driver or a goal34.
Complying with legal and regulatory requirements is an objective of using global standards related to risk management that involves meeting and exceeding the expectations and obligations of the external authorities or bodies that govern or oversee the organization’s activities and operations, such as laws, regulations, standards, or contracts34. However, thisobjective is not theprimary reason because it is a constraint and a challenge of continuously improving risk management processes, rather than a motivation or a benefit34.
Identifying gaps in risk management practices is an objective of using global standards related to risk management that involves assessing and comparing the current and desiredstate of the organization’s risk management processes, and identifying the areas or aspects that need to be improved or addressed34. However, this objective is not the primary reason because it is a step and a tool of continuously improving risk management processes, rather than a reason or a result34. References =
1: ISO - ISO 31000 — Risk management1
2: Risk Management Standards2
3: Risk IT Framework, ISACA, 2009
4: IT Risk Management Framework, University of Toronto, 2017
Where should a risk practitioner document the current state and desired future state of organizational risk?
Risk register
Risk action plan
Risk management strategy
Business continuity plan (BCP)
A risk practitioner has discovered a deficiency in a critical system that cannot be patched. Which of the following should be the risk practitioner ' s FIRST course of action?
Report the issue to internal audit.
Submit a request to change management.
Conduct a risk assessment.
Review the business impact assessment.
The first course of action for a risk practitioner when discovering a deficiency in a critical system that cannot be patched is to conduct a risk assessment. A risk assessment is a process of identifying, analyzing, and evaluating the risks that could affect the achievement of the objectives of the system or the organization. A risk assessment helps to determine the level and nature of the risk exposure, and to prioritize and respond to the risks. Conducting a risk assessment is the first course of action, as it helps to understand the source, cause, and impact of the deficiency, and to estimate the likelihood and consequences of the risk events that could exploit the deficiency. Conducting a risk assessment also helps to identify and evaluate the existing or potential controls or mitigations that could address the deficiency, and to recommend the appropriate risk treatment options. Reporting the issue to internal audit, submitting a request to change management, and reviewing the business impact assessment are not the first courses ofaction, as they are either the outputs or the inputs of the risk assessment process, and they do not address the primary need of assessing the risk situation and status. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 49.
A business unit is updating a risk register with assessment results for a key project. Which of the following is MOST important to capture in the register?
The methodology used to perform the risk assessment
Action plans to address risk scenarios requiring treatment
Date and status of the last project milestone
The individuals assigned ownership of controls
Updating a risk register with assessment results for a key project must primarily capture action plans to address risk scenarios requiring treatment.
Risk Register Purpose:
Documentation of Risks:The risk register is a central repository for all identified risks and their respective treatment plans. It ensures that all risks are documented, tracked, and managed throughout the project lifecycle.
Action Plans:It is crucial to document action plans for risks that require treatment. This ensures that there are clear strategies in place to mitigate or manage these risks.
Importance of Action Plans:
Mitigation and Management:Action plans detail the steps necessary to mitigate identified risks, providing a clear path for risk management. This is vital for ensuring that risks do not negatively impact the project.
Accountability and Tracking:Including action plans in the risk register assigns responsibility and timelines for risk treatment, which is essential for accountability and tracking progress.
The MOST effective way to increase the likelihood that risk responses will be implemented is to:
create an action plan
assign ownership
review progress reports
perform regular audits.
Risk responses are the actions or strategies that are taken to address the risks that may affect the organization’s objectives, performance, or value creation12.
The most effective way to increase the likelihood that risk responses will be implemented is to assign ownership, which is the process of identifying and appointing the individuals or groups who are responsible and accountable for the execution and monitoring of the risk responses34.
Assigning ownership is the most effective way because it ensures the clarity and commitment of the roles and responsibilities for the risk responses, and avoids the confusion or ambiguity that may arise from the lack of ownership34.
Assigning ownership is also the most effective way because it enhances the communication and collaboration among the stakeholders involved in the risk responses, and provides the feedback and input that are necessary for the improvement and optimization of the risk responses34.
The other options are not the most effective way, but rather possible steps or tools that may support or complement the assignment of ownership. For example:
Creating an action plan is a step that involves defining and documenting the specific tasks, resources, timelines, and deliverables for the risk responses34. However, this step is not the most effective way because it does not guarantee the implementation of the risk responses, especially if there is no clear or agreed ownership for the action plan34.
Reviewing progress reports is a tool that involves collecting and analyzing the information and data on the status and performance of the risk responses, and identifying the issues or gaps that need to be addressed34. However, this tool is not the most effective way because it does not ensure the implementation of the risk responses, especially if there is no ownership for the progress reports or the corrective actions34.
Performing regular audits is a tool that involves conducting an independent and objective assessment of the adequacy and effectiveness of the risk responses, and providing the findings and recommendations for improvement56. However, this tool is not the most effective way because it does not ensure the implementation of the risk responses,especially if there is no ownership for the audit results or the follow-up actions56. References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
3: Risk Response Plan in Project Management: Key Strategies & Tips1
4: ProjectManagement.com - How to Implement Risk Responses2
5: IT Audit and Assurance Standards, ISACA, 2014
6: IT Audit and Assurance Guidelines, ISACA, 2014
Which of the following provides the MOST useful information when determining if a specific control should be implemented?
Business impact analysis (BIA)
Cost-benefit analysis
Attribute analysis
Root cause analysis
A cost-benefit analysis is a tool that compares the costs and benefits of different alternatives, such as implementing or not implementing a specific control. A cost-benefit analysis provides the most useful information when determining if a specific control should be implemented, as it can show the potential savings, benefits, and risks of each option, and help the decision-makers choose the best course of action. A cost-benefit analysis can also include qualitative factors, such as security, compliance, performance, and customer satisfaction, that may be affected by thecontrol implementation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 256. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 256. Most Asked CRISC Exam Questions and Answers, Question 10. CRISC by Isaca Actual Free Exam Q & As, Question 9.
A risk owner has identified a risk with high impact and very low likelihood. The potential loss is covered by insurance. Which of the following should the risk practitioner do NEXT?
Recommend avoiding the risk.
Validate the risk response with internal audit.
Update the risk register.
Evaluate outsourcing the process.
According to the CRISC Review Manual1, the risk register is a tool that records the results of risk identification, analysis, evaluation, and treatment. The risk register should be updated whenever there is a change in the risk profile, such as when a risk response is implemented or a new risk is identified. Updating the risk register allows the organization to monitor the current status of risks and the effectiveness of risk responses. Therefore, the next step for the risk practitioner after identifying a risk with high impact and very low likelihood that is covered by insurance is to update the risk register with the new information. References = CRISC Review Manual1, page 191.
Which strategy employed by risk management would BEST help to prevent internal fraud?
Require control owners to conduct an annual control certification.
Conduct regular internal and external audits on the systems supporting financial reporting.
Ensure segregation of duties are implemented within key systems or processes.
Require the information security officer to review unresolved incidents.
Ensuring segregation of duties are implemented within key systems or processes is the best strategy employed by risk management to prevent internal fraud, because it reduces the opportunity for a single person to manipulate or misuse the system or process for fraudulent purposes. Segregation of duties is a control that assigns different roles and responsibilities to different individuals, such that no one person can perform all the steps of a transaction or process. Requiring control owners to conduct an annual control certification, conducting regular internal and external audits on the systems supporting financial reporting, and requiring the information security officer to review unresolved incidents are all useful strategies to detect ordeter internal fraud, but they are not the best strategy to prevent it, as they do not directly address the root cause of fraud. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.1, page 197
Which of the following conditions presents the GREATEST risk to an application?
Application controls are manual.
Application development is outsourced.
Source code is escrowed.
Developers have access to production environment.
The production environment is the environment where the application is deployed and used by the end users. The production environment should be protected from unauthorized or unintended changes that could compromise the availability, integrity, or confidentiality of the application and its data. Developers have access to the production environment presents the greatest risk to an application, as it could allow them tobypass the change management process, introduce errors or vulnerabilities, or manipulate the application or its data for malicious purposes. The other options are not as risky as developers having access to the production environment, as they involve different aspects of the application lifecycle:
Application controls are manual means that the application relies on human intervention to perform some functions or validations, such as data entry, reconciliation, or authorization. This could increase the risk of human error, fraud, or inefficiency, but it does not directly affect the production environment.
Application development is outsourced means that the application is developed by a third party, such as a vendor or a contractor. This could increase the risk of quality issues, contractual disputes, or intellectual property rights, but it does not directly affect the production environment.
Source code is escrowed means that the source code of the application is deposited with a trusted third party, such as a lawyer or a bank. This could provide assurance and continuity in case the original developer is unable or unwilling to maintain or support the application, but it does not directly affect the production environment. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.1.1.1, pp. 144-145.
Which of the following is a responsibility of the second line of defense in the three lines of defense model?
Performing duties independently to provide assurance
Alerting operational management to emerging issues
Implementing corrective actions to address deficiencies
Owning risk scenarios and bearing the consequences of loss
The second line (risk management, compliance) provides oversight and support to the first line (operations). It monitors risk-related activities, issues alerts, and helps ensure controls are properly designed and implemented, but does not own the risk.
A vendor’s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
Business application owner
Business continuity manager
Chief risk officer (CRO)
IT infrastructure manager
The business application owner is accountable for business impact and must approve any change that affects application availability. ISACA’s CRISC emphasis on ownership roles indicates business owners should approve changes with risk implications.
Which of the following is the MOST important input when developing risk scenarios?
Key performance indicators
Business objectives
The organization ' s risk framework
Risk appetite
The most important input when developing risk scenarios is the business objectives, as they provide the context and scope for the risk identification and analysis process. Risk scenarios are hypothetical situations that describe the possible causes, events, and consequences of a risk. Risk scenarios help to understand and communicate the nature and impact of the risk, and to supportthe risk assessment and response planning. The business objectives are the goals andtargets that the organization wants to achieve through its processes, functions, and projects. The business objectives define the expected outcomes and performance of the organization, and the criteria for measuring and evaluating the success or failure of the organization. The business objectives also reflect the organization’s vision, mission, values, and strategy, and the needs and expectations of the stakeholders. The other options are not the most important inputs when developing risk scenarios, although they may be useful or relevant information. Key performance indicators are metrics that measure and monitor the progress and achievement of the business objectives, but they do not provide the context or scope for the risk scenarios. The organization’s risk framework is the set of principles, policies, and processes that guide and support the risk management activities across the organization, but it does not provide the context or scope for the risk scenarios. Risk appetite is the level of risk that the organization is willing to accept or avoid in pursuit of its business objectives, but it does not provide the context or scope for the risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 58.
Which of the following is the BEST metric to measure the effectiveness of an organization ' s disaster recovery program?
Percentage of applications subject to disaster recovery tests
Number of personnel dedicated to the disaster recovery program
Number of disaster recovery tests performed per year
Percentage of systems meeting defined recovery objectives
Meeting defined RTOs and RPOs indicates that the DR plan can achieve its intended goals under real conditions. This metric directly reflects the effectiveness and reliability of the program.
What would be a risk practitioner ' s BEST recommendation when several key performance indicators (KPIs) for a control process fail to meet service level agreements (SLAs)?
Adjust the process KPI threshold.
Develop an IT risk response plan.
Review the organization ' s IT risk profile.
Review process efficiency.
Which of the following is the MOST important reason to communicate risk assessments to senior management?
To ensure actions can be taken to align assessment results to risk appetite
To ensure key risk indicator (KRI) thresholds can be adjusted for tolerance
To ensure awareness of risk and controls is shared with key decision makers
To ensure the maturity of the assessment program can be validated
Communicating risk assessments to senior management is crucial for ensuring that key decision-makers are aware of the organization ' s risk landscape. This awareness enables informed decision-making regarding risk responses, resource allocation, and strategic planning. It also fosters a risk-aware culture throughout the organization.
Which of the following is the BEST key control indicator (KCI) for a vulnerability management program?
Percentage of high-risk vulnerabilities missed
Number of high-risk vulnerabilities outstanding
Defined thresholds for high-risk vulnerabilities
Percentage of high-risk vulnerabilities addressed
A key control indicator (KCI) is a metric that measures the effectiveness of a control in mitigating a risk. A good KCI for a vulnerability management program should reflect how well the program is reducing the exposure to high-risk vulnerabilities. The percentage of high-risk vulnerabilities addressed is a KCI that shows the proportion of identified high-risk vulnerabilities that have been remediated or mitigated within a defined time frame. This KCI can help monitor the progress and performance of the vulnerability management program and identify areas for improvement.
The other options are not the best KCI for a vulnerability management program because they do not measure the effectiveness of the control. The percentage of high-risk vulnerabilities missed is a measure of the completeness of the vulnerability scanning process, not the control. The number of high-risk vulnerabilities outstanding is a measure of the current risk exposure, not the control. The defined thresholds for high-risk vulnerabilities are a measure of the risk appetite, not the control. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3: IT Risk Assessment, Section 3.4: Risk Indicators, p. 133-134.
Reviewing which of the following BEST helps an organization gain insight into its overall risk profile?
Threat landscape
Risk appetite
Risk register
Risk metrics
Reviewing the risk register is the best way to help an organization gain insight into its overall risk profile, because it provides a comprehensive and structured representation of all the key risks that the organization faces, along with their likelihood, impact, and response strategies. A risk register is a tool that records and tracks the current status of risks, their sources, causes, consequences, and controls. A risk register helps to facilitate the communication and reporting of risks, and to support the risk-based decision making and prioritization. A risk profile is a summary of the key risks that an organization faces, and their implications forthe organization’s objectives and strategy. Reviewing the risk register is the best way to understand the risk profile, as it reflects the nature and level of exposure that the organization has from the various risk sources and scenarios. Reviewing the threat landscape, the risk appetite, and the risk metrics are all useful ways to help an organization gain insight into its overall risk profile, but they are not the best way, as they do not provide a comprehensive and structured view of the risks and theirresponses. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.1, page 83
Which of the following statements describes the relationship between key risk indicators (KRIs) and key control indicators (KCIs)?
KRI design must precede definition of KCIs.
KCIs and KRIs are independent indicators and do not impact each other.
A decreasing trend of KRI readings will lead to changes to KCIs.
Both KRIs and KCIs provide insight to potential changes in the level of risk.
KRIs and KCIs are both metrics that measure and monitor the risk and control environment of an enterprise. KRIs are indicators that reflect the level and trend of risk exposure, and help to identify potential risk events or issues. KCIs are indicators that reflect the performance andeffectiveness of the risk controls, and help to ensure that the controls are operating as intended and mitigating the risk. Both KRIs and KCIs provide insight to potential changes in the level of risk, as they can signal the need for risk response actions, such as enhancing, modifying, or implementing new controls, or adjusting the risk strategy and objectives. References = Most Asked CRISC Exam Questions and Answers. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 240.
What is the PRIMARY reason an organization should include background checks on roles with elevated access to production as part of its hiring process?
To eliminate risk associated with personnel
To reduce internal threats
To ensure new hires have the required skills
To reduce exposure to vulnerabilities
The correct answer is B because the primary reason for conducting background checks on individuals who will have elevated access to production systems is to reduce internal threats . Personnel with privileged access can significantly affect confidentiality, integrity, and availability. Background screening is a preventive governance and personnel security control intended to lower the likelihood of insider misuse, fraud, abuse of privilege, or other harmful actions.
The other options are less appropriate:
A. To eliminate risk associated with personnel is incorrect because risk cannot be fully eliminated.
C. To ensure new hires have the required skills is handled more directly through recruitment, vetting, and qualification review, not primarily through background checks.
D. To reduce exposure to vulnerabilities is too indirect; vulnerabilities are weaknesses in systems or controls, while this question is about personnel risk.
Exact Extracts supporting the answer:
“The MOST effective measure against insider threats to confidential information is role-based access control.”
“The PRIMARY reason that an enterprise would establish segregation of duties controls is to prevent errors or fraudulent activity on high-risk transactions.”
“The control that focuses directly on preventing the risk of collusion is mandatory job rotation.”
“The MOST concern to the risk practitioner regarding applications running in production is backdoors.”
These extracts support that elevated access roles create significant internal threat exposure and require preventive controls focused on reducing insider risk. Therefore, the primary reason for background checks is to reduce internal threats .
===========
QUESTION NO: 91 [Risk Assessment]
Which of the following would be MOST helpful to review when prioritizing the implementation of multiple IT-related initiatives?
A. Risk awareness program objectives
B. Risk assessment results
C. Risk profile
D. Risk policy
Answer: C
The correct answer is C because the risk profile provides the most useful enterprise-level view when prioritizing multiple IT-related initiatives. It reflects the aggregated level of risk facing the organization, helps identify which exposures are most significant, and supports comparison across initiatives based on business impact, likelihood, and current exposure.
The other options are less useful for prioritization at this level:
A. Risk awareness program objectives relate to culture and communication, not implementation prioritization.
B. Risk assessment results are important, but the risk profile is more useful when consolidating and prioritizing across multiple initiatives.
D. Risk policy sets direction and expectations, but it does not provide the comparative view needed for prioritization.
Exact Extracts supporting the answer:
“The most important aspect to consider in relation to a risk profile is the aggregated risk to the enterprise.”
“The main purpose of risk monitoring is to provide timely information on the actual status of the enterprise with regard to risk with the risk profile offering an overall risk status.”
“When reporting the status of the IT control environment to management the most important component is the risk profile of the enterprise.”
“The PRIMARY result of a risk assessment process is input for risk-aware decisions.”
These extracts show that the risk profile is the best consolidated basis for prioritizing multiple IT-related initiatives.
===========
QUESTION NO: 92 [Risk and Control Monitoring and Reporting]
Which of the following attributes of data provided to an automated log analysis tool is MOST important for effective risk monitoring?
A. Confidentiality
B. Scalability
C. Retention
D. Relevancy
Answer: D
The correct answer is D because the most important attribute of data fed into an automated log analysis tool is relevancy . For effective risk monitoring, the tool must receive data that is meaningful, useful, and directly related to the risks, events, controls, and activities being monitored. Irrelevant data reduces signal quality, obscures important indicators, and weakens timely detection.
The other options are less important for monitoring effectiveness itself:
A. Confidentiality is important for protecting the data, but it does not by itself make the monitoring effective.
B. Scalability is a system capability, not a core attribute of the data itself.
C. Retention is important for historical review and forensics, but not the most important factor for effective real-time or ongoing monitoring.
Exact Extracts supporting the answer:
“If the correct information was not received by the necessary recipients in time to allow proper action this can be categorized as relevance risk.”
“The most important consideration when implementing key risk indicators is linking the metric to a specific risk.”
“The MOST essential criterion for the effectiveness of operational metrics is relevance to the recipient.”
“The main purpose of continuous monitoring is detecting changes to the enterprise’s risk environment.”
These extracts directly support that relevant information is essential for useful monitoring and effective action. Therefore, relevancy is the most important attribute.
===========
QUESTION NO: 93 [Risk Assessment]
In the context of a business impact analysis (BIA) which of the following activities would be MOST complex and time-consuming for a risk practitioner in a large global organization?
A. Calculating recovery time objectives (RTOs)
B. Analyzing the financial impact of a disruption
C. Analyzing the interdependences between business departments
D. Identifying critical IT business processes and procedures
Answer: C
The correct answer is C because in a large global organization, the most complex and time-consuming BIA activity is analyzing the interdependencies between business departments . Large enterprises have numerous cross-functional, regional, operational, legal, and technical dependencies. Understanding how disruption in one area affects another is often the most difficult and resource-intensive part of a business impact analysis.
The other options are important, but generally less complex in a large global environment:
A. Calculating recovery time objectives (RTOs) is important, but it is usually derived after understanding process criticality and dependencies.
B. Analyzing the financial impact of a disruption can be difficult, but interdependency mapping is often broader and more complicated.
D. Identifying critical IT business processes and procedures is foundational, but in a global organization the network of dependencies is typically the harder task.
Exact Extracts supporting the answer:
“The objective of a business impact analysis is best described as the identification of time-sensitive critical business functions and interdependencies.”
“The most useful process in developing a series of recovery time objectives is business impact analysis.”
“A business impact analysis is primarily used to evaluate the impact of disruption on an enterprise’s ability to operate over time.”
“The main outcome of a business impact analysis (BIA) is the criticality of business processes.”
These extracts show that identifying interdependencies is central to BIA. In a large global organization, that makes it the most complex and time-consuming activity.
===========
QUESTION NO: 94 [Risk and Control Monitoring and Reporting]
Which of the following criteria is MOST important to include in an agreement with a penetration testing vendor?
A. Details of testing methods to be used
B. Expectations of code escrow safeguards
C. Scope of the systems to be assessed
D. Steps to remediate identified vulnerabilities
Answer: C
The correct answer is C because the most important criterion to include in an agreement with a penetration testing vendor is the scope of the systems to be assessed . Clear scope is essential to define what is authorized, what assets may be tested, what environments are in scope, and what boundaries apply. Without a clearly defined scope, testing could miss key assets or unintentionally affect systems that were not authorized for assessment.
The other options are less important as the primary agreement requirement:
A. Details of testing methods to be used are useful, but they come after scope is clearly established.
B. Expectations of code escrow safeguards are unrelated to most penetration testing agreements.
D. Steps to remediate identified vulnerabilities may follow from the test results, but they are not the most important initial contractual criterion.
Exact Extracts supporting the answer:
“Prior to conducting a penetration test the most important step is obtaining senior management approval of exercise parameters.”
“Before beginning a black box penetration test it ' s crucial to have a clearly stated definition of scope in place.”
“To best preserve service availability during a penetration test it ' s essential to schedule testing of critical systems during maintenance windows.”
“For an Internet-facing application penetration testing is the most effective control assessment type.”
These extracts directly support that clear scope is the most important criterion in an agreement with a penetration testing vendor.
Which of the following BEST helps to ensure disaster recovery staff members
are able to complete their assigned tasks effectively during a disaster?
Performing parallel disaster recovery testing
Documenting the order of system and application restoration
Involving disaster recovery staff members in risk assessments
Conducting regular tabletop exercises and scenario analysis
When of the following provides the MOST tenable evidence that a business process control is effective?
Demonstration that the control is operating as designed
A successful walk-through of the associated risk assessment
Management attestation that the control is operating effectively
Automated data indicating that risk has been reduced
Automated data indicating that risk has been reduced provides the most tenable evidence that a business process control is effective, because it shows the actual impact and outcome of thecontrol on the risk level. A demonstration that the control is operating as designed, a successful walk-through of the associated risk assessment, and a management attestation that the control is operating effectively are not the most tenable evidence, because they are based on subjective judgments, assumptions, or expectations, not on objective facts or results. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
An organization ' s financial analysis department uses an in-house forecasting application for business projections. Who is responsible for defining access roles to protect the sensitive data within this application?
IT risk manager
IT system owner
Information security manager
Business owner
According to the Data Roles and Responsibilities article, the business owner is the person who has authority over the business process that is supported by the data. The business owner is responsible for defining the access roles to protect the sensitive data within the application, as well as approving the access requests and ensuring the compliance with the data policies andstandards. The business owner may delegate this responsibility to a data steward, who is a person who acts on behalf of the business owner to manage the data quality, security, and usage. Therefore, the answer is D. Business owner. References = Data Roles and Responsibilities
Which of the following is the MOST important reason to integrate IT risk management practices into the enterprise-wide operational risk management framework?
To reduce conflicts of interest between IT and non-IT business units
To align the operational risk management framework with regulatory requirements
To optimize the efficiency of enterprise-wide risk management resources
To ensure IT risk scenarios are reflected in the corporate risk profile
Integration of IT risk management into enterprise-wide risk management ensures that IT-related risks arenot treated in isolationbut are included in the overallcorporate risk profile, reflecting their true impact on strategic and operational objectives.
According to the CRISC manual and ISACA’s Risk IT Framework:
IT risk is asubsetof enterprise risk and must be managed as part of the overall operational risk context.
Integrating IT risk management ensuresrisk aggregation and visibilityat the enterprise level, allowing accurate reporting to senior management and the board.
Supporting extract (CRISC Slide 32–33):
“The most important aspect for an effective IT risk management process is aligning with enterprise risk management. The primary goal of an enterprise’s IT risk management process is to protect the enterprise and its ability to perform its mission.”
This integration allows:
Inclusion of IT risk scenarios (e.g., data breaches, system outages) in overall enterprise risk assessments.
Unified reporting to management for strategic decisions.
A common language and tolerance level for all risk types.
Hence,D. To ensure IT risk scenarios are reflected in the corporate risk profileis the correct answer.
A hospital recently implemented a new technology to allow virtual patient appointments. Which of the following should be the risk practitioner ' s FIRST course of action?
Reassess the risk profile.
Modify the risk taxonomy.
Increase the risk tolerance.
Review the risk culture.
Reassessing the risk profile is the first course of action that a risk practitioner should take after a hospital recently implemented a new technology to allow virtual patient appointments. This is because reassessing therisk profile can help identify, analyze, and evaluate the new or changed risks that the new technology may introduce or affect, such as data privacy, security, quality, reliability, or compliance risks. Reassessing the risk profile can also help determine the appropriate risk response and mitigation strategies, as well as monitor and report the risk performance and outcomes. According to the CRISC Review Manual 2022, reassessing the risk profile is one of the key steps in the IT risk management process1. According to the web search results, reassessing the risk profile is a common and recommended practice for addressing the risks of virtual patient appointments
Which of the following is a risk practitioner ' s MOST appropriate course of action upon learning that an organization is not compliant with its patch management policy?
Document the concern in an issue tracker.
Strengthen data loss prevention (DLP) controls.
Apply the most recent available patches.
Escalate the issue to the ethics committee.
Which of the following is the PRIMARY reason for monitoring activities performed in a production database environment?
Ensuring that database changes are correctly applied
Enforcing that changes are authorized
Deterring illicit actions of database administrators
Preventing system developers from accessing production data
Ensuring that database changes are correctly applied is the primary reason for monitoring activities performed in a production database environment, as it helps to maintain the integrity, availability, and performance of the database and the applications that depend on it. Database changes are any modifications made to the database structure, configuration, data, or code, such as adding or deleting tables, columns, indexes, or triggers, updating or inserting data, or altering stored procedures or functions. Database changes can have significant impacts on the database functionality and behavior, and may introduce errors, inconsistencies, or vulnerabilities if not applied correctly. Therefore, monitoring database changes is essential to verify that the changes are implemented as intended, comply with the design specifications and standards, and do not cause any adverse effects or conflicts with the existing database or application components.
The other options are not the primary reasons for monitoring activities performed in a production database environment. Enforcing that changes are authorized is an important aspect of database change management, but it is not the main purpose of database monitoring. Database change management is the process of planning, reviewing, approving, and implementing database changes in a controlled and consistent manner. Database change management helps to ensure that the changes are authorized by the appropriate stakeholders, aligned with the business requirements and objectives, and documented and communicated to the relevant parties. Database monitoring can support database change management by providing information and feedback on the change implementation and performance, but it does not enforce the change authorization. Deterring illicit actions of database administrators is a possible benefit of database monitoring, but it is not the primary reason for it. Database administrators are the users who have the highest level of access and privilege to the database, and they are responsible for managingand maintaining the database operations and security. Database monitoring can help to deter illicit actions of database administrators by tracking and auditing their activities and actions on the database, and alerting or escalating any suspicious or malicious behavior. However, database monitoring is not the only or the most effective way to prevent or detect illicit actions of database administrators. Other measures, such as implementing the principle of least privilege, segregating duties, enforcing password policies, and encrypting data, are also necessary to protect the database from unauthorized or improper access or manipulation by database administrators or other users. Preventing system developers from accessing production data is apossible benefit of database monitoring, but it is not the primary reason for it. System developers are the users who design, develop, and test the applications that interact with the database. System developers should not have access to the production data, as it may contain sensitive or confidential information that could be compromised or misused by the developers. System developers should only use test or dummy data for their development and testing purposes. Database monitoring can help to prevent system developers from accessing production data by controlling and restricting their access and privilege to the database, and logging and reporting any unauthorized or inappropriate access attempts. However, database monitoring is not the only or the most effective way to prevent system developers from accessing production data. Other measures, such as implementing access control policies, masking or anonymizing data, and isolating development and production environments, are also necessary to safeguard the production data from system developers or other users. References = Database Monitoring: Basics & Introduction | Splunk, IT Risk Resources | ISACA, Best Practices for Database Performance Monitoring
Which of the following is a KEY responsibility of the second line of defense?
Implementing control activities
Monitoring control effectiveness
Conducting control self-assessments
Owning risk scenarios
The second line of defense is a group of functions that provide oversight, guidance, and monitoring of the risk management activities of the first line of defense. The second line of defense includes risk management, compliance, and internal control departments. Their key responsibility is to monitor the effectiveness of the control activities implemented by the first line of defense, and to report any issues or gaps to senior management and the board. The second line of defense also supports the first line of defense by providing frameworks, policies, tools,and techniques to identify, measure, and manage risks. The other options are not the key responsibility of the second line of defense, as explained below:
A. Implementing control activities is the responsibility of the first line of defense, which consists of the business units and process owners that own and manage the risks associated with their daily operations.
C. Conducting control self-assessments is a technique used by the first line of defense to evaluate the design and operation of their own controls, and to identify and report any deficiencies or improvement opportunities.
D. Owning risk scenarios is the responsibility of the first line of defense, which is accountable for the risks inherent in their business activities, and for developing and executing risk response strategies. References = Modernizing The Three Lines of Defense Model | Deloitte US, The second line of defence: fit for purpose, not an uncomfortable fit | Knowledge | Linklaters, COSO’s Take on the Three Lines of Defense | ERM - Enterprise Risk Management, Three Lines of Defense | Risk Management - Schneider Downs CPAs, What is the Three Lines of Defense Approach to Risk Management?
Which of the following is the BEST method for assessing control effectiveness against technical vulnerabilities that could be exploited to compromise an information system?
Vulnerability scanning
Systems log correlation analysis
Penetration testing
Monitoring of intrusion detection system (IDS) alerts
Penetration testing is the best method for assessing control effectiveness against technical vulnerabilities that could be exploited to compromise an information system, as it simulates areal-world attack scenario and evaluates the security posture of the system. Penetration testing is a type of security testing that involves performing authorized and ethical hacking activities on a system to identify and exploit its vulnerabilities and weaknesses. Penetration testing can help to measure and improve the effectiveness and efficiency of the controls implemented to protect the system from unauthorized access, modification, or damage.
The other options are not the best methods for assessing control effectiveness against technical vulnerabilities that could be exploited to compromise an information system. Vulnerability scanning is an automated process that uncovers potential vulnerabilities in systems and software, but it does not provide information on the impact and severity of the vulnerability or how they can be exploited using different exploitation techniques1. Systems log correlation analysis is a process of examining and analyzing the records of system activities and events, but it does not directly test the controls or simulate the attack scenarios. Monitoring of intrusion detection system (IDS) alerts is a process of tracking and auditing the system or network for any signs of malicious or anomalous activities, but it does not evaluate the control performance or identify the root causes of the vulnerabilities. References = Vulnerability Assessment Principles | Tenable®, A Complete Guide on Vulnerability Assessment Methodology, Karen Scarfone Scarfone Cybersecurity - NIST Computer Security Resource …
An organization is considering modifying its system to enable acceptance of credit card payments. To reduce the risk of data exposure, which of the following should the organization do FIRST?
Conduct a risk assessment.
Update the security strategy.
Implement additional controls.
Update the risk register.
The FIRST thing that the organization should do to reduce the risk of data exposure when modifying its system to enable acceptance of credit card payments is to conduct a risk assessment, because it is a process that involves identifying and analyzing the potential risks, threats, and vulnerabilities that may affect the system and the data, and their likelihood and impact on the business objectives and processes. A risk assessment can help to determine the current risk level and exposure, and to provide the basis for selecting and implementing the appropriate risk responses and controls. The other options are not the first thing that the organization should do, because:
Option B: Updating the security strategy is a result of conducting a risk assessment, but not the first thing that the organization should do. A security strategy is a plan that defines the security objectives, policies, standards, and procedures for the system and the data, and it should be aligned with the risk assessment results and the business requirements and expectations.
Option C: Implementing additional controls is a response to the risk assessment results, but not the first thing that the organization should do. Controls are the measures that are designed and implemented to prevent or reduce the occurrence or impact of the risks, threats, and vulnerabilities, and to ensure the confidentiality, integrity, and availability of the system and the data.
Option D: Updating the risk register is a part of the risk assessment process, but not the first thing that the organization should do. A risk register is a tool that documents and tracks the identified risks, their characteristics, their status, and their responses, and it should be updated regularly to reflect the current risk profile and exposure of the system and the data. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 108.
Which of the following should be done FIRST when developing an initial set of risk scenarios for an organization?
Refer to industry standard scenarios.
Use a top-down approach.
Consider relevant business activities.
Use a bottom-up approach.
Which of the following is MOST important for successful incident response?
The quantity of data logged by the attack control tools
Blocking the attack route immediately
The ability to trace the source of the attack
The timeliness of attack recognition
The most important factor for successful incident response is the timeliness of attack recognition. Incident response is the process of detecting, analyzing, containing, eradicating, recovering, and reporting on security incidents that could affect the organization’s IT systems or data. The timeliness of attack recognition is the speed and accuracy with which the organization can identify and confirm that an attack has occurred or is in progress. The timeliness of attack recognition is crucial for successful incident response, as it affects the ability and effectiveness of the organization to respond to and mitigate the attack, and to minimize the damage and impact of the attack. The other options are not as important as the timeliness of attack recognition, although they may also contribute to or influence the incident response. The quantity of data logged by the attack control tools, the ability to trace the source of the attack, and the blocking of the attack route immediately are all factors that could help or hinder the incident response, but they are not the most important factor for successful incident response. References = CISA Review Manual, 27th Edition, Chapter 5, Section 5.4.1, page 5-32.
The BEST use of key risk indicators (KRIs) is to provide:
Early indication of increasing exposure to a specific risk.
Lagging indication of major information security incidents.
Early indication of changes to required risk response.
Insight into the performance of a monitored process.
Key risk indicators are designed to provide early warnings about increasing risk exposure, enabling timely risk mitigation efforts. This supports proactive risk management, as outlined in theRisk Monitoring and Reportingdomain of CRISC.
In which of the following system development life cycle (SDLC) phases should controls be incorporated into system specifications?
Implementation
Development
Design
Feasibility
Controls should be incorporated into system specifications in the design phase of the system development life cycle (SDLC), because this is the phase where the system requirements are translated into detailed specifications and architectures that define how the system will be built and operated. Incorporating controls in the design phase ensures that the system is secure, reliable, and compliant from the start, and reduces the cost and complexity of implementing controls later in the SDLC. The other options are not the correct answers, because they are not the phases where controls are incorporated into system specifications. The implementation phase is the phase where the system is installed, configured, and tested. The development phase is the phase where the system is coded, integrated, and tested. The feasibility phase is the phase where the system concept and scope are defined and evaluated. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Who should be responsible for strategic decisions on risk management?
Chief information officer (CIO)
Executive management team
Audit committee
Business process owner
Strategic decisions on risk management are the decisions that involve setting the direction, objectives, and priorities for risk management within an organization, as well as aligning them with the organization’s overall strategy, vision, and mission1. Strategic decisions on riskmanagement also involve defining the organization’s risk appetite and tolerance, which are the amount and level of risk that the organization is willing and able to accept to achieve its goals2. The responsibility for strategic decisions on risk management should belong to the executive management team, which is the group of senior leaders who have the authority and accountability for the organization’s performance and governance3. The executive management team has the best understanding of the organization’s strategic context, environment, and stakeholders, and can make informed and balanced decisions that consider the benefits and costsof risk-taking4. The executive management team also has the ability and responsibility to communicate and cascade the strategic decisions on risk management to the rest of the organization, and to monitor and evaluate their implementation and outcomes5. The chief information officer (CIO), the audit committee, and the business process owner are not the best choices for being responsible for strategic decisions on risk management, as they do not have the same level of authority and accountability as the executive management team. The CIO is the senior leader who oversees the organization’s information andtechnology strategy, resources, and systems6. The CIO may be involved in providing input and feedback to the executive management team on the strategic decisions on risk management, especially those related to IT risk, but they do not have the final say or the overall responsibility for them. The audit committee is a subcommittee of the board of directors that oversees the organization’s financial reporting, internal controls, and external audits7. The audit committee may be involved in reviewing and approving the strategic decisions on risk management, as well as ensuring their compliance with the relevant laws and standards, but they do not have the authority or the expertise to make or implement them. The business process owner is the person who has the authority and accountability for a business process that supports or enables the organization’s objectives and functions. The business process owner may be involved in executing and reporting on the strategic decisions on risk management, as well as identifying and mitigating the risks related to their business process, but they do not have the perspective or the influence to make or communicate them. References = 1: Strategic Risk Management: Complete Overview (With Examples)2: [Risk Appetite and Tolerance - ISACA] 3: [Senior Management - Definition, Roles andResponsibilities] 4: Stanford Strategic Decision and Risk Management | Stanford Online5: A 7-Step Process for Strategic Risk Management — RiskOptics - Reciprocity6: [Chief Information Officer (CIO) - Gartner ITGlossary] 7: [Audit Committee - Overview, Functions, and Responsibilities] : [Business Process Owner - Gartner IT Glossary] : [Business Process Owner - Roles and Responsibilities] : [Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.1: IT Risk Concepts, pp. 17-19.]
Which of the following should be considered FIRST when assessing risk associated with the adoption of emerging technologies?
Organizational strategy
Cost-benefit analysis
Control self-assessment (CSA)
Business requirements
The first factor that should be considered when assessing risk associated with the adoption of emerging technologies is the organizational strategy. The organizational strategy defines the vision, mission, goals, and objectives of the enterprise, and provides the direction and guidance for its activities and decisions. The adoption of emerging technologies should be aligned with the organizational strategy, and support its achievement and performance. The organizational strategy also helps to determine the risk appetite and tolerance of the enterprise, and the criteria for evaluating the risks and benefits of the emerging technologies. Cost-benefit analysis, control self-assessment, and business requirements are also important factors to consider when assessing risk associated with the adoption of emerging technologies, but they are not the first factor to consider. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.1.1, page 181
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 656.
Which of the following is the BEST way to support communication of emerging risk?
Update residual risk levels to reflect the expected risk impact.
Adjust inherent risk levels upward.
Include it on the next enterprise risk committee agenda.
Include it in the risk register for ongoing monitoring.
Emerging risk is a risk that is new or evolving, and has the potential to significantly affect the enterprise’s objectives, performance, or reputation. Emerging risk can arise from changes in the internal or external environment, such as technological innovations, regulatory developments, or social trends. The best way to support communication of emerging risk is to include it on the next enterprise risk committee agenda. The enterprise risk committee is a group of senior executives who oversee the enterprise-wide risk management program, and provide guidance and direction to the risk owners and practitioners. By including the emerging risk on the agenda, the risk practitioner can ensure that the enterprise risk committee is aware of the risk, its causes, impacts, and likelihood, and can decide on the appropriate risk response strategy and actions. The other options are not the best way to support communication of emerging risk, as they involve different aspects of the risk management process:
Update residual risk levels to reflect the expected risk impact means that the risk practitioner adjusts the risk levels after considering the existing or planned risk responses. This may not befeasible or accurate for emerging risk, as the risk responses may not be defined or implemented yet, or may not be effective for the new or evolving risk.
Adjust inherent risk levels upward means that the risk practitioner increases the risk levels before considering any risk responses. This may not reflect the true nature or magnitude of the emerging risk, as the inherent risk levels are based on the assumptions and estimates of the risk practitioner, and may not account for the uncertainties or complexities of the emerging risk.
Include it in the risk register for ongoing monitoring means that the risk practitioner records and tracks the emerging risk, its causes, impacts, likelihood, responses, and owners. This is an important step in the risk management process, but it does not necessarily support communication ofthe emerging risk, as the risk register may not be accessible or visible to all the relevant stakeholders, or may not be updated or reviewed frequently enough to capture the changes in the emerging risk. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.2.2, pp. 21-22.
Which of the following emerging technologies is frequently used for botnet distributed denial of service (DDoS) attacks?
Internet of Things (IoT)
Quantum computing
Virtual reality (VR)
Machine learning
Internet of Things (IoT) is an emerging technology that refers to the network of devices, such as cameras, sensors, appliances, or vehicles, that can communicate and exchange data via the internet. IoT is frequently used for botnet distributed denial of service (DDoS) attacks, which are cyberattacks that aim to disrupt or disable a target’s online services by overwhelming them with traffic from multiple sources. IoT devices are often unsecured, unpatched, or misconfigured, which makes them vulnerable to being infected by malware and controlled by attackers. Attackers can use IoT devices to create large and powerful botnets that can launch DDoS attacks against various targets, such as websites, servers, or networks. According to the CRISC Review Manual 2022, IoT is one of the key emerging technologies that pose new IT risks, including DDoS attacks1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, IoT is the correct answer to this question2. According to the web search results, IoT devices are commonly used for botnet DDoS attacks, such as the Mirai botnet, the Emotet botnet, and the BoT-IoT dataset345.
Which of the following provides the MOST useful information for developing key risk indicators (KRIs)?
Business impact analysis (BIA) results
Risk scenario ownership
Risk thresholds
Possible causes of materialized risk
Key risk indicators (KRIs) are metrics that provide an early warning of increasing risk exposure in various areas of the organization. They help to monitor changes in the level of risk and enable timely actions to mitigate the risk. The most useful information for developing KRIs is the possible causes of materialized risk, which are the factors or events that trigger or contribute to the occurrence of a risk. By identifying the possible causes of materialized risk, an organization can design KRIs that measure the likelihood and impact of the risk, and alert the management when the risk exceeds the acceptable level. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following would BEST indicate to senior management that IT processes are improving?
Changes in the number of intrusions detected
Changes in the number of security exceptions
Changes in the position in the maturity model
Changes to the structure of the risk register
The best indicator to senior management that IT processes are improving is the changes in the position in the maturity model. A maturity model is a framework that defines the levels of capability and performance of a process, such as IT processes, based on the criteria such as governance, management, control, measurement, and improvement. A maturity model can help to assess the current state and the desired state of the IT processes, and to identify the gaps, strengths, and opportunities for improvement. A maturity model can also help to communicate the progress and the value of the IT processes to the senior management, and to support the strategic alignment and integration of the IT processes with the business objectives. Changes in the position in the maturity model indicate that the IT processes are improving, as they show that the IT processes are moving from a lower level to a higher level of maturity, and that they are achieving higher standards of quality, efficiency, and effectiveness. Changes in the number of intrusions detected, changes in the number of security exceptions, and changes to the structure of the risk register are not as good as changes in the position in the maturity model, as they do not provide a comprehensive and consistent measure of the IT processes improvement, and they may not reflect the actual impact and performance of the IT processes. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 36.
Risk mitigation procedures should include:
buying an insurance policy.
acceptance of exposures
deployment of counter measures.
enterprise architecture implementation.
Risk mitigation procedures are the actions and plans that an organization implements to reduce the likelihood and impact of identified risks. Risk mitigation procedures should include the deployment of counter measures, which are the specific controls or solutions that address the root causes or sources of the risks, and prevent or minimize the potential losses or damages. For example, a counter measure for therisk of data breach could be encrypting the data or implementing a firewall. The deployment of counter measures should be based on a cost-benefit analysis, a risk assessment, and a risk response strategy. The other options are not necessarily part of risk mitigation procedures. Buying an insurance policy is an example of risk transfer,which is a risk response strategy that shifts the responsibility or burden of the risk to another party, such as an insurer or a vendor. However, risk transfer does not eliminate or reduce the risk itself, and it may involve additional costs or conditions. Acceptance of exposures is an example of risk acceptance, which is a risk response strategy that acknowledges the existence and consequences of the risk, and decides not to take any action to change the risk situation. However, risk acceptance does not mitigate the risk, and it may require contingency plans or reserves to deal with the potential outcomes. Enterprise architecture implementation is an example of a business process or project that may involve or create risks, but it is not a risk mitigation procedure itself. Enterprise architecture is the design and structure of an organization’s IT systems, networks, and resources, and how they align with the organization’s goals and strategies. Enterprise architecture implementation may require risk management activities, such as risk identification, assessment, and response, but it is not a risk mitigation procedure itself. References = Risk IT Framework, ISACA, 2022, p. 151
A business unit has decided to accept the risk of implementing an off-the-shelf, commercial software package that uses weak password controls. The BEST course of action would be to:
obtain management approval for policy exception.
develop an improved password software routine.
select another application with strong password controls.
continue the implementation with no changes.
A policy exception is a deviation from the established policies, standards, or procedures of the enterprise, such as the information security policy. A policy exception may be granted by the management when there is a valid business reason or justification for the deviation, and when the risk associated with the deviation is acceptable or mitigated. The best course of action when a business unit has decided to accept the risk of implementing an off-the-shelf, commercialsoftware package that uses weak password controls is to obtain management approval for policy exception. This will ensure that the business unit is aware of the implications and consequences of the policy exception, and that the management agrees with the risk acceptance and approves the policy exception. The other options are not the best course of action, as they involve different risk response strategies or outcomes:
Develop an improved password software routine means that the business unit modifies or enhances the password controls of the software package, such as by increasing the password length, complexity, or expiration. This may not be a feasible or effective way to address the risk of weak password controls, as it may violate the terms and conditions of the software vendor, or may not be compatible or consistent with the software package.
Select another application with strong password controls means that the business unit replaces the software package with another application that has better password controls, such as by using encryption, authentication, or authorization. This may not be a desirable or efficient way to address the risk of weak password controls, as it may incur additional costs, delays, or complexities, or may not meet the business requirements or expectations of the business unit.
Continue the implementation with no changes means that the business unit proceeds with the software package without any modifications or improvements to the password controls, or without any approval or documentation of the policy exception. This may not be a responsible or ethical way to address the risk of weak password controls, as it may expose the enterprise to legal, financial, or reputational risks, or may compromise the security or compliance of the enterprise. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.4.1.1, pp. 121-122.
During a risk treatment plan review, a risk practitioner finds the approved risk action plan has not been completed However, there were other risk mitigation actions implemented. Which of the fallowing is the BEST course of action?
Review the cost-benefit of mitigating controls
Mark the risk status as unresolved within the risk register
Verify the sufficiency of mitigating controls with the risk owner
Update the risk register with implemented mitigating actions
The best course of action for a risk practitioner who finds that the approved risk action plan has not been completed but other risk mitigation actions have been implemented is to verify the sufficiency of mitigating controls with the risk owner. This is because the risk owner is the person who is accountable for the risk and the risk response strategy, and therefore should be consulted to ensure that the alternative actions are adequate and effective in reducing the risk to an acceptable level. The other options are not the best course of action, although they may also be performed after verifying the sufficiency of mitigating controls with the risk owner. Reviewing the cost-benefit of mitigating controls, marking the risk status as unresolved within the risk register, and updating the risk register with implemented mitigating actions are secondary actions that depend on the outcome of the verification process. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.3.2, p. 193.
A risk practitioner has been asked to evaluate a new cloud-based service to enhance an organization ' s access management capabilities. When is the BEST time for the risk practitioner to provide opinions on control strength?
After the initial design
Before production rollout
After a few weeks in use
Before end-user testing
Providing opinions on control strength after the initial design is the best time for the risk practitioner, because it helps to ensure that the controls are aligned with the requirements and objectives of the new cloud-based service, and that they are effective and efficient in mitigating the risks associated with the service. A cloud-based service is a service that is delivered over the internet, where the service provider owns and manages the IT infrastructure, platforms, or applications, and the customer pays only for the resources or functions they use. An access management capability is a capability that enables the organization to control and monitor the access to its IT systems or networks, such as authentication, authorization, or auditing. Controls are policies, procedures, or mechanisms that help to reduce or eliminate the risks that may affect the security, reliability, performance, or compliance of the cloud-based service. Providing opinions on control strength after the initial design is the best time, as it allows the risk practitioner to review the design specifications and requirements, and to provide feedback and recommendations on the adequacy and suitability of the controls. Providing opinions on control strength before production rollout, after a few weeks in use, or before end-user testing are all possible times for the risk practitioner, but they are not the best time, as they may be too late or too early to influence the design and implementation of the controls. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.1, page 183
Which of the following is the FIRST step in risk assessment?
Review risk governance
Asset identification
Identify risk factors
Inherent risk identification
The first step in risk assessment is asset identification, which is the process of identifying and documenting the assets that are relevant and valuable to the organization, such as people, information, systems, processes, or infrastructure1. Asset identification can help to:
Establish the scope and boundaries of the risk assessment, and ensure that all the assets within the scope are considered and covered2.
Determine the criticality and priority of the assets, and assign them appropriate values or ratings based on their importance and contribution to the organization’s objectives3.
Identify the potential threats and vulnerabilities that may affect the assets, and assess their likelihood and impact on the assets4.
The other options are not the first step in risk assessment, because:
Review risk governance is not the first step, but rather a prerequisite or a foundation for risk assessment. Risk governance is the system of principles, policies, roles, and responsibilities that guide and oversee the risk management activities and initiatives of the organization5. Reviewing risk governance can help to ensure that the risk assessment is aligned with the organization’sriskstrategy, culture, and appetite, and that the risk assessment process is consistent, effective, and efficient6.
Identify risk factors is not the first step, but rather a subsequent or a parallel step to asset identification. Risk factors are the elements or conditions that influence or contribute to the occurrence or outcome of a risk event7. Identifying risk factors can help to understand the causes and sources of the risks, and to analyze and evaluate the risks based on their probability and severity.
Inherent risk identification is not the first step, but rather a later or a dependent step on asset identification and risk factor identification. Inherent risk is the level of risk that exists before the implementation of risk responses. Identifying inherent risk can help to measure the exposure or uncertainty of the assets, and to determine the need and extent of the risk responses.
References =
Risk Governance - CIO Wiki
Risk Governance Framework - CIO Wiki
Asset Identification - CIO Wiki
Asset Identification and Valuation - ISACA
Asset Criticality - CIO Wiki
Threat and Vulnerability Assessment - CIO Wiki
Risk Factor - CIO Wiki
[Risk Factor Analysis - CIO Wiki]
[Inherent Risk - CIO Wiki]
[Inherent Risk Assessment - CIO Wiki]
[Risk Assessment - CIO Wiki]
Which of the following is the MOST important enabler of effective risk management?
User awareness of policies and procedures
Implementation of proper controls
Senior management support
Continuous monitoring of threats and vulnerabilities
According to the CRISC Review Manual1, senior management support is the commitment and involvement of the top-level executives and leaders in the risk management process. Senior management support is the most important enabler of effective risk management, as it helps to establish and communicate the risk vision, strategy, and culture of the organization. Senior management support also helps to allocate the necessary resources, authority, and accountability for risk management, and to ensure the alignment of the risk management objectives and activities with the organization’s strategy, goals, and values. References = CRISC Review Manual1, page 198.
Which of the following is the MOST effective way to help ensure future risk levels do not exceed the organization ' s risk appetite?
Establishing a series of key risk indicators (KRIs).
Adding risk triggers to entries in the risk register.
Implementing key performance indicators (KPIs).
Developing contingency plans for key processes.
KRIs provide predictive metrics to monitor changes in risk levels, enabling timely interventions to maintain risks within the organization ' s appetite. This aligns with theRisk Monitoring and Reportingframework, which emphasizes proactive identification of risk thresholds.
Which of the following BEST helps to mitigate risk associated with users inputting incorrect data into a system?
Sequence check
Tool tips
User training
Allowed values
The correct answer isDbecauseallowed valuesis the best control to mitigate the risk of users entering incorrect data into a system. Allowed values are an input validation control that restricts entries to predefined acceptable data, preventing invalid or improper inputs at the point of entry.
The other options are less effective:
A. Sequence checkis useful for detecting missing or duplicate sequence items, but not for general incorrect input values.
B. Tool tipsmay guide users, but they do not enforce correct input.
C. User traininghelps reduce errors, but it is weaker than an automated preventive input control.
Exact Extracts supporting the answer:
“In reviewing transaction data for fraudulent activity the concept of data validation that is MOST likely to be of value to enterprises is reasonableness.”
“To validate data integrity during processing in multiple applications the BEST assurance for maintaining data integrity is provided by range checking.”
“The vulnerability that makes a web application MOST susceptible to a SQL injection attack is inadequate validation of input.”
“The attack that occurs PRIMARILY because user input is not properly validated is cross-site scripting.”
These extracts support that the strongest mitigation for incorrect user input isinput validation, and among the choices,allowed valuesis the best preventive control.
===========
When an organization’s disaster recovery plan (DRP) has a reciprocal agreement, which of the following risk treatment options is being applied?
Acceptance
Mitigation
Transfer
Avoidance
A reciprocal agreement is an agreement made by two or more organizations to use each other’s resources during a disaster1. For example, two organizations with similar IT infrastructure may agree to provide backup servers or data centers for each other in case of a major disruption. By doing so, they transfer the risk of losing their IT capabilities to the other party, who agrees to share the responsibility and cost of recovery.
A reciprocal agreement is a form of risk transfer, which is one of the four risk treatment options according to ISO 270012. Risk transfer means that the organization shifts the potential negative consequences of a risk to another party, such as an insurance company, a vendor, or a partner. This reduces the organization’s exposure and liability to the risk, but it does not eliminate the risk completely, as the other party may fail to fulfill their obligations or charge a high price for their services.
References = Reciprocal Agreement - Risky Thinking, ISO 27001 Risk Assessment & Risk Treatment: The Complete Guide - Advisera
Which of the following would provide the MOST useful information for communicating an organization’s risk level to senior management?
A list of organizational threats
A high-level risk map
Specialized risk publications
A list of organizational vulnerabilities
Ahigh-level risk mapvisually summarizes risk exposure by plottinglikelihood versus impactfor all key risk scenarios. This helps senior management quickly identify priority risks.
ISACA CRISC notes:
“Risk heat maps or risk matrices are effective tools to communicate risk levels to executives because they visually demonstrate the distribution and severity of risks across the organization.”
Threat lists (A) or vulnerability lists (D) are too detailed and not decision-oriented.
Therefore,B. A high-level risk mapis correct.
CRISC Reference:Domain 4 – Risk and Control Monitoring and Reporting, Topic: Risk Communication Tools and Dashboards.
A recently purchased IT application does not meet project requirements. Of the following, who is accountable for the potential impact?
Business analyst
Project sponsor
IT project team
IT project management office (PMO)
Which of the following should be the HIGHEST priority when developing a risk response?
The risk response addresses the risk with a holistic view.
The risk response is based on a cost-benefit analysis.
The risk response is accounted for in the budget.
The risk response aligns with the organization ' s risk appetite.
A risk response is the action or plan that is taken to address a specific risk that has been identified, analyzed, and evaluated. It can be one of the following types: mitigate, transfer, avoid, or accept.
The highest priority when developing a risk response is to ensure that it aligns with the organization’s risk appetite, which is the amount and type of risk that the organization is willing to accept in pursuit of its goals. The risk appetite is usually expressed as a range or a threshold, and it is aligned with the organization’s strategy and culture.
Aligning the risk response with the organization’s risk appetite ensures that the risk response is consistent, appropriate, and proportional to the level and nature of the risk, and that it supports the organization’s objectives and values. It also helps to optimize the balance between risk and return, and to create and protect value for the organization and its stakeholders.
The other options are not the highest priority when developing a risk response, because they do not address the fundamental question of whether the risk response is suitable and acceptable for the organization.
The risk response addresses the risk with a holistic view means that the risk response considers the interrelationships and dependencies among the risk sources, events, impacts, and responses, and the potential secondary and residual effects of the risk response. This is important to ensure that the risk response is comprehensive and effective, and that it does not create new or unintended risks, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite.
The risk response is based on a cost-benefit analysis means that the risk response compares the expected costs and benefits of implementing the risk response, and selects the risk response that provides the most favorable net outcome. This is important to ensure that the risk response is efficient and economical, and that it maximizes the return on investment, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite.
The risk response is accounted for in the budget means that the risk response is included in the financial plan and allocation of resources for the organization or the project. This is important toensure that the risk response is feasible and realistic, and that it has the necessary funding and support, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 29-30, 34-35, 38-39, 44-45, 50-51, 54-55
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 147
Which of the following risk register updates is MOST important for senior management to review?
Extending the date of a future action plan by two months
Retiring a risk scenario no longer used
Avoiding a risk that was previously accepted
Changing a risk owner
A risk register is a document that records and tracks the information and status of the identified risks and their responses. It includes the risk description, category, source, cause, impact, probability, priority, response, owner, action plan, status, etc.
A risk register update is a change or modification to the information or status of the risks and their responses in the risk register. It may be triggered by the occurrence or resolution of a risk event, the identification or evaluation of a new or emerging risk, the implementation or completion of a risk response, the monitoring or review of the risk performance, etc.
The most important risk register update for senior management to review is avoiding a risk that was previously accepted, which means that the organization has decided to eliminate or withdraw from the risk exposure or activity that may cause the risk, instead of tolerating or retaining the risk as before. This may indicate a significant change in the organization’s risk appetite, strategy, objectives, or environment, and it may have a major impact on the organization’s performance and value.
The other options are not the most important risk register updates for senior management to review, because they do not indicate a significant change or impact on the organization’s risk profile or performance.
Extending the date of a future action plan by two months means that the organization has postponed the implementation or completion of the planned actions or measures to address the risk, due to some reasons or constraints. This may indicate a delay or deviation from the expected or desired risk outcome, but it may not have a major impact on the organization’s performance and value, unless the risk is very urgent or critical.
Retiring a risk scenario no longer used means that the organization has removed or discarded the risk scenario that is no longer relevant or applicable to the organization’s objectives or operations, due to some changes or developments. This may indicate a reduction or improvement in the organization’s risk exposure or level, but it may not have a major impact on the organization’s performance and value, unless the risk scenario was very significant or influential.
Changing a risk owner means that the organization has assigned or transferred the responsibility and accountability for the risk and its response to a different person or role, due to some reasons or circumstances. This may indicate a change or improvement in the organization’s risk governance or culture, but it may not have a major impact on the organization’s performance and value, unless the risk owner was very ineffective or inappropriate. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 160
CRISC Practice Quiz and Exam Prep
Which of the following BEST enables the identification of trends in risk levels?
Correlation between risk levels and key risk indicators (KRIs) is positive.
Measurements for key risk indicators (KRIs) are repeatable
Quantitative measurements are used for key risk indicators (KRIs).
Qualitative definitions for key risk indicators (KRIs) are used.
Key risk indicators (KRIs) are metrics or measures that provide information on the current or potential exposure and performance of an organization in relation to specific risks. KRIs can help to monitor and track the changes or trends in the risk level and the risk response over time, identify and alert the risk issues or events that require attention or action, evaluate and report the effectiveness and efficiency of the risk management processes and practices, and support and inform the risk decision making and improvement1.
The best way to enable the identification of trends in risk levels is to ensure that the correlation between risk levels and KRIs is positive, because it means that the KRIs are aligned with andreflective of the risk levels, and that they can capture and indicate the variations or movements in the risk levels accurately and reliably. A positive correlation between risk levels and KRIs can be achieved by:
Selecting and defining the KRIs that are relevant and appropriate for the specific risks that the organization faces, and that are consistent and comparable across different domains and contexts
Collecting and analyzing the data and information that are reliable and sufficient for the KRIs, and that are sourced from various methods and sources, such as risk assessments, audits, monitoring, alerts, or incidents
Applying and using the tools and techniques that are suitable and feasible for the KRIs, such as risk matrices, risk registers, risk indicators, or risk models
Reviewing and updating the KRIs periodically or as needed, and ensuring that they reflect the current or accurate risk levels, which may change over time or due to external factors23
The other options are not the best ways to enable the identification of trends in risk levels, but rather some of the factors or aspects of KRIs. Measurements for KRIs are repeatable is a factor that can enhance the reliability and validity of the KRIs, as it means that the KRIs can produce the same or similar results under the same or similar conditions. However, repeatability does not necessarily imply accuracy or sensitivity, and it may not capture or reflect the changes or trends in the risk levels. Quantitative measurements are used for KRIs is an aspect that can improve the objectivity and precision of the KRIs, as it means that the KRIs are expressed in numerical or measurable values, such as percentages, probabilities, or monetary amounts. However, quantitative measurements may not be suitable or feasible for all types of risks or KRIs, and they may not capture or reflect the complexity or uncertainty of the risk levels. Qualitative definitions for KRIs are used is an aspect that can enhance the understanding and communication of the KRIs, as it means that the KRIs are expressed in descriptive or subjective terms, such as high, medium, or low, based on criteria such as likelihood, impact, or severity. However, qualitative definitions may not be consistent or comparable across different risks or KRIs, and they may not capture or reflect the magnitude or variation of the risk levels. References =
Key Risk Indicators: What They Are and How to Use Them
Key Risk Indicators: A Practical Guide | SafetyCulture
Key Risk Indicators: Types and Examples
[CRISC Review Manual, 7th Edition]
An organization has decided to use an external auditor to review the control environment of an outsourced service provider. The BEST control criteria to evaluate the provider would be based on:
a recognized industry control framework
guidance provided by the external auditor
the service provider ' s existing controls
The organization ' s specific control requirements
The best control criteria to evaluate the outsourced service provider would be based on a recognized industry control framework. A control framework is a set of best practices, guidelines, and methodologies that provide a comprehensive and consistent approach to designing, implementing, and assessing controls. A recognized industry control framework is a control framework that is widely accepted and adopted by the industry and the regulators, and that reflects the current and emerging standards andexpectations for the control environment. A recognized industry control framework can help to ensure that the outsourced service provider meets the minimum and acceptable level of control quality and effectiveness, and that the control evaluation is objective, reliable, and comparable. The other options are not as good as a recognized industry control framework, as they are related to the specific sources, aspects, or requirements of the control criteria, not the overall structure and quality of the control criteria. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: IT Control Assessment, page 69.
Which of the following is the PRIMARY benefit when senior management periodically reviews and updates risk appetite and tolerance levels?
It ensures compliance with the risk management framework.
It ensures an effective risk aggregation process.
It ensures decisions are risk-informed.
It ensures a consistent approach for risk assessments.
Risk appetite and tolerance reflect strategic priorities. As business and external environments evolve, regular updates ensure that risk responses and decisions remain aligned with organizational goals and acceptable boundaries.
Which of the following presents the GREATEST privacy risk related to personal data processing for a global organization?
Privacy risk awareness training has not been conducted across the organization.
The organization has not incorporated privacy into its risk management framework.
The organization allows staff with access to personal data to work remotely.
Personal data processing occurs in an offshore location with a data sharing agreement.
Greatest Privacy Risk:
Jurisdictional Challenges: Processing personal data in an offshore location often involves dealing with different legal and regulatory requirements, which can complicate compliance with data privacy laws such as GDPR or CPRA.
Data Transfer Risks: Even with a data sharing agreement, the protection and enforcement of privacy rights can be less stringent in the offshore location compared to the home jurisdiction. This can lead to increased risks of data breaches and misuse.
Enforcement Difficulties: If privacy violations occur, enforcing legal actions across borders can be challenging, potentially leading to inadequate redress for affected individuals.
Comparison with Other Options:
Privacy Risk Awareness Training Not Conducted: This is a significant risk but can be mitigated relatively quickly with proper training programs.
Privacy Not Incorporated into Risk Management Framework: While critical, the risk can be managed by integrating privacy into the framework without immediate severe consequences.
Remote Work by Staff with Access to Personal Data: This introduces risks related to secure access and data protection but can be managed with proper security controls.
Best Practices:
Data Sovereignty Considerations: Ensure data is processed in jurisdictions with strong privacy laws that align with the organization ' s regulatory requirements.
Regular Audits and Assessments: Conduct regular audits of data processing practices in offshore locations to ensure compliance with data privacy agreements.
Legal Safeguards: Establish robust legal safeguards and contracts to enforce data protection standards across jurisdictions.
The PRIMARY reason for a risk practitioner to review business processes is to:
Benchmark against peer organizations.
Identify appropriate controls within business processes.
Assess compliance with global standards.
Identify risk owners related to business processes.
A review of business processes is crucial for identifying risk owners, as risk ownership is tied to specific processes within the organization. Risk owners are accountable for managing and mitigating risks within their respective areas. This ensures that risks are effectively addressed where they arise and aligns mitigation efforts with business objectives. Properly identifying risk owners supports better governance, accountability, and alignment with the organization ' s risk management strategy.
Which of the following controls BEST enables an organization to ensure a complete and accurate IT asset inventory?
Prohibiting the use of personal devices for business
Performing network scanning for unknown devices
Requesting an asset list from business owners
Documenting asset configuration baselines
IT asset inventory is the process of tracking and managing the financial, physical, licensing, and contractual aspects of IT assets throughout their life cycle1. IT assets include hardware, software, and network components that an organization values and uses to achieve its objectives2. A complete and accurate IT asset inventory can help an organization to optimize its IT budget, reduce security risks, ensure compliance, and improve performance3.
One of the best controls to enable an organization to ensure a complete and accurate IT asset inventory is performing network scanning for unknown devices. Network scanning is the process of identifying and collecting information about the devices connected to a network, such as their IP addresses, operating systems, open ports, services, and vulnerabilities4. Network scanning can help an organization to:
Discover and inventory all the IT assets on the network, including those that are unauthorized, unmanaged, or hidden
Detect and remove any rogue or malicious devices that may pose a threat to the network security or performance
Update and verify the asset inventory data regularly and automatically, and alert on any changes or discrepancies
Support the asset lifecycle management and maintenance activities, such as patching, upgrading, or retiring assets5
References = IT Asset Valuation, Risk Assessment and Control Implementation Model, ITAM: The ultimate guide to IT asset management, Navigating Security Threats with IT Inventory Management, Network Scanning - Wikipedia, 8 Best IT Asset Management Software (2024)
A department has been granted an exception to bypass the existing approval process for purchase orders. The risk practitioner should verify the exception has been approved by which of the following?
Internal audit
Control owner
Senior management
Risk manager
A purchase order approval process is a set of procedures that companies use to authorize the purchase of goods or services from suppliers1. This process typically involves multiple levels of approvals, ensuring that purchases are compliant with company regulations and policies, and within budget limitations1. Sometimes, a department may be granted an exception to bypass the existing approval process for purchase orders, for example, due to urgency, emergency, or special circumstances2. However, such exceptions should not compromise the effectiveness and integrity of the purchase order approval process, and should be properly documented and justified2. Therefore, the risk practitioner should verify that the exception has been approved by senior management, as they are ultimately responsible for setting and overseeing the purchase order approval process, and for ensuring that the exceptions are reasonable and aligned with the company’s objectives and risk appetite3. Internal audit is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Internal audit’s role is to provide independent assurance and advice on the adequacy and effectiveness of thepurchase order approval process and its controls, and to report any issues or recommendations for improvement4. Control owner is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Control owner’s role is to design, implement, and operate the controls that support the purchase order approval process, and to monitor and report on the performance and compliance of the controls5. Risk manager is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Risk manager’s role is to identify, assess, and mitigate the risks associated with the purchase order approval process, and to communicate and report on the risk status and issues6. References = 1: A Step-by-Step Guide to a Purchase Order Approval Process2: Purchase Order Exceptions | Fordham3: Purchase Order (PO) Approval Process and Approval Workflow - ProcureDesk4: IT Risk Resources | ISACA5: CRISC Resources [updated 2021] | Infosec6: Riskand Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.
During a data loss incident, which role in the RACI chart would be aligned to the risk practitioner?
Responsible
Accountable
Informed
Consulted
Which of the following is the BEST indication of an effective risk management program?
Risk action plans are approved by senior management.
Residual risk is within the organizational risk appetite
Mitigating controls are designed and implemented.
Risk is recorded and tracked in the risk register
An effective risk management program is a systematic and consistent process of identifying, analyzing, evaluating, treating, monitoring, and communicating risks that may affect the achievement of the organization’s objectives12.
The best indication of an effective risk management program is that the residual risk, which is the risk remaining after risk treatment, is within the organizational risk appetite, which is the amount and type of risk that the organization is willing to accept in pursuit of its objectives12.
This indicates that the organization has successfully implemented appropriate risk responses that align with its risk strategy and criteria, and that the organization is able to balance the potential benefits and costs of taking risks12.
The other options are not the best indication, but rather components or outcomes of an effective risk management program. For example:
Risk action plans are approved by senior management is an outcome of an effective risk management program that demonstrates the commitment and accountability of the leadership for risk management12.
Mitigating controls are designed and implemented is a component of an effective risk management program that involves reducing the likelihood or impact of a risk event12.
Risk is recorded and tracked in the risk register is a component of an effective risk management program that involves documenting and updating the risk information and status12. References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
Which of the following should be the PRIMARY goal of developing information security metrics?
Raising security awareness
Enabling continuous improvement
Identifying security threats
Ensuring regulatory compliance
Information security metrics are quantitative or qualitative measures that indicate the performance and effectiveness of the information security processes, controls, and objectives. The primary goal of developing information security metrics is to enable continuous improvement of the information security program and to align it with the business goals and strategy. Information security metrics can help to identify the strengths and weaknesses of thesecurity program, to monitor and report on the progress and outcomes of the security initiatives, to evaluate the return on investment and value of the security activities, and to provide feedback and guidance for improvement actions. Information security metrics should be relevant, reliable, consistent, and actionable. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.2, p. 116-117
Which of the following BEST indicates whether security awareness training is effective?
User self-assessment
User behavior after training
Course evaluation
Quality of training materials
Security awareness training is a process of educating and informing the users about the security policies, procedures, and best practices of the organization, and the potential threats and risks that may affect the confidentiality, integrity, and availability of the information and systems.
The best indicator of whether security awareness training is effective is user behavior after training. This means that the users demonstrate and apply the knowledge and skills that they have learned from the training, such as following the security rules and guidelines, reporting any security incidents or issues, avoiding any risky or malicious actions, etc.
User behavior after training helps to measure the actual impact and outcome of the training, compare them with the expected or desired objectives and standards, identify any gaps or issuesthat may affect the training effectiveness or efficiency, and take appropriate actions to address them.
The other options are not the best indicators of whether security awareness training is effective. They are either subjective or not essential for security awareness training.
The references for this answer are:
Risk IT Framework, page 30
Information Technology & Security, page 24
Risk Scenarios Starter Pack, page 22
An organization has implemented a system capable of comprehensive employee monitoring. Which of the following should direct how the system is used?
Organizational strategy
Employee code of conduct
Industry best practices
Organizational policy
The best answer is D. Organizational policy. An organizational policy is a set of rules and guidelines that defines how the organization operates and conducts its activities. Anorganizational policy should direct how the employee monitoring system is used, because it can specify the purpose, scope, methods, and limitations of the monitoring, as well as the roles and responsibilities of the parties involved, the data protection and privacy measures, and the consequences of non-compliance. An organizational policy can also help to ensure that the employee monitoring system is aligned with the organization’s objectives, values, and culture, and that it complies with the relevant laws and regulations. The other options are not the best answer, although they may be related or influential to the organizational policy. Organizational strategy is a plan of action that outlines the organization’s vision, mission, goals, and initiatives, but it does not provide the details or the rules of how the employee monitoring system is used. Employee code of conduct is a document that describes the expected behavior and ethics of the employees, but it does not address the specific aspects or the procedures of the employee monitoring system. Industry best practices are the proven methods and standards that are adopted by the leading organizations in a specific field or sector, but they may not be applicable or suitable for every organization or situation. References = Workplace Monitoring Policy Template - CurrentWare, The All-In-One Guide to Employee Monitoring - G2
While evaluating control costs, management discovers that the annual cost exceeds the annual loss expectancy (ALE) of the risk. This indicates the:
control is ineffective and should be strengthened
risk is inefficiently controlled.
risk is efficiently controlled.
control is weak and should be removed.
Risk is inefficiently controlled when the annual cost of the control exceeds the annual loss expectancy (ALE) of the risk, as this means that the organization is spending more on the control than the potential loss that the control is supposed to prevent or reduce. This indicates that the control is not cost-effective or optimal, and that the organization should consider alternative or complementary controls that can lower the cost or increase the benefit of the risk management. Control is ineffective and should be strengthened when the control does not reduce the likelihood or impact of the risk to an acceptable level, regardless of the cost. Risk is efficiently controlled when the annual cost of the control is equal to or less than the annual loss expectancy (ALE) of the risk, as this means that the organization is spending less or equal on the control than the potential loss that the control is supposed to prevent or reduce. Control is weak and should be removed when the control does not provide any benefit or value to the risk management,regardless of the cost. References = CRISC Certified in Risk and Information Systems Control – Question205; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 205.
Which of the following statements in an organization ' s current risk profile report is cause for further action by senior management?
Key performance indicator (KPI) trend data is incomplete.
New key risk indicators (KRIs) have been established.
Key performance indicators (KPIs) are outside of targets.
Key risk indicators (KRIs) are lagging.
A risk profile report is a document that summarizes the current status and trends of the risks that an organization faces, as well as the actions taken or planned to manage them1. A risk profile report is a useful tool for senior management to monitor and oversee the organization’s risk management performance and to make informed decisions and adjustments as needed2. One of the key components ofa risk profile report is the key performance indicators (KPIs), which are metrics used to measure andevaluate the achievement of the organization’s objectives and strategies3. KPIs are aligned with the organization’s risk appetite and tolerance, and they have specific targets or benchmarks that indicate the desired level of performance4. Therefore, if the KPIs are outside of targets, it means that the organization is not meeting its objectives and strategies, and that there may be gaps or issues in the risk management process or the risk response actions. This is a cause for further action by senior management, as they need to investigate the root causes of the deviation, assess the impact and implications of the underperformance, and take corrective or preventive measures to improve the situation and bringthe KPIs back to the targets. Incomplete KPI trend data, new KRIs, and lagging KRIs are not the most critical statements in a risk profile report that require further action by senior management, as they do not directly indicate a failure or a problem in the risk management performance or the achievement of the objectives and strategies. Incomplete KPI trend data means that there is missing or insufficient information on the historical or projected changes in the KPIs over time. This may affect the accuracy and reliability of the risk profile report, but it does not necessarily mean that the KPIs are outside of targets or that the objectives and strategies are not met. Senior management may need to request or obtain the complete KPI trend data, but this is not as urgent or important as addressing the KPIs that are outside of targets. New KRIs means that there are additional or revised metrics used to measure and monitor the level of risk associated with a particular process, activity, or system within the organization. This may reflect the changes or updates in the risk environment, the risk appetite and tolerance, or the risk assessment methodology. However, new KRIs do not directly indicate a failure or a problem inthe risk management performance or the achievement of the objectives and strategies. Senior management may need to review and approve the new KRIs, but this is not as urgent or important as addressing the KPIs that are outside of targets. Lagging KRIs means that there are metrics that measure and monitor the level of risk after a risk event has occurred or a risk response has been implemented. This may provide useful feedback and lessons learned for the risk management process, but it does not directly indicate a failure or a problem in the risk management performance or the achievement of the objectives and strategies. Senior management may need to analyze and evaluate the lagging KRIs, but this is not as urgent or important as addressing the KPIs that are outside of targets. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.3: Risk Reporting, pp. 201-205.
Which of the following would be MOST effective in monitoring changes in an organization ' s IT risk environment?
Lagging indicators
Risk mitigation plans
Industry regulatory reports
Risk inventory
The risk inventory contains a current and historical record of identified risks and their statuses. Monitoring this inventory reveals emerging risks, shifts in severity, and whether mitigation is effective. It supports trend analysis and continuous improvement.
Which of the following risk activities is BEST facilitated by enterprise architecture (EA)?
Aligning business unit risk responses to organizational priorities
Determining attack likelihood per business unit
Adjusting business unit risk tolerances
Customizing incident response plans for each business unit
Which of the following is the PRIMARY purpose of analyzing control effectiveness during risk analysis?
To enable a control cost-benefit analysis
To evaluate the risk impact
To determine the likelihood of occurrence
To determine the current risk level
During risk analysis, CRISC distinguishes between inherent risk (without controls) and residual or current risk (with controls). Analyzingcontrol effectiveness—both in design and operation—is central to determining thecurrent risk level. Effective controls reduce either the likelihood of occurrence, the impact, or both. The assessment of their strength, coverage, and reliability allows the practitioner to adjust the initial inherent risk estimate down to a realistic residual risk figure and compare this to appetite and tolerance. Cost-benefit analysis of controls is a later step in risk response decision-making. Impact evaluation depends more on the nature of assets and processes than on controls. Likelihood is influenced by controls, but the primary purpose of control effectiveness analysis is to calculate the updated (residual) risk level, not just likelihood independently.
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
The organization has incorporated blockchain technology in its operations.
The organization has not reviewed its encryption standards.
The organization has implemented heuristics on its network firewall.
The organization has not adopted Infrastructure as a Service (laaS) for its operations.
An organization has outsourced its backup and recovery procedures to a third-party cloud provider. Which of the following is the risk practitioner s BEST course of action?
Accept the risk and document contingency plans for data disruption.
Remove the associated risk scenario from the risk register due to avoidance.
Mitigate the risk with compensating controls enforced by the third-party cloud provider.
Validate the transfer of risk and update the register to reflect the change.
The risk practitioner’s BEST course of action is to validate the transfer of risk and update the register to reflect the change, because outsourcing the backup and recovery procedures to a third-party cloud provider does not eliminate the risk, but rather transfers it to the service provider. The risk practitioner should verify that the service provider has adequate controls and capabilities to handle the backup and recovery procedures, and that the contractual agreement specifies the roles and responsibilities of both parties. The risk practitioner should also update the risk register to reflect the new risk owner and the residual risk level. The other options are not the best course of action, because:
Option A: Accepting the risk and documenting contingency plans for data disruption is not the best course of action, because it implies that the risk practitioner is still responsible for the risk, even though it has been transferred to the service provider. Contingency plans are also reactive measures, rather than proactive ones.
Option B: Removing the associated risk scenario from the risk register due to avoidance is not the best course of action, because it implies that the risk has been eliminated, which is not the case. The risk still exists, but it has been transferred to the service provider. The risk register should reflect the current risk status and ownership.
Option C: Mitigating the risk with compensating controls enforced by the third-party cloud provider is not the best course of action, because it implies that the risk practitioner is still involved in the risk management process, even though the risk has been transferred to the service provider. The risk practitioner should rely on the service provider’s controls and capabilities, andmonitor their performance and compliance. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 196.
A risk practitioner has been tasked with conducting a risk identification workshop with stakeholders to compile an IT risk profile. Which of the following would be MOST helpful in the brainstorming phase of this exercise?
List of issues and events from the risk register.
Internal audit reports with adverse findings.
IT control assessment results and trends.
Key risk indicators (KRIs) outside of appetite.
The BEST answer is A because a risk register is the direct repository of identified risk, issues, scenarios, impact, probability, mitigation action, and ownership. For a brainstorming workshop to compile an IT risk profile, previous issues and events from the risk register provide the most relevant starting point for identifying and discussing risk scenarios. The uploaded CRISC notes state that the risk register includes “risk scenario, date, description, impact, probability, risk score, mitigation action and owner,” and that preparation of a risk register begins in the risk identification process. They also state that the risk register is maintained as a repository of identified risk for decision-making.
ISACA’s CRISC outline places Risk Events , Risk Scenario Development and Evaluation , and Risk Register under Domain 2: Risk Assessment, supporting that this is a risk identification/risk assessment activity.
B, C, and D are useful inputs, but they are narrower. Audit findings and control assessment results focus mainly on control weaknesses, while KRIs outside appetite indicate monitored risk conditions. The risk register is broader and more directly aligned to brainstorming an IT risk profile.
===========
Which of the following is the PRIMARY risk management responsibility of the second line of defense?
Monitoring risk responses
Applying risk treatments
Providing assurance of control effectiveness
Implementing internal controls
The primary risk management responsibility of the second line of defense is to monitor the risk responses. The second line of defense is the function that oversees and supports the risk management activities of the first line of defense, which is the function that owns and manages the risks. The second line of defense includes the risk management, compliance, and quality assurance functions, among others. The second line of defense is responsible for monitoring the risk responses, which are the actions taken to address the risks, such as avoiding, transferring, mitigating, or accepting the risks. The second line of defense monitors the risk responses to ensure that they are implemented effectively and efficiently, that they achieve the desired outcomes, and that they are aligned with the risk appetite and tolerance of the organization. The second line of defense also provides guidance, advice, and feedback to the first line of defense on the risk responses, and reports the results and issues to the senior management and the board. Applying risk treatments, providing assurance of control effectiveness, and implementing internal controls are not the primary risk management responsibilities of the second line of defense, as they are either the responsibilities of the first line of defense or the third line ofdefense, which is the function that provides independent assurance of the risk management activities, such as the internal audit function. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 36.
Which of the following should be of GREATEST concern when reviewing the results of an independent control assessment to determine the effectiveness of a vendor ' s control environment?
The report was provided directly from the vendor.
The risk associated with multiple control gaps was accepted.
The control owners disagreed with the auditor ' s recommendations.
The controls had recurring noncompliance.
The most concerning issue when reviewing the results of an independent control assessment to determine the effectiveness of a vendor’s control environment is that the controls had recurring noncompliance. This indicates that the vendor’s controls are not operating as intended or designed, and that the vendor is not taking corrective actions to address the control deficiencies. This can increase the risk exposure and liability for the organization that outsources the service or function to the vendor. The report being provideddirectly from the vendor, the risk associated with multiple control gaps being accepted, and the control owners disagreeing with the auditor’s recommendations are other possible issues, but they are not as critical as the recurring noncompliance. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 11; CRISC Review Manual, 6th Edition, page 144.
Which of the following is the PRIMARY objective of establishing an organization ' s risk tolerance and appetite?
To align with board reporting requirements
To assist management in decision making
To create organization-wide risk awareness
To minimize risk mitigation efforts
Risk tolerance and appetite are the expressions of the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk tolerance is the acceptable level of variation that the organization is willing to allow for the outcome of its risk decisions. Riskappetite is the broad-based amount of risk that the organization is willing to accept in its activities. The primary objective of establishing an organization’s risk tolerance and appetite is to assist management in decision making, as they provide guidance and boundaries for the risk management activities and decisions. By establishing the risk tolerance and appetite, the organization can align its risk exposure with its strategic goals, optimize its risk-return trade-off, and enhance its risk culture and performance. References = CRISC Review Manual, 7th Edition, page 61.
Which of the following would be the GREATEST challenge when implementing a corporate risk framework for a global organization?
Privacy risk controls
Business continuity
Risk taxonomy
Management support
The greatest challenge when implementing a corporate risk framework for a global organization is the management support. A corporate risk framework is a set of principles, policies, standards, and processes that guide and govern the risk management activities across the organization. Acorporate risk framework helps to establish a consistent and integrated approach to risk management, and to align the risk management objectives and strategies with the business goals and values. Implementing a corporate risk framework for a global organization requires the management support, which is the commitment, involvement, and endorsement of the senior management and the board. Management support is essential for providing the vision, direction, and resources for the risk management initiatives, and for ensuring the accountability, responsibility, and ownership of the risk management roles and functions. Management support is also critical for creating and sustaining a risk-aware culture, and for promoting the risk management awareness and communication among the stakeholders. Management support can be challenging to obtain and maintain, especially for a global organization, as it may face various barriers, such as different expectations, priorities, preferences, or perspectives of the management, lack of trust or confidence in the risk management value or performance, resistance to change or innovation, or competing interests or agendas. Privacy risk controls, business continuity, and risk taxonomy are not as challenging as management support, as they are thecomponents or outcomes of the corporate risk framework, andthey can be addressed or improved by applying the appropriate methods, techniques, or tools. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 35.
Which of the following is a responsibility of the second line in the three lines model?
Alerting operational management to emerging issues
Implementing corrective actions to address deficiencies
Owning risk scenarios and bearing the consequences of loss
Performing duties independently to provide assurance
In the three lines model (formerly three lines of defense), thesecond lineprovides risk management, compliance oversight, and specialized support to the first line (operational management). One of its key responsibilities is monitoring the risk environment andalerting operational management to emerging issues—such as new regulatory requirements, changes in risk levels, and control weaknesses—while advising on appropriate responses. Implementing corrective actions is primarily the responsibility of the first line, which owns the processes. Owning risk scenarios and bearing loss consequences are first-line management responsibilities. Performing duties independently to provide assurance is the role of the third line (internal audit), which maintains organizational independence. Thus, the function of monitoring and advising, including escalation of emerging issues, aligns directly with the mandate of the second line.
Which of the following provides the BEST evidence of the effectiveness of an organization ' s account provisioning process?
User provisioning
Role-based access controls
Security log monitoring
Entitlement reviews
An organization’s account provisioning process is the process of creating, modifying, or deleting user accounts and access rights for the organization’s information systems and resources. It involves defining the access requirements, policies, and standards, and implementing and enforcing them across the organization.
The best evidence of the effectiveness of an organization’s account provisioning process is entitlement reviews, which are the periodic or regular reviews and validations of the user accounts and access rights that are granted or assigned to the users or entities that interact with the organization’s information systems and resources. Entitlement reviews can provide assurance and verification that the account provisioning process is accurate, consistent, and compliant, and that it meets the organization’s security and business objectives and requirements.
Entitlement reviews can be performed using various techniques, such as automated tools, reports, audits, surveys, etc. Entitlement reviews can also be integrated with the organization’s governance, risk management, and compliance functions, and aligned with the organization’s policies and standards.
The other options are not the best evidence of the effectiveness of an organization’s account provisioning process, because they do not provide the same level of assurance and verification that the account provisioning process is accurate, consistent, and compliant, and that it meets the organization’s security and business objectives and requirements.
User provisioning is the process of creating, modifying, or deleting user accounts and access rights for a specific user or entity, based on their identity, role, or function in the organization. User provisioning is an important part of the account provisioning process, but it is not the best evidence of the effectiveness of the account provisioning process, because it does not indicate whether the user accounts and access rights are appropriate and authorized, and whether they comply with the organization’s policies and standards.
Role-based access controls are the controls that grant or restrict user accounts and access rights based on the predefined roles or functions that the users or entities perform or assume in the organization. Role-based access controls are an important part of the account provisioningprocess, but they are not the best evidence of the effectiveness of the account provisioning process, because they do not indicate whether the roles or functions are defined and assigned correctly and consistently, and whether they comply with the organization’s policies and standards.
Security log monitoring is the process of collecting, analyzing, and reporting on the security events or activities that are recorded or logged by the organization’s information systems and resources. Security log monitoring is an important part of the account provisioning process, but it is not the best evidence of the effectiveness of the account provisioning process, because it does not indicate whether the security events or activities are legitimate or authorized, and whether they comply with the organization’s policies and standards. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 173
CRISC Practice Quiz and Exam Prep
A data processing center operates in a jurisdiction where new regulations have significantly increased penalties for data breaches. Which of the following elements of the risk register is MOST important to update to reflect this change?
Risk impact
Risk trend
Risk appetite
Risk likelihood
Risk impact is the potential loss or damage that a risk event can cause to an organization. Risk impact can be expressed in qualitative or quantitative terms, such as financial, reputational, operational, or legal. A risk register is a tool that records and tracks the key information about the identified risks, such as their description, likelihood, impact, response, and status. A risk register helps an organization to monitor and manage its risks effectively and efficiently. When there is a change in the external or internal environment that affects the organization’s risks, such as new regulations, the risk register should be updated to reflect this change. The most important element of the risk register to update in this case is the risk impact, because the new regulations have significantly increased the penalties for data breaches, which means that the potential loss or damage that a data breach can cause to the organization has also increased. By updating the risk impact, the organization can reassess the severity and priority of the data breach risk, and adjust its risk response accordingly. The other elements of the risk register are less important toupdate in this case. The risk trend shows the direction and rate of change of the risk over time, which may or may not be affected by the new regulations. The risk appetite is the amount and type of risk that the organization is willing to accept in pursuit of its objectives, which is unlikely to change due to the new regulations. The risk likelihood is the probability of a risk event occurring, which is also independent of the new regulations. References = Risk IT Framework, ISACA, 2022, p. 131
A bank has outsourced its statement printing function to an external service provider. Which of the following is the MOST critical requirement to include in the contract?
Monitoring of service costs
Provision of internal audit reports
Notification of sub-contracting arrangements
Confidentiality of customer data
The MOST critical requirement to include in the contract is the confidentiality of customer data, because it is a legal and ethical obligation of the bank to protect the privacy and security of its customers’ personal and financial information. Outsourcing the statement printing function to an external service provider exposes the customer data to potential unauthorized access, disclosure, or misuse by the service provider or its sub-contractors. Therefore, the contract should specify the terms and conditions for the handling, storage, and disposal of the customer data, as well as the penalties for any breach of confidentiality. The other options are not as critical as the confidentiality of customer data, because:
Option A: Monitoring of service costs is an important requirement to ensure that the service provider delivers the statement printing function within the agreed budget and scope, but it is not as critical as the confidentiality of customer data, which has legal and reputational implications for the bank.
Option B: Provision of internal audit reports is a useful requirement to verify that the service provider complies with the internal and external standards and regulations for the statement printing function, but it is not as critical as the confidentiality of customer data, which is a core value of the bank and its customers.
Option C: Notification of sub-contracting arrangements is a relevant requirement to ensure that the service provider does not delegate the statement printing function to another party without the bank’s consent and oversight, but it is not as critical as the confidentiality of customer data, which is the primary responsibility of the bank and its service provider. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 197.
Which of the following would be MOST helpful to a risk owner when making risk-aware decisions?
Risk exposure expressed in business terms
Recommendations for risk response options
Resource requirements for risk responses
List of business areas affected by the risk
Risk exposure is the potential loss or negative impact that may result from a risk. Expressing risk exposure in business terms means translating the technical or quantitative aspects of risk into meaningful and understandable information for the risk owner and other stakeholders. This canhelp the risk owner to make risk-aware decisions, as it can provide a clear and consistent basis for comparing and prioritizing risks, evaluating the cost-benefit of risk responses, and aligning the risk management strategy with the business objectives and value. The other options are not as helpful as risk exposure expressed in business terms, because they do not provide a comprehensive and relevant view of the risk, but rather focus on specific or partial aspects of the risk. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 45.
Which of the following is the GREATEST concern associated with the use of artificial intelligence (AI) language models?
The model could be hacked or exploited.
The model could be used to generate inaccurate content.
Staff could become overly reliant on the model.
It could lead to biased recommendations.
Biased recommendations from AI models can perpetuate or exacerbate organizational risks, especially in decision-making processes, regulatory compliance, and ethical standards. Addressing such concerns is vital under theEmerging Technology Risksdomain in risk management.
Several newly identified risk scenarios are being integrated into an organization ' s risk register. The MOST appropriate risk owner would be the individual who:
is in charge of information security.
is responsible for enterprise risk management (ERM)
can implement remediation action plans.
is accountable for loss if the risk materializes.
According to the CRISC Review Manual, a risk owner is the person who is accountable for the risk and its associated mitigation actions. The risk owner is responsible for monitoring the risk, reporting the risk status, and implementing the risk response. Therefore, the most appropriate risk owner would be the individual who is accountable for loss if the risk materializes, as it implies that they have the authority and the incentive to manage the risk effectively. The other options are not the most appropriate risk owners, as they are not directly accountable for the risk or its consequences. The person who is in charge of information security is responsible for overseeing the IT security function and ensuring that the IT security policy is enforced, but they may not have the authority or the resources to manage the risk. The person who is responsible for enterprise risk management (ERM) is responsible for establishing and maintaining the ERM framework and processes, but they may not have the knowledge or the involvement to manage the risk. The person who can implement remediation action plans is responsible for executing the risk response, but they may not have the decision-making power or the accountability to manage the risk. References = CRISC Review Manual, 7th Edition, Chapter 3, Section 3.1.2, page 108.
Which of the following is MOST important to have in place to ensure the effectiveness of risk and security metrics reporting?
Organizational reporting process
Incident reporting procedures
Regularly scheduled audits
Incident management policy
The most important factor to have in place to ensure the effectiveness of risk and security metrics reporting is an organizational reporting process. An organizational reporting process is a set of procedures that defines the roles, responsibilities, frequency, format, and distribution of the risk and security metrics reports. An organizational reporting process helps to ensure that the risk and security metrics are relevant, accurate, consistent, and timely, and that they provide useful information for decision making and performance improvement. An organizational reporting process also helps to align the risk and security metrics reporting with the enterprise’s objectives, strategies, and policies, and to communicate the risk and security status and issues to the appropriate stakeholders. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.3.2, page 2421
Which of the following is the PRIMARY objective of engaging key stakeholders in the IT risk assessment process?
Reducing the time required for risk analysis
Increasing the quality of analysis
Building a risk aware culture
Ensuring proper budget allocation for risk remediation
The correct answer isBbecause engaging key stakeholders in the IT risk assessment process primarily improves thequality of analysis. Stakeholders provide business context, operational knowledge, and understanding of risk impacts, dependencies, and priorities. This leads to more accurate and relevant risk assessment results.
The other options are less appropriate:
A. Reducing the time required for risk analysisis not the primary objective.
C. Building a risk aware cultureis a valuable secondary benefit, but not the main reason for engagement in the assessment process.
D. Ensuring proper budget allocation for risk remediationmay result later, but not the primary objective of stakeholder involvement.
Exact Extracts supporting the answer:
“To ensure the overall effectiveness of a risk management program it is essential to have the participation of relevant stakeholders.”
“An interdisciplinary team within the enterprise offers the best perspective on risk management to employees and stakeholders.”
“The BEST approach when developing risk scenarios for an enterprise is to use both the top-down and the bottom-up approach because they have different perspectives.”
“The PRIMARY result of a risk assessment process is input for risk-aware decisions.”
These extracts show that stakeholder engagement is primarily valuable because it improves the completeness, relevance, and quality of risk analysis.
===========
Which of the following is the PRIMARY benefit of using a risk map with stakeholders?
Consolidates risk response options by severity
Aligns risk appetite with business objectives
Correlates risk scenarios to risk appetite
Defines an organizational risk taxonomy
Arisk maphelps stakeholders understand how risk scenarios align with the organization’srisk appetite. This visualization facilitates informed decision-making and ensures risk responses are consistent with organizational priorities.
===========
Which of the following is MOST helpful to understand the consequences of an IT risk event?
Fault tree analysis
Historical trend analysis
Root cause analysis
Business impact analysis (BIA)
Business impact analysis (BIA) is a process that involves analyzing the potential consequences of an IT risk event on the organization’s critical business functions and processes. BIA can help to understand the severity and duration of the disruption, the financial and operational losses, the recovery time objectives, and the recovery point objectives. BIA can also help to prioritize the recovery activities and resources, as well as to determine the acceptable level of risk and the risk mitigation strategies. BIA is the most helpful tool to understand the consequences of an IT risk event, as it provides a comprehensive and quantitative assessment of the impact and the recovery requirements. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.2, p. 206-207
Which of the following should be management ' s PRIMARY consideration when approving risk response action plans?
Ability of the action plans to address multiple risk scenarios
Ease of implementing the risk treatment solution
Changes in residual risk after implementing the plans
Prioritization for implementing the action plans
The management’s primary consideration when approving risk response action plans should be the changes in residual risk after implementing the plans. Residual risk is the level of risk that remains after the implementation of risk responses1. It indicates the degree of exposure or uncertainty that the organization still faces, and the potential impact or consequences of the risk events. The management should evaluate the effectiveness and adequacy of the risk responses, and decide whether the residual risk is acceptable or not2. The management should also compare the residual risk with the risk appetite, which is the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives3. The management should ensure that the residual risk is aligned with the risk appetite, and that the risk responses are consistent and proportional to the risk level4.
The other options are not the primary consideration when approving risk response action plans, because:
Ability of the action plans to address multiple risk scenarios is a desirable but not essential criterion for approving risk response action plans. Risk scenarios are hypothetical situations that describe how a risk event could occur and what the consequences could be5. They can help to understand and communicate the nature and impact of the risks, and to design and evaluate the risk responses6. However, not all risk scenarios are equally likely or relevant, and some risk scenarios may be too complex or improbable to address. Therefore, the ability of the action plansto address multiple risk scenarios is not the primary consideration, but rather a secondary or supplementary one.
Ease of implementing the risk treatment solution is a practical but not critical criterion for approving risk response action plans. Risk treatment is the process of selecting and applying appropriate measures to modify the risk7. It can involve different strategies, such as avoid, reduce, transfer, or accept the risk8. The ease of implementing the risk treatment solution depends on various factors, such as the availability of resources, the feasibility of the solution, or the cooperation of the stakeholders. However, the ease of implementation is not the primary consideration, but rather a supporting or facilitating one.
Prioritization for implementing the action plans is a useful but not vital criterion for approving risk response action plans. Prioritization is the process of ranking the action plans according to their importance, urgency, or impact. It can help to allocate the resources, schedule the activities, and monitor the progress of the action plans. However, prioritization is not the primary consideration, but rather a subsequent or follow-up one.
References =
Residual Risk - CIO Wiki
What is Residual Risk? - Definition from Techopedia
Risk Appetite - CIO Wiki
Risk Appetite: What It Is and Why It Matters - Gartner
Risk Scenarios Toolkit - ISACA
Risk Scenarios Starter Pack - ISACA
Risk Treatment - CIO Wiki
Risk Treatment Plan - CIO Wiki
[Prioritization - CIO Wiki]
Which of the following is the GREATEST benefit when enterprise risk management (ERM) provides oversight of IT risk management?
Aligning IT with short-term and long-term goals of the organization
Ensuring the IT budget and resources focus on risk management
Ensuring senior management ' s primary focus is on the impact of identified risk
Prioritizing internal departments that provide service to customers
Enterprise risk management (ERM) is a holistic and strategic approach to managing the risks that an organization faces across its various functions, processes, and activities. ERM aims to align the organization’s risk appetite and tolerance with its objectives and vision, and to optimize the value and performance of the organization1.
IT risk management is a subset of ERM that focuses on identifying, assessing, and mitigating the risks related to the use of information technology (IT) in the organization. IT risk management aims to ensure the confidentiality, integrity, and availability of IT resources and information, and to support the IT governance and strategy of the organization2.
The greatest benefit when ERM provides oversight of IT risk management is aligning IT with short-term and long-term goals of the organization, because it can help to:
Integrate IT risk management with the overall business strategy and risk management, and ensure that IT risks are considered and addressed at the enterprise level
Align IT risk appetite and tolerance with the business risk appetite and tolerance, and ensure that IT risks are balanced with the expected benefits and opportunities
Enhance IT risk awareness and communication among the stakeholders, and ensure that IT risks are reported and escalated appropriately
Optimize IT risk response and control, and ensure that IT risks are managed efficiently and effectively
Demonstrate IT risk value and impact, and ensure that IT risks are measured and monitored against the business objectives and performance34
The other options are not the greatest benefit when ERM provides oversight of IT risk management, but rather some of the outcomes or consequences of it. Ensuring the IT budget and resources focus on risk management is a benefit that can help to allocate and prioritize the IT resources and funds according to the IT risk level and the business needs. Ensuring senior management’s primary focus is on the impact of identified risk is a benefit that can help to increase the senior management’s involvement and accountability in IT risk management, and to support the IT risk decision making and reporting. Prioritizing internal departments that provide service to customers is a benefit that can help to improve the quality and efficiency of the IT service delivery and customer satisfaction. References =
Enterprise Risk Management - ISACA
IT Risk Management - ISACA
Aligning IT risks with Enterprise Risk Management (ERM)
Five Benefits of Enterprise Risk Management : Articles : Resources …
[CRISC Review Manual, 7th Edition]
During a risk assessment of a financial institution, a risk practitioner discovers that tellers can initiate and approve transactions of significant value. This team is also responsible for ensuring transactions are recorded and balances are reconciled by the end of the day. Which of the following is the risk practitioner ' s BEST recommendation to mitigate the associated risk?
Implement continuous monitoring.
Require a second level of approval.
Implement separation of duties.
Require a code of ethics.
To help identify high-risk situations, an organization should:
continuously monitor the environment.
develop key performance indicators (KPIs).
maintain a risk matrix.
maintain a risk register.
To help identify high-risk situations, an organization should continuously monitor the environment, as it can help to detect and respond to any changes or emerging risks that may affect the organization’s objectives and strategy. Continuous monitoring can also provide timely and relevant feedback and information to the decision-makers and stakeholders, and enable them to adjust the risk strategy and response actions accordingly. Continuous monitoring can also help to ensure that the risk management process is aligned with the organization’s risk appetite andtolerance, and supports the achievement of the organization’s goals and value creation. References = ISACA Certified in Risk and Information Systems Control (CRISC)Certification Exam Question and Answers, Question 243. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 243. CRISC Sample Questions 2024, Question 243.
Which of the following is MOST important information to review when developing plans for using emerging technologies?
Existing IT environment
IT strategic plan
Risk register
Organizational strategic plan
The most important information to review when developing plans for using emerging technologies is the organizational strategic plan. The organizational strategic plan is a document that defines the vision, mission, goals, and objectives of the organization. It also outlines the strategies, actions, and resources that are needed to achieve them. The organizational strategic plan provides the direction, alignment, and guidance for the use of emerging technologies, and ensures that they are aligned with and support the organizational needs and priorities. The other options are not as important as the organizational strategic plan, as they are related to the current state, specific area, or potential issues of the use of emerging technologies, not the overall purpose and value of the use of emerging technologies. References = Risk and InformationSystems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.2: IT Risk Identification Methods, page 19.
The PRIMARY benefit of conducting continuous monitoring of access controls is the ability to identify:
inconsistencies between security policies and procedures
possible noncompliant activities that lead to data disclosure
leading or lagging key risk indicators (KRIs)
unknown threats to undermine existing access controls
The primary benefit of conducting continuous monitoring of access controls is the ability to identify possible noncompliant activities that lead to data disclosure. Continuous monitoring of access controls is a process that involves collecting, analyzing, and reporting on the performance and effectiveness of the access controls on a regular basis. Continuous monitoring of access controls helps to detect and prevent any unauthorized or inappropriate access to information assets, and to ensure that the access controls arealigned with the enterprise’s security policies and standards. Continuous monitoring of access controls also helps to identify possible noncompliant activities that lead to data disclosure, such as data leakage, data theft, data tampering, or data breach. By identifying these activities, the enterprise can take timely and appropriate actions to mitigate the risk and protect the confidentiality, integrity, and availability of the information assets. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.3.2, page 1411
A review of an organization s controls has determined its data loss prevention {DLP) system is currently failing to detect outgoing emails containing credit card data. Which of the following would be MOST impacted?
Key risk indicators (KRls)
Inherent risk
Residual risk
Risk appetite
Residual risk is the risk that remains after applying controls to mitigate the inherent risk. Inherent risk is the risk that exists before considering the controls. Key risk indicators (KRIs) are metricsthat measure the level and impact of risks. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. The failure of the data loss prevention (DLP) system to detect outgoing emails containing credit card data would most impact the residual risk, because it would increase the likelihood and impact of data leakage, data loss, and data exfiltration incidents. These incidents could cause financial, reputational, legal, and regulatory damages to the organization. The failure of the DLP system would also affect the KRIs, as they would show a higher level of risk exposure and a lower level of control effectiveness. However, the KRIs are not the risk itself, but rather the indicators of the risk. The failure of the DLP system would not directly impact the inherent risk or the risk appetite, as they are independent of the controls. The inherent risk would remain the same, as it is based on the nature and value of the data and the threats and vulnerabilities that exist. The risk appetite would also remain the same, as it is based on the organization’s culture, strategy, and stakeholder expectations. Therefore, the most impacted factor would be the residual risk, as it reflects the actual risk level that the organization faces after applying the controls. References = Risk IT Framework, ISACA, 2022, p. 131
Which of the following is the PRIMARY role of the first line of defense with respect to information security policies?
Draft the information security policy.
Approve the information security policy.
Audit the implementation of the information security policy.
Implement controls in response to the policy requirements.
An organization has decided to implement a new Internet of Things (loT) solution. Which of the following should be done FIRST when addressing security concerns associated with this new technology?
Develop new loT risk scenarios.
Implement loT device monitoring software.
Introduce controls to the new threat environment.
Engage external security reviews.
The first thing that should be done when addressing security concerns associated with a new Internet of Things (IoT) solution is to develop new IoT risk scenarios. IoT is a network of physical devices, such as sensors, cameras, appliances, etc., that are connected to the internet and can collect, process, and exchange data. IoT introduces new security concerns, such as privacy, confidentiality, integrity, availability,and accountability of the data and devices, as well as new threats and vulnerabilities, such as unauthorized access, manipulation, or disruption of the data and devices. Developing new IoT risk scenarios is the first thing that should be done, because it helps to identify, analyze, and evaluate the potential risks that could affect the IoT solution’s objectives or operations. Developing new IoT risk scenarios also helps to select the most appropriate and effective controls to minimize the risks, such as avoiding, reducing, transferring, or accepting the risks. The other options are not the first thing that should be done, although theymay be part of or derived from the IoT risk scenarios. Implementing IoT device monitoring software, introducing controls to the new threat environment, and engaging external security reviews are all activities that can help to support or improve the security of the IoT solution, but they do not necessarily identify, analyze, or evaluate the risks that could affect the IoT solution. References = 1
Effective risk communication BEST benefits an organization by:
helping personnel make better-informed decisions
assisting the development of a risk register.
improving the effectiveness of IT controls.
increasing participation in the risk assessment process.
Effective risk communication best benefits an organization by helping personnel make better-informed decisions. Risk communication is the process of exchanging information and opinions among stakeholders about the nature, magnitude, significance, or control of a risk. By communicating risk information clearly and consistently, the organization can enhance the understanding and awareness of the risk, and enable the personnel to make decisions that are aligned with the risk appetite and objectives of the organization. Assisting the development of a risk register, improving the effectiveness of IT controls, and increasing participation in the risk assessment process are other possible benefits, but they are not as important as helping personnel make better-informed decisions. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 12; CRISC Review Manual, 6th Edition, page 215.
Which of the following is the BEST indicator of the effectiveness of a control action plan ' s implementation?
Increased number of controls
Reduced risk level
Increased risk appetite
Stakeholder commitment
The effectiveness of a control action plan’s implementation can be measured by the extent to which it achieves the desired risk reduction. A control action plan is a set of actions that are designed to address the root causes of a risk and mitigate its impact or likelihood. The best indicator of the effectiveness of a control action plan’s implementation is the reduced risk level, which means that the risk is either eliminated or brought within the acceptable range. The otheroptions are not the best indicators, because they do not directly reflect the risk reduction. Increased number of controls may not necessarily reduce the risk level, especially if the controls are not aligned with the risk causes, objectives, and priorities. Increased risk appetite may indicate a higher tolerance for risk, but it does not mean that the risk level has been reduced. Stakeholder commitment may facilitate the implementation of the control action plan, but it does not guarantee the effectiveness of the plan. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3: Risk Response, Section 3.2: Control Action Plan, p. 170-171.
To implement the MOST effective monitoring of key risk indicators (KRIs), which of the following needs to be in place?
Threshold definition
Escalation procedures
Automated data feed
Controls monitoring
Key risk indicators (KRIs) are the metrics or measures that provide information and insight on the level and trend of the risks that may affect the organization’s objectives and operations. KRIscan help the organization to monitor and communicate the risks, and to support the decision making and planning for the risk management.
To implement the most effective monitoring of KRIs, one of the essential elements that needs to be in place is threshold definition, which is the process of establishing and specifying the acceptable or tolerable ranges or limits for the KRIs, based on the organization’s risk appetite and tolerance. Threshold definition can help the organization to monitor KRIs by providing the following benefits:
It can enable the comparison and evaluation of the actual or current values of the KRIs with the expected or desired values of the KRIs, and to identify and quantify the deviations or variations that may indicate the changes or developments in the risk level or performance.
It can trigger the alerts or notifications when the values of the KRIs exceed or fall below the thresholds, and to initiate the appropriate actions or responses to address or correct the risks and their impacts.
It can provide useful references and benchmarks for the alignment and integration of the KRIs with the organization’s risk management function, and for the compliance with the organization’s risk policies and standards.
The other options are not the essential elements that need to be in place to implement the most effective monitoring of KRIs, because they do not address the main purpose and benefit of threshold definition, which is to establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Escalation procedures are the processes and guidelines for communicating and sharing the information and status of the risks and their responses among the relevant stakeholders, and for escalating or transferring the risks and their responses to the appropriate levels orparties when necessary or required. Escalation procedures can help the organization to monitor KRIs by ensuring the awareness and involvement of the stakeholders, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Automated data feed is the process of using a software tool or system to collect and transmit the data or information that are related or relevant to the KRIs, and to ensure the accuracy, reliability, and timeliness of the data or information. Automated data feed can help the organization to monitor KRIs by providing the data or information that are necessary and relevant for the KRIs, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Controls monitoring is the process of verifying and validating the adequacy and effectiveness of the controls that are intended to ensure the confidentiality, integrity, availability, and reliabilityof the information systems and resources that are affected by the risks. Controls monitoring can help the organization to monitor KRIs by providing the assurance and evidence on the performance and compliance of the controls, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 206
CRISC Practice Quiz and Exam Prep
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
Creating metrics to track remote connections
Updating the organizational policy for remote access
Updating remote desktop software
Implementing multi-factor authentication
Automated asset management software is the best method to track asset inventory, as it can provide accurate, timely, and comprehensive information about the organization’s IT assets, such as their location, status, configuration, ownership, and value. Automated asset management software can also help to optimize the utilization, performance, and lifecycle of the IT assets, and to reduce the risks of loss, theft, damage, or obsolescence. Automated asset management software can integrate with other systems, such as configuration management database (CMDB), service desk, and security tools, to enable better visibility, control, and governance of the IT assets.
An organization has experienced a cyber-attack that exposed customer personally identifiable information (Pll) and caused extended outages of network services. Which of the following stakeholders are MOST important to include in the cyber response team to determine response actions?
Security control owners based on control failures
Cyber risk remediation plan owners
Risk owners based on risk impact
Enterprise risk management (ERM) team
Risk owners based on risk impact are the most important stakeholders to include in the cyber response team, as they are responsible for the business outcomes affected by the cyber attack and can decide on the appropriate response actions. The other options are not the most important stakeholders to include in the cyber response team, although they may be involved in the process.
Which of the following BEST protects an organization against breaches when using a software as a service (SaaS) application?
Control self-assessment (CSA)
Security information and event management (SIEM) solutions
Data privacy impact assessment (DPIA)
Data loss prevention (DLP) tools
Software as a service (SaaS) is a cloud computing model that provides software applications over the internet, without requiring the customer to install or maintain them on their own devices1. SaaS applicationscan offer many benefits, such as scalability, accessibility, and cost-efficiency, but they also pose security risks, such as data breaches, unauthorized access, and compliance violations2.
One of the best ways to protect an organization against breaches when using a SaaS application is to use data loss prevention (DLP) tools. DLP tools are software solutions that monitor, detect,and prevent the unauthorized transmission or leakage of sensitive data from an organization’s network or devices3. DLP tools can help an organization to:
Identify and classify sensitive data, such as personal information, intellectual property, or financial records, and apply appropriate policies and controls to protect them
Encrypt data in transit and at rest, and use secure protocols and encryption keys to ensure data confidentiality and integrity
Block or alert on suspicious or malicious data transfers, such as unauthorized uploads, downloads, or sharing of data to external sources or devices
Audit and report on data activities and incidents, and provide evidence for compliance with data protection regulations and standards, such as GDPR, HIPAA, or PCI-DSS4
References = What is SaaS?, Top 7 SaaS Security Risks (and How to Fix Them), What is Data Loss Prevention (DLP)?, Data Loss Prevention (DLP) for SaaS Applications
When reviewing the business continuity plan (BCP) of an online sales order system, a risk practitioner notices that the recovery time objective (RTO) has a shorter lime than what is defined in the disaster recovery plan (DRP). Which of the following is the BEST way for the risk practitioner to address this concern?
Adopt the RTO defined in the BCR
Update the risk register to reflect the discrepancy.
Adopt the RTO defined in the DRP.
Communicate the discrepancy to the DR manager for follow-up.
A recovery time objective (RTO) is the maximum acceptable time that a business process or function can be disrupted or unavailable before it causes significant damage or loss to the organization. A business continuity plan (BCP) is a document that describes how the organization will resume its critical business operations in the event of a disaster or disruption. A disaster recovery plan (DRP) is a document that describes how the organization will restore its IT systems and infrastructure in the event of a disaster or disruption. The RTO defined in the BCP and the DRP should be consistent and aligned, as they both support the continuity and recovery of the business. If the RTO defined in the BCP is shorter than the RTO defined in the DRP, it means that the BCP expects the business process or function to be restored faster than the DRP can provide. This can create a gap or a conflict between the BCP and the DRP, and can compromise the effectiveness and efficiency of the continuity and recovery efforts. Therefore, the best way for the risk practitioner to address this concern is to communicate the discrepancy to the DR manager for follow-up, meaning that the risk practitioner should report the issue and its implications to the DR manager, who is responsible for developing and maintaining the DRP. The DR manager should review the discrepancy and determine whether it is justified or not, and whether it requires any adjustment or alignment of the RTOs in the BCP and the DRP. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.2, p. 206-207
Which of the following is the MOST effective way to reduce potential losses due to ongoing expense fraud?
Implement user access controls
Perform regular internal audits
Develop and communicate fraud prevention policies
Conduct fraud prevention awareness training.
Developing and communicating fraud prevention policies is the most effective way to reduce potential losses due to ongoing expense fraud because it creates a culture of integrity and accountability, sets clear expectations and consequences for employees, and deters fraudulent behavior. Implementing user access controls, performing regular internal audits, and conducting fraud prevention awareness training are also important controls, but they are more reactive and detective than preventive. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 4-26.
Which of the following is the BEST approach to mitigate the risk associated with outsourcing network management to an external vendor who will have access to sensitive information assets?
Prepare a skills matrix to illustrate tasks and required expertise.
Require periodic security assessments of the vendor within the contract.
Perform due diligence to enable holistic assessment of the vendor.
Plan a phased approach for the transition of processes to the vendor.
Performing due diligence is the most effective initial step in mitigating risks associated with outsourcing. This comprehensive assessment evaluates the vendor ' s capabilities, security posture, compliance with regulations, and overall suitability for handling sensitive information assets. It ensures that potential risks are identified and addressed before entering into a contractual agreement.
Which of the following is a PRIMARY benefit of creating an organizational code of conduct?
Clear expectations for employee behavior
Identification of ethical risk facing the organization
Improvement in workforce productivity
Enhanced integrity of management
The correct answer isAbecause the primary benefit of an organizationalcode of conductis to establishclear expectations for employee behavior. A code of conduct communicates the standards of ethical and professional behavior expected within the organization and provides a common basis for decision-making, accountability, and awareness.
The other options are less appropriate:
B. Identification of ethical risk facing the organizationmay result indirectly, but this is not the primary purpose of a code of conduct.
C. Improvement in workforce productivitycould occur as a secondary effect, but it is not the main benefit.
D. Enhanced integrity of managementmay be supported, but the code of conduct applies across the organization and primarily clarifies expected behavior.
Exact Extracts supporting the answer:
“The most effective way to support adherence to an enterprise ' s code of ethics is by ensuring periodic training evaluation and attestation of employees.”
“The most significant benefit when stakeholders promote and follow professional ethics is that it increases risk management effectiveness within an enterprise.”
“The best proactive approach for practicing professional ethics within an enterprise is to provide ethics awareness training.”
“Developing and practicing ethical behavior within an enterprise contributes the most to building the risk culture.”
These extracts support that ethics-related governance mechanisms such as a code of conduct are intended to guide and reinforce expected behavior throughout the enterprise. Therefore, the primary benefit isclear expectations for employee behavior.
===========
A data privacy regulation has been revised to incorporate more stringent requirements for personal data protection. Which of the following provides the MOST important input to help ensure compliance with the revised regulation?
Gap analysis
Current control attestation
Risk profile update
Business impact analysis (BIA)
Gap analysisidentifies differences between existing controls and the new regulatory requirements.
CRISC guidance explains:
“When a regulatory or compliance requirement changes, the first step is to conduct a gap analysis comparing current controls to the new requirements.”
This allows the practitioner to identify areas requiring remediation or policy enhancement.
Hence,A. Gap analysisis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Compliance and Regulatory Alignment.
Conduct targeted risk assessments.
Recommend management accept the low risk scenarios.
Assess management ' s risk tolerance.
Propose mitigating controls.
Even if the residual risks are low, an ineffective key control warrants proposing additional mitigating controls to strengthen risk management. Accepting the risks without controls may expose the enterprise to unnecessary vulnerabilities. Targeted assessments may follow but addressing control weaknesses is the immediate priority. Risk tolerance is relevant but secondary in this context.
Which of the following contributes MOST to the effective implementation of risk responses?
Clear understanding of the risk
Comparable industry risk trends
Appropriate resources
Detailed standards and procedures
Appropriate resources contribute most to the effective implementation of risk responses. Resources include people, time, money, equipment, and materials that are needed to execute the risk responses. Without appropriate resources, the risk responses may not be implemented properly, timely, or efficiently, and may not achieve the desired outcomes. The other options are not as important as appropriate resources, as they are related to the understanding, comparison, or documentation of the risk responses, which are less critical than the execution of the riskresponses. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
In addition to the risk exposure, which of the following is MOST important for senior management to understand prior to approving the use of artificial intelligence (Al) solutions?
Potential benefits from use of Al solutions
Monitoring techniques required for AI solutions
Changes to existing infrastructure to support Al solutions
Skills required to support Al solutions
A risk practitioner is defining metrics for security threats that were not identified by antivirus software. Which type of metric is being developed?
Key control indicator (KCI)
Key risk indicator (KRI)
Operational level agreement (OLA)
Service level agreement (SLA)
A KRI is a measure used by an organization to measure the health of a particular risk. In this case, the risk practitioner is developing a metric to measure the risk associated with security threats that were not identified by antivirus software12.
References
1Standardized Scoring for Security and Risk Metrics - ISACA
2Key Performance Indicators for Security Governance, Part 1 - ISACA
Which of the following is the BEST method for identifying vulnerabilities?
Batch job failure monitoring
Periodic network scanning
Annual penetration testing
Risk assessments
The best method for identifying vulnerabilities is periodic network scanning. Network scanning is a process of scanning and probing the network devices, systems, and applications to discover and analyze their security weaknesses, such as configuration errors, outdated software, or open ports. Network scanning can help to identify the vulnerabilities that could be exploited by attackers to gain unauthorized access, compromise data, or disrupt services. Periodic network scanning is the best method, because it can provide a regular and comprehensive view of the network security posture, and it can detect and address the new or emerging vulnerabilities in a timely manner. Periodic network scanning can also help to comply with the legal and regulatory requirements and standards for network security, such as the ISO/IEC 27001, the NIST SP 800-53, or the PCI DSS123. The other options are not the best method, although they may be useful or complementary to periodic network scanning. Batch job failure monitoring is a process of monitoring and reporting the failures or errors that occur during the execution of batch jobs, such as data processing, backup, or synchronization. Batch job failure monitoring can help to identify the operational or technical issues that affect the performance or availability of the network services, but it does not directly identify the security vulnerabilities or the potential threats. Annual penetration testing is a process of simulating a real-world attack on the network devices, systems, and applications to evaluate their security defenses and resilience. Penetration testing can help to identify and exploit the vulnerabilities that could be used by attackers to compromise the network security, and to provide recommendations for improvement. However, annual penetration testing is not the best method, because it is not frequent or consistent enough to keep up with the changing and evolving network security landscape, and it may not cover all thenetwork components or scenarios. Risk assessments are a process of identifying, analyzing, and evaluating the risks associated with the network devices, systems, and applications. Risk assessments can help to estimate the probability and impact of the vulnerabilities and the threats, and to prioritize and respond to the risks accordingly. However, risk assessments are not the same as or a substitute for vulnerability identification, as they rely on the vulnerability information as an input, rather than an output. References = Vulnerability Testing: Methods, Tools, and 10 Best Practices, ISO/IEC 27001 Information Security Management, NIST SP 800-53 Rev. 5
In a public company, which group is PRIMARILY accountable for ensuring sufficient attention and resources are applied to the risk management process?
Board of directors
Risk officers
Line management
Senior management
Which of the following is the MOST important objective of regularly presenting the project risk register to the project steering committee?
To allocate budget for resolution of risk issues
To determine if new risk scenarios have been identified
To ensure the project timeline is on target
To track the status of risk mitigation actions
Project risk register: A document that records the identified risks, their likelihood, impact, and mitigation strategies for a project1.
Project steering committee: A group of senior stakeholders and experts who oversee and support a project from a higher level2.
Risk mitigation actions: The measures taken to prevent, reduce, or transfer the risks that may affect a project3.
The most important objective of regularly presenting the project risk register to the project steering committee is to track the status of risk mitigation actions. Tracking the status of risk mitigation actions can help the project steering committee to:
Monitor and measure the performance and effectiveness of the risk management process and controls
Evaluate the progress and outcomes of the risk mitigation actions against the project goals and objectives
Identify and resolve any issues, challenges, or gaps in the risk mitigation actions
Provide guidance, feedback, and support to the project manager and the project team
Adjust or revise the risk mitigation actions as needed to reflect the changes in the project scope, schedule, budget, or environment
The other options are not the most important objective of regularly presenting the project risk register to the project steering committee, although they may be relevant or beneficial. Allocating budget for resolution of risk issues, which means assigning financial resources to address and resolve the risks that may affect a project, may be a part of the risk management process, but it is not the primary purpose of presenting the project risk register, which is more focused on tracking and reporting the risk status and actions. Determining if new risk scenarios have been identified, which means finding out if there are any additional or emerging risks that may impact a project, may be a useful outcome of presenting the project risk register, but it is not the main objective, which is more concerned with tracking and reporting the existing risk status and actions. Ensuring the project timeline is on target, which means verifying that the project is progressing according to the planned schedule and milestones, may be a benefit of presenting the project risk register, but it is not the key objective, which is more related to tracking and reporting the risk status and actions.
References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana, Project Steering Committee: Roles, Best Practices, Challenges, Risk Mitigation: Definition, Strategies, and Examples
An organization learns of a new ransomware attack affecting organizations worldwide. Which of the following should be done FIRST to reduce the likelihood of infection from the attack?
Identify systems that are vulnerable to being exploited by the attack.
Confirm with the antivirus solution vendor whether the next update will detect the attack.
Verify the data backup process and confirm which backups are the most recent ones available.
Obtain approval for funding to purchase a cyber insurance plan.
The first step to reduce the likelihood of infection from the attack is to identify systems that are vulnerable to being exploited by the attack. This would help the organization to assess the scope and severity of the risk, and to prioritize the systems that need immediate protection. Identifying systems that are vulnerable to being exploited by the attack would also help the organization to apply the appropriate patches, updates, or configurations to prevent or mitigate the attack, and to isolate or disconnect the systems that are already infected or compromised. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.2, page 60123
Which of the following is the MOST important consideration when communicating the risk associated with technology end-of-life to business owners?
Cost and benefit
Security and availability
Maintainability and reliability
Performance and productivity
The most important consideration when communicating the risk associated with technology end-of-life to business owners is the cost and benefit of the risk response options. Technology end-of- life is the situation when a technology product or service is no longer supported by the vendor or manufacturer, and may pose security, compatibility, or performance issues. The risk practitioner should communicate the cost and benefit of the possible risk responses, such as replacing, upgrading, or maintaining the technology, to the business owners, and help them to make informed and rational decisions. Security and availability, maintainability and reliability, and performance and productivity are other possible considerations, but they are not as important as the cost and benefit. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
Who is BEST suited to provide objective input when updating residual risk to reflect the results of control effectiveness?
Control owner
Risk owner
Internal auditor
Compliance manager
The internal auditor is the best suited to provide objective input when updating residual risk to reflect the results of control effectiveness. The internal auditor is an independent and impartial function that evaluates the adequacy and effectiveness of the internal controls and reports on the findings and recommendations. The internal auditor can provide an unbiased and reliable assessment of the residual risk, which is the risk that remains after the controls are applied. The other options are not as objective as the internal auditor, as they may have vested interests orconflicts of interest in the control environment. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Response, page 87.
Which of the following is the MOST important consideration when establishing a recovery point objective (RPO)?
Latency of the alternate site
Amount of acceptable data loss
Time and resources for offsite backups
Cost of testing the business continuity plan (BCP)
RPOdefines themaximum tolerable data lossin case of a disruption — i.e., how much data the enterprise can afford to lose between the last backup and an incident.
ISACA’s business continuity and CRISC guidance:
“The recovery point objective (RPO) is based on the amount of acceptable data loss determined by business requirements.”
A, C, Dare logistical concerns; onlyBdefines the RPO itself.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Business Continuity Objectives (RTO/RPO).
Which of the following should be of GREATEST concern to a risk practitioner reviewing an organization ' s disaster recovery plan (DRP)?
Risk scenarios used for the plan were last tested two years ago.
The IT steering committee determined the application recovery priorities.
The disaster recovery plan (DRP) does not identify a hot site.
The call list in the plan was last updated a year ago.
Which of the following is the BEST approach for determining whether a risk action plan is effective?
Comparing the remediation cost against budget
Assessing changes in residual risk
Assessing the inherent risk
Monitoring changes of key performance indicators(KPIs)
According to the CRISC Review Manual (Digital Version), assessing changes in residual risk is the best approach for determining whether a risk action plan is effective, as it measures the impact and value of the risk response actions and controls on the risk level. Residual risk is the risk that remains after the risk response actions and controls have been implemented. Assessing changes in residual risk helps to:
Evaluate the extent to which the risk response actions and controls have reduced the likelihood and/or impact of the risk to an acceptable level
Identify and report any deviations, errors, or weaknesses in the risk response actions and controls and their performance
Recommend and implement corrective actions or improvement measures to address any issues or deficiencies in the risk response actions and controls
Monitor and measure the effectiveness and efficiency of the risk response actions and controls and their alignment with the organization’s risk appetite and risk tolerance
Update the risk register and the risk treatment plan to reflect the current risk status and the residual risk levels
References = CRISC Review Manual (Digital Version), Chapter 3: IT Risk Response, Section 3.2: Risk Response Process, pp. 161-1621
Which of the following is the BEST approach for obtaining management buy-in
to implement additional IT controls?
List requirements based on a commonly accepted IT risk management framework.
Provide information on new governance, risk, and compliance (GRC) platform functionalities.
Describe IT risk impact on organizational processes in monetary terms.
Present new key risk indicators (KRIs) based on industry benchmarks.
Presenting the impact of IT risks on organizational processes in monetary terms is effective for obtaining management buy-in because it directly relates to the organization ' s financial health and decision-making. It provides a clear and tangible understanding of the potential financialimplications of risks, making it easier for management to appreciate the need for additional controls.
Which of the following BEST supports the integration of IT risk management into an organization ' s strategic planning?
Clearly defined organizational goals and objectives
Incentive plans that reward employees based on IT risk metrics
Regular organization-wide risk awareness training
A comprehensive and documented IT risk management plan
A comprehensive and documented IT risk management plan provides a structured approach to identifying, assessing, and mitigating IT risks. Integrating this plan into the organization ' s strategic planning ensures that IT risk considerations are aligned with business objectives and are factored into decision-making processes at the strategic level.
Which of the following is a crucial component of a key risk indicator (KRI) to ensure appropriate action is taken to mitigate risk?
Management intervention
Risk appetite
Board commentary
Escalation triggers
The best answer is D. Escalation triggers. Escalation triggers are predefined thresholds or conditions that indicate when a key risk indicator (KRI) has reached a critical level that requires immediate attention or action. Escalation triggers can be based on quantitative or qualitative measures, such as percentages, scores, ratings, or colors. Escalation triggers can help to ensure appropriate action is taken to mitigate risk, because they provide clear and timely signals that alert the risk owners, managers, and other stakeholders of the need to review and revise the risk response plan, or to implement additional or alternative controls. Escalation triggers can also help to communicate and report the risk status and the risk response actions to the senior management and the board, and to obtain their support and approval, if needed. The otheroptions are not the best answer, although they may be related or influential to the KRI and the risk mitigation. Management intervention is a part of the risk response process, which involves the actions and decisions taken by the management to address the risk, such as approving, implementing, or monitoring the controls. Management intervention can help to mitigate risk, but it is not a component of the KRI, rather it is a consequence or a result of the escalation triggers. Risk appetite is the amount and type of risk that an organization is willing to accept or pursue in order to achieve its objectives. Risk appetite can help to define and align the KRI and the escalation triggers with the organizational strategy and culture, but it is not a component of the KRI, rather it is a factor or a driver of the KRI. Board commentary is a part of the risk reporting process, which involves the feedback and guidance provided by the board on the risk management process and performance. Board commentary can help to improve and enhance the KRI and the risk mitigation, but it is not a component of the KRI, rather it is a source or a resource of the KRI. References = Key Risk Indicators: A Practical Guide | SafetyCulture, KRI Framework for Operational Risk Management | Workiva
An organization is considering the adoption of an aggressive business strategy to achieve desired growth From a risk management perspective what should the risk practitioner do NEXT?
Identify new threats resorting from the new business strategy
Update risk awareness training to reflect current levels of risk appetite and tolerance
Inform the board of potential risk scenarios associated with aggressive business strategies
Increase the scale for measuring impact due to threat materialization
The next thing that the risk practitioner should do from a risk management perspective when the organization is considering the adoption of an aggressive business strategy to achieve desired growth is to identify new threats resulting from the new business strategy. A threat is a potentialcause of an unwanted incident that may affect the achievement of the objectives. An aggressive business strategy is a strategy that involves pursuing high-risk, high-reward opportunities or initiatives to gain a competitive advantage or a significant market share. An aggressive business strategy may introduce new threats or increase thelikelihood or impact of existing threats, such as market volatility, regulatory changes, customer dissatisfaction, or competitor retaliation. Therefore, the risk practitioner should identify the new threats resulting from the new business strategy, and assess their potential consequences and implications for the organization. The other options are not as immediate as identifying new threats resulting from the new business strategy, as they are related to the update, information, or measurement of the risk management process, not the identification or analysis of the risk. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.3: IT Risk Scenarios, page 23.
Which of the following BEST indicates that an organization ' s disaster recovery plan (DRP) will mitigate the risk of the organization failing to recover from a major service disruption?
An experienced and certified disaster recovery team
A record of quarterly disaster recovery tests
A comprehensive list of critical applications
A defined recovery point objective (RPO)
Frequent and well-documented testing of the DRP demonstrates the plan ' s effectiveness and readiness to handle real disruptions.
Which of the following BEST measures the efficiency of an incident response process?
Number of incidents escalated to management
Average time between changes and updating of escalation matrix
Average gap between actual and agreed response times
Number of incidents lacking responses
The average gap between actual and agreed response times is the best measure of the efficiency of an incident response process, as it indicates how well the process meets the service level agreements (SLAs) and the expectations of the stakeholders. A smaller gap means that the process is more efficient and effective in resolving incidents within the agreed time frame. The other options are not the best measures of the efficiency of an incident response process, as they do not directly reflect the performance of the process against the SLAs. The number of incidents escalated to management may indicate the complexity or severity of the incidents, but not the efficiency of the process. The average time between changes and updating of escalation matrix may indicate the agility or flexibility of the process, but not the efficiency of the process. The number of incidents lacking responses may indicate the capacity or availability of the process, but not the efficiency of the process. References = Top 5 Incident Response Metrics with Real-World Examples & Impact; Mastering Incident Response: Best Practices for Effective Handling; The Five Steps of Incident Response
Which of the following is the BEST way to validate the results of a vulnerability assessment?
Perform a penetration test.
Review security logs.
Conduct a threat analysis.
Perform a root cause analysis.
According to the CRISC Review Manual (Digital Version), the best way to validate the results of a vulnerability assessment is to perform a penetration test, which is a type of security testing that simulates an attack on the IT assets and processes to exploit the identified vulnerabilities and evaluate the potential impact and severity of the attack. Performing a penetration test helps to:
Confirm the existence and exploitability of the vulnerabilities detected by the vulnerability assessment
Measure the effectiveness and efficiency of the existing security controls and countermeasures
Identify and prioritize the risks and gaps in the security posture of the IT assets and processes
Recommend and implement appropriate remediation and mitigation actions to address the vulnerabilities and risks
Enhance the security awareness and resilience of the organization
References = CRISC Review Manual (Digital Version), Chapter 1: IT Risk Identification, Section 1.5: IT Risk Identification Methods and Techniques, pp. 36-371
When determining the accuracy of a key risk indicator (KRI), it is MOST important that the indicator:
is correlated to risk and tracks variances in the risk.
is assigned to IT processes and projects with a low level of risk.
has a high correlation with the process outcome.
triggers response based on risk thresholds.
The accuracy of a key risk indicator (KRI) is the degree to which the indicator reflects the true level and trend of the risk. It is most important that the indicator is correlated to risk and tracks variances in the risk, as this ensures that the indicator is relevant, reliable, and responsive to the risk situation. A correlated indicator has astrong and consistent relationship with the risk, meaning that changes in the indicator reflect changes in the risk. A variance-tracking indicator measures the difference between the actual and expected risk level, meaning that the indicator can detect and report deviations from the risk appetite or threshold. According to the CRISC Review Manual 2022, correlation and variance tracking are two of the key characteristics of an effective KRI1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, correlation and variance tracking are the correct answer to this question2.
Assigning the indicator to IT processes and projects with a low level of risk, having a high correlation with the process outcome, and triggering response based on risk thresholds are not the most important factors for determining the accuracy of a KRI. These factors may be useful or desirable, but they do not directly affect the accuracy of the indicator. Assigning the indicator to IT processes and projects with a low level of risk may reduce the complexity and uncertainty ofthe indicator, but it may also limit the scope and value of the indicator. Having a high correlation with the process outcome may indicate that the indicator is aligned with the business objectives, but it may not capture the risk factors or drivers that affect the outcome. Triggering response based on risk thresholds may indicate that the indicator is actionable and timely, but it may not reflect the actual or potential changes in the risk level.
Which of the following should be the risk practitioner ' s FIRST course of action when an organization plans to adopt a cloud computing strategy?
Request a budget for implementation
Conduct a threat analysis.
Create a cloud computing policy.
Perform a controls assessment.
A risk practitioner is utilizing a risk heat map during a risk assessment. Risk events that are coded with the same color will have a similar:
risk score
risk impact
risk response
risk likelihood.
A risk heat map is a graphical tool that displays the risk events in a matrix based on their likelihood and impact. Risk events that are coded with the same color will have a similar risk likelihood, which is the probability or frequency of occurrence of a risk event. Risk score, riskimpact, and risk response are other possible attributes of risk events, but they are not represented by the color coding in a risk heatmap. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Which of the following is MOST important for ensuring anonymous reporting of non-compliant activity?
Implementing homomorphic encryption.
Establishing an employee feedback channel.
Establishing a dedicated compliance function.
Implementing an incentive program.
The correct answer is B because anonymous reporting requires a reporting channel through which employees can raise concerns or report non-compliant activity without being personally identified. ISACA’s Code of Professional Ethics includes reporting obligations and states that anyone who witnesses a member violation can report it through the ethics complaint process.
The uploaded CRISC notes emphasize that a risk-aware culture escalates issues when suspicious activity is noticed and that failure to internally report a successful attack is a major concern.
A is too technical and unrelated to employee reporting. C may support compliance oversight, but it does not ensure anonymous reporting. D may encourage reporting, but incentives do not provide anonymity.
===========
Which of the following should be the PRIMARY consideration when assessing the risk of using Internet of Things (loT) devices to collect and process personally identifiable information (Pll)?
Costs and benefits
Local laws and regulations
Security features and support
Business strategies and needs
Local laws and regulations should be the primary consideration when assessing the risk of using Internet of Things (IoT) devices to collect and process personally identifiable information (PII), because they define the legal and ethical obligations and boundaries for the protection and privacy of PII, and the potential consequences of non-compliance or violation. IoT devices are devices that are connected to the internet and can collect, transmit, or process data, such as smart watches, cameras, sensors, or appliances. PII is information that can be used to identify, locate, or contact an individual, such as name, address, phone number, or email address. PII is considered sensitive and confidential, and may be subject to various laws and regulations that govern how it should be collected, processed, stored, shared, or disposed, such as the General Data Protection Regulation (GDPR) in the European Union, or the California Consumer Privacy Act (CCPA) in the United States. Therefore, local laws and regulations should be the primary consideration, as they provide the legal and ethical framework and guidance for the use of IoT devices to collect and process PII, and the potential risks and impacts of non-compliance or violation. Costs and benefits, security features and support, and business strategies and needs are all possible considerations when assessing the risk of using IoT devices to collect and process PII, but they are not the primary consideration, as they may vary or conflict depending on the situation or context, and may not override the local laws and regulations. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 158
Which of the following tools is MOST effective in identifying trends in the IT risk profile?
Risk self-assessment
Risk register
Risk dashboard
Risk map
A risk dashboard is a graphical tool that displays the key indicators and metrics of the organization’s IT risk profile, such as the risk level, status, trend, performance, etc., using charts, graphs, tables, etc. A risk dashboard can help the organization to monitor and communicate the IT risk profile, and to support the decision making and planning for the IT risk management.
A risk dashboard is the most effective tool in identifying trends in the IT risk profile, because it provides a visual and intuitive representation of the changes and variations in the IT risk profile over time, and highlights the most significant and relevant IT risks that need to be addressed or monitored. A risk dashboard can also help to compare and contrast the IT risk profile with the organization’s IT objectives and risk appetite, and to identify the gaps or opportunities for improvement.
The other options are not the most effective tools in identifying trends in the IT risk profile, because they do not provide the same level of visibility and clarity that a risk dashboard provides, and they may not be updated or aligned with the organization’s IT objectives and risk appetite.
A risk self-assessment is a process of identifying, analyzing, and evaluating the IT risks that may affect the organization’s objectives and operations, using the input and feedback from the individuals or groups that are involved or responsible for the IT activities or functions. A risk self-assessment can help the organization to understand and document the IT risk profile, and to align it with the organization’s IT strategy and culture, but it is not the most effective tool in identifying trends in the IT risk profile, because it may not reflect the current or accurate state and performance of the IT risk profile, and it may not cover all the relevant or emerging IT risks that may exist or arise.
A risk register is a document that records and tracks the information and status of the identified IT risks and their responses. It includes the IT risk description, category, source, cause, impact, probability, priority, response, owner, action plan, status, etc. A risk register can help the organization to identify, analyze, evaluate, and communicate the IT risks and their responses, and to align them with the organization’s IT strategy and culture, but it is not the most effective tool in identifying trends in the IT risk profile, because it may not provide a visual and intuitive representation of the changes and variations in the IT risk profile over time, and it may not highlight the most significant and relevant IT risks that need to be addressed or monitored.
A risk map is a graphical tool that displays the results of the IT risk analysis in a matrix format, using colors and symbols to indicate the level and priority of the IT risks. A risk map can show the distribution and comparison of the IT risks based on various criteria, such as likelihood, impact, category, source, etc. A risk map can help the organization to assess and prioritize the IT risks, and to design and implement appropriate controls or countermeasures to mitigate or prevent the IT risks, but it is not the most effective tool in identifying trends in the IT risk profile, because it may not provide a visual and intuitive representation of the changes and variations in the IT risk profile over time, and it may not reflect the organization’s IT objectives and risk appetite. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 180
CRISC Practice Quiz and Exam Prep
Which of the following is the MOST important reason to link an effective key control indicator (KCI) to relevant key risk indicators (KRIs)?
To monitor changes in the risk environment
To provide input to management for the adjustment of risk appetite
To monitor the accuracy of threshold levels in metrics
To obtain business buy-in for investment in risk mitigation measures
Key control indicators (KCIs) are metrics that measure how well a specific control is performing in reducing the causes, consequences, or likelihood of a risk1. Key risk indicators (KRIs) are metrics that measure changes in the risk exposure or the potential impact of a risk2. By linkingan effective KCI to relevant KRIs, the organization can monitor changes in the risk environment and assess how the control is influencing the risk level3. This can help the organization to:
Identify emerging or escalating risks and take timely and appropriate actions
Evaluate the effectiveness and efficiency of the control and make improvements if needed
Align the control with the risk appetite and tolerance of the organization
Communicate the risk and control status to stakeholders and regulators
References = Risk and Information Systems Control Study Manual, Chapter 6: Risk Response and Mitigation4
A risk practitioner has determined that a key control does not meet design expectations. Which of the following should be done NEXT?
Document the finding in the risk register.
Invoke the incident response plan.
Re-evaluate key risk indicators.
Modify the design of the control.
The next step after determining that a key control does not meet design expectations is to document the finding in the risk register, because this helps to record and track the information about the identified risk, such as its description, likelihood, impact, response, and status. A key control is a control that addresses a significant risk or supports a critical business process or objective. A control design expectation is a criterion or requirement that defines how the control should operate or perform to achieve its objective. If a key control does not meet its design expectation, it means that there is a gap, weakness, or deficiency in the control that may compromise its effectiveness or efficiency, and increase the risk exposure or impact. By documenting the finding in the risk register, the risk practitioner can communicate and report the risk issue to the relevant stakeholders, such as the risk owner, the management, or the auditor, and initiate the appropriate risk response actions, such as modifying the design of the control, implementing a compensating control, or accepting the risk. The other options are not the best next steps after determining that a key control does not meet design expectations. Invoking the incident response plan is a reactive measure that is triggered when a risk event occurs or is imminent, and requires immediate action to contain, mitigate, or recover from the incident. However, in this case, the risk event has not occurred yet, and there may be time to prevent or reduce it by improving the control design. Re-evaluating key risk indicators is a monitoring activity that measures and evaluates the level and impact of risks, and provides timely signals that something may be going wrong or needs urgent attention. However, in this case, the risk practitioner has already identified the risk issue, and needs to document and address it, rather than re-evaluate it. Modifying the design of the control is a possible risk response action that may be taken to improve the control and reduce the risk, but it is not the next step after determining that the key control does not meet design expectations. The next step is to document the finding in the risk register, and then decide on the best risk response action, which may or may not be modifying the design of the control, depending on the cost-benefit analysis, the risk assessment, and the risk response strategy. References = Risk IT Framework, ISACA, 2022, p. 13
Which of the following is the MOST effective way to determine if a risk factor exceeds risk tolerance?
Review the risk profile.
Conduct a gap analysis.
Monitor changes in external risk factors.
Analyze key performance indicators (KPIs).
The correct answer isAbecause therisk profileis the most effective tool for determining whether a risk factor exceedsrisk tolerance. The risk profile provides an aggregated view of current enterprise risk, including likelihood, impact, and status, which allows management and practitioners to judge whether exposure remains within acceptable thresholds.
The other options are less suitable:
B. Conduct a gap analysishelps identify differences between current and desired states, but it is not the main tool for determining whether current exposure exceeds tolerance.
C. Monitor changes in external risk factorsmay identify triggers, but it does not itself determine whether tolerance has been exceeded.
D. Analyze key performance indicators (KPIs)measures performance, not risk exposure as directly as the risk profile.
Exact Extracts supporting the answer:
“The most important aspect to consider in relation to a risk profile is the aggregated risk to the enterprise.”
“The main purpose of risk monitoring is to provide timely information on the actual status of the enterprise with regard to risk with the risk profile offering an overall risk status.”
“When reporting the status of the IT control environment to management the most important component is the risk profile of the enterprise.”
“Risk tolerance is the permissible deviation from declared risk appetite levels in an enterprise.”
“A risk treatment plan should be developed when risk levels exceed risk appetite or tolerance.”
These extracts show that therisk profileis the main instrument for understanding current enterprise risk exposure and judging whether it remains within tolerance.
Which of the following is the BEST evidence of a well-defined risk event?
Forensic investigations include chain-of-custody requirements
Impact analyses include annual loss expectancy (ALE)
Incident response plans include recovery time objectives (RTOs)
Critical systems include key performance indicators (KPIs)
Annual Loss Expectancy (ALE)quantifies a risk event’sexpected financial impactand is derived fromSingle Loss Expectancy (SLE) × Annualized Rate of Occurrence (ARO).
CRISC guidance states:
“A well-defined risk event includes quantified impact analysis such as annual loss expectancy to facilitate prioritization and comparison.”
Chain-of-custody and KPIs are unrelated to defining risk events.
Hence,Bis correct.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Risk Quantification and Impact Analysis.
Which of the following would MOST effectively reduce risk associated with an increased volume of online transactions on a retailer website?
Hot backup site
Transaction limits
Scalable infrastructure
Website activity monitoring
Scalable infrastructure ensures the system can handle increased load without failure, thus minimizing the risk of downtime or degraded performance during traffic spikes.
Which of the following deficiencies identified during a review of an organization ' s cybersecurity policy should be of MOST concern?
The policy lacks specifics on how to secure the organization ' s systems from cyberattacks.
The policy has gaps against relevant cybersecurity standards and frameworks.
The policy has not been reviewed by the cybersecurity team in over a year.
The policy has not been approved by the organization ' s board.
The policy has not been approved by the organization’s board should be of most concern, as it indicates a lack of governance and oversight for the organization’s cybersecurity posture. The board is ultimately responsible for setting the strategic direction, objectives, and risk appetite of the organization, and for ensuring that the cybersecurity policy aligns with them. Without the board’s approval, the policy may not reflect the organization’s vision, mission, values, and culture, and may not be communicated, implemented, or enforced effectively. The board’s approval also demonstrates the commitment and support of the senior management for the cybersecurity program, and enhances the accountability and responsibility of the stakeholders involved.
Avoiding a business activity removes the need to determine:
systemic risk
residual risk
inherent risk
control risk
Avoidancemeans the risk is no longer relevant because the activity is not pursued. As a result, there isno residual riskto manage or control. ISACA’s risk response options include avoidance, which eliminates the need for further risk treatment.
===========
Which of the following is the MOST important outcome of reviewing the risk management process?
Assuring the risk profile supports the IT objectives
Improving the competencies of employees who performed the review
Determining what changes should be made to IS policies to reduce risk
Determining that procedures used in risk assessment are appropriate
The most important outcome of reviewing the risk management process is assuring that the risk profile supports the IT objectives, because this ensures that the organization is managing its IT-related risks in alignment with its business goals and priorities. The risk profile is a summary of the key risks that the organization faces, their likelihood, impact, and response strategies. The IT objectives are the specific and measurable outcomes that the organization expects to achieve from its IT investments and activities. Byreviewing the risk management process, the organization can evaluate whether the risk profile is accurate, complete, and up-to-date, and whether the risk responses are effective, efficient, and consistent with the IT objectives. The review can also identify any gaps, issues, or opportunities for improvement in the risk management process, and provide recommendations for enhancing the process and its outcomes. The review can also help to communicate and report the value and performance of the risk management process to the senior management, the board of directors, and other stakeholders. References = Risk IT Framework, ISACA, 2022, p. 17
The MAIN purpose of selecting a risk response is to.
ensure compliance with local regulatory requirements
demonstrate the effectiveness of risk management practices.
ensure organizational awareness of the risk level
mitigate the residual risk to be within tolerance
The main purpose of selecting a risk response is to mitigate the residual risk to be within tolerance. Residual risk is the risk that remains after applying a risk response. Risk tolerance is the amount and type of risk that an organization is willing to accept in order to achieve its objectives. Risk response is the process of selecting and implementing actions to address risk. The goal of risk response is to reduce the residual risk to a level that is acceptable to the organization and its stakeholders. The other options are not the main purpose of selecting a risk response, although they may be secondary benefits or outcomes. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.1, page 4-23.
Which of the following would be a risk practitioner ' s MOST important action upon learning that an IT control has failed?
Implement a replacement control.
Adjust residual risk rating.
Escalate to senior management.
Review compensating controls.
Upon discovering that an IT control has failed, the risk practitioner ' s most important action is to review compensating controls. This involves assessing whether other existing controls can mitigate the risk associated with the failed control. Evaluating compensating controls helps determine the immediate impact of the control failure and guides decisions on necessary remediation steps.
Which of the following has the GREATEST influence on an organization ' s risk appetite?
Threats and vulnerabilities
Internal and external risk factors
Business objectives and strategies
Management culture and behavior
Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite is influenced by various factors, such as the organization’s mission, vision, values, culture, stakeholders, resources, capabilities, etc. However, the factor that has the greatest influence on the organization’s risk appetite is the business objectives and strategies, which are the desired outcomes and the plans to achieve them. The business objectives and strategies define the direction and scope of the organization, and the risk appetite reflects the level of risk that the organization is prepared to take to accomplish them. The risk appetite should be aligned with the business objectives and strategies, andshould provide guidance for the risk management activities and decisions. References = CRISC Review Manual, 7th Edition, page 61.
An organization has procured a managed hosting service and just discovered the location is likely to be flooded every 20 years. Of the following, who should be notified of this new information FIRST.
The risk owner who also owns the business service enabled by this infrastructure
The data center manager who is also employed under the managed hosting services contract
The site manager who is required to provide annual risk assessments under the contract
The chief information officer (CIO) who is responsible for the hosted services
The risk owner is the person who has the authority and accountability to manage a specific risk and its associated controls. The risk owner is also responsible for ensuring that the risk is within the acceptable level and that the risk response is effective and efficient. In this case, the risk owner is also the owner of the business service that depends on the managed hosting service. Therefore, the risk owner should be notified of the new information about the flood risk first, as they have the most interest and influence on the risk and its impact on the business objectives. The risk owner can then decide on the appropriate actions to take, such as reviewing the contract terms, requesting additional controls, or changing the service provider. The other options are not the correct answers because they are not the primary stakeholders of the risk and its consequences. The data center manager is an employee of the managed hosting service provider, not the organization that procured the service. The data center manager may not have the authority or the incentive to address the flood risk or inform the organization. The site manager is also an employee of the managed hosting service provider, and their role is to conduct annual risk assessments under the contract. The site manager may not be aware of the new information or have the responsibility to communicate it to the organization. The CIO is the senior executive who oversees the IT strategy and operations of the organization. The CIO may have a general interest in the managed hosting service and its risks, but they are not the direct owner or managerof the specific risk or the business service that relies on the service. References = CRISC Review Manual, pages 32-331; CRISC Review Questions, Answers & Explanations Manual, page 702
Business information security officer
Service level manager
Business process manager
Data center operations manager
The business process manager is best suited to own business continuity controls because they have direct responsibility for the continuity of the business process and understand the criticality of maintaining operations during disruptions. While security officers and operations managers have important roles, the business process manager is accountable for ensuring the process continues to meet business objectives and should lead continuity efforts【5:513, 5:514†CRISC_SentenceinNOTE30.pptx】.
A key risk indicator (KRI) indicates a reduction in the percentage of appropriately patched servers. Which of the following is the risk practitioner ' s BEST course of action?
Determine changes in the risk level.
Outsource the vulnerability management process.
Review the patch management process.
Add agenda item to the next risk committee meeting.
A key risk indicator (KRI) is a metric that measures the changes in the level of risk exposure, such as by monitoring the risk drivers, triggers, or events. A KRI indicates a reduction in the percentage of appropriately patched servers means that the enterprise is not applying the latest security updates or fixes to its servers, which could expose them to vulnerabilities or threats. The best course of action for the risk practitioner when a KRI indicates a reduction in the percentage of appropriately patched servers is to determine changes in the risk level. The risk level is the measure of the impact and likelihood of the risk, and it should be consistent and comparable across the enterprise and over time. By determining changes in the risklevel, the risk practitioner can assess the current or emerging risks, and decide on the appropriate risk response strategy and actions. The other options are not the best course of action, as they involve different aspects or outcomes of the risk management process:
Outsource the vulnerability management process means that the enterprise transfers the responsibility or burden of identifying, analyzing, prioritizing, and remediating the vulnerabilities in the IT systems and applications to a third party, such as a vendor or a contractor. This may not be a feasible or effective way to address the risk of unpatched servers, as it may not reduce the exposure or impact of the risk, or may introduce new risks, such as contractual disputes, quality issues, or intellectual property rights.
Review the patch management process means that the enterprise evaluates the existing procedures and practices for applying the security updates or fixes to the servers, and identifies the gaps or weaknesses that need to be addressed. This may be a useful step in the risk management process, but it is not the best course of action, as it may not provide immediate or sufficient information or action to address the risk of unpatched servers, or may not account for the uncertainties or complexities of the risk.
Add agenda item to the next risk committee meeting means that the enterprise communicates the risk of unpatched servers to the senior executives who oversee the enterprise-wide risk management program, and provide guidance and direction to the risk owners and practitioners. This may be a helpful step in the risk management process, but it is not the best course of action, as it may not provide timely or adequate information or action to address the risk of unpatched servers, or may not reflect the urgency or priority of the risk. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.3.2.1, pp. 171-172.
An organization has outsourced its billing function to an external service provider. Who should own the risk of customer data leakage caused by the service provider?
The service provider
Vendor risk manager
Legal counsel
Business process owner
The business process owner should own the risk of customer data leakage caused by the service provider, as they have the responsibility and authority over the design, execution, and performance of the business process. The business process owner is also accountable for the risks and controls associated with their process, and they can provide valuable input and feedback on the likelihood and impact of customer data leakage on the process outcomes and objectives.
The other options are not the best choices for owning the risk of customer data leakage caused by the service provider. The service provider is responsible for delivering and supporting the billing function and ensuring the security and privacy of the customer data, but they may not have the full visibility or understanding of the business process and objectives. The vendor risk manager is responsible for managing and monitoring the vendor relationship and performance, but they may not have the direct involvement or influence on the business process and its risks and controls. The legal counsel is responsible for providing legal advice and guidance on the contractual and regulatory obligations and implications of the outsourcing arrangement, but they may not have the detailed knowledge or experience of the business process and its risks andcontrols. References = Guide to Vendor Risk Assessment | Smartsheet, IT Risk Resources | ISACA, Data Ownership: Considerations for Risk Management - ISACA
Which of the following is the MOST important consideration when selecting key risk indicators (KRIs) to monitor risk trends over time?
Ongoing availability of data
Ability to aggregate data
Ability to predict trends
Availability of automated reporting systems
Ongoing availability of data is the most important consideration when selecting key risk indicators (KRIs) to monitor risk trends over time, as it ensures that the KRIs can provide timely and reliable information on the current and future risk status and performance. KRIs are metrics that measure the level of risk exposureand the effectiveness of risk response strategies, and they should be aligned with the enterprise’s risk appetite and objectives. Ongoing availability ofdatameans that the data sources and collection methods for the KRIs are consistent, accessible, and sustainable, and that the data quality and integrity are maintained and verified. Ability to aggregate data, ability to predict trends, and availability of automated reporting systems are not the most important considerations, as they do not affect the validity and usefulness of the KRIs, but rather the presentation and analysis of the KRI data. References = CRISC Certified in Risk and Information Systems Control – Question213; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 213.
When reviewing management ' s IT control self-assessments, a risk practitioner noted an ineffective control that links to several low residual risk scenarios. What should be the NEXT course of action?
Assess management ' s risk tolerance.
Recommend management accept the low-risk scenarios.
Propose mitigating controls
Re-evaluate the risk scenarios associated with the control
IT control self-assessments are techniques that involve identifying and evaluating the effectiveness and efficiency of the IT controls that are designed and implemented to mitigate the IT risks, by the managers and staff within the organization12.
An ineffective control is a control that does not achieve its intended objective or purpose, or does not operate as designed or expected34.
A low residual risk scenario is a situation or occurrence that has a low likelihood and impact of affecting the organization’s objectives, performance, or value creation, after considering the existing controls and their effectiveness56.
The next course of action when reviewing management’s IT control self-assessments and noting an ineffective control that links to several low residual risk scenarios is to recommend management accept the low-risk scenarios, which is a risk response strategy that involves acknowledging and tolerating the level of risk exposure, and not taking any further action to reduce or eliminate it78.
Recommending management accept the low-risk scenarios is the next course of action because it is the most cost-effective and reasonable option, given that the level of risk exposure is low andacceptable, and the cost and effort of implementing or improving the control may outweigh the potential benefits or value78.
Recommending management accept the low-risk scenarios is also the next course of action because it is consistent with the risk management process and objectives, which are to identifyand address the risks that may affect the achievement of the organization’s goals and the delivery of value to the stakeholders, and to optimize the balance between risk and reward78.
The other options are not the next course of action, but rather possible alternatives or steps that may be considered or followed in different circumstances or scenarios. For example:
Assessing management’s risk tolerance is a step that involves determining and communicating the acceptable or tolerable level of risk exposure for the organization or its business units, based on the organization’s risk appetite, criteria, and objectives78. However, this stepis not the next course of action because it is usually done before or during the risk assessment process, and not after noting an ineffective control that links to several low residual risk scenarios78.
Proposing mitigating controls is a course of action that involves suggesting or recommending additional or alternative controls that can reduce or eliminate the level of risk exposure, and improve the effectiveness and efficiency of the risk management process78. However, this course of action is not the next course of action because it is not necessary or appropriate for low residual risk scenarios, as the cost and effort of implementing or improving the controls may outweigh the potential benefits or value78.
Re-evaluating the risk scenarios associated with the control is a course of action that involves revising and updating the likelihood and impact of the risk scenarios, and the level of risk exposure or tolerance for the organization, based on the current or changed conditions or factors that influence the risk landscape78. However, this course of action is not the next course of action because it is not required or relevant for low residual risk scenarios, as the level of risk exposure is already low and acceptable, and the ineffective control does not significantly affect the risk assessment78. References =
1: Control Self Assessments - PwC1
2: Control self-assessment - Wikipedia2
3: Ineffective Controls: What They Are and How to Identify Them3
4: Ineffective Controls: What They Are and How to Identify Them4
5: Residual Risk - Definition and Examples5
6: Residual Risk: Definition, Formula & Management6
7: Risk IT Framework, ISACA, 2009
8: IT Risk Management Framework, University of Toronto, 2017
Which of the following is MOST important when creating a program to reduce ethical risk?
Defining strict policies
Developing an organizational communication plan
Conducting a gap analysis
Obtaining senior management commitment
Which of the following is MOST important for maintaining the effectiveness of an IT risk register?
Removing entries from the register after the risk has been treated
Recording and tracking the status of risk response plans within the register
Communicating the register to key stakeholders
Performing regular reviews and updates to the register
An IT risk register is a document that records the identified IT risks, their analysis, and their responses. It is a useful tool for managing and communicating the IT risks throughout the project or the organization. The most important factor for maintaining the effectiveness of an IT risk register is to perform regular reviews and updates to the register, meaning that the riskpractitioner should periodically check and revise the riskregister to reflect the changes in the IT risk environment, the project status, or the organization’s objectives. Performing regular reviews and updates to the register can help to ensure that the risk register is accurate, complete, and current, and that it provides relevant and reliable information for the risk management decision making and actions. Performing regular reviews and updates to the register can also help to identify any new or emerging IT risks, as well as to monitor and report on the IT risk performance and improvement. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.1, p. 106-107
Which of the following BEST balances the costs and benefits of managing IT risk*?
Prioritizing and addressing risk in line with risk appetite. Eliminating risk through preventive and detective controls
Considering risk that can be shared with a third party
Evaluating the probability and impact of risk scenarios
Risk appetite is the broad-based amount of risk that an organization is willing to accept in its activities. Risk appetite reflects the level of risk that the organization is prepared to take to achieve its strategic goals, and provides guidance and boundaries for the risk management activities and decisions. The best way to balance the costs and benefits of managing IT risk is to prioritize and address risk in line with risk appetite, which means that the organization should identify, assess, treat, monitor, and communicate the risks that are within or exceed the risk appetite, and allocate the resources and efforts accordingly. By doing so, the organization can optimize its risk-return trade-off, align its risk exposure with its strategic objectives, and enhance its risk culture and performance. References = 5
Which of the following is the GREATEST risk to an organization when using a public AI system to process credit card transactions?
Potential exposure of sensitive information
Use of financial data to train the AI model
Noncompliance with security standards
AI hallucinations and bias
The correct answer isAbecause the greatest risk when using apublic AI systemto process credit card transactions is thepotential exposure of sensitive information. Credit card data is highly sensitive, and use of a public AI platform can introduce serious confidentiality, privacy, and data handling concerns. Exposure of that data can lead to fraud, regulatory issues, contractual violations, and significant business impact.
The other options are important, but not the greatest primary risk:
B. Use of financial data to train the AI modelis a specific form of data misuse, but it falls within the broader and more critical risk of sensitive information exposure.
C. Noncompliance with security standardsis also significant, but it is often a consequence of exposing or improperly handling sensitive payment data.
D. AI hallucinations and biasare important AI risks, but they are not the primary concern in payment card processing.
Exact Extracts supporting the answer:
“The MOST important consideration when transmitting personal information across networks is ensuring the privacy of the personal information.”
“The data security control that BEST protects the confidentiality of data stored on backup media in transit to a third-party storage facility is encryption.”
“The MOST significant risk associated with handling credit card data through a web application is failure to store credit card data in a secure area segregated from the demilitarized zone.”
“To determine the level of protection required for securing personally identifiable information a risk practitioner should PRIMARILY consider the sensitivity property of the information.”
These extracts support that the primary concern with payment-card-related processing is protecting the confidentiality of sensitive data. Therefore, the greatest risk is thepotential exposure of sensitive information.
===========
Which of the following roles should be assigned accountability for monitoring risk levels?
Risk practitioner
Business manager
Risk owner
Control owner
The risk owner should be assigned accountability for monitoring risk levels, as they have the authority and responsibility to manage the risk and its associated controls, and to report on the risk status and performance. The risk practitioner, the business manager, and the control owner are not the best choices, as they have different roles and responsibilities related to risk identification, assessment, response, and reporting, but they are not accountable for the risk and its monitoring. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following is the GREATEST advantage of implementing a risk management program?
Enabling risk-aware decisions
Promoting a risk-aware culture
Improving security governance
Reducing residual risk
A risk management program is a systematic and structured approach to identify, analyze, evaluate, treat, monitor, and communicate the risks that may affect the organization’s objectives and performance.
The greatest advantage of implementing a risk management program is enabling risk-aware decisions. This means that the organization incorporates the risk information and analysis into its decision making process, such as strategic planning, resource allocation, project management, etc.
Enabling risk-aware decisions helps to optimize the outcomes and benefits of the decisions, balance the opportunities and threats of the decisions, and align the decisions with the organization’s risk appetite and tolerance.
The other options are not the greatest advantages of implementing a risk management program. They are either secondary or not essential for risk management.
The references for this answer are:
Risk IT Framework, page 25
Information Technology & Security, page 19
Risk Scenarios Starter Pack, page 17
The BEST way to improve a risk register is to ensure the register:
is updated based upon significant events.
documents possible countermeasures.
contains the risk assessment completion date.
is regularly audited.
A risk register is a tool that records and tracks the identified risks, their causes, impacts, probabilities, responses, and owners. It is a living document that should be updated regularly to reflect the changes in therisk environment and the status of the risk responses12. The best way to improve a risk register is to ensure that it is updated based upon significant events, such as:
New risks are identified or existing risks are eliminated
Risk probabilities or impacts change due to internal or external factors
Risk responses are implemented or modified
Risk owners or stakeholders change
Risk incidents or issues occur
Risk thresholds or appetite change
Risk reporting or communication requirements change
Updating the risk register based upon significant events can help to:
Maintain the accuracy and relevance of the risk information
Enhance the risk awareness and accountability of the risk owners and stakeholders
Support the risk monitoring and reporting activities
Facilitate the risk evaluation and decision-making processes
Improve the risk management performance and maturity
References =
Risk Register - Project Management Knowledge
How to Create a Risk Register: A Step-by-Step Guide - ProjectManager.com
After a risk has been identified, who is in the BEST position to select the appropriate risk treatment option?
The risk practitioner
The business process owner
The risk owner
The control owner
After a risk has been identified, the risk owner is in the best position to select the appropriate risk treatment option. The risk owner is the person or entity with the accountability and authority to manage a risk1. The risk owner is responsible for evaluating the risk, choosing the most suitable risk treatment option, implementing the risk treatment plan, and monitoring and reviewing the risk and its treatment2. The risk owner has the most knowledge and stake in the risk and its impact on the objectives and activities of the organization. The other options are not the best choices for selecting the risk treatment option, as they do not have the same level of accountability and authority as the risk owner. The risk practitioner is the person or entity with the knowledge and skills to perform the risk management activities1. The risk practitioner can assist the risk owner in identifying, analyzing, evaluating, and treating the risk, but the final decision and responsibility lies with the risk owner. The business process owner is the person or entity with the accountability and authority to manage a business process3. The business processowner may be affected by the risk or involved in the risk treatment, but the risk owner is the one who has the overall responsibility for the risk. The control owner is the person or entity with the accountability and authority to ensure that the controls are properly designed, implemented, and operated4. The control owner can provide input and feedback on the effectiveness and efficiency of the controls, but the risk owner is the one who decides which controls are needed and how they are applied. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.3, Page 51.
A failure in an organization s IT system build process has resulted in several computers on the network missing the corporate endpoint detection and response (EDR) software. Which of the following should be the risk practitioner’s IMMEDIATE concern?
Multiple corporate build images exist.
The process documentation was not updated.
The IT build process was not followed.
Threats are not being detected.
The risk associated with inadvertent disclosure of database records from a public cloud service provider (CSP) would MOST effectively be reduced by:
encrypting the data
including a nondisclosure clause in the CSP contract
assessing the data classification scheme
reviewing CSP access privileges
Encrypting the data would MOST effectively reduce the risk associated with inadvertent disclosure of database records from a public cloud service provider (CSP), because it is a control that protects the confidentiality and integrity of the data by transforming it into an unreadable and unmodifiable form, using a secret key or algorithm. Encrypting the data can prevent or minimize the unauthorized or accidental access, modification, or leakage of the data, especially when the data is stored, transmitted, or processed in a public cloud environment, which may have less security and control than a private or on-premise environment. The other options are not as effective as encrypting the data, because:
Option B: Including a nondisclosure clause in the CSP contract is a legal measure that can deter or penalize the CSP from disclosing the data to any third party, but it does not reduce the risk of inadvertent disclosure of the data, which may occur due to human error, system failure, or malicious attack, and it does not protect the data from unauthorized or accidental access, modification, or leakage.
Option C: Assessing the data classification scheme is a process that can help to identify and categorize the data according to its sensitivity, value, and criticality, and to determine the appropriate level of protection and handling for the data, but it does not reduce the risk of inadvertent disclosure of the data, which may affect any type or class of data, and it does not provide the specific or effective control to protect the data from unauthorized or accidental access, modification, or leakage.
Option D: Reviewing CSP access privileges is a procedure that can help to monitor and verify the access rights and permissions of the CSP to the data, and to ensure that they are aligned with the business needs and expectations, but it does not reduce the risk of inadvertent disclosure of the data, which may occur even with the legitimate or authorized access of the CSP, and it does not protect the data from unauthorized or accidental access, modification, or leakage by otherparties. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 211.
Which of the following is the PRIMARY risk management responsibility of the third line of defense?
Providing assurance of the effectiveness of risk management activities
Providing guidance on the design of effective controls
Providing advisory services on enterprise risk management (ERM)
Providing benchmarking on other organizations ' risk management programs
An organization has implemented a preventive control to lock user accounts after three unsuccessful login attempts. This practice has been proven to be unproductive, and a change in the control threshold value has been recommended. Who should authorize changing this threshold?
Risk owner
IT security manager
IT system owner
Control owner
According to the CRISC Review Manual, a control owner is the person who is accountable for ensuring that specific control activities are performed. The control owner is responsible for defining, implementing, monitoring, and improving the control. Therefore, the control ownershould authorize changing the control threshold value, as it is part of their role to ensure that the control is effective and efficient. The other options are not the correct answers, because they are not directly involved in the control activities. The risk owner is the person who is accountable for the risk and its associated mitigation actions. The IT security manager is the person who is responsible for overseeing the IT security function and ensuring that the IT security policy is enforced. The IT system owner is the person who is responsible for the operation andmaintenance of the IT system and its associated data. References = CRISC Review Manual, 7th Edition, Chapter 3, Section 3.1.2, page 108.
An audit reveals that several terminated employee accounts maintain access. Which of the following should be the FIRST step to address the risk?
Perform a risk assessment
Disable user access.
Develop an access control policy.
Perform root cause analysis.
The risk of terminated employee accounts maintaining access is that the former employees or unauthorized parties may use the accounts to access or manipulate the organization’s information systems or resources, and cause harm or damage to the organization and its stakeholders, such as data loss, data breach, system failure, fraud, etc.
The first step to address the risk of terminated employee accounts maintaining access is to disable user access, which means to revoke or remove the permissions or privileges that allow the accounts to access or use the organization’s information systems or resources. Disabling user access can help the organization to address the risk by providing the following benefits:
It can prevent or stop the former employees or unauthorized parties from accessing or using the organization’s information systems or resources, and reduce or eliminate the potential harm or damage that they may cause for the organization and its stakeholders.
It can ensure the confidentiality, integrity, availability, and reliability of the organization’s information systems or resources, and protect them from unauthorized access or manipulation.
It can provide useful evidence and records for the verification and validation of the organization’s access control function, and for the compliance with the organization’s access control policies and standards.
The other options are not the first steps to address the risk of terminated employee accounts maintaining access, because they do not provide the same level of urgency and effectiveness that disabling user access provides, and they may not be sufficient or appropriate to address the risk.
Performing a risk assessment is a process of measuring and comparing the likelihood and impact of various risk scenarios, and prioritizing them based on their significance and urgency.Performing a risk assessment can help the organization to understand and document the risk of terminated employee accounts maintaining access, but it is not the first step to address the risk, because it does not prevent or stop the former employees or unauthorized parties from accessing or using the organization’s information systems or resources, and it may not be timely or feasible to perform a risk assessment before disabling user access.
Developing an access control policy is a process of defining and describing the rules or guidelines that specify the expectations and requirements for the organization’s access control function, such as who can access what, when, how, and why. Developing an access control policy can help the organization to establish and communicate the boundaries and objectives for the organization’s access control function, but it is not the first step to address the risk, because it does not prevent or stop the former employees or unauthorized parties from accessing or using the organization’s information systems or resources, and it may not be relevant or applicable to the existing or emerging risk scenarios that may affect the organization’s access control function.
Performing a root cause analysis is a process of identifying and understanding the underlying or fundamental causes or factors that contribute to or result in a problem or incident that has occurred or may occur in the organization. Performing a root cause analysis can help the organization to address and correct the risk of terminated employee accounts maintaining access, and prevent or reduce its recurrence or impact, but it is not the first step to address the risk, because it does not prevent or stop the former employees or unauthorized parties from accessing or using the organization’s information systems or resources, and it may not be timely or feasible to perform a root cause analysis before disabling user access. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 207
CRISC Practice Quiz and Exam Prep
An organization has just implemented changes to close an identified vulnerability that impacted a critical business process. What should be the NEXT course of action?
Redesign the heat map.
Review the risk tolerance.
Perform a business impact analysis (BIA)
Update the risk register.
According to the CRISC Review Manual1, the risk register is a tool that records the results of risk identification, analysis, evaluation, and treatment. It should be updated whenever there is a change in the risk profile, such as when a vulnerability is closed or a new threat is identified. Updating the risk register allows the organization to monitor the current status of risks and the effectiveness of risk responses. Therefore, the next course of action after implementing changes to close an identifiedvulnerability is to update the risk register with the new information. References = CRISC Review Manual1, page 191.
An organization is planning to outsource its payroll function to an external service provider Which of the following should be the MOST important consideration when selecting the provider?
Disaster recovery plan (DRP) of the system
Right to audit the provider
Internal controls to ensure data privacy
Transparency of key performance indicators (KPIs)
The most important consideration when selecting an external service provider for outsourcing the payroll function is the internal controls to ensure data privacy. The payroll function involves processing and storingsensitive personal and financial information of the employees, such as salaries, taxes, benefits, bank accounts, etc. This information needs to be protected from unauthorized access, disclosure, modification, or loss, as it may result in legal, regulatory, reputational, or financial consequences for the organization and the employees. Therefore, the external service provider should have adequate internal controls, such as encryption, access control, backup, logging, monitoring, etc., to ensure data privacy and compliance with the organization’s policies and standards. Disaster recovery plan, right to audit, and transparency ofKPIs are also important considerations when selecting an external service provider, but they are not as important as internal controls to ensure data privacy. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.2.1.2, page 2461
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 648.
Which of the following will BEST help to ensure new IT policies address the enterprise ' s requirements?
involve IT leadership in the policy development process
Require business users to sign acknowledgment of the poises
involve business owners in the pokey development process
Provide policy owners with greater enforcement authority
To ensure that new IT policies address the enterprise’s requirements, it is important to involve the business owners who are the primary stakeholders of the IT services and processes. Business owners can provide valuable input on the business objectives, risks, and expectations that the IT policies should align with and support. By involving business owners in the policy development process, the IT policies will be more relevant, realistic, and acceptable to the business units. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.3: IT Risk Scenarios, page 23.
Which of the following is MOST important to communicate to senior management during the initial implementation of a risk management program?
Regulatory compliance
Risk ownership
Best practices
Desired risk level
The most important factor to communicate to senior management during the initial implementation of a risk management program is the desired risk level, which is the level of risk that the organization aims to achieve in order to fulfill its objectives and strategy1. The desired risk level can help to:
Define and communicate the risk appetite and tolerance, which are the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives2.
Guide and align the risk identification, analysis, evaluation, and treatment processes, and ensure that the risks are consistent and proportional to the desired risk level3.
Measure and monitor the risk performance and outcome, and ensure that the actual risk level is within the desired risk level, or take corrective actions if needed4.
The other factors are not the most important to communicate to senior management, because:
Regulatory compliance is a necessary but not sufficient factor to communicate to senior management, as it ensures that the risk management program complies with the applicable laws, rules, or standards that govern the organization’s activities and operations5. However, regulatory compliance does not guarantee that the risk management program is relevant and useful for the organization’s specific objectives and strategy.
Risk ownership is a desirable but not essential factor to communicate to senior management, as it assigns the roles and responsibilities for managing the risks and implementing the risk responses to the appropriate individuals or entities within the organization. However, risk ownership does not ensure that the risk management program is effective and efficient in achieving the desired risk level.
Best practices are a useful but not critical factor to communicate to senior management, as they provide the guidelines and standards for designing and implementing the risk management program, based on the experience and knowledge of the industry or the profession. However, best practices do not ensure that the risk management program is suitable and feasible for the organization’s specific context and capabilities.
References =
Desired Risk Level - CIO Wiki
Risk Appetite and Tolerance - CIO Wiki
Risk Management Process - CIO Wiki
Risk Monitoring - CIO Wiki
Regulatory Compliance - CIO Wiki
[Risk Ownership - CIO Wiki]
[Best Practice - CIO Wiki]
[Risk Management - CIO Wiki]
Which of the following is the MAIN reason for documenting the performance of controls?
Obtaining management sign-off
Demonstrating effective risk mitigation
Justifying return on investment
Providing accurate risk reporting
The main reason for documenting the performance of controls is to provide accurate risk reporting. Risk reporting is a process that communicates and discloses the relevant and reliable information about the risks and their management to the stakeholders and decision makers. Risk reporting is an essential component of the risk management process, as it helps to monitor and evaluate the effectiveness and efficiency of the risk identification, assessment, response, and monitoring activities, as well as to support and inform the risk governance and oversight functions. Documenting the performance of controls is a technique that records and tracks the results and outcomes of the controls that are implemented to address the risks, such as the control objectives,
Which of the following situations reflects residual risk?
Risk that is present before risk acceptance has been finalized
Risk that is removed after a risk acceptance has been finalized
Risk that is present before mitigation controls have been applied
Risk that remains after mitigation controls have been applied
Residual riskrefers to the risk that remains after mitigation measures have been applied. It represents the exposure that an organization decides to accept, transfer, or further address, aligning with its risk appetite and tolerance.
Which of the following should be determined FIRST when a new security vulnerability is made public?
How severe the vulnerability is across the industry
Whether the affected technology is internet-facing
Whether the affected technology is used within the organization
What mitigating controls are currently in place
The very first action in vulnerability management is confirmingwhether the affected technology exists in the organization’s environment.
CRISC notes:
“Before prioritizing or mitigating, it is critical to determine whether the enterprise uses the affected asset or service.”
If the organization isnot usingthe affected technology, no further response is required.
After that, severity and mitigating controls are reviewed.
Hence,Cis correct.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Vulnerability and Asset Validation.
Which of the following is a detective control?
Limit check
Periodic access review
Access control software
Rerun procedures
A detective control is a type of internal control that seeks to uncover problems in a company’s processes once they have occurred. Examples of detective controls include physical inventory checks, reviews of account reports and reconciliations, as well as assessments of current controls1. A periodic access review is a detective control that involves verifying the access rightsand privileges of users to ensure that they are appropriate and authorized. A periodic access review can help to detect any unauthorized or inappropriate access, such as excessive or redundant permissions, segregation of duties violations, or dormant ororphaned accounts23. The other options are not detective controls, but rather preventive controls, which are designed to prevent errors or fraud from occurring in the first place. A limit check is a preventive control that validates the input data against a predefined range or limit, and rejects any data that falls outside the acceptable range4. Access control software is a preventive control that restricts the access to information systems or resources based on the identity, role, or credentials of the user5. Rerun procedures are preventive controls that ensure the accuracy and completeness of data processing by repeating the same process and comparing the results6. References = Detective Control: Definition, Examples, Vs. Preventive Control; Detective Control - What Is It, Examples, Vs Preventive Control; Limit Check - an overview |ScienceDirect Topics; Access Control Software - an overview | ScienceDirect Topics; Rerun Procedures - an overview | ScienceDirect Topics
Which of the following is the MAIN benefit to an organization using key risk indicators (KRIs)?
KRIs assist in the preparation of the organization ' s risk profile.
KRIs signal that a change in the control environment has occurred.
KRIs provide a basis to set the risk appetite for an organization
KRIs provide an early warning that a risk threshold is about to be reached.
The main benefit of using key risk indicators (KRIs) for an organization is that they provide an early warning that a risk threshold is about to be reached. KRIs are metrics that measure the likelihood and impact of risks, and help monitor and prioritize the most critical risks. KRIs also help to trigger timely and appropriate risk responses, before the risk becomes unmanageable or unacceptable. The other options are not the main benefit of using KRIs, although they may be secondary benefits or outcomes. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.1, page 4-36.
A compensating control is MOST appropriate when:
Management wants to increase the number of controls.
A vulnerability is identified.
Existing controls are inadequate.
A key control is already in place and operating effectively.
A compensating control addresses risk when the primary control cannot meet the required objectives due to practical constraints.
Which of the following is the MOST important consideration for a risk practitioner when making a system implementation go-live recommendation?
Completeness of system documentation
Results of end user acceptance testing
Variances between planned and actual cost
availability of in-house resources
End user acceptance testing is a process that verifies that a system or service meets the requirements and expectations of the end users, who are the actual or potential customers or beneficiaries of the system or service. End user acceptance testing is the final stage of testing before the system or service is deployed or released to the production environment. The results of end user acceptance testing are the most important consideration for a risk practitioner when making a system implementation go-live recommendation, as they indicate the quality, functionality, usability, and reliability of the system or service from the end user perspective. The results of end user acceptance testing can help to identify and resolve any defects, errors, or issues that may affect the performance, satisfaction, or acceptance of the system or service by the end users. The results of end user acceptance testing can also help to evaluate the benefits, value, and risks of the system or service for the end users and the organization. The other options are not the most important consideration for a risk practitioner when making a system implementation go-live recommendation, although they may be relevant and useful. The completeness of system documentation is a factor that affects the maintainability, supportability, and auditability of the system or service, but it does not measure the end user experience or satisfaction. The variances between planned and actual cost is a measure of the efficiency and budget management of the system or service development or implementation, but it does not reflect the end user needs or expectations. The availability of in-house resources is a resource that supports the system or service delivery and operation, but it does not ensure the end user acceptance or approval. References = CRISC Review Manual, pages 180-1811; CRISC Review Questions, Answers & Explanations Manual, page 87
Technical controls affecting access permissions for systems should be implemented according to:
Integration testing requirements.
Separation of duties.
Configuration baselines.
Contingency scenarios.
The correct answer isBbecause technical controls affecting access permissions should be implemented according toseparation of duties. Access permissions must be structured so that no single individual has incompatible responsibilities that could enable unauthorized activity, fraud, or unapproved changes. This is a core principle of access control governance and control design.
The other options are less appropriate:
A. Integration testing requirementsrelate to testing system interactions, not the primary basis for assigning access permissions.
C. Configuration baselinesare important for standard settings, but access authorization must first align with role separation and accountability.
D. Contingency scenariosare related to continuity and recovery, not normal access permission design.
Exact Extracts supporting the answer:
“The PRIMARY reason that an enterprise would establish segregation of duties controls is to prevent errors or fraudulent activity on high-risk transactions.”
“The MOST effective control to prevent segregation of duties violations is implementing role-based access.”
“To ensure that developers do not have access to implement changes to production applications an enterprise must have segregation of duties between application development and operations.”
“The control a risk practitioner would recommend is segregation of duties” when personnel can both change system configuration settings and modify logs.
These extracts show that access permissions and technical access controls should be aligned withseparation of dutiesto prevent misuse and reduce risk.
===========
Which of the following would be MOST helpful to a risk practitioner when preparing a summary of current IT risk for senior management review?
Changes in risk mitigation plans
Resolution status of audit findings
Areas of elevated risk
Industry risk management benchmarks
Senior management requireshigh-level, decision-relevantinformation. CRISC guidance states that the most valuable elements to communicate areareas of elevated risk, because these represent conditions that may exceed risk appetite or require immediate action. Changes in mitigation plans and audit findings are important operational details but do not provide a clear picture of current exposure. Industry benchmarks offer context but do not describe the organization’s actual risk posture. Highlighting elevated risks helps executives prioritize resources, make treatment decisions, and determine whether escalations are required.
Which of the following is the GREATEST concern associated with redundant data in an organization ' s inventory system?
Poor access control
Unnecessary data storage usage
Data inconsistency
Unnecessary costs of program changes
Data inconsistency is the greatest concern associated with redundant data in an organization’s inventory system, as it can lead to inaccurate, unreliable, and conflicting information that can affect the decision-making and performance of the organization. Redundant data can occur when the same data is stored in multiple locations or formats, or when data is not updated or synchronized properly. Data inconsistency can cause errors, confusion, and inefficiency in the inventory management process, and can also increase the risk of fraud, theft, or loss of inventory. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 238. CRISC by Isaca Actual Free Exam Q & As, Question 9. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 238. CRISC Sample Questions 2024, Question 238.
Which of the following is the MOST important step to ensure regulatory requirements are adequately addressed within an organization?
Obtain necessary resources to address regulatory requirements
Develop a policy framework that addresses regulatory requirements
Perform a gap analysis against regulatory requirements.
Employ IT solutions that meet regulatory requirements.
The most important step to ensure regulatory requirements are adequately addressed within an organization is to develop a policy framework that addresses regulatory requirements. A policy framework is a set of principles, rules, and standards that guide the organization’s actions and decisions. By developing a policy framework that addresses regulatory requirements, the organization can establish a clear and consistent direction, expectation, and accountability for complying with the relevant laws and regulations. Obtaining necessary resources, performing a gap analysis, and employing IT solutions are other possible steps, but they are not as important as developing a policy framework. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 4; CRISC Review Manual, 6th Edition, page 153.
Which process is MOST effective to determine relevance of threats for risk scenarios?
Vulnerability assessment
Business impact analysis (BIA)
Penetration testing
Root cause analysis
A vulnerability assessment is a process that identifies and quantifies vulnerabilities in a system. It is the most effective process to determine the relevance of threats for risk scenarios as it helps in identifying potential security threats and vulnerabilities, quantifying the seriousness of each, and prioritizing techniques to mitigate attack and protect IT resources1.
References
2Identifying and Estimating Cybersecurity Risk for Enterprise Risk Management
3Threat Modeling Process | OWASP Foundation
1Threat modeling explained: A process for anticipating cyber attacks
4Hazard Identification and Risk Assessment: A Guide - SafetyCulture
5How to Write Strong Risk Scenarios and Statements - ISACA
Which of the following should a risk practitioner do NEXT after learning that Internet of Things (loT) devices installed in the production environment lack appropriate security controls for
sensitive data?
Assess the threat and associated impact.
Evaluate risk appetite and tolerance levels
Recommend device management controls
Enable role-based access control.
Assessing the threat and associated impact is the next thing that a risk practitioner should do after learning that Internet of Things (IoT) devices installed in the production environment lack appropriate security controls for sensitive data. This is because assessing the threat and associated impact can help determine the level and nature of the risk posed by the IoT devices, as well as the potential consequences and costs of a security breach or incident. Assessing the threat and associated impact can also provide the basis for further risk analysis and response steps, such as evaluating risk appetite and tolerance levels, recommending device management controls, or enabling role-based access control. According to the CRISC Review Manual 2022, assessing the threat and associated impact is one of the key steps in the IT risk assessment process1. According to the web search results, assessing the threat and associated impact is a common and recommended practice for addressing the security risks of IoT devices
A highly regulated enterprise is developing a new risk management plan to specifically address legal and regulatory risk scenarios What should be done FIRST by IT governance to support this effort?
Request a regulatory risk reporting methodology
Require critical success factors (CSFs) for IT risks.
Establish IT-specific compliance objectives
Communicate IT key risk indicators (KRIs) and triggers
The first thing that should be done by IT governance to support the development of a new risk management plan to specifically address legal and regulatory risk scenarios is to establish IT-specific compliance objectives. Compliance objectives are the goals or targets that the organization sets to ensure that its IT activities and processes comply with the relevant laws, regulations, standards, and contracts. Compliance objectives help to define the scope, criteria, and expectations for the IT compliance program, and to align the IT compliance activities with the organization’s strategy, risk appetite, and performance measures. Compliance objectives also help to communicate and demonstrate the organization’s commitment and accountability for IT compliance to the internal and external stakeholders, such as the board, management, regulators, auditors, and customers. The other options are not the first thing that should be done, although they may be useful or necessary steps or components of the IT compliance program. Requesting a regulatory risk reporting methodology, requiring critical success factors (CSFs) for IT risks, and communicating IT key risk indicators (KRIs) and triggers are all activities that can help to implement and monitor the IT compliance program, but they require the prior definition and agreement of the IT compliance objectives. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.4.1, page 2-37.
Which of the following is MOST appropriate to prevent unauthorized retrieval of confidential information stored in a business application system?
Implement segregation of duties.
Enforce an internal data access policy.
Enforce the use of digital signatures.
Apply single sign-on for access control.
An internal data access policy is a set of rules and guidelines that define who, how, when, and why the users can access, use, share, or modify the data stored in a business application system, based on the data classification, sensitivity, and ownership.
Enforcing an internal data access policy is the most appropriate way to prevent unauthorized retrieval of confidential information stored in a business application system. This means that the organization implements and maintains effective controls to ensure that only the authorized users can access the confidential information, and that the access is logged and monitored for compliance and security purposes.
The other options are not the most appropriate ways to prevent unauthorized retrieval of confidential information stored in a business application system. They are either secondary or not essential for data access control.
The references for this answer are:
Risk IT Framework, page 28
Information Technology & Security, page 22
Risk Scenarios Starter Pack, page 20
Which of the following provides the MOST up-to-date information about the effectiveness of an organization ' s overall IT control environment?
Key performance indicators (KPIs)
Risk heat maps
Internal audit findings
Periodic penetration testing
The IT control environment is the set of standards, processes, and structures that provide the basis for carrying out IT internal control across the organization1. The IT control environment comprises the IT governance, IT policies and procedures, IT organizational structure, IT roles and responsibilities, IT competencies and training, and IT culture and ethics2. The effectiveness of the IT control environment can be measured by how well it supports the achievement of the organization’s IT objectives, such as IT reliability, security, compliance, and performance3.
One of the best ways to provide the most up-to-date information about the effectiveness of the organization’s overall IT control environment is to perform periodic penetrationtesting. Penetration testing is the process of simulating real-world cyberattacks on the organization’s IT systems, networks, and applications, to identify and exploit any vulnerabilities, weaknesses, or gaps in the IT control environment4. Penetration testing can help to:
Evaluate the current state and maturity of the IT control environment and its alignment with the organization’s risk appetite and tolerance
Detect and prioritize the most critical and urgent IT risks and threats that may compromise the organization’s IT objectives or assets
Test and validate the effectiveness and efficiency of the existing IT controls and their ability to prevent, detect, or respond to cyberattacks
Provide recommendations and feedback for improving the IT control environment and enhancing the IT security posture and resilience of the organization
References = COSO – Control Environment - Deloitte, How to use COSO to assess IT controls - Journal of Accountancy, What is Penetration Testing?, [Penetration Testing: A Guide for Business Leaders]
When of the following is the BEST key control indicator (KCI) to determine the effectiveness of en intrusion prevention system (IPS)?
Percentage of system uptime
Percentage of relevant threats mitigated
Total number of threats identified
Reaction time of the system to threats
The percentage of relevant threats mitigated is the best key control indicator (KCI) to determine the effectiveness of an intrusion prevention system (IPS), because it measures how well the IPS is performing its intended function of preventing unauthorized access or attacks. The percentageof system uptime is not a good KCI, because it does not reflect the quality or accuracy of the IPS. The total number of threats identified is not a good KCI, because it does not indicate how many of those threats were actually prevented by the IPS. The reaction time of the system to threats is not a good KCI, because it does not measure the impact or severity of the threats that were prevented or not prevented by the IPS. References = CRISC: Certified in Risk & Information Systems Control Sample Questions2
A large organization is replacing its enterprise resource planning (ERP) system and has decided not to deploy the payroll module of the new system. Instead, the current payroll system will continue to be
used. Of the following, who should own the risk if the ERP and payroll system fail to operate as expected?
The business owner
The ERP administrator
The project steering committee
The IT project manager
The business owner should own the risk if the ERP and payroll system fail to operate as expected, because the business owner is ultimately responsible for the business processes and objectives that depend on the systems. The other options are not the risk owners, because:
Option B: The ERP administrator is responsible for the technical aspects of the ERP system, but not the payroll system or the business outcomes.
Option C: The project steering committee is responsible for overseeing the project of replacing the ERP system, but not the ongoing operation and maintenance of the systems or the business risks.
Option D: The IT project manager is responsible for managing the project of replacing the ERP system, but not the payroll system or the business risks. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 90.
A risk practitioner wants to identify potential risk events that affect the continuity of a critical business process. Which of the following should the risk practitioner do FIRST?
Evaluate current risk management alignment with relevant regulations
Determine if business continuity procedures are reviewed and updated on a regular basis
Conduct a benchmarking exercise against industry peers
Review the methodology used to conduct the business impact analysis (BIA)
The risk practitioner shouldfirst review the methodology of the BIAbecause the BIA identifies critical processes and the impacts of disruptions. This ensures that any identified risks are grounded in reliable, updated business impact data.
===========
A risk assessment has revealed that the probability of a successful cybersecurity attack is increasing. The potential loss could exceed the organization ' s risk appetite. Which of the following ould be the MOST effective course of action?
Re-evaluate the organization ' s risk appetite.
Outsource the cybersecurity function.
Purchase cybersecurity insurance.
Review cybersecurity incident response procedures.
Cybersecurity incident response procedures are the plans and actions that an organization takes to respond to and recover from a cybersecurity attack. They include identifying the source and scope of the attack, containing and eradicating the threat, restoring normal operations, and analyzing the root cause and lessons learned. Reviewing cybersecurity incident response procedures is the most effective course of action when the probability of a successful cybersecurity attack is increasing and the potential loss could exceed the organization’s risk appetite, as it helps to prepare the organization for minimizing the impact and duration of the attack, as well as improving the resilience and security posture of the organization.
Which of the following BEST enforces access control for an organization that uses multiple cloud technologies?
Senior management support of cloud adoption strategies
Creation of a cloud access risk management policy
Adoption of a cloud access security broker (CASB) solution
Expansion of security information and event management (SIEM) to cloud services
A cloud access security broker (CASB) solution is the best way to enforce access control for an organization that uses multiple cloud technologies, as it provides a centralized and consistent platform to manage and monitor the access to various cloud services and applications. A CASB solution can help to implement and enforce the enterprise’s access policies and standards, as well as to detect and prevent unauthorized or malicious access attempts. Senior management support of cloud adoption strategies, creation of a cloud access risk management policy, and expansion of security information and event management (SIEM) to cloud services are not the best ways to enforce access control for an organization that uses multiple cloud technologies, as they do not provide the technical capabilities or tools to manage and monitor the access to various cloud services and applications. References = CRISC by Isaca Actual Free Exam Q & As, question 210; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 210.
Which of the following is the FIRST step in managing the risk associated with the leakage of confidential data?
Maintain and review the classified data inventor.
Implement mandatory encryption on data
Conduct an awareness program for data owners and users.
Define and implement a data classification policy
The risk associated with the leakage of confidential data is the possibility and impact of unauthorized disclosure, access, or use of sensitive information that may harm the organization or its stakeholders12.
The first step in managing the risk associated with the leakage of confidential data is to define and implement a data classification policy, which is a document that establishes the criteria, categories, roles, and responsibilities for identifying, labeling, and handling different types of data according to their sensitivity, value, and protection needs34.
Defining and implementing a data classification policy is the first step because it provides the foundation and framework for the data protection strategy, and enables the organization to prioritize and allocate the appropriate resources and controls for the most critical and confidential data34.
Defining and implementing a data classification policy is also the first step because it supports the compliance with the relevant laws and regulations, such as GDPR, HIPAA, or PCI-DSS, that require the organization to classify and protect the personal or financial data of its customers or clients34.
The other options are not the first step, but rather possible subsequent steps that may depend on or follow the data classification policy. For example:
Maintaining and reviewing the classified data inventory is a step that involves creating and updating a record of the data assets that have been classified, and verifying their accuracy and completeness over time34. However, this step is not the first step because it requires the data classification policy to provide the guidance and standards for the data inventory process34.
Implementing mandatory encryption on data is a step that involves applying a cryptographic technique that transforms the data into an unreadable format, and requires a key or a password to decrypt and access the data56. However, this step is not the first step because it requires the dataclassification policy to determine which data needs to be encrypted, and what level of encryption is appropriate56.
Conducting an awareness program for data owners and users is a step that involves educating and training the people who are responsible for or have access to the data, and informing them of their roles, obligations, and best practices for data protection78. However, this step is not the first step because it requires the data classification policy to define the data ownership and user rights, and the data protection policies and procedures78. References =
1: Top Four Damaging Consequences of Data Leakage | ZeroFox1
2: 8 Data Leak Prevention Strategies for 2023 | UpGuard2
3: Data Classification: What It Is, Why You Need It, and How to Do It3
4: Data Classification Policy Template - IT Governance USA4
5: Encryption: What It Is, How It Works, and Why You Need It5
6: Encryption Policy Template - IT Governance USA6
7: What Is Security Awareness Training and Why Is It Important? - Kaspersky7
8: Security Awareness Training - Cybersecurity Education Online | Proofpoint US8
A peer review of a risk assessment finds that a relevant threat community was not included. Mitigation of the risk will require substantial changes to a software application. Which of the following is the BEST course of action?
Ask the business to make a budget request to remediate the problem.
Build a business case to remediate the fix.
Research the types of attacks the threat can present.
Determine the impact of the missing threat.
Determining the impact of the missing threat is the best course of action for a peer review of a risk assessment, as it helps to assess the potential consequences and severity of the threat on the information system and the business objectives. Determining the impact of the missing threat is a process of estimating and quantifying the possible harm or loss that could result from the occurrence of the threat event, such as data breach, system failure, or service disruption. Determining the impact of the missing threat can help to:
Identify and prioritize the critical assets, processes, and functions that could be affected by the threat
Evaluate and measure the extent and magnitude of the damage or disruption caused by the threat
Analyze and compare the current and residual risk levels and control effectiveness
Develop and implement appropriate risk response and mitigation strategies and actions
Communicate and report the risk exposure and status to the relevant stakeholders
Determining the impact of the missing threat is an essential step to ensure the completeness and accuracy of the risk assessment and to improve the quality and reliability of the risk management and control processes.
The other options are not the best courses of action for a peer review of a risk assessment. Asking the business to make a budget request to remediate the problem is a possible action to allocate the resources and costs for the risk mitigation, but it does not address the root cause or the severity of the problem. Building a business case to remediate the fix is a possible action to justify and support the risk mitigation, but it does not provide a clear and comprehensive analysis of the problem. Researching the types of attacks the threat can present is a possible action to understand and anticipate the threat scenarios andtechniques, but it does not evaluate the actual or potential impact of the threat. References = Risk Assessment and Analysis Methods: Qualitative and Quantitative, IT Risk Resources | ISACA, Peer Review Assessment Framework
Which of the following presents the GREATEST challenge to managing an organization ' s end-user devices?
Incomplete end-user device inventory
Unsupported end-user applications
Incompatible end-user devices
Multiple end-user device models
A recent vulnerability assessment of a web-facing application revealed several weaknesses. Which of the following should be done NEXT to determine the risk exposure?
Code review
Penetration test
Gap assessment
Business impact analysis (BIA)
The next step to determine the risk exposure after a vulnerability assessment of a web-facing application is to perform a penetration test. A penetration test is a simulated attack on the application to exploit the identified vulnerabilities and measure the potential impact and likelihood of a successful breach. A penetration test can help to quantify and prioritize the risks associated with the web-facing application. Code review, gap assessment, and business impact analysis (BIA) are other possible steps, but they are not as effective as a penetration test. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Which of the following provides the MOST useful information to trace the impact of aggregated risk across an organization ' s technical environment?
Business case documentation
Organizational risk appetite statement
Enterprise architecture (EA) documentation
Organizational hierarchy
Enterprise architecture (EA) documentation provides the most useful information to trace the impact of aggregated risk across the organization’s technical environment, because it describesthe structure and behavior of the organization’s IT systems, applications, infrastructure, and processes, and how they support and enable the organization’s strategy and objectives. EA documentation also defines the principles, standards, and guidelines that govern the design and implementation of the IT solutions and services. Aggregated risk is the total or combined level of risk that the organization faces from multiple or interrelated sources or scenarios. Aggregated risk may have a greater impact than the sum of the individual risks, due to the synergistic or compounding effects of the risks. The technical environment is the set of IT components and capabilities that support the organization’s business functions and processes. Tracing the impact of aggregated risk across the technical environment is a process of identifying and assessing the potential or actual consequences of the aggregated risk on the performance, functionality, or security of the IT systems, applications, infrastructure, or processes. EA documentation provides the most useful information, as it helps to understand and analyze the interdependencies and relationships of the IT components and capabilities, andto evaluate the effect of the aggregated risk on the alignment and integration of IT with the organization’s strategy and objectives. Business case documentation, organizational risk appetite statement, and organizational hierarchy are all possible sources of information to trace the impact of aggregated risk, but they are not the most useful information, as they do not provide a comprehensive and detailed view of the technical environment and its architecture. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.1, page 183
Key risk indicators (KRIs) BEST support risk treatment when they:
Set performance expectations for controls.
Align with key business objectives.
Indicate that the risk is approaching predefined thresholds.
Articulate likelihood and impact in quantitative terms.
KRIs are most effective when they signal that a risk is nearing or exceeding predefined thresholds. This early warning enables organizations to take proactive measures to mitigate risks before they materialize into significant issues.
A risk manager has determined there is excessive risk with a particular technology. Who is the BEST person to own the unmitigated risk of the technology?
IT system owner
Chief financial officer
Chief risk officer
Business process owner
The best person to own the unmitigated risk of the technology is the IT system owner. The IT system owner is the person or entity that has the authority and responsibility for the acquisition, development, maintenance, and operation of the IT system. The IT system owner is also responsible for ensuring that the IT system meets the business requirements, security standards, and compliance obligations of the enterprise. The IT system owner should own the unmitigated risk of the technology, as they are in the best position to understand the nature and impact of the risk, and to implement the appropriate risk responses to reduce the risk exposure to an acceptable level. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.3.1, page 251234
An organization wants to grant remote access to a system containing sensitive data to an overseas third party. Which of the following should be of GREATEST concern to management?
Transborder data transfer restrictions
Differences in regional standards
Lack of monitoring over vendor activities
Lack of after-hours incident management support
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
Business continuity manager
Chief risk officer (CRO)
IT infrastructure manager
Business application owner
The business application owner is responsible for the application ' s performance and availability. Therefore, they should approve any maintenance schedules that could impact the application ' s functionality, including temporary loss of failover capabilities. Their approval ensures that the business implications are considered and that appropriate contingency plans are in place.
Who should be responsible for implementing and maintaining security controls?
End user
Internal auditor
Data owner
Data custodian
The data custodian is the person who is responsible for implementing and maintaining security controls to protect the data entrusted to them by the data owner. The data custodian is typically a system administrator or a security systems administrator who has the technical skills and access rights to manage the security systems and processes that safeguard the data. The data custodian’s responsibilities include, but are not limited to: Installing, configuring, and updating security systems such as firewalls, anti-virus software, encryption tools, etc. Monitoring network trafficand system logs to detect and respond to security incidents. Conducting regular security assessments and audits to ensure compliance with security policies and standards. Implementing backup and recovery procedures to ensure data availability and integrity. The data custodian works under the direction and guidance of the data owner, who is the person who has the authority and accountability for the data and its use. The data owner defines the data classification, the data retention period, and the data access rights and privileges. The data owner also approves any changes to the security controls or the data itself. The data owner is typically a senior manager or a business unit leader who has the business knowledge and responsibility for the data. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.3: Data Classification, pp. 11-131
Which of the following is the BEST reason to use qualitative measures to express residual risk levels related to emerging threats?
Qualitative measures require less ongoing monitoring.
Qualitative measures are better aligned to regulatory requirements.
Qualitative measures are better able to incorporate expert judgment.
Qualitative measures are easier to update.
Qualitative measures are methods of expressing risk levels using descriptive terms, such as high, medium, or low, based on subjective criteria, such as likelihood, impact, or severity. Qualitative measures are often used to identify and prioritize risks, and to communicate risk information to stakeholders1.
Residual risk is the level of risk that remains after the risk response has been implemented. Residual risk reflects the effectiveness and efficiency of the risk response, and the need for further action or monitoring2.
Emerging threats are new or evolving sources or causes of risk that have the potential to adversely affect the organization’s objectives, assets, or operations. Emerging threats are oftencharacterized by uncertainty, complexity, and ambiguity, and may require innovative or adaptive risk responses3.
The best reason to use qualitative measures to express residual risk levels related to emerging threats is that qualitative measures are better able to incorporate expert judgment. Expert judgment is the opinion or advice of a person or a group of people who have specialized knowledge, skills, or experience in a particular domain or field. Expert judgment can help to:
Provide insights and perspectives on the nature and characteristics of the emerging threats, and their possible causes and consequences
Assess the likelihood and impact of the emerging threats, and their interactions and dependencies with other risks
Evaluate the suitability and effectiveness of the risk responses, and their alignment with the organization’s risk appetite and tolerance
Identify and recommend the best practices and lessons learned for managing the emerging threats, and for improving the risk management process45
Qualitative measures are better able to incorporate expert judgment than quantitative measures, which are methods of expressing risk levels using numerical or measurable values, such as percentages, probabilities, or monetary amounts. Quantitative measures are often used to estimate and analyze risks, and to support risk decision making1. However, quantitative measures may not be suitable or feasible for expressing residual risk levels related to emerging threats, because:
Quantitative measures require reliable and sufficient data and information, which may not be available or accessible for the emerging threats
Quantitative measures rely on mathematical models and techniques, which may not be able to capture or reflect the complexity and uncertainty of the emerging threats
Quantitative measures may create a false sense of precision or accuracy, which may not be justified or warranted for the emerging threats
Quantitative measures may be influenced or manipulated by biases or assumptions, which may not be valid or appropriate for the emerging threats67
Therefore, qualitative measures are better able to incorporate expert judgment, which can enhance the understanding and management of the residual risk levels related to emerging threats.
The other options are not the best reasons to use qualitative measures to express residual risk levels related to emerging threats, but rather some of the advantages or disadvantages of qualitative measures. Qualitative measures require less ongoing monitoring than quantitative measures, because they are simpler and easier to apply and update. However, this does not mean that qualitative measures can eliminate or reduce the need for monitoring, which is an essential part of the risk management process. Qualitative measures are better aligned to regulatory requirements than quantitative measures, because they are more consistent and comparable across different domains and contexts. However, this does not mean that qualitative measures can satisfy or comply with all the regulatory requirements, which may vary depending on theindustry or sector. Qualitative measures are easier to update than quantitative measures, because they do not depend on complex calculations or formulas. However, this does not mean that qualitative measures can always reflect the current or accurate risk levels, which may change over time or due to external factors. References =
Qualitative Risk Analysis vs. Quantitative Risk Analysis - ISACA
Residual Risk - ISACA
Emerging Threats - ISACA
Expert Judgment - ISACA
Expert Judgment in Project Management: Narrowing the Theory-Practice Gap
Quantitative Risk Analysis - ISACA
Quantitative Risk Analysis: A Critical Review
[CRISC Review Manual, 7th Edition]
When reporting to senior management on changes in trends related to IT risk, which of the following is MOST important?
Materiality
Confidentiality
Maturity
Transparency
The most important factor when reporting to senior management on changes in trends related to IT risk is materiality. Materiality is the extent to which the information reported is significant, relevant, and useful for decision-making purposes. Materiality helps to prioritize the most important risks and communicate them effectively to senior management12
1: Integrating KRIs and KPIs for Effective Technology Risk Management - ISACA 2: CRISC Review Manual, 7th Edition, page 271
Which of the following functions independently reviews and provides feedback regarding the achievement of organizational objectives?
Risk management
Internal audit
IT governance
Senior leadership
Internal auditis thethird line of defense, providingindependent assuranceregarding risk management, controls, and governance effectiveness.
According to CRISC and the Three Lines Model:
“Internal audit independently reviews risk management processes and provides feedback on the achievement of objectives.”
Risk management (second line) monitors, not audits. Senior leadership (first line) executes strategy. Thus,Bis correct.
CRISC Reference:Domain 1 – IT Risk Governance, Topic: Three Lines Model Roles.
Which of the following BEST helps to mitigate risk associated with excessive access by authorized users?
Monitoring user activity using security logs
Revoking access for users changing roles
Granting access based on least privilege
Conducting periodic reviews of authorizations granted
The principle of least privilege is a key concept in information security that aims to provide users with the minimum level of access—or permissions—necessary to perform their job functions. Byensuring that users only have the access they need, organizations can significantly reduce the risk associated with excessive access by authorized users.
Understanding Least Privilege
The principle of least privilege restricts access rights for users to the bare minimum permissions they need to perform their work. This minimizes the potential damage from accidents or malicious activities.
Least privilege should be applied to all user accounts, including administrative and service accounts.
Implementation
Implementing least privilege involves a detailed analysis of job functions and the necessary access required for each role.
Regularly review and update access permissions to ensure they remain aligned with current job responsibilities and organizational needs.
Mitigating Risk
By limiting access to only what is necessary, organizations can prevent users from having permissions that could be exploited, intentionally or unintentionally, to cause harm.
This also includes revoking unnecessary privileges when users change roles or no longer need access.
Comparison with Other Options
A. Monitoring user activity using security logs: While monitoring can detect inappropriate activity, it does not prevent it.
B. Revoking access for users changing roles: This is a necessary practice but does not address the initial allocation of excessive privileges.
D. Conducting periodic reviews of authorizations granted: Periodic reviews are important but are reactive rather than proactive.
References
Sybex-CISSP-Official-Study-Guide-9-Edition.pdf, p. 641, discussing the principle of least privilege and its implementation.
Which of the following roles would be MOST helpful in providing a high-level view of risk related to customer data loss?
Customer database manager
Customer data custodian
Data privacy officer
Audit committee
A data privacy officer is a role that is responsible for ensuring that the organization complies with the applicable laws, regulations, and standards regarding the collection, processing, storage, and disclosure of customer data1. A data privacy officer is also responsible for developing and implementing policies, procedures, and controls to protect the privacy and security of customer data, and to prevent or mitigate the risk of customer data loss2. A data privacy officer is the most helpful role in providing a high-level view of risk related to customer data loss, because:
A data privacy officer has the knowledge and expertise of the legal and ethical requirements and best practices for customer data protection, and can identify and assess the potential threats and vulnerabilities that may compromise customer data3.
A data privacy officer has the authority and accountability to oversee and monitor the customer data lifecycle, and to ensure that the organization follows the principles of data minimization, purpose limitation, accuracy, integrity, confidentiality, and accountability4.
A data privacy officer has the visibility and communication skills to report and advise the management and other stakeholders on the customer data risk profile, and to recommend and implement appropriate risk responses and improvement actions5.
The other options are not the most helpful roles in providing a high-level view of risk related to customer data loss, because:
A customer database manager is a role that is responsible for designing, developing, maintaining, and optimizing the database systems that store and manage customer data6. A customer database manager may have some technical skills and knowledge to protect the customer data from unauthorized access, modification, or deletion, but may not have the comprehensive or holistic view of the customer data risk, as they may focus only on the database level, and not on the organizational or regulatory level.
A customer data custodian is a role that is responsible for handling, processing, and storing customer data according to the instructions and permissions of the data owner7. A customer data custodian may have some operational duties and responsibilities to safeguard the customer data from accidental or intentional loss, damage, or disclosure, but may not have the strategic or analyticalview of the customer data risk, as they may follow only the predefined rules and procedures, and not the risk management principles and practices.
An audit committee is a group of independent directors or members that is responsible for overseeing and evaluating the organization’s financial reporting, internal control, and auditfunctions. An audit committee may have some oversight and assurance roles andresponsibilities to review and verify the organization’s compliance and performance regarding customer data protection, but may not have the direct or proactive view of the customer data risk, as they may rely only on the audit reports and findings, and not on the risk assessment and analysis.
References =
Data Privacy Officer - CIO Wiki
What is a Data Protection Officer (DPO)? - Definition from Techopedia
Data Privacy Officer: Roles and Responsibilities - ISACA
Data Protection Principles - CIO Wiki
Data Privacy Officer: How to Be One and Why You Need One - ISACA
Database Manager - CIO Wiki
Data Custodian - CIO Wiki
[Audit Committee - CIO Wiki]
Which of the following is MOST important to update when an organization ' s risk appetite changes?
Key risk indicators (KRIs)
Risk reporting methodology
Key performance indicators (KPIs)
Risk taxonomy
The most important element to update when an organization’s risk appetite changes is the key risk indicators (KRIs). KRIs are metrics that provide an early warning of increasing risk exposure in various areas of the organization. They help to monitor the level of risk and to trigger risk responses when the risk exceeds the risk appetite. The risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk reportingmethodology, key performance indicators (KPIs), and risk taxonomy are other elements that may be updated, but they are not as important as the KRIs. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 12; CRISC Review Manual, 6th Edition, page 215.
An organization ' s risk tolerance should be defined and approved by which of the following?
The chief risk officer (CRO)
The board of directors
The chief executive officer (CEO)
The chief information officer (CIO)
The organization’s risk tolerance should be defined and approved by the board of directors, as they are the highest governing body of the organization and have the ultimate responsibility and accountability for the strategic direction and oversight of the risk management process. The board of directors should establish and communicate the risk appetite and tolerance of the organization, and ensure that they are aligned with the organization’s vision, mission, values, and goals. The board of directors should also monitor and review the risk management performance and outcomes, and provide guidance and support to the management and staff. The other options are not the correct answers, as they do not have the authority or responsibility to define and approve the organization’s risk tolerance, although they may have some roles or involvement in the risk management process. The chief risk officer (CRO) is the senior executive who leads and coordinates the risk management activities across the organization, and reports to the board of directors and the chief executive officer (CEO). The CRO should advise and assist the board of directors in defining and approving the risk tolerance, but they cannot do it on their own. The chief executive officer (CEO) is thehighest-ranking manager of the organization and has the responsibility and accountability for the execution and implementation of the risk management process. The CEO should support and communicate the risk tolerance defined and approved by the board of directors, but they cannot do it on their own. The chief information officer (CIO) is the senior executive who oversees and manages the information and technology functions and resources of the organization. The CIO should ensure that the IT risks and controls are aligned with the risk tolerance defined and approved by the board of directors, but they cannot do it on their own. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, page 24.
Which of the following is the PRIMARY reason to compare the business impact analysis (BIA) against the organization ' s business continuity plan (BCP)?
The results of the BIA quantify the BCP objectives and supporting technology for each operational area.
The BCP provides detailed information on alternative facilities to use in case of business interruptions.
The results of the BIA quantify the cost of the technology environment needed to restart each operational area.
The BCP provides the backup and restoration procedures to follow in case of business interruptions.
The BIA identifies critical processes, maximum tolerable downtime, and the business impact of disruptions. CRISC and business continuity practices emphasize that the BCP must bealignedwith BIA results. Comparing the BIA with the BCP ensures that recovery strategies, objectives (RTOs/RPOs), and supporting technologies specified in the BCP actually reflect the priorities and impact levels identified in the BIA for each operational area. Alternative facilities and backup/restoration procedures are important BCP components, but theprimary reasonfor comparison is to validate that the chosen solutions and recovery targets match business requirements. The BIA does not primarily “quantify the cost of the technology environment”; cost analysis may follow but is not the core BIA purpose. Therefore, ensuring that BCP objectives and enabling technology are consistent with BIA findings is the key objective of the comparison.
Which of the following BEST enables the timely detection of changes in the security control environment?
Control self-assessment (CSA)
Log analysis
Security control reviews
Random sampling checks
Understanding the Question:
The question asks which method best enables timely detection of changes in the security control environment.
Analyzing the Options:
A. Control self-assessment (CSA):Allows for continuous monitoring and quick detection of any changes or deficiencies in controls.
B. Log analysis:Useful for detecting security incidents but not as comprehensive as CSA for overall control environment changes.
C. Security control reviews:Typically periodic and might not be as timely.
D. Random sampling checks:Not as systematic or comprehensive as CSA.
Control Self-Assessment (CSA):CSA involves regular, structured evaluations by internal staff to ensure controls are working effectively. It promotes early detection of issues by those directly responsible for the controls.
Timeliness:CSA is an ongoing process, making it more timely in identifying changes compared to periodic reviews or random checks.
Accountability for a particular risk is BEST represented in a:
risk register
risk catalog
risk scenario
RACI matrix
A RACI matrix is a tool that assigns the roles and responsibilities for each risk, such as who is responsible, accountable, consulted, and informed. A RACI matrix helps to clarify the expectations and accountabilities for each risk owner and stakeholder, and to ensure that the risk is managed and monitored effectively and efficiently.
A risk register is a document that records and tracks the identified risks, their likelihood, impact, and mitigation strategies. A risk register does not assign the accountability for each risk, but rather the ownership and response.
A risk catalog is a collection of risks that have been identified and categorized based on common attributes, such as source, type, or impact. A risk catalog does not assign the accountability for each risk, but rather the classification and description.
A risk scenario is a technique that simulates the possible outcomes of different risk events and assesses their impact on the enterprise’s objectives and operations. A risk scenario does not assign the accountability for each risk, but rather the analysis and evaluation.
Which of the following should be the PRIMARY area of focus when reporting changes to an organization ' s risk profile to executive management?
Risk management resources
Risk tolerance
Cyberattack threats
Risk trends
When a risk practitioner is building a key risk indicator (KRI) from aggregated data, it is CRITICAL that the data is derived from:
business process owners.
representative data sets.
industry benchmark data.
data automation systems.
Building Key Risk Indicators (KRIs):
KRIs are metrics used to provide an early signal of increasing risk exposure in various areas of an organization.
Importance of Representative Data Sets:
To ensure KRIs are accurate and meaningful, it is critical that the data used is representative of the entire population or relevant subset of activities being monitored.
Representative data ensures that the KRIs reflect the true state of risk and are not biased or incomplete.
Impact on KRIs:
Using representative data sets improves the reliability and validity of KRIs, enabling better risk detection and management.
It ensures that the KRIs provide a realistic view of potential risk trends and patterns.
Comparing Other Data Sources:
Business Process Owners:While they provide valuable insights, data from them alone may not be representative.
Industry Benchmark Data:Useful for comparisons but not specific to the organization’s unique context.
Data Automation Systems:Helpful for efficiency but must ensure the data is representative.
References:
The CRISC Review Manual emphasizes the importance of using representative data to build effective KRIs (CRISC Review Manual, Chapter 3: Risk Response and Mitigation, Section 3.11 Data Collection Aggregation Analysis and Validation) .
Who is accountable for authorizing application access in a cloud Software as a Service (SaaS) solution?
Cloud service provider
IT department
Senior management
Business unit owner
The business unit owner is accountable for authorizing application access in a SaaS environment because they are responsible for aligning access controls with business needs. They determine the roles and permissions needed to ensure operational effectiveness while adhering to the principle ofAccess Managementin the CRISC framework.
Which of the following is the MOST useful input when developing risk scenarios?
Common attacks in other industries
Identification of risk events
Impact on critical assets
Probability of disruptive risk events
Identifying risk events is essential for developing realistic and relevant risk scenarios. This step enables the creation of scenarios that reflect actual vulnerabilities and potential disruptions, adhering to the CRISC ' s focus onRisk Identification.
Because of a potential data breach, an organization has decided to temporarily shut down its online sales order system until sufficient controls can be implemented. Which risk treatment has been selected?
Avoidance
Acceptance
Mitigation
Transfer
Risk avoidance involves ceasing activities that expose the organization to significant risks, such as shutting down the sales order system. This decision aligns withRisk Treatment Strategiesaimed at eliminating exposure.
Which of the following describes the relationship between risk appetite and risk tolerance?
Risk appetite is completely independent of risk tolerance.
Risk tolerance is used to determine risk appetite.
Risk appetite and risk tolerance are synonymous.
Risk tolerance may exceed risk appetite.
Relationship between Risk Appetite and Risk Tolerance:
Risk Appetite: Defined as the amount of risk an organization is willing to accept in pursuit of its objectives. It is a broad measure that reflects the organization ' s strategy and goals.
Risk Tolerance: Refers to the acceptable level of variation in performance relative to achieving objectives. It is narrower and can sometimes exceed the risk appetite in specific situations where deviations are permissible.
Contextual Understanding:
Controlled Exceedance: Risk tolerance allows for occasional and controlled exceedance of the risk appetite, typically under specific conditions and for compelling business reasons.
Management Decisions: Decisions to exceed risk appetite should be carefully considered and documented, ensuring they do not threaten the overall risk capacity of the organization.
Comparison with Other Options:
Independent of Each Other: Incorrect, as risk tolerance is related to risk appetite.
Risk Tolerance Determines Risk Appetite: Incorrect, risk appetite is generally broader and set before determining risk tolerance.
Synonymous: Incorrect, they are distinct concepts with risk tolerance providing operational flexibility within the boundaries set by risk appetite.
Best Practices:
Clear Definitions: Clearly define and communicate the organization’s risk appetite and risk tolerance.
Regular Reviews: Regularly review and adjust risk appetite and tolerance to align with changes in business strategy and external environment.
An organization has recently hired a large number of part-time employees. During the annual audit, it was discovered that many user IDs and passwords were documented in procedure manuals for use by the part-time employees. Which of the following BEST describes this situation?
Threat
Risk
Vulnerability
Policy violation
Documenting user IDs and passwords in procedure manuals is a vulnerability that exposes the organization to unauthorized access, data breaches, and other security risks. A vulnerability is a weakness or flaw in a system, process, or control that can be exploited by a threat. A threat is a potential cause of an unwanted incident that may harm the system or organization. A risk is the combination of the likelihood and impact of a threat exploiting a vulnerability. A policy violation is an act of non-compliance with a rule or standard that is established by the organization. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 67.
Which of the following is the PRIMARY reason to update a risk register with risk assessment results?
To communicate the level and priority of assessed risk to management
To provide a comprehensive inventory of risk across the organization
To assign a risk owner to manage the risk
To enable the creation of action plans to address nsk
The primary reason to update a risk register with risk assessment results is to communicate the level and priority of assessed risk to management, as this enables them to make informed decisions about risk response and allocation of resources. The risk register is a tool for documenting and reporting the current status of risks, their causes, impacts, likelihood, and responses. Updating the risk register with risk assessment results ensures that the information is accurate, relevant, and timely. The risk register also helps to monitor and track the progress and effectiveness of risk management activities. The other options are not the primary reasons to update the risk register, although they may be secondary benefits or outcomes of doing so. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Assessment, page 109.
Which of the following is MOST helpful when determining whether a system security control is effective?
Control standard operating procedures
Latest security assessment
Current security threat report
Updated risk register
Thelatest security assessmentprovides a detailed evaluation of the control’s performance and identifies gaps or weaknesses. This is critical for determining the effectiveness of a system security control in mitigating threats.
The BEST way to test the operational effectiveness of a data backup procedure is to:
conduct an audit of files stored offsite.
interview employees to compare actual with expected procedures.
inspect a selection of audit trails and backup logs.
demonstrate a successful recovery from backup files.
The best way to test the operational effectiveness of a data backup procedure is to perform a complete restoration of every file to a clean system and verify that there has not been any data corruption or loss. This will ensure that the backup procedure can successfully recover the data in the event of a disaster or incident. The other options are not sufficient to test the operational effectiveness of a data backup procedure, as they do not involve actually restoring the data and verifying its integrity and usability. References = How to review and test backup procedures to ensure data restoration; HOW TO TEST DATA BACKUPS: A BRIEF GUIDE; How to Test a Database Backup
An incentive program is MOST likely implemented to manage the risk associated with loss of which organizational asset?
Employees
Data
Reputation
Customer lists
An incentive program is most likely implemented to manage the risk associated with loss of employees, as it aims to motivate, retain, and reward the employees who have valuable skills, knowledge, and experience, and to reduce the risk of employee turnover, dissatisfaction, or underperformance. Data, reputation, and customer lists are not the organizational assets that are most likely managed by an incentive program, as they are more related to the information, image, or relationship of the organization, respectively, rather than the human capital of the organization. References = CRISC Review Manual, 7th Edition, page 100.
Which of the following is the BEST metric to demonstrate the effectiveness of an organization’s software testing program?
Average time to complete software test cases
Percentage of applications with defined business cases
Number of incidents resulting from software changes
Percentage of staff completing software development training
CRISC states that an effective software testing program reduces the number of defects that reach production. Therefore, thenumber of incidents caused by software changesis the strongest outcome-based measure of testing effectiveness. Time to complete test cases reflects efficiency, not effectiveness. Business cases for applications and staff training are not indicators of testing quality. A low number of production incidents demonstrates that testing is detecting and eliminating issues before deployment.
Which of the following is MOST helpful in reducing the likelihood of inaccurate risk assessment results?
Involving relevant stakeholders in the risk assessment process
Updating organizational risk tolerance levels
Reviewing the applicable risk assessment methodologies
Having internal audit validate control effectiveness
Involving stakeholders ensures all perspectives are considered, leading to more accurate risk identification, assessment, and prioritization.
An organization is participating in an industry benchmarking study that involves providing customer transaction records for analysis Which of the following is the MOST important control to ensure the privacy of customer information?
Nondisclosure agreements (NDAs)
Data anonymization
Data cleansing
Data encryption
Data anonymization is the most important control to ensure the privacy of customer information when participating in an industry benchmarking study that involves providing customer transaction records for analysis. Data anonymization is the process of removing or modifying personally identifiable information (PII) from data sets, such as names, addresses, phone numbers, email addresses, etc., so that the data cannot be traced back to specific individuals.Data anonymization protects the confidentiality and privacy of customers, while still allowing for meaningful analysis and comparison of data. Nondisclosure agreements (NDAs), data cleansing, and data encryption are also useful controls, but they do not eliminate the risk of data breaches or unauthorized access to PII. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.1, page 3-21.
The BEST key performance indicator (KPI) to measure the effectiveness of the security patching process is the percentage of patches installed:
by the security administration team.
successfully within the expected time frame.
successfully during the first attempt.
without causing an unplanned system outage.
The best key performance indicator (KPI) to measure the effectiveness of the security patching process is the percentage of patches installed successfully within the expected time frame. This KPI can help to evaluate how well the security patching process meets the predefined objectives and standards, and how timely the patches are applied to reduce the risk exposure. The percentage of patches installed by the security administration team, successfully during the first attempt, or without causing an unplanned system outage are other possible KPIs, but they are not as relevant as the percentage of patches installed successfully within the expected time frame. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
What is the MOST important consideration when aligning IT risk management with the enterprise risk management (ERM) framework?
Risk and control ownership
Senior management participation
Business unit support
Risk nomenclature and taxonomy
According to the CRISC Review Manual1, risk nomenclature and taxonomy is the set of terms and definitions that are used to describe and classify risks and their attributes. Risk nomenclature and taxonomy is the most important consideration when aligning IT risk management with the enterprise risk management (ERM) framework, as it helps to ensure a common and consistent understanding and communication of risks across the organization. Risk nomenclature and taxonomy also helps to integrate and harmonize the IT risk management processes and activities with the ERM framework, and to facilitatethe aggregation and reporting of risks at different levels of the organization. References = CRISC Review Manual1, page 197.
Which of the following BEST facilitates the development of effective IT risk scenarios?
Utilization of a cross-functional team
Participation by IT subject matter experts
Integration of contingency planning
Validation by senior management
The best way to facilitate the development of effective IT risk scenarios is to utilize a cross-functional team. A cross-functional team is a group of people with different skills, expertise, and perspectives who work together to achieve a common goal. A cross-functional team can help to create realistic, comprehensive, and relevant IT risk scenarios by bringing diverse knowledge, experience, and insights from various domains and functions. A cross-functional team can alsohelp to identify and address the interdependencies, interactions, and impacts of IT risks across the organization. The other options are not the best ways to facilitate the development of effective IT risk scenarios, although they may be useful or necessary depending on the context and nature of the IT risks. Participation by IT subject matter experts is important, but it is notsufficient, as IT risks may affect or be affected by non-IT factors and stakeholders. Integration of contingency planning is a part of the risk response process, which follows the risk scenario development process, but it is not the same as creating the risk scenarios. Validation by senior management is a quality assurance step that ensures the accuracy and completeness of the risk scenarios, but it is not the same as facilitating the development of the risk scenarios. References = Six Steps to Using Risk Scenarios for Improved Risk Management, IT Risk Scenarios - Morland-Austin, IT Risk Resources | ISACA
A risk practitioner wants to identify potential risk events that affect the continuity of a critical business process. Which of the following should the risk practitioner do FIRST?
Evaluate current risk management alignment with relevant regulations.
Determine if business continuity procedures are reviewed and updated on a regular basis.
Review the methodology used to conduct the business impact analysis (BIA).
Conduct a benchmarking exercise against industry peers.
Reviewing the methodology used to conduct the business impact analysis (BIA) is the first thing that a risk practitioner should do when wanting to identify potential risk events that affect the continuity of a critical business process, because it helps to ensure that the BIA is conducted in a consistent, comprehensive, and reliable manner, and that it covers all the relevant aspects and scenarios of the business process and its continuity. A BIA is a process of analyzing the potential impact of disruption to the critical business functions or processes, and identifying the recovery priorities and requirements. A BIA methodology is a set of principles, standards, and techniques that guide and support the BIA process, such as the scope, objectives, data sources, data collection methods, data analysis methods, and reporting methods. Reviewing the BIA methodology is the first thing to do, as it helps to establish the foundation and framework for the BIA process, and to ensure that the BIA results are valid and useful for identifying the potential risk events and their consequences. Evaluating current risk management alignment with relevant regulations, determining if business continuity proceduresare reviewed and updated on a regular basis, and conducting a benchmarking exercise against industry peers are all possible things to do after reviewing the BIA methodology, but they are not the first thing to do, as they depend on the quality and accuracy of the BIA process and outcomes. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 143
A service provider is managing a client’s servers. During an audit of the service, a noncompliant control is discovered that will not be resolved before the next audit because the client cannot afford the downtime required to correct the issue. The service provider’s MOST appropriate action would be to:
develop a risk remediation plan overriding the client ' s decision
make a note for this item in the next audit explaining the situation
insist that the remediation occur for the benefit of other customers
ask the client to document the formal risk acceptance for the provider
A noncompliant control is a control that does not meet the requirements or standards of an audit, regulation, or policy. A noncompliant control can expose the organization to risks such as errors, fraud, or breaches. When a noncompliant control is identified, the service provider and the client should work together to resolve the issue as soon as possible. However, sometimes the resolution may not be feasible or cost-effective, and the client may decide to accept the risk associated with the noncompliant control.
In this case, the service provider’s most appropriate action would be to ask the client to document the formal risk acceptance for the provider. This means that the client should acknowledge the existence and consequences of the noncompliant control, and provide a written justification for accepting the risk. The risk acceptance document should also specify the roles and responsibilities of the service provider and the client, and the duration and conditions of the risk acceptance. The risk acceptance document should be signed by the client’s senior management and the service provider’s management, and kept as part of the audit evidence.
The other options are not appropriate actions for the service provider. Developing a risk remediation plan overriding the client’s decision would be disrespectful and unprofessional, as it would ignore the client’s authority and preference. Making a note for this item in the next audit explaining the situation would be insufficient and misleading, as it would imply that the issue is still unresolved and that the service provider is responsible for it. Insisting that the remediation occur for the benefit of other customers would be unreasonable and impractical, as it woulddisregard the client’s business needs and constraints, and potentially harm the relationship between the service provider and the client. References =
Risk Acceptance - Institute of Internal Auditors
New Guidance on the Evaluation of Non-compliance with the Risk Assessment Standard and its Peer Review Impact - REVISED
The Impact of Non-compliance: Understanding The Risks And Consequences
Which of the following is MOST helpful in providing a high-level overview of current IT risk severity*?
Risk mitigation plans
heat map
Risk appetite statement
Key risk indicators (KRls)
A heat map is a graphical tool that displays the level of risk severity for various risk scenarios or categories using different colors, shapes, or sizes. A heat map is most helpful in providing a high-level overview of current IT risk severity, as it can show the relative importance and urgency of the risks, and highlight the areas that require attention or action. A heat map can also help to communicate the risk information to the stakeholders, and facilitate the risk prioritization and decision making. References = 5
Which of the following will BEST help an organization select a recovery strategy for critical systems?
Review the business impact analysis.
Create a business continuity plan.
Analyze previous disaster recovery reports.
Conduct a root cause analysis.
According to the CRISC Review Manual (Digital Version), reviewing the business impact analysis (BIA) will best help an organization select a recovery strategy for critical systems, as it provides an assessment of the potential impact and consequences of a disruption to the organization’s critical business functions and processes. Reviewing the BIA helps to:
Identify and prioritize the critical systems and their dependencies that support the critical business functions and processes
Estimate the maximum tolerable downtime (MTD) and the recovery time objective (RTO) for each critical system
Evaluate the feasibility and cost-effectiveness of various recovery strategies and options for each critical system
Select the most appropriate recovery strategy and option for each critical system based on the organization’s objectives and requirements
Develop and implement the recovery plan and procedures for each critical system
References = CRISC Review Manual (Digital Version), Chapter 3: IT Risk Response, Section 3.3: Risk Response Options, pp. 174-1751
A risk practitioner ' s BEST guidance to help an organization develop relevant risk scenarios is to ensure the scenarios are:
Aligned with risk management capabilities.
Based on industry trends.
Related to probable events.
Mapped to incident response plans.
Risk scenarios should reflect probable events to ensure relevance and practicality in risk assessments. This guidance supports theRisk Identification and Scenario Developmentprocess.
An upward trend in which of the following metrics should be of MOST concern?
Number of business change management requests
Number of revisions to security policy
Number of security policy exceptions approved
Number of changes to firewall rules
A security policy exception is a deviation from the established security policy that is granted to an individual or a group for a specific purpose or period of time. A security policy exception may be necessary when the security policy is too restrictive, outdated, or incompatible with the business requirements or objectives. However, a security policy exception also introduces a risk to the organization, as it may weaken the security posture, expose the organization to threats orvulnerabilities, or violate the compliance or regulatory obligations. Therefore, an upward trend in the number of security policy exceptions approved should be of most concern, as it indicates that the security policy is not effective or aligned with the organization’s needs and goals, and that the organization is accepting more risk than desired. The other options are not as concerning as the number of security policy exceptions approved, because they do not imply a direct or immediate risk to the organization, but rather reflect the normal or expected activities of the security management process, as explained below:
A. Number of business change management requests is a metric that measures the volume and frequency of the requests to modify the business processes, systems, or functions. An upward trend in this metric may indicate that the organization is undergoing a transformation, innovation, or improvement, which may have positive or negative impacts on the organization’s performance and security. However, this metric does not necessarily imply a risk to the organization, as the change management requests may be properly assessed, approved, and implemented, following the established change management procedures and controls.
B. Number of revisions to security policy is a metric that measures the amount and extent of the changes made to the security policy over time. An upward trend in this metric may indicate that the security policy is being updated, refined, or enhanced, which may improve or maintain the security posture and compliance of the organization. However, this metric does not necessarily imply a risk to the organization, as the revisions to the security policy may be based on the best practices, standards, and expectations for security management, and may be communicated and enforced effectively across the organization.
D. Number of changes to firewall rules is a metric that measures the number and type of the modifications made to the firewall configuration, which controls the incoming and outgoing network traffic based on predefined rules. An upward trend in this metric may indicate that the firewall is being adjusted, optimized, or customized, which may increase or decrease the firewall performance and security. However, this metric does not necessarily imply a risk to the organization, as the changes to the firewall rules may be justified, authorized, and validated,following the established firewall management procedures and controls. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 115. Security Policy Exceptions: What Are They and How to Manage Them, Security Policy Exceptions: How to Handle Them in a Secure Manner, Security Policy Exceptions: A Necessary Evil?
Which of the following will BEST help to ensure the continued effectiveness of the IT risk management function within an organization experiencing high employee turnover?
Well documented policies and procedures
Risk and issue tracking
An IT strategy committee
Change and release management
The best way to ensure the continued effectiveness of the IT risk management function within an organization experiencing high employee turnover is to have well documented policies and procedures. Policies and procedures are the formal documents that define the roles, responsibilities, processes, and standards for the IT risk management function. They provide guidance, consistency, and continuity for the IT risk management activities and outcomes. They also facilitate the knowledge transfer, training, and performance evaluation of the IT risk management staff. The other options are not as helpful as well documented policies and procedures, as they are related to the tools, mechanisms, or structures that support the IT risk management function, not the foundation and direction of the IT risk managementfunction. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.1: IT Risk Management Process, page 15.
Following the implementation of an Internet of Things (loT) solution, a risk practitioner identifies new risk factors with impact to existing controls. Which of the following is MOST important to include in a report to stakeholders?
Identified vulnerabilities
Business managers ' concerns
Changes to residual risk
Risk strategies of peer organizations
An organization is conducting a review of emerging risk. Which of the following is the BEST input for this exercise?
Audit reports
Industry benchmarks
Financial forecasts
Annual threat reports
The best input for conducting a review of emerging risk is the annual threat reports. Emerging risk is the risk that arises from new or evolving sources, or from existing sources that have not been previously considered or recognized. Emerging risk may have significant impact on the organization’s objectives, strategies, operations, or reputation, and may require new or different risk responses. Annual threat reports are the reports that provide information and analysis on the current and future trends, developments, and challenges in the threat landscape, such as cyberattacks, natural disasters, geopolitical conflicts, or pandemics. Annual threat reports can help to identify and assess the emerging risk, as they can provide insights into the sources, drivers, indicators, and scenarios of the emerging risk, as well as the potential impact and likelihood of the emerging risk. Annual threat reports can also help to benchmark and compare the organization’s risk exposure and preparedness with the industry and the peers, and to prioritize and respond to the emerging risk. Audit reports, industry benchmarks, and financial forecasts are not as useful as annual threat reports, as they do not focus on the emerging risk, and may not capture the latest or future changes in the threat landscape. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 50.
Which of the following is a specific concern related to machine learning algorithms?
Low software quality
Lack of access controls
Data breaches
Data bias
Data biasin machine learning algorithms can lead to inaccurate predictions or decisions, as biases in training data are amplified in the output. Addressing bias is essential for ethical and reliable algorithm performance.
Which of the following is the MOST important consideration when determining the appropriate data retention period throughout the data management life cycle?
Data storage and collection methods
Data owner preferences
Legal and regulatory requirements
Choice of encryption algorithms
Legal and regulatory requirements are paramount when determining data retention periods. Compliance with laws such as GDPR, HIPAA, or industry-specific regulations ensures that data is retained appropriately and disposed of when no longer necessary, thereby mitigating legal risks.
A newly hired risk practitioner finds that the risk register has not been updated in the past year. What is the risk practitioner ' s BEST course of action?
Identify changes in risk factors and initiate risk reviews.
Engage an external consultant to redesign the risk management process.
Outsource the process for updating the risk register.
Implement a process improvement and replace the old risk register.
The best course of action for a newly hired risk practitioner who finds that the risk register has not been updated in the past year is to identify changes in risk factors and initiate risk reviews. This would help the risk practitioner to update the risk register with the current and relevant information on the risks facing the enterprise, such as their sources, drivers, indicators, likelihood, impact, and responses. It would also help the risk practitioner to evaluate the effectiveness of the existing controls, and to identify any new or emerging risks that need to be addressed. Identifying changes in risk factors and initiating risk reviews would enable the risk practitioner to maintain the accuracy and completeness of the risk register, and to provide valuable input for the risk management process. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.1.1, page 2271
An organization uses a web application hosted by a cloud service that is populated by data sent to the vendor via email on a monthly basis. Which of the following should be the FIRST consideration when analyzing the risk associated with the application?
Whether the service provider ' s data center is located in the same country
Whether the data sent by email has been encrypted
Whether the data has been appropriately classified
Whether the service provider contract allows right of onsite audit
Data classification is the process of assigning labels or categories to data based on its sensitivity, value, and criticality to the organization. Data classification is the first consideration when analyzing the risk associated with the web application hosted by a cloud service, as it determines the level of protection and controls required for the data. Data classification can help the organization to comply with legal, regulatory, and contractual obligations, such as GDPR,CCPA, and PCI DSS, and to prevent data breaches, leaks, or losses. Data classification can also help the organization to evaluate the suitability and trustworthiness of the cloud service provider, and to negotiate the terms and conditions of the service level agreement (SLA).
Which of the following should be done FIRST upon learning that the organization will be affected by a new regulation in its industry?
Transfer the risk.
Perform a gap analysis.
Determine risk appetite for the new regulation.
Implement specific monitoring controls.
A gap analysis is the process of comparing the current state of the organization’s compliance with the new regulation and the desired state of compliance. It helps to identify the gaps or deficiencies that need to be addressed and prioritize the actions to close them. Performing a gap analysis is the first step to understand the impact of the new regulation and plan the appropriate risk response.
References
•ISACA CRISC Review Manual, 7th Edition, Domain 2: IT Risk Assessment, Section 2.2.3: Gap Analysis
•Regulatory Change: Future of Risk in the Digital Era | Deloitte US
•Gap Analysis: What It Is and How to Perform One | The Blueprint
A risk practitioner has learned that an effort to implement a risk mitigation action plan has stalled due to lack of funding. The risk practitioner should report that the associated risk has been:
mitigated
accepted
avoided
deferred
The risk practitioner should report that the associated risk has been deferred, as this means that the risk response has been postponed or delayed due to lack of resources or other constraints. Deferring a risk response implies that the risk owner acknowledges the risk and intends to implement the risk mitigation action plan at a later stage, when the resources or conditions are available. The other options are not correct, as they do not reflect the actual status of the risk response. Mitigating a risk means that the risk response has been implemented and the risk level has been reduced. Accepting a risk means that the risk response has been rejected or waived, and the risk level has been accepted as it is. Avoiding a risk means that the risk response has beenimplemented and the risk level has been eliminated or transferred. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk Response, page 146.
Who is MOST important lo include in the assessment of existing IT risk scenarios?
Technology subject matter experts
Business process owners
Business users of IT systems
Risk management consultants
Business process owners are the most important to include in the assessment of existing IT risk scenarios, as they have the authority and responsibility to manage the business processes and their associated risks and controls, and to provide the business perspective and requirements for the IT risk scenarios. Technology subject matter experts, business users of IT systems, and risk management consultants are not the most important to include, as they may have different roles and responsibilities related to the technical, operational, or advisory aspects of IT risk scenarios, respectively, but they do not own the business processes or the IT risk scenarios. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following is the PRIMARY reason to obtain independent reviews of risk assessment and response mechanisms?
To ensure risk thresholds are properly defined
To minimize the subjectivity of risk assessment results
To correct errors in the risk assessment process
To validate impact and probability ratings
The correct answer isBbecause the primary reason for obtainingindependent reviewsof risk assessment and response mechanisms is tominimize subjectivityand improve objectivity, consistency, and credibility in the assessment results. Independent reviewers help reduce bias and provide a more reliable evaluation of how risk is identified, analyzed, and responded to.
The other options are narrower or secondary outcomes:
A. To ensure risk thresholds are properly definedmay be part of a review, but it is not the primary reason.
C. To correct errors in the risk assessment processis beneficial, but independent review is broader than error correction.
D. To validate impact and probability ratingsis part of review activity, but the larger reason is reducing subjectivity and bias.
Exact Extracts supporting the answer:
“The most important reason for reviewing the risk management process by independent risk auditors and assessors is to ensure that the risk factors and risk profile are well-defined.”
“An independent risk management professional should assess whether the risk profile and risk factors are properly defined during the risk management process review.”
“Using representative and significant historical data addresses the potential for bias in developing risk scenarios.”
“A peer review is BEST suited for reviewing IT risk analysis results before sending them to management.”
“Assessments by an objective and independent third party are most relied upon by a regulatory body.”
These extracts support that independence improves objectivity and reduces bias in risk assessment and response review. Therefore, the primary reason is tominimize the subjectivity of risk assessment results.
Which of the following provides the MOST useful input to the development of realistic risk scenarios?
Balanced scorecard
Risk appetite
Risk map
Risk events
Risk events are specific occurrences or changes that have a potential impact on the achievement of objectives. They can be positive or negative, and they can be internal or external to the organization. Risk events provide the basis for developing realistic risk scenarios, which are hypothetical situations that illustrate the possible consequences of a risk event. Risk scenarios help to understand and communicate the nature, sources, and causes of risk, as well as the potential impact and likelihood of risk occurrence. Risk scenarios can also be used to test the effectiveness of risk responses and controls.
The other options are not as useful as risk events for developing realistic risk scenarios. A balanced scorecard (A) is a strategic management tool that measures the performance of the organization against its objectives, vision, and strategy. It does not provide specific information about risk events or their consequences. A risk appetite (B) is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. It does not describe the risk events or their scenarios, but rather the level of risk tolerance and acceptance. A risk map © is a graphical representation of the risk profile of the organization, showing the relationship between the likelihood and impact of different risks. It does not provide the details or context of the risk events or their scenarios, but rather the relative ranking and prioritization of risks.
A new software package that could help mitigate risk in an organization has become available. Which of the following is the risk practitioner’s BEST course of action?
Review risk governance policies
Perform a business impact analysis (BIA)
Review industry best practices
Perform a cost-benefit analysis
When evaluating new technology or tools for risk mitigation, the practitioner must ensure that the benefits justify the cost.
CRISC states:
“Risk practitioners should perform a cost-benefit analysis to determine the feasibility and value of implementing new controls or technologies.”
Governance or best practices are general references.
Thecost-benefit analysisdirectly supports decision-making and accountability.
Hence,Dis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Control Selection and Cost-Effectiveness.
The BEST indicator of the risk appetite of an organization is the
regulatory environment of the organization
risk management capability of the organization
board of directors ' response to identified risk factors
importance assigned to IT in meeting strategic goals
The board of directors’ response to identified risk factors is the best indicator of the risk appetite of an organization. The board of directors is the highest governing body of the organization, and it is responsible for setting the strategic direction, objectives, and risk appetite of the organization. The board of directors should also oversee the risk management process, and ensure that the risks are aligned with the organization’s goals and values. The board of directors’ response to identified risk factors reflects how much and what type of risk the organization is willing to pursue, retain, or take in order to achieve its objectives. The regulatory environment, the risk management capability, and the importance assigned to IT are not direct indicators of the risk appetite, although they may influence or constrain it. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.2.1, page 1-8.
During implementation of an intrusion detection system (IDS) to monitor network traffic, a high number of alerts is reported. The risk practitioner should recommend to:
reset the alert threshold based on peak traffic
analyze the traffic to minimize the false negatives
analyze the alerts to minimize the false positives
sniff the traffic using a network analyzer
An intrusion detection system (IDS) is a network security tool that monitors network traffic and devices for known malicious activity, suspicious activity or security policy violations1. An IDS can generate alerts when it detects any potential threats, but not all alerts are accurate or relevant. There are two types of errors that can affect the performance and reliability of an IDS: false positives and false negatives2.
A false positive is when an IDS incorrectly flags a benign or normal activity as malicious or suspicious. For example, an IDS may alert on a legitimate network scan or a harmless software update. False positives can reduce the credibility and efficiency of an IDS, as they can overwhelm the security team with unnecessary alerts, distract them from the real threats, and cause them to ignore or disable the IDS3.
A false negative is when an IDS fails to flag a malicious or suspicious activity as such. For example, an IDS may miss a stealthy or novel attack that does not match any known signatures or patterns. False negatives can compromise the security and integrity of the network, as they can allow attackers to bypass the IDS and cause damage or steal data without being detected4.
The risk practitioner should recommend to analyze the alerts to minimize the false positives, because this is the best way to improve the accuracy and usefulness of the IDS. By analyzing the alerts, the risk practitioner can:
Identify the sources and causes of the false positives, such as misconfigured or outdated IDS rules, network anomalies, or legitimate traffic that resembles malicious traffic5.
Adjust or fine-tune the IDS settings, such as the alert threshold, the sensitivity level, the detection method, or the rule base, to reduce the number of false positives without increasing the risk of false negatives.
Validate or verify the alerts with other sources of information, such as logs, network traffic analysis, or threat intelligence, to confirm or dismiss the alerts as true or false positives.
Prioritize or classify the alerts based on their severity, impact, or likelihood, to focus on the most critical or relevant alerts and avoid alert fatigue.
The other options are not the best course of action, because:
Resetting the alert threshold based on peak traffic is not a reliable or effective way to minimize the false positives, as it may also increase the risk of false negatives. The alert threshold is the level of activity or deviation that triggers an alert from the IDS. If the threshold is set too high, the IDS may miss some malicious or suspicious activity that occurs below the threshold. If the threshold is set too low, the IDS may generate too many alerts for normal or benign activity that exceeds the threshold. The optimal threshold depends on various factors, such as the network size, topology, traffic volume, and baseline. Peak traffic is not a good indicator of the optimal threshold, as it may vary depending on the time, day, or season, and it may not reflect the normal or expected network behavior.
Analyzing the traffic to minimize the false negatives is not the main issue or goal in this scenario, as the problem is the high number of alerts, not the low number of alerts. Analyzing thetraffic can help to identify the malicious or suspicious activity that the IDS may have missed, but it does not address the root cause of the false positives or improve the IDS performance. Moreover, analyzing the traffic can be time-consuming and resource-intensive, especially for large or complex networks, and it may require specialized tools or skills that the risk practitioner may not have.
Sniffing the traffic using a network analyzer is not a suitable or feasible option in this scenario, as it may violate the privacy or security policies of the network or the organization. Sniffing the traffic means capturing and inspecting the network packets that are transmitted or received by the devices on the network. A network analyzer is a tool that can perform this function and display the packet data in a readable format. However, sniffing the traffic can also expose sensitive or confidential information, such as passwords, usernames, or credit card numbers, that may be contained in the packets. Therefore, sniffing the traffic may require authorization or consent from the network owners or users, and it may be restricted or prohibited by law or regulation.
References =
What is an intrusion detection system (IDS)? - IBM
Intrusion detection system - Wikipedia
What Are Intrusion Detection Systems? - MUO
12 Best Intrusion Detection System (IDS) Software 2024 - Comparitech
What is an Intrusion Detection System (IDS)? - Fortinet
[False Positive and False Negative in Intrusion Detection System]
[False Positives and False Negatives in Intrusion Detection Systems]
[How to Reduce False Positives for Your IDS/IPS]
[How to Set the Right Alert Thresholds for Your IDS/IPS]
[Network Traffic Analysis: What It Is and How It Works]
[What is a Network Analyzer? - Definition from Techopedia]
Identifying which of the following would BEST help an organization define an IT asset ' s criticality?
Data classification policy
Number of business users
The asset ' s end of life status
Business processes
CRISC suggests that asset criticality is determined by thebusiness processes and services the asset enables, and the impact if those processes are disrupted. By mapping IT assets to business processes, the organization can understand which systems support revenue generation, regulatory compliance, safety, or other critical outcomes. The data classification policy helps assess data sensitivity (confidentiality), which is related but not sufficient by itself to determine overall criticality; availability and integrity requirements also matter. The number of business users may indicate importance, but some highly critical systems (e.g., settlement engines, control systems) may have few users yet enormous impact. End-of-life status is relevant for obsolescence risk but does not necessarily correlate with business criticality. Therefore, linking assets to the processes they support is the most reliable basis for defining criticality.
Which of the following is the BEST key performance indicator (KPI) for determining how well an IT policy is aligned to business requirements?
Total cost to support the policy
Number of exceptions to the policy
Total cost of policy breaches
Number of inquiries regarding the policy
An IT policy is a document that defines the rules, standards, and procedures for the use, management, and security of IT resources within an organization. An IT policy should be aligned to the business requirements, which are the needs, expectations, and objectives of the business stakeholders, such as customers, employees, managers, partners, regulators, etc. An IT policy that is aligned to the business requirements can help support the business strategy, improve the business performance, and enhance the business value. A key performance indicator (KPI) is a metric that measures the achievement of a specific goal or objective. A KPI should be relevant, measurable, achievable, realistic, and time-bound. The best KPI for determining how well an IT policy is aligned to the business requirements is the number of exceptions to the policy. An exception to the policy is a deviation or violation of the policy rules, standards, or procedures, which may be intentional or unintentional, authorized or unauthorized, justified or unjustified. The number of exceptions to the policy can indicate how well the policy is understood, communicated, implemented, and enforced within the organization. The number of exceptions to the policy can also indicate how well the policy reflects the current and future business needs and expectations, and how flexible and adaptable the policy is to the changing business environment. A low number of exceptions to the policy can suggest that the policy is well aligned to the business requirements, while a high number of exceptions to the policy can suggest that the policy is misaligned or outdated, and may need to be reviewed or revised. References = Key Performance Indicator (KPI): Definition, Types, andExamples, Business KPIs: 5 important characteristics to be effective, What is a KPI? How To Choose the Best KPIs for Your Business - HubSpot Blog.
A PRIMARY advantage of involving business management in evaluating and managing risk is that management:
better understands the system architecture.
is more objective than risk management.
can balance technical and business risk.
can make better-informed business decisions.
Involving business management in evaluating and managing risk is beneficial, as it enables management to have a comprehensive and holistic view of the risk environment and its impact on the organization’s objectives and strategy. By participating in the risk management process, management can make better-informed business decisions, as they can consider the risk factors and implications of their choices, and align their decisions with the organization’s risk appetite and tolerance. Involving business management in evaluating and managing risk can also enhance the risk culture and governance of the organization, and foster a proactive and collaborative approach to risk management. References = Most Asked CRISC Exam Questions and Answers. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 253. ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 253. CRISC by Isaca Actual Free Exam Q & As, Question 9.
Which of the following aspects of risk can be transferred to a third party?
Reputation impact
Ownership
Financial impact
Accountability
While responsibility and accountability generally remain with the enterprise, financial impact (e.g., via insurance or outsourcing) can be transferred to a third party.
Which of We following is the MOST effective control to address the risk associated with compromising data privacy within the cloud?
Establish baseline security configurations with the cloud service provider.
Require the cloud prowler 10 disclose past data privacy breaches.
Ensure the cloud service provider performs an annual risk assessment.
Specify cloud service provider liability for data privacy breaches in the contract
Specifying cloud service provider liability for data privacy breaches in the contract is the most effective control to address the risk associated with compromising data privacy within the cloud, because it establishes the roles and responsibilities of the cloud service provider and the customer in case of a data breach, and defines the compensation or remediation measures that the cloud service provider should provide. This control also creates an incentive for the cloud service provider to implement adequate security measures to protect the customer’s data and comply with the relevant laws and regulations. The other options are not the most effective controls, although they may also be helpful in reducing the risk of data privacy breaches. Establishing baseline security configurations with the cloud service provider, requiring the cloud service provider to disclose past data privacy breaches, and ensuring the cloud service provider performs an annual risk assessment are examples of preventive or detective controls that aim to reduce the likelihood or impact of a data breach, but they do not address the accountability or liability of the cloud service provider in case of a data breach. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
When prioritizing risk response, management should FIRST:
evaluate the organization s ability and expertise to implement the solution.
evaluate the risk response of similar organizations.
address high risk factors that have efficient and effective solutions.
determine which risk factors have high remediation costs
According to the Risk and Information Systems Control Study Manual, the first step in prioritizing risk response is to address the high risk factors that have efficient and effective solutions. This means that management should focus on the risks that have the most impact on the organization’s objectives and can be mitigated with the least amount of resources and effort. This approach helps to optimize the risk response process and achieve the best results in terms of risk reduction and value creation. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.3.2, Page 223.
Which group has PRIMARY ownership of reputational risk stemming from unethical behavior within the organization?
Board of directors
Human resources (HR)
Risk management committee
Audit committee
The group that has primary ownership of reputational risk stemming from unethical behavior within the organization is A. Board of directors. According to the CFA Institute, the board of directors is responsible for setting the tone at the top and ensuring that the company adheres to high ethical standards and values. The board of directors also oversees the company’s culture, governance, and risk management practices, and holds the management accountable for any misconduct or breach of trust1 The board of directors may delegate some of its oversight functions to other committees, such as the human resources, risk management, or audit committee, but ultimately, the board of directors bears the ultimate responsibility for the company’s reputation and integrity
A deficient control has been identified which could result in great harm to an organization should a low frequency threat event occur. When communicating the associated risk to senior management the risk practitioner should explain:
mitigation plans for threat events should be prepared in the current planning period.
this risk scenario is equivalent to more frequent but lower impact risk scenarios.
the current level of risk is within tolerance.
an increase in threat events could cause a loss sooner than anticipated.
The risk practitioner should explain to senior management that mitigation plans for threat events should be prepared in the current planning period, as this would demonstrate a proactive and responsible approach to risk management. Mitigation plans are documents that outline the actions and resources needed to reduce the likelihood and/or impact of a specific risk scenario. Mitigation plans should include the following elements:
Risk scenario description and risk ID
Risk owner and other stakeholders
Risk response strategy and objectives
Risk response actions and tasks
Resources, costs, and benefits
Roles and responsibilities
Timeline and milestones
Performance indicators and monitoring mechanisms
Contingency plans and triggers
Mitigation plans help to address the gap between the current and desired risk levels and align the risk response with the organizational risk appetite and objectives. Mitigation plans also facilitate the communication, coordination, and collaboration among the risk owners and other stakeholders involved in the risk response process. Mitigation plans should be prepared in the current planning period, as this would allow the organization to act timely and effectively in the event of a low frequency threat event. Preparing mitigation plans in advance would also help to avoid or minimize the potential harm to the organization and its reputation.
The other options are not the best ways to communicate the associated risk to senior management. Explaining that this risk scenario is equivalent to more frequent but lower impact risk scenarios may not accurately reflect the true nature and severity of the risk. Explaining that the current level of risk is within tolerance may not convey the urgency and importance of addressing the risk. Explaining that an increase in threat events could cause a loss sooner than anticipated may not provide a clear and actionable solution for the risk. References = Four steps for managing risk at the CEO level, IT Risk Resources | ISACA, How to Communicate Risk to Stakeholders | Anitian
Which of the following is the PRIMARY purpose of a risk register?
It guides management in determining risk appetite.
It provides management with a risk inventory.
It aligns risk scenarios to business objectives.
It monitors the performance of risk and control owners.
The MOST effective approach to prioritize risk scenarios is by:
assessing impact to the strategic plan.
aligning with industry best practices.
soliciting input from risk management experts.
evaluating the cost of risk response.
The most effective approach to prioritize risk scenarios is by assessing the impact to the strategic plan, because this will help to align the risk management process with the organization’s vision, mission, and goals. The strategic plan is the document that defines the organization’s direction, priorities, and objectives, and guides the allocation of resources and efforts. By assessing theimpact to the strategic plan, the organization can determine which risk scenarios pose the greatest threat or opportunity to the achievement of the strategic objectives, and prioritize them accordingly. The other options are not as effective as assessing the impact to the strategic plan, because they do not directly relate to the organization’s specific context, needs, and expectations, as explained below:
B. Aligning with industry best practices is an approach that involves following the standards, norms, and expectations for risk management that are established and followed by the peers or competitors in the same industry or sector. Aligning with industry best practices can help to benchmark and compare the organization’s risk management performance and maturity, and identify areas for improvement or innovation. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not account for the organization’s unique and customized risk scenarios, which may differ from the industry average or standard.
C. Soliciting input from risk management experts is an approach that involves seeking advice, guidance, or feedback from the professionals or specialists who have the knowledge, experience, or skills in risk management. Soliciting input from risk management experts can help to enhance the quality and validity of the risk analysis and evaluation, and provide insights and recommendations for risk mitigation. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not reflect the organization’s risk appetite, preferences, and expectations, which may differ from the risk management experts’ opinions or perspectives.
D. Evaluating the cost of risk response is an approach that involves estimating the resources and efforts required to implement the risk response strategies, such as avoiding, reducing, transferring, or accepting the risk. Evaluating the cost of risk response can help to optimize the risk management efficiency and effectiveness, and balance the potential benefits and costs of taking risks. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not consider the potential consequences and outcomes of the risk scenarios, which may affect the organization’s performance and reputation. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 45. The Ultimate Guide to Risk Prioritization - Hyperproof, Risk Prioritization: What Is It? [2021 Guide & Matrix] - ERM Software, What is Risk Prioritization | Centraleyes, Scenario Planning in Risk Management: Why It is Needed - SmartCompliance
Which of the following is the BEST way to mitigate the risk to IT infrastructure availability?
Establishing a disaster recovery plan (DRP)
Establishing recovery time objectives (RTOs)
Maintaining a current list of staff contact delays
Maintaining a risk register
The best way to mitigate the risk to IT infrastructure availability is to establish a disaster recovery plan (DRP), because a DRP is a document that defines the procedures and resources needed to restore the IT infrastructure and resume the critical business functions in the event of a disaster or disruption. A DRP helps to minimize the downtime, data loss, and financial impact of a disaster, and ensures the continuity of operations and services. The other options are not the best ways to mitigate the risk to IT infrastructure availability, although they may also be helpful in supporting the DRP. Establishing recovery time objectives (RTOs), maintaining a current list of staff contact details, and maintaining a risk register are examples of planning or monitoring activities that aim to define the requirements, roles, and responsibilities for the disaster recovery process, but they do not address the actual implementation or execution of the DRP. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Which of the following would MOST effectively reduce the potential for inappropriate exposure of vulnerabilities documented in an organization ' s risk register?
Limit access to senior management only.
Encrypt the risk register.
Implement role-based access.
Require users to sign a confidentiality agreement.
A risk register is a document that contains information about potential cybersecurity risks that could threaten a project’s success, or even the business itself2. Therefore, it is important to protect the confidentiality and integrity of the risk register from unauthorized or inappropriate access, modification, or disclosure. One way to do this is to implement role-based access, which is a method of restricting access to the risk register based on the roles or responsibilities of the users1. This way, only authorized users who need to view or edit the risk register for legitimate purposes can do so, and the access rights can be revoked or modified as needed. This would most effectively reduce the potential for inappropriate exposure of vulnerabilities documented in the risk register. The other options are not as effective or feasible as option C, as they do not address the need to balance the security and availability of the risk register. Option A, limiting access to senior management only, would compromise the availability and usefulness of the risk register, as other stakeholders such as project managers, risk owners, or auditors may need to access therisk register for risk identification, analysis, response, or monitoring purposes3. Option B, encrypting the risk register, would enhance the security of the risk register, but it would not prevent authorized users from exposing the vulnerabilities to unauthorized parties, either intentionally or unintentionally. Encryption also adds complexity and cost to the risk register management process, and may affect the performance or usability of the risk register4. Option D, requiring users to sign a confidentiality agreement, would rely on the compliance and ethics of the users, but it would not prevent or detect any breaches of the agreement. A confidentiality agreement also does not specify the access rights or roles of the users, and may not be legally enforceable in some cases5.
Which of the following should a risk practitioner recommend FIRST when an increasing trend of risk events and subsequent losses has been identified?
Conduct root cause analyses for risk events.
Educate personnel on risk mitigation strategies.
Integrate the risk event and incident management processes.
Implement controls to prevent future risk events.
Conducting root cause analyses for risk events is the first recommendation that a risk practitioner should make when an increasing trend of risk events and subsequent losses has been identified, as this helps to identify the underlying causes and sources of the risk events, and to determine the appropriate actions to address them. Root cause analysis is a systematic process of collecting and analyzing data, finding the root causes, and implementing solutions to prevent recurrence or reduce the impact of the risk events. Educating personnel on risk mitigation strategies, integrating the risk event and incident management processes, and implementing controls to prevent future risk events are not the first recommendations, but rather the possible outcomes or actions of conducting root cause analyses for risk events. References = CRISC Certified in Riskand Information Systems Control – Question208; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 208.
Which of the following is the MOST likely reason an organization would engage an independent reviewer to assess its IT risk management program?
To ensure IT risk management is focused on mitigating emerging risk
To confirm that IT risk assessment results are expressed in quantitative terms
To evaluate threats to the organization ' s operations and strategy
To identify gaps in the alignment of IT risk management processes and strategy
An independent review is typically sought to provide an objective assessment of the IT risk management program, ensuring that it aligns with the organization’s overall strategy andobjectives. The reviewer can identify areas where the program may not be effectively addressing the organization’s strategic goals or where improvements can be made to better manage IT risks.
Which of the following should be a risk practitioner’s MOST important consideration when developing IT risk scenarios?
The impact of controls on the efficiency of the business in delivering services
Linkage of identified risk scenarios with enterprise risk management
Potential threats and vulnerabilities that may have an impact on the business
Results of network vulnerability scanning and penetration testing
The MOST important consideration when developing IT risk scenarios is the potential threats and vulnerabilities that may have an impact on the business, because they are the key elements of a risk scenario that describe the sources and causes of the risk, and the potential consequences and impacts of the risk on the business objectives and processes. The other options are not as important as the potential threats and vulnerabilities, because:
Option A: The impact of controls on the efficiency of the business in delivering services is a secondary consideration that may affect the cost-benefit analysis of the risk response, but it does not directly affect the identification and assessment of the risk scenario.
Option B: Linkage of identified risk scenarios with enterprise risk management is a good practice that ensures the alignment and integration of the IT risk management with the overall enterprise risk management, but it does not directly affect the identification and assessment of the risk scenario.
Option D: Results of network vulnerability scanning and penetration testing are useful sources of information that may reveal some of the threats and vulnerabilities in the IT environment, but they are not the only or the most important consideration when developing IT risk scenarios, as they may not cover all the aspects and dimensions of the risk. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 104.
Which of the following should be the PRIMARY focus of a disaster recovery management (DRM) framework and related processes?
Restoring IT and cybersecurity operations
Assessing the impact and probability of disaster scenarios
Ensuring timely recovery of critical business operations
Determining capacity for alternate sites
Ensuring Timely Recovery of Critical Business Operations:
Primary Focus: The primary focus of a Disaster Recovery Management (DRM) framework is to ensure that critical business operations can be recovered and resumed in a timely manner after a disruption.
Business Continuity: Timely recovery of operations is essential for maintaining business continuity and minimizing the impact of disruptions on the organization’s ability to deliver products and services.
Recovery Objectives: Establishing clear recovery time objectives (RTOs) and recovery point objectives (RPOs) ensures that critical operations are prioritized and recovery efforts are aligned with business needs.
Comparison with Other Options:
Restoring IT and Cybersecurity Operations: While important, this is part of the broader goal of recovering critical business operations.
Assessing Impact and Probability of Disaster Scenarios: This is a preparatory step that informs the DRM framework but is not the primary focus.
Determining Capacity for Alternate Sites: This is a component of the DRM strategy but supports the primary focus of ensuring timely recovery.
Best Practices:
Comprehensive Planning: Develop comprehensive disaster recovery plans that prioritize the recovery of critical business operations.
Regular Testing: Regularly test and update disaster recovery plans to ensure they remain effective and aligned with business objectives.
Cross-Functional Collaboration: Involve all relevant business units in disaster recovery planning to ensure a coordinated and effective response.
Which of the following is the MOST important benefit of implementing a data classification program?
Reduction in data complexity
Reduction in processing times
Identification of appropriate ownership
Identification of appropriate controls
A data classification program helpsidentify appropriate controlsby categorizing data based on sensitivity and criticality. This ensures that data protection measures are aligned with its value and risk level, improving overall security posture.
Which of the following is the PRIMARY responsibility of a control owner?
To make risk-based decisions and own losses
To ensure implemented controls mitigate risk
To approve deviations from controls
To design controls that will eliminate risk
A control owner ' s primary responsibility is to ensure that the controls under their purview are effectively implemented and functioning as intended to mitigate associated risks. This involves regular monitoring, evaluation, and reporting on the performance of controls to maintain the organization ' s risk posture within acceptable limits.
Which of the following is the MOST important consideration when selecting either a qualitative or quantitative risk analysis?
Expertise in both methodologies
Maturity of the risk management program
Time available for risk analysis
Resources available for data analysis
The most important consideration when selecting either a qualitative or quantitative risk analysis is the time available for risk analysis, as this affects the level of detail and accuracy that can be achieved in the risk assessment process. Qualitative risk analysis is a method that uses subjective judgments and ratings to measure and prioritize the risks based on their likelihood and impact, as well as other factors such as urgency, velocity, and persistence. Qualitative risk analysis is usually faster and simpler than quantitative risk analysis, but it may also be less precise and consistent. Quantitative risk analysis is a method that uses numerical data and mathematicalmodels to measure and prioritize the risks based on theirprobability and magnitude, as well as other factors such as frequency, duration, and correlation. Quantitative risk analysis is usually more complex and time-consuming than qualitative risk analysis, but it may also provide more objective and reliable results. The other options are not the most important considerations when selecting either a qualitative or quantitative risk analysis, although they may have some influence or relevance. Expertise in both methodologies is desirable, but it does not determine the choice of the risk analysis method, as it depends on the availability and suitability of the experts for the specific risk context and objectives. Maturity of the risk management program is important, but it does not dictate the choice of the risk analysis method, as it depends on the level of integration and alignment of the risk management activities with the enterprise’s strategy and goals. Resources available for data analysis are relevant, but they do not decide the choice of the risk analysis method, as they depend on the quality and availability of the data sources and tools for the risk assessment process. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Assessment, page 81.ST
A risk practitioner ' s BEST guidance to help an organization develop relevant risk scenarios is to ensure the scenarios are:
based on industry trends.
mapped to incident response plans.
related to probable events.
aligned with risk management capabilities.
Understanding the Question:
The question asks for the best guidance for developing relevant risk scenarios.
Analyzing the Options:
A. Based on industry trends:Important but may not always be directly relevant to the specific organization.
B. Mapped to incident response plans:Useful but secondary to ensuring the scenarios are probable.
C. Related to probable events:Ensures the scenarios are realistic and likely, making them more relevant and actionable.
D. Aligned with risk management capabilities:Important for managing risks but not as critical as ensuring scenarios are probable.
Probable Events:Developing risk scenarios that are based on probable events ensures that the organization is prepared for the most likely risks. This makes risk management efforts more practical and focused on real threats.
Relevance:By focusing on probable events, the scenarios will be more relevant to the organization ' s actual risk environment, making it easier to allocate resources and plan responses effectively.
Which of the following will BEST help to ensure that information system controls are effective?
Responding promptly to control exceptions
Implementing compensating controls
Testing controls periodically
Automating manual controls
The best way to ensure that information system controls are effective is to test them periodically. Testing controls periodically helps to verify that the controls are operating as intended, and that they are aligned with the enterprise’s objectives, policies, and standards. Testing controls periodically also helps to identify any gaps, weaknesses, or deficiencies in the controls, and to implement corrective actions or improvements. Responding promptly to control exceptions, implementing compensating controls, and automating manual controls are good practices, but they are not the best way to ensure control effectiveness. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1.2, page 1071
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 641.
Which of the following provides the MOST useful information to senior management about risk mitigation status?
Risk strategy
Risk register
Gap analysis
Business impact analysis (BIA)
A risk register is the primary tool for communicating progress: it consolidates risk scenarios, mitigation plans, current status, and residual risk in a structured format. Senior management relies on it to make informed decisions.
When defining thresholds for control key performance indicators (KPIs). it is MOST helpful to align:
information risk assessments with enterprise risk assessments.
key risk indicators (KRIs) with risk appetite of the business.
the control key performance indicators (KPIs) with audit findings.
control performance with risk tolerance of business owners.
The most helpful factor to align when defining thresholds for control key performance indicators (KPIs) is the control performance with the risk tolerance of business owners. Control KPIs are metrics that measurethe effectiveness and efficiency of the controls that are implemented to mitigate the risks. By aligning the control performance with the risk tolerance of business owners, the thresholds for control KPIs can reflect the acceptable level of risk and the desired level of control for the business processes and objectives. Information risk assessments with enterprise risk assessments, key risk indicators (KRIs) with risk appetite of the business, andcontrol KPIs with audit findings are other possible factors to align, but they are not as helpful as control performance with risk tolerance of business owners. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 12; CRISC Review Manual, 6th Edition, page 215.
The GREATEST concern when maintaining a risk register is that:
impacts are recorded in qualitative terms.
executive management does not perform periodic reviews.
IT risk is not linked with IT assets.
significant changes in risk factors are excluded.
A risk register is a tool that records and tracks the identified risks, their causes, impacts, likelihood, responses, and owners. The greatest concern when maintaining a risk register is that significant changes in risk factors are excluded. Risk factors are the internal and external variables that influence the occurrence and impact of risks. Risk factors can change over time due to changes in the business environment, the IT landscape, the threat landscape, or the regulatory requirements. If the risk register does not reflect the significant changes in risk factors, it may not provide an accurate and current view of the enterprise’s risk profile and may not support effective risk management decisions and actions. The other options are not as concerning as the exclusion of significant changes in risk factors, as they involve different aspects of the risk register:
Impacts are recorded in qualitative terms means that the risk register uses descriptive scales, such as low, medium, and high, to measure the potential consequences of the risks. This may not be asprecise or consistent as quantitative measures, such as monetary values or percentages, but it does not necessarily affect the validity or usefulness of the risk register.
Executive management does not perform periodic reviews means that the risk register is not regularly evaluated and updated by the senior leaders of the enterprise. This may indicate a lack of management commitment or oversight for risk management, but it does not directly affect the quality or completeness of the risk register.
IT risk is not linked with IT assets means that the risk register does not associate the identified risks with the specific IT resources, such as hardware, software, data, or services, that are affected by or contribute to the risks. This may limit the visibility and traceability of the risks, but it does not necessarily affect the identification or assessment of the risks. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.2.2, pp. 21-22.
An organization does not have a defined process to revoke IT access of staff members who have changed roles within the organization. Which of the following is the GREATEST concern associated with this deficiency?
Noncompliance with the access management policy
Fraudulent insider activities
Misaligned job duties
Inefficient access review processes
CRISC highlights that inadequate termination or role-change procedures for access rights expose the organization to serious insider threats. When users change roles but retain access not needed for their new responsibilities, the risk offraudulent insider activitiesand unauthorized use of systems significantly increases. Excessive privileges can be abused intentionally or misused accidentally, leading to data breaches, financial loss, or regulatory non-compliance. While noncompliance with policy is an issue, it is a secondary, formal concern—the primary risk is actual misuse of privileges. Misaligned job duties and inefficiencies in access review are consequences but not as severe as the potential for fraud, sabotage, or data theft. Therefore, the greatest concern is the exposure to insider risk due to inadequate de-provisioning and access recertification processes.
Which of the following provides the BEST protection for Internet of Things (loT) devices that are accessed within an organization?
Identity and access management (IAM)
Comprehensive patching program
Source code reviews
Adoption of a defense-in-depth strategy
Days before the realization of an acquisition, a data breach is discovered at the company to be acquired. For the accruing organization, this situation represents which of the following?
Threat event
Inherent risk
Risk event
Security incident
A risk event is an occurrence or situation that has a negative impact on the objectives, operations, or resources of an enterprise. A data breach at the company to be acquired is a risk event for the acquiring organization, because it can affect the value, reputation, or performance of the acquisition. A risk event can also trigger other risks or consequences that may require further actions or responses. The other options are not the correct answers, because they do not describe the situation accurately. A threat event is an occurrence or situation that exploits a vulnerability or causes harm to an asset or process. An inherent risk is the risk that exists before applying any controls or treatments. A security incident is an event that violates the security policies or procedures of an enterprise. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
The BEST reason to classify IT assets during a risk assessment is to determine the:
priority in the risk register.
business process owner.
enterprise risk profile.
appropriate level of protection.
Classifying IT assets during a risk assessment is a process of assigning values to the IT assets based on their importance, sensitivity, and criticality to the enterprise. The best reason to classify IT assets is todetermine the appropriate level of protection that each IT asset requires, based on its value and the potential impact of its loss or compromise. This helps the enterprise to allocate resources and implement controls that are proportional to the risk exposure of the IT assets, and to optimize the cost and benefit of risk mitigation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 233. CRISC by Isaca Actual Free Exam Q & As, Question 9. CRISC Sample Questions 2024, Question 233. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 233.
An organization moved its payroll system to a Software as a Service (SaaS) application. A new data privacy regulation stipulates that data can only be processed within the countrywhere it is collected. Which of the following should be done FIRST when addressing this situation?
Analyze data protection methods.
Understand data flows.
Include a right-to-audit clause.
Implement strong access controls.
The first step when addressing the situation of moving the payroll system to a SaaS application and complying with the new data privacy regulation is to understand the data flows. This means identifying where the data is collected, stored, processed, and transferred, and who has access to it. Understanding the data flows can help to determine the scope and impact of the regulation, as well as the potential risks and gaps in the current state. It can also help to identify the roles and responsibilities of the organization and the SaaS provider regarding data protection and compliance. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.1.2, p. 237-238
Which of the following is the MOST effective way to help ensure accountability for managing risk?
Assign process owners to key risk areas.
Obtain independent risk assessments.
Assign incident response action plan responsibilities.
Create accurate process narratives.
The most effective way to help ensure accountability for managing risk is to assign process owners to key risk areas. Process owners are the persons or entities that have the authority andresponsibility to manage a specific process or a group of related processes. Process owners help to identify, assess, and respond to the risks associated with the process, and to monitor and report on the process performance and improvement. Process owners also help to communicate and coordinate the process management activities with the relevant stakeholders, such as the board, management, business units, and IT functions. Assigning process owners to key risk areas helps to ensure accountability for managing risk, because it helps to define and clarify the roles and responsibilities of the process owners, and to establish and enforce the expectations and standards for the process owners. Assigning process owners to key risk areas also helps to measure and evaluate the effectiveness and efficiency of the process owners, and to identify and address any issues or gaps in the process management activities. The other options are not as effective as assigning process owners to key risk areas, although they may be related to the risk management process. Obtaining independent risk assessments, assigning incident response action plan responsibilities, and creating accurate process narratives are all activities that can help to support or improve the risk management process, but they do not necessarily ensure accountability for managing risk. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, page 2-11.
Which of the following would MOST likely cause a risk practitioner to reassess risk scenarios?
A change in the risk management policy
A major security incident
A change in the regulatory environment
An increase in intrusion attempts
The most likely cause for a risk practitioner to reassess risk scenarios is a change in the regulatory environment. A regulatory environment is the set of laws, rules, and standards that apply to an organization and its activities, such as data privacy, security, compliance, or governance. A change in the regulatory environment can occur due to various factors, such as new legislation, court rulings, enforcement actions, or industry trends. A change in the regulatory environment can affect the risk scenarios that the organization faces, as it may introduce new or modified risks, or alter the probability or impact of existing risks. For example, a new regulation may require the organization to implement additional or different controls, or to report or disclose more information, which may increase the cost, complexity, or vulnerability of the organization’s processes and systems. A change in the regulatory environment may also affect the risk appetite, tolerance, and capacity of the organization, as it may impose different requirements or expectations for the organization’s risk management performance and outcomes. Therefore, a risk practitioner should reassess the risk scenarios when there is a change in the regulatory environment, to ensure that the risk scenarios are accurate, complete, and relevant, and that the risk response strategies and plans are appropriate, effective, and compliant. The other options are not the most likely cause, although they may be related or influential to the riskscenarios. A change in the risk management policy is a change in the rules and guidelines that define how the organization manages its risks, such as the roles and responsibilities, the processes and procedures, the tools and techniques, or the reporting and communication. A change in the risk management policy can affect the risk scenarios, as it may change the way the organization identifies, analyzes, evaluates, and responds to the risks, but it does not directly create or modify the risks themselves. A major security incident is an event or situation that compromises the confidentiality, integrity, or availability of the organization’s information or systems, such as a data breach, a denial-of-service attack, or a ransomware infection. A major security incident can affect the risk scenarios, as it may indicate or reveal the existence or severity of the risks, or trigger or escalate the consequences of the risks, but it is not a cause, rather it is an effect of the risks. An increase in intrusion attempts is an increase in the frequency or intensity of the unauthorized or malicious attempts to access or exploit the organization’s information or systems, such as phishing, malware, or brute-force attacks. An increase in intrusion attempts can affect the risk scenarios, as it may increase the likelihood or impact of the risks, or expose or exacerbate the vulnerabilities of the organization’s processes and systems, but it is not a cause, rather it is a manifestation of the risks. References = Risk Scenarios Toolkit -ISACA, How to Write Strong Risk Scenarios and Statements - ISACA, The Impact of Regulatory Change on Business - Deloitte
A risk practitioner has been notified of a social engineering attack using artificial intelligence (Al) technology to impersonate senior management personnel. Which of the following would BEST mitigate the impact of such attacks?
Training and awareness of employees for increased vigilance
Increased monitoring of executive accounts
Subscription to data breach monitoring sites
Suspension and takedown of malicious domains or accounts
Understanding the Question:
The question is about mitigating the impact of social engineering attacks that use AI technology to impersonate senior management personnel.
Analyzing the Options:
A. Training and awareness of employees for increased vigilance:This is the most proactive approach. Educating employees about the risks and signs of social engineering attacks enhances their ability to recognize and respond appropriately to such threats.
B. Increased monitoring of executive accounts:Useful but reactive; it doesn ' t prevent initial attempts.
C. Subscription to data breach monitoring sites:Helps detect breaches but doesn’t directly mitigate impersonation attacks.
D. Suspension and takedown of malicious domains or accounts:Reactive measure and might not be immediate or comprehensive.
Importance of Training:Employees are often the first line of defense against social engineering attacks. Regular training ensures they are aware of the tactics used in such attacks, including those leveraging AI, and how to respond effectively.
Proactive Measure:Training increases vigilance and the likelihood of early detection, reducing the potential impact of the attack.
Who is ULTIMATELY accountable for risk treatment?
Risk owner
Enterprise risk management (ERM)
Risk practitioner
Control owner
The risk owner holds ultimate accountability for risk treatment, as they are responsible for decisions regarding the management and mitigation of the risk. This is a fundamental principle ofRisk Ownership and Accountabilitywithin the CRISC framework.
Which of the following would be the BEST recommendation if the level of risk in the IT risk profile has decreased and is now below management ' s risk appetite?
Optimize the control environment.
Realign risk appetite to the current risk level.
Decrease the number of related risk scenarios.
Reduce the risk management budget.
The level of risk in the IT risk profile is the aggregate measure of the likelihood and impact of IT-related risks that may affect the enterprise’s objectives and operations.
The risk appetite is the amount and type of risk that the enterprise is willing to accept in pursuit of its goals. It is usually expressed as a range or a threshold, and it is aligned with the enterprise’s strategy and culture.
If the level of risk in the IT risk profile has decreased and is now below management’s risk appetite, it means that the enterprise has more capacity and opportunity to take on additional risks that may offer higher rewards or benefits.
The best recommendation in this situation is to optimize the control environment, which is the set of policies, procedures, standards, and practices that provide the foundation for managing IT risks and controls. Optimizing the control environment means enhancing the efficiency and effectiveness of the controls, reducing the costs and complexity of compliance, and aligning the controls with the enterprise’s objectives and values.
Optimizing the control environment can help the enterprise to achieve the optimal balance between risk and return, and to leverage its risk management capabilities to create and protect value.
The other options are not the best recommendations, because they do not address the opportunity to improve the enterprise’s performance and resilience.
Realigning risk appetite to the current risk level may result in missing out on potential gains or advantages that could be obtained by taking more risks within the acceptable range.
Decreasing the number of related risk scenarios may reduce the scope and depth of risk analysis and reporting, and impair the enterprise’s ability to identify and respond to emerging or changing risks.
Reducing the risk management budget may compromise the quality and reliability of the risk management process and activities, and weaken the enterprise’s risk culture and governance. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 29-30, 34-35, 38-39, 44-45
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 145
Which of the following would be the GREATEST risk associated with a new implementation of single sign-on?
Inability to access key information
Complex security administration
User resistance to single sign-on
Single point of failure
Single sign-on (SSO)simplifies authentication but introduces asingle point of failure. If the SSO mechanism is compromised or goes down, it can result in the loss of access across multiple systems, leading to widespread business disruption or security breaches.
Which of the following introduces the GREATEST amount of risk during the software development life cycle (SDLC)?
Use of debugging tools
Incorrect firewall configuration
Inability to pass user acceptance tests (UATs)
Untested changes to production
CRISC emphasizes thatuntested changes in productionrepresent high operational risk due to potential downtime, integrity issues, or security failures.
Supporting extract:
“Untested changes to production systems introduce the greatest amount of risk because they may disrupt operations or introduce security vulnerabilities.”
UAT failureordebuggingpose limited impact confined to pre-production stages.
Hence,Dis the correct and verified answer.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Risk in the System Development Life Cycle.
Which of the following should be reported periodically to the risk committee?
System risk and control matrix
Emerging IT risk scenarios
Changes to risk assessment methodology
Audit committee charter
Reporting to the Risk Committee:
Role of Risk Committee: The risk committee is responsible for overseeing the organization’s risk management practices, including identifying, assessing, and mitigating risks.
Emerging IT Risks: Reporting emerging IT risk scenarios to the committee ensures that new and evolving threats are identified and addressed proactively.
Importance of Emerging IT Risk Scenarios:
Proactive Risk Management: By staying informed about emerging risks, the committee can implement preventive measures and avoid potential impacts.
Strategic Planning: Understanding emerging risks allows for better strategic planning and resource allocation to address these risks.
Comparison with Other Options:
System Risk and Control Matrix: Useful for ongoing monitoring but may not capture new and emerging risks.
Changes to Risk Assessment Methodology: Important for refining risk management processes but not as critical as identifying new risks.
Audit Committee Charter: Relevant for governance but not directly related to proactive risk management.
Best Practices:
Regular Updates: Provide the risk committee with regular updates on emerging IT risk scenarios.
Collaborative Approach: Engage various stakeholders in identifying and reporting emerging risks.
An IT manager insists on accepting an IT risk associated with a key business process due to the limited resources available to mitigate. Which of the following is the risk practitioner ' s MOST important action?
Seek additional resources for risk mitigation.
Document the business rationale for risk acceptance.
Validate the decision with the process owner
Conduct a follow-up business process analysis.
The correct answer isCbecause theprocess owneris the appropriate risk owner for a key business process, and therefore the most important action is tovalidate the decision with the process owner. An IT manager may provide operational input, but acceptance of business risk must be confirmed by the accountable business owner.
The other options are less important as the primary action:
A. Seek additional resources for risk mitigationmay be worthwhile, but first the acceptance decision must be validated by the actual risk owner.
B. Document the business rationale for risk acceptanceis necessary, but only after the correct owner has validated the decision.
D. Conduct a follow-up business process analysismay support the discussion, but the main issue is proper authority for accepting the risk.
Exact Extracts supporting the answer:
“For an IT system supporting a critical business process senior managers should be accountable for the risk.”
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“Accountability for a risk treatment plan lies with the risk owner.”
“The PRIMARY objective of risk reporting is to provide the risk owner with information to initiate risk response.”
“The risk practitioner’s primary role is to consult and recommend risk responses.”
These extracts show that the business or process owner is the accountable party for accepting risk associated with a key business process. Therefore, the risk practitioner should firstvalidate the decision with the process owner.
===========
The BEST indication that risk management is effective is when risk has been reduced to meet:
risk levels.
risk budgets.
risk appetite.
risk capacity.
The best indication that risk management is effective is when risk has been reduced to meet the risk appetite of the enterprise. Risk appetite is the amount and type of risk that an enterprise is willing to accept in pursuit of its objectives. Risk appetite reflects the enterprise’s risk culture, strategy, and values, and provides a basis for setting risk tolerance levels and risk response strategies. Risk management is effective when it enables the enterprise to align its risk exposure with its risk appetite, and to optimize the risk-return trade-off. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.1, page 181
A recent audit identified high-risk issues in a business unit though a previous control self-assessment (CSA) had good results. Which of the following is the MOST likely reason for the difference?
The audit had a broader scope than the CSA.
The CSA was not sample-based.
The CSA did not test control effectiveness.
The CSA was compliance-based, while the audit was risk-based.
A compliance-based CSA focuses on ensuring that the business unit follows the policies and procedures established by the enterprise, regardless of the actual risk level or impact of the controls.
A risk-based CSA focuses on identifying and evaluating the risks that may affect the business unit’s objectives, and designing and implementing controls that are appropriate to mitigate those risks.
A compliance-based CSA may not capture all the high-risk issues that exist in a business unit, especially if they are not aligned with the enterprise’s standards or expectations.
A risk-based CSA may identify more high-risk issues than a compliance-based CSA, because it considers both internal and external factors that may affect the business unit’s performance or security.
Therefore, a difference in results between a previous control self-assessment (CSA) and an audit indicates that either one of them was not risk-based, but rather compliance-based.
The references for this answer are:
Risk IT Framework, page 9
Information Technology & Security, page 3
Risk Scenarios Starter Pack, page 1
Which of the following is MOST important for a risk practitioner to consider when evaluating plans for changes to IT services?
Change testing schedule
Impact assessment of the change
Change communication plan
User acceptance testing (UAT)
According to the CRISC Review Manual1, impact assessment is the process of identifying and evaluating the potential effects of changes to IT services on the organization’s business objectives, processes, resources, and risks. Impact assessment is essential for ensuring that the changes are aligned with the organization’s strategy, goals, and risk appetite, and that the benefits of the changes outweigh the costs and risks. Impact assessment also helps to prioritize, plan, and implement the changes effectively and efficiently, and to monitor and measure the outcomes of the changes. Therefore, the most important factor for a risk practitioner to consider when evaluating plans for changes to IT services is the impact assessment of the change. References = CRISC Review Manual1, page 224.
Which of the following BEST indicates effective information security incident management?
Monthly trend of information security-related incidents
Average time to identify critical information security incidents
Frequency of information security incident response plan testing
Percentage of high-risk security incidents
The average time to identify critical information security incidents is the best indicator of effective information security incident management, as it measures how quickly the organization can detect and respond to the most severe threats to its information assets. The faster the organization can identify critical incidents, the lower the potential impact and damage they can cause. The average time to identify critical incidents also reflects the efficiency and accuracy of the monitoring and reporting mechanisms, as well as the awareness and training of the staff and stakeholders. The other options are not the best indicators of effective information security incident management, as they do not directly measure the performance or quality of the incident response process. The monthly trend of information security-related incidents may show the frequency or severity of the incidents, but not how well they are managed. The frequency of information security incident response plan testing may show the preparedness or maturity of the organization, but not the actual effectiveness of the plan. The percentage of high-risk security incidents may show the risk exposure or appetite of the organization, but not the risk mitigationor treatment. References = 7 Types of Information Security Incidents and How to Respond; Annex A.16: Information Security Incident Management - ISMS.online; CISM Isaca Exam Questions and Answers - CertLibrary.com
An organization outsources the processing of us payroll data A risk practitioner identifies a control weakness at the third party trial exposes the payroll data. Who should own this risk?
The third party ' s IT operations manager
The organization ' s process owner
The third party ' s chief risk officer (CRO)
The organization ' s risk practitioner
The organization’s process owner should own the risk of exposing the payroll data due to a control weakness at the third party, because the process owner is the person who is responsible for the business process that generates, uses, or transfers the payroll data. The process owner should also ensure that the third party complies with the contractual obligations and service level agreements that define the expected performance and security standards of the payroll data processing. The other options are not the correct answers, because they are not the primary owners of the risk, although they may also be involved in the risk management process. The third party’s IT operations manager, the third party’s chief risk officer (CRO), and the organization’s risk practitioner are examples of secondary owners or stakeholders of the risk, who may provide support, guidance, or oversight to the risk owner, but they are not accountable for the risk or the risk response strategy. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Which of the following is the BEST key control indicator (KCI) for risk related to IT infrastructure failure?
Number of times the recovery plan is reviewed
Number of successful recovery plan tests
Percentage of systems with outdated virus protection
Percentage of employees who can work remotely
A key control indicator (KCI) is a metric that provides information on the extent to which a given control is meeting its intended objectives in terms of loss prevention, reduction, etc. A KCI should have an explicit relationship to both the specific control and the specific risk against which the control has been implemented. For risk related to IT infrastructure failure, a possible control is to have a recovery plan that can restore the critical IT services and minimize the impact of the failure. A KCI that can measure the effectiveness of this control is the number of successful recovery plan tests, which indicates how well the recovery plan can be executed in a real scenario. The higher the number of successful tests, the lower the risk of IT infrastructure failure. Therefore, this is the best KCI among the given options. References =
Integrating KRIs and KPIs for Effective Technology Risk Management
Key Control Indicator (KCI) - CIO Wiki
Infrastructure Issues: Understanding and Mitigating Risks
Which of the following is the PRIMARY reason for managing emerging risk?
The organization is likely to become prone to continuous disruptive events.
Risk assessment methodologies cannot be applied to emerging risk.
Assumptions about the future state are likely to become invalid.
The number of risk scenarios may become uncontrollably high.
While reviewing a contract of a cloud services vendor, it was discovered that the vendor refuses to accept liability for a sensitive data breach. Which of the following controls will BES reduce the risk associated with such a data breach?
Ensuring the vendor does not know the encryption key
Engaging a third party to validate operational controls
Using the same cloud vendor as a competitor
Using field-level encryption with a vendor supplied key
Encryption is a technique that transforms data into an unreadable format using a secret key, so that only authorized parties can access and decrypt the data. Encryption can help to protectsensitive data from unauthorized access or disclosure, especially when the data is stored or transmitted in the cloud1.
Ensuring the vendor does not know the encryption key is a control that will best reduce the risk associated with a data breach, because it can help to:
Prevent the vendor from accessing or disclosing the sensitive data, intentionally or unintentionally
Limit the exposure or impact of the data breach, even if the vendor’s systems or networks are compromised by hackers or malicious insiders
Maintain the confidentiality and integrity of the sensitive data, regardless of the vendor’s liability or responsibility
Enhance the trust and confidence of the customers and stakeholders, who may be concerned about the vendor’s refusal to accept liability for a data breach23
The other options are not as effective as ensuring the vendor does not know the encryption key for reducing the risk associated with a data breach. Engaging a third party to validate operational controls is a control that can help to verify and improve the vendor’s security practices and processes, but it does not guarantee that the vendor will prevent or respond to a data breach adequately or timely. Using the same cloud vendor as a competitor is not a control, but rather a business decision that may increase the risk associated with a data breach, as the vendor may have access to or disclose the sensitive data of both parties, or may favor one party over the other. Using field-level encryption with a vendor supplied key is a control that can help to encrypt specific fields or columns of data, such as names, addresses, or credit card numbers, but it does not prevent the vendor from accessing or disclosing the data, as the vendor has the encryption key4. References =
Encryption - ISACA
Cloud Encryption: Using Data Encryption in The Cloud
Cloud Encryption: Why You Need It and How to Do It Right
Field-Level Encryption - ISACA
[CRISC Review Manual, 7th Edition]
Which of the following is the PRIMARY reason to aggregate risk assessment results from different business units?
To improve communication of risk to senior management
To compare risk profiles across the business units
To allocate budget for risk management resources
To determine overall impact to the organization
Aggregating risk assessment results helps evaluate the total exposure and provides a consolidated view of risk, supporting enterprise-wide decision-making.
Which of the following BEST enables the integration of IT risk management across an organization?
Enterprise risk management (ERM) framework
Enterprise-wide risk awareness training
Robust risk reporting practices
Risk management policies
Understanding the Question:
The question asks what best enables the integration of IT risk management across an organization.
Analyzing the Options:
A. Enterprise risk management (ERM) framework:Provides a comprehensive approach to integrating risk management across the entire organization.
B. Enterprise-wide risk awareness training:Important for education but doesn ' t ensure integration.
C. Robust risk reporting practices:Crucial for communication but not integration.
D. Risk management policies:Necessary but need to be part of an overall framework for effective integration.
ERM Framework:An ERM framework ensures that risk management practices are standardized and integrated throughout the organization. It aligns risk management with business objectives, ensuring that IT risk is considered within the broader context of enterprise risk.
Comprehensive Approach:ERM covers all aspects of risk, including IT, and facilitates a unified approach to managing risk across all departments and levels.
The risk associated with an asset after controls are applied can be expressed as:
a function of the cost and effectiveness of controls.
the likelihood of a given threat.
a function of the likelihood and impact.
the magnitude of an impact.
The risk associated with an asset after controls are applied can be expressed as a function of the likelihood and impact, as it helps to measure and quantify the residual risk level and exposure. Residual risk is the risk that remains after the implementation of controls or risk treatments. Residual risk can be calculated by multiplying the likelihood and impact of a risk event, where likelihood is the probability or frequency of the risk event occurring, and impact is the consequence or severity of the risk event on the asset or objective. Residual risk can be expressed as:
ResidualRisk=Likelihood×Impact
Expressing the risk associated with an asset after controls are applied as a function of the likelihood and impact helps to provide the following benefits:
It enables a data-driven and evidence-based approach to risk assessment and reporting, rather than relying on subjective or qualitative judgments.
It facilitates a consistent and standardized way of measuring and communicating risk levels and exposure across the organization and to the external stakeholders.
It supports the alignment of risk management and control activities with the organizational strategy and objectives, and helps to evaluate the achievement of the desired outcomes.
It helps to identify and prioritize the areas for improvement and enhancement of the risk management and control processes, and guide the development and implementation of corrective or preventive actions.
It provides feedback and learning opportunities for the risk management and control processes, and helps to foster a culture of continuous improvement and innovation.
The other options are not the best ways to express the risk associated with an asset after controls are applied. A function of the cost and effectiveness of controls is a measure of the inputs or outputs of therisk management and control processes, but it does not indicate the risk level or exposure. The likelihood of a given threat is a component of the risk calculation, but it does not reflect the impact or consequence of the threat. The magnitude of an impact is a component of the risk calculation, but it does not reflect the likelihood or probability of the risk event.References=Risk Assessment and Analysis Methods: Qualitative and Quantitative,IT Risk Resources | ISACA,Residual Risk: Definition, Formula & Management - Video & Lesson …
A risk practitioner observes that the fraud detection controls in an online payment system do not perform as expected. Which of the following will MOST likely change as a result?
Impact
Residual risk
Inherent risk
Risk appetite
Residual risk is the amount of risk that remains after the implementation of risk mitigation controls. If the fraud detection controls in an online payment system do not perform as expected, the residual risk will most likely change as a result, because the controls will not be able toreduce the impact or likelihood of the fraud risk as intended. The residual risk may increase or decrease depending on the performance of the controls, and the risk practitioner may need to adjust the risk response strategy accordingly. The other options are not as likely to change as the residual risk, because they are not directly affected by the performance of the controls, but rather depend on other factors, such as the source of the risk, the organization’s objectives, or the external environment, as explained below:
A. Impact is the extent or magnitude of the harm or loss caused by a risk. The impact of the fraud risk in an online payment system may not change as a result of the controls’ performance, becausethe impact is determined by the potential consequences of the fraud, such as financial losses, reputational damage, or legal liabilities, which are independent of the controls.
C. Inherent risk is the amount of risk that exists before the implementation of any risk mitigation controls. The inherent risk of the fraud risk in an online payment system may not change as a result of the controls’ performance, because the inherent risk is determined by the nature and characteristics of the risk, such as the type, source, or frequency of the fraud, which are independent of the controls.
D. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. The risk appetite of the organization may not change as a result of the controls’ performance, because the risk appetite is determined by the organization’s strategy, culture, and values, which are independent of the controls. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.1.1, page 32. What is Residual Risk? Definition, Examples, and More, Residual Risk: Definition, Formula & Management - Video & Lesson Transcript | Study.com, Residual Risk: What It Is and How to Manage It
Which of the following is the BEST method to maintain a common view of IT risk within an organization?
Collecting data for IT risk assessment
Establishing and communicating the IT risk profile
Utilizing a balanced scorecard
Performing and publishing an IT risk analysis
The best method to maintain a common view of IT risk within an organization is to establish and communicate the IT risk profile. An IT risk profile is a document that summarizes the key IT risks that the organization faces or accepts, and their likelihood, impact, and priority. An IT risk profile helps to identify and prioritize the most critical or relevant IT risks, and to align them with the organization’s objectives, strategy, and risk appetite. Establishing and communicating the IT risk profile is the best method to maintain a common view of IT risk, because it helps to create a shared understanding and awareness of the IT risks among the organization’s stakeholders, such as the board, management, business units, and IT functions. Establishing andcommunicating the IT risk profile also helps to facilitate the IT risk decision-making and reporting processes, and to monitor and control the IT risk performance and improvement. Theother options are not the best method to maintain a common view of IT risk, although they may be part of or derived from the IT risk profile. Collecting data for IT risk assessment, utilizing a balanced scorecard, and performing and publishing an IT risk analysis are all activitiesthat can help to support or update the IT risk profile, but they are not the best method to maintain a common view of IT risk. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.1, page 1-15.
Which of the following BEST supports the communication of risk assessment results to stakeholders?
Monitoring of high-risk areas
Classification of risk profiles
Periodic review of the risk register
Assignment of risk ownership
A risk profile is a summary of the key risks that affect an organization, a business unit, a process, or a project. A risk profile can help stakeholders understand the current and potential exposure to various sources of uncertainty, and prioritize the risk response accordingly. Classification of risk profiles is the process of grouping and categorizing risks based on common characteristics, such as source, impact, likelihood, or response strategy. Classification of risk profiles can help communicate risk assessment results to stakeholders by providing a clear and consistent way of presenting and comparing risks across different domains, levels, or perspectives. Classification of risk profiles can also help identify patterns, trends, and interrelationships among risks, and facilitate the allocation of resources and responsibilities for risk management. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.1: Risk Profile, p. 193-195.
Which of the following is MOST important to determine when assessing the potential risk exposure of a loss event involving personal data?
The cost associated with incident response activitiesThe composition and number of records in the information asset
The maximum levels of applicable regulatory fines
The length of time between identification and containment of the incident
When assessing the potential risk exposure of a loss event involving personal data, the most important factor to determine is the composition and number of records in the information asset. The composition refers to the type and sensitivity of the personal data, such as name, address, phone number, email, social security number, health information, financial information, etc. The number of records refers to the quantity and scope of the personal data that is affected by the loss event. The composition and number of records in the information asset determine the severity and impact of the loss event, as they indicate the extent of the harm and damage that can be caused to the data subjects, the organization, and other stakeholders.The composition and number of records in the information asset also influence the cost of the incident responseactivities, the level of the regulatory fines, and the duration of the incident containment and recovery. References = CRISC Review Manual, 7th Edition, page 159.
An IT risk practitioner ' s report includes a treatment plan and projected risk ratings if recommendations are implemented. Once corrective actions are taken by the system owner, which of the following types of risk will the projected risk become?
Control
Inherent
Residual
Compliance
The correct answer isCbecause once corrective actions are implemented, the remaining projected risk becomesresidual risk. Residual risk is the exposure that remains after controls or treatment actions have been applied.
The other options are incorrect:
A. Controlis not a type of risk in this context.
B. Inherentrisk exists before controls are implemented.
D. Compliancerisk is a category of risk, not the remaining level after treatment.
Exact Extracts supporting the answer:
“Residual risk is best reflected as risk remaining after the implementation of new or enhanced controls.”
“The primary objective of a risk management program is to maintain residual risk at an acceptable level.”
“Acceptable risk for an enterprise is achieved when residual risk is within tolerance levels.”
“The risk most likely to be reduced to achieve acceptable risk is residual risk.”
These extracts directly show that once corrective actions are taken, the projected remaining risk isresidual risk.
===========
Which of the following should be the PRIMARY basis for deciding whether to disclose information related to risk events that impact external stakeholders?
Stakeholder preferences
Contractual requirements
Regulatory requirements
Management assertions
Regulatory requirements should be the primary basis for deciding whether to disclose information related to risk events that impact external stakeholders, because they define the rules or standards that the organization must comply with to meet the expectations of the regulators, such as government agencies or industry bodies, and to avoid legal or reputational consequences. A risk event is an occurrence or incident that may cause harm or damage to the organization or its objectives, such as a natural disaster, a cyberattack, or a human error. An external stakeholder is a person or group that has an interest or influence in the organization or its activities, but is not part of the organization, such as customers, suppliers, partners, investors, or regulators. Disclosing information related to risk events that impact external stakeholders is a process of communicating or reporting the relevant facts or details of the risk events to the affected or interested parties. Disclosing information related to risk events may have benefits, such as maintaining trust, transparency, and accountability, but it may also have drawbacks, such as exposing vulnerabilities, losing competitive advantage, or inviting litigation. Therefore, regulatory requirements should be the primary basis for deciding whether to disclose information, as they provide the legal and ethical obligations and boundaries for the disclosure process. Stakeholder preferences, contractual requirements, and management assertions are all possible factors for deciding whether to disclose information related to risk events, but they are not the primary basis, as they may vary or conflict depending on the situation or context, and may not override the regulatory requirements. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 158
Which of the following should be the PRIMARY consideration when identifying and assigning ownership of IT-related risk?
Accountability for control operation
Ability to design controls to mitigate the risk
Accountability for losses due to impact
Span of control within the organization
The correct answer isCbecause the primary consideration when assigning ownership of IT-related risk isaccountability for losses due to impact. Risk ownership should be assigned to the person or function with the authority and accountability for the business consequences if the risk materializes. Ownership should align to business accountability, not just technical control operation.
The other options are less appropriate:
A. Accountability for control operationmay belong to a control owner, but that is not always the same as the risk owner.
B. Ability to design controls to mitigate the riskis relevant to implementation, not primary ownership.
D. Span of control within the organizationmay influence practicality, but it is not the key principle for assigning risk ownership.
Exact Extracts supporting the answer:
“Accountability for business risk related to IT primarily lies with users of IT services.”
“For an IT system supporting a critical business process senior managers should be accountable for the risk.”
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“The best basis for establishing risk ownership is mapping identified risk to a specific business process.”
“During the risk assessment process it is most important to establish a clear line of accountability to ensure that risk ownership is assigned to the appropriate level.”
These extracts show that risk ownership must align with the party accountable for the business impact of the risk. Therefore, the primary consideration isaccountability for losses due to impact.
Which of the following is MOST important when developing key performance indicators (KPIs)?
Alignment to risk responses
Alignment to management reports
Alerts when risk thresholds are reached
Identification of trends
Key performance indicators (KPIs) are quantifiable measures of progress toward an intended result, such as a strategic objective or a desired outcome12.
The most important factor when developing KPIs is the alignment to risk responses, which are the actions taken to address the risks that may affect the achievement of the intended result12.
Alignment to risk responses means that the KPIs should reflect the effectiveness and efficiency of the risk responses, and provide feedback and guidance for improving the risk responses12.
Alignment to risk responses also means that the KPIs should be consistent and compatible with the risk responses, and support the risk management process and objectives12.
The other options are not the most important factor, but rather possible aspects or features of KPIs that may vary depending on the context and purpose of the KPIs. For example:
Alignment to management reports is an aspect of KPIs that relates to the communication and presentation of the KPIs to the relevant stakeholders, such as senior management,board members, or external parties12. However, this aspect does not determine the quality or validity of the KPIs, or the alignment to the intended result12.
Alerts when risk thresholds are reached is a feature of KPIs that relates to the monitoring and control of the KPIs, and the triggering of actions or decisions when the KPIs exceed or fall below a certain level or range12. However, this feature does not define the content or scope of the KPIs, or the alignment to the intended result12.
Identification of trends is a feature of KPIs that relates to the analysis and interpretation of the KPIs, and the identification of patterns or changes in the KPIs over time or across different dimensions12. However, this feature does not specify the criteria or methodology of the KPIs, or the alignment to the intended result12. References =
1: What is a Key Performance Indicator (KPI)? Guide & Examples - Qlik3
2: What is a Key Performance Indicator (KPI)? - KPI.org4
A risk practitioner shares the results of a vulnerability assessment for a critical business application with the business manager. Which of the following is the NEXT step?
Develop a risk action plan to address the findings.
Evaluate the impact of the vulnerabilities to the business application.
Escalate the findings to senior management and internal audit.
Conduct a penetration test to validate the vulnerabilities from the findings.
According to the CRISC Review Manual1, a risk action plan is a document that defines the specific actions, resources, responsibilities, and timelines for implementing the risk responses. A risk action plan should be developed after the results of a vulnerability assessment are shared with the relevant stakeholders, such as the business manager, to address the identified vulnerabilities and mitigate the associated risks. Developing a risk action plan is the next step in the risk management process, as it helps to ensure that the risk responses are executed effectively and efficiently, and that the residual risks are within the acceptable levels. References = CRISC Review Manual1, page 201.
Which of the following is the PRIMARY reason to perform ongoing risk assessments?
Emerging risk must be continuously reported to management.
New system vulnerabilities emerge at frequent intervals.
The risk environment is subject to change.
The information security budget must be justified.
The primary reason to perform ongoing risk assessments is that the risk environment is subject to change. The risk environment is the external and internal factors that influence the level and nature of the risks that the organization faces1. These factors include economic, political, social, technological, legal,and environmental aspects, as well as the organization’s objectives, strategies, culture, and resources2. The risk environment is dynamic and unpredictable, and may change due to various events, trends, ordevelopments that create new or modify existing risks3. Therefore, it is important to perform ongoing risk assessments to identify, analyze, and evaluate the changes in the risk environment, and to adjust the risk response and management accordingly. Ongoing risk assessments help to ensure that the organization’s risk profile is up to date and reflects the current reality, and that the organization’s risk appetite and tolerance are aligned with the changing risk environment4. The other options are not the primary reason to perform ongoing risk assessments, as they are either less comprehensive or less relevant than the changing risk environment. Emerging risk must be continuously reported to management. This option is a consequence or outcome of performing ongoing risk assessments, not a reason for doing so. Emerging risk is a new or evolving risk that has the potential to affect the organization’s objectives, operations, or performance5. Ongoing risk assessments can help to identify and monitor emerging risks, and to report them to management for decision making and action. However, this is not the main reason for performing ongoing risk assessments, as it does not cover the existing or modified risks that may also change due to the risk environment. Newsystem vulnerabilities emerge at frequent intervals. This option is a specific or narrow example of a changing risk environment, not a general or broad reason for performing ongoing risk assessments. System vulnerabilities are weaknesses or flaws in the design, implementation, or operation of information systems that can be exploited by threats to cause harm or loss6. Ongoing risk assessments can help to discover and assess new system vulnerabilities that may emerge due to technological changes, cyberattacks, or human errors. However, this is not the primary reason for performing ongoing risk assessments, as it does not encompass the other types or sources of risks that may also change due to the risk environment. The information security budget must be justified. This option is a secondary or incidental benefit of performing ongoing risk assessments, not a primary or essential reason for doing so. The information security budget is the amount of money that the organization allocates for implementing and maintaining information security measures and controls7. Ongoing risk assessments can help tojustify the information security budget by demonstrating the value and effectiveness of the security measures and controls in reducing the risks, and by identifying the gaps or needs for additional or improved security measures and controls. However, this is not the main reason for performing ongoing risk assessments, as it does not address the purpose or objective of risk assessment, which is to identify, analyze, and evaluate the risks and their impact on the organization. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1, Page 47.
Which of the following BEST promotes commitment to controls?
Assigning control ownership
Assigning appropriate resources
Assigning a quality control review
Performing regular independent control reviews
Commitment to controls is the degree to which the organization and its stakeholders support and adhere to the controls that are designed and implemented to manage or mitigate the risks1. Commitment to controls is essential for ensuring the effectiveness and efficiency of the controls, as well as the achievement of the organization’s objectives and strategies2. The best way to promote commitment to controls is to assign control ownership, which is the process ofidentifying and assigning the person or entity that has the authority and accountability for a control and its management3. By assigning control ownership, the organization can ensure that the controls are properly and promptly designed, implemented, monitored, and maintained, and that the issues or gaps in the controls are identified andresolved4. Assigning control ownership also helps to establish and communicate the roles and responsibilities of the control owners and the other stakeholders, and to enforce the accountability and performance of the control owners5. Assigning appropriate resources, assigning a quality control review, and performing regular independent control reviews are not the best ways to promote commitment to controls, as they donot provide the same level of authority and accountability as assigning control ownership. Assigning appropriate resources is the process of allocating and providing the necessary funds, staff, equipment, or technology that are required to support or enable the controls. Assigning appropriate resources can enhance the quality and performance of the controls, but it does not ensure that the controls are managed or maintained by a specific person or entity. Assigning a quality control review is the process of conducting and documenting a systematic and objective examination and evaluation of the controls, to ensure that they meet the established standards and requirements. Assigning a quality control review can improve the reliability and compliance of the controls, but it does not ensure that the controls are owned or operated by a specific person or entity. Performing regular independent control reviews is the process of performing and reporting an independent and impartial assessment and verification of the controls, to provide assurance and advice on the adequacy and effectiveness of the controls. Performing regular independent control reviews can provide feedback and recommendations for the controls, but it does notensure that the controls are implemented or improved by a specific person or entity. References = 1: Commitment Controls - IMF2: 17 COSO Principles of Effective Internal Control | Weaver3: [Control Ownership - ISACA] 4: [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.1: Control Design, pp. 233-235.] 5: [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.2: Control Implementation, pp. 243-245.] : Resource Allocation - an overview | ScienceDirect Topics : Quality Control Review - an overview | ScienceDirect Topics : IT Risk Resources | ISACA : [Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.1: Risk Identification, pp. 57-59.] : [Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.3: Control Monitoring and Maintenance, pp. 251-253.]
Which of the following would BEST facilitate the maintenance of data classification requirements?
Scheduling periodic audits
Assigning a data custodian
Implementing technical controls over the assets
Establishing a data loss prevention (DLP) solution
Scheduling periodic audits is the best way to facilitate the maintenance of data classification requirements, because it helps to verify and validate that the data are classified and handled according to the established policies, standards, and guidelines, and that the data classification requirements are updated and aligned with the changes in the data environment or regulations. Data classification is a process of categorizing data according to their sensitivity, confidentiality, and value to the organization, and specifying the appropriate handling and protection measures for each category. Data classification requirements are the rules or criteria that define how data should be classified and treated. Scheduling periodic audits is the best way to ensure that the data classification requirements are followed and maintained, and that any issues or gaps are identified and addressed. Assigning a data custodian, implementing technical controls over theassets, and establishing a data loss prevention (DLP) solution are all useful ways to facilitate the maintenance of data classification requirements, but they are not the best way, as they do not provide a comprehensive and independent review and assessment of the data classification process and outcomes. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 158
Which of the following is the MOST important foundational element of an effective three lines of defense model for an organization?
A robust risk aggregation tool set
Clearly defined roles and responsibilities
A well-established risk management committee
Well-documented and communicated escalation procedures
The most important foundational element of an effective three lines of defense model for an organization is clearly defined roles and responsibilities. The three lines of defense model is a framework that outlinesthe roles and responsibilities of different functions or groups within the organization in relation to risk management and internal control1. The three lines of defense are:
The first line of defense, which consists of the operational management and staff who own and manage the risks associated with their activities and processes. They are responsible for identifying, assessing, and mitigating the risks, as well as designing, implementing, and operating the controls.
The second line of defense, which consists of the specialized functions or units that provide oversight, guidance, and support to the first line of defense in managing the risks and controls. They are responsible for developing and maintaining the risk management framework, policies, and standards, as well as monitoring and reporting on the risk and control performance.
The third line of defense, which consists of the internal audit function that provides independent and objective assurance on the effectiveness and efficiency of the risk management and internal control system. They are responsible for evaluating and testing the design and operation of the risks and controls, as well as reporting and recommending improvements to the seniormanagement and the board. Clearly defined roles and responsibilities are essential for ensuring that the three lines of defense model works effectively and efficiently. They help to avoid confusion, duplication, or gaps in the risk management and internal control activities, as well as to ensure accountability, coordination, and communication among the different functions or groups. They also help to establish the appropriate level of independence, authority, and competence for each line of defense, as well as to align the risk management and internal control objectives and strategies with the organization’s goals and values2. The other options are not the most important foundational element of an effective three lines of defense model for an organization, as they are either less relevant or less specific than clearly defined roles and responsibilities. A robust risk aggregation tool set is a set of methods or techniques that enable the organization to collect, consolidate, and analyze the risk data and information from different sources, levels, or perspectives. A robust risk aggregation tool set can help to enhance the risk identification, assessment, and reporting processes, as well as to support the risk decision making and prioritization. However, a robust risk aggregationtool set is not the most important foundational element of an effective three lines of defense model for an organization, as it does not address the roles and responsibilities of the different functions or groups in relation to risk management and internal control. A well-established risk management committee is a group of senior executives or managers who are responsible for overseeing and directing the risk management activities and performance of the organization. A well-established risk management committee can help to ensure the alignment and integration of the risk management objectives and strategies with the organization’s goals and values, as well as to provide guidance and support to the different functions or groups involved in risk management and internal control. However, a well-established risk management committee is not the most important foundational element of an effective three lines of defense model for an organization, as it does not cover theroles and responsibilities of the operational management and staff, the specialized functions or units, or the internal audit function. Well-documented and communicated escalation procedures are the steps or actions that are taken to report and resolve any issues or incidents that may affect the risk management and internal control activities or performance of the organization. Well-documented and communicated escalation procedures can help to ensure the timely and appropriate response and resolution of the issues or incidents, as well as to inform and involve the relevant stakeholders and authorities. However, well-documented and communicated escalation procedures are not the most important foundational element of an effective three lines of defense model for an organization, as they do not define the roles and responsibilities of the different functions or groups in relation to risk management and internal control. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1, Page 85.
Before selecting a final risk response option for a given risk scenario, management should FIRST:
determine control ownership.
evaluate the risk response of similar sized organizations.
evaluate the organization ' s ability to implement the solution.
determine the remediation timeline.
Which of the following would BEST enable mitigation of newly identified risk factors related to internet of Things (loT)?
Introducing control procedures early in the life cycle
Implementing loT device software monitoring
Performing periodic risk assessments of loT
Performing secure code reviews
The BEST way to enable mitigation of newly identified risk factors related to internet of Things (loT) is to introduce control procedures early in the life cycle, because it can help to prevent or reduce the occurrence or impact of the risk factors, and to ensure that the loT devices and systems are designed and developed with security and quality in mind. The control procedures should include requirements analysis, design review, testing, validation, and verification of the loT devices and systems. The other options are not as effective as introducing control procedures early in the life cycle, because:
Option B: Implementing loT device software monitoring is a good way to detect and respond to the risk factors related to loT, but it does not enable mitigation of the risk factors, which is the proactive and preventive approach. Software monitoring is a reactive and corrective measure that may not be able to prevent or reduce the occurrence or impact of the risk factors, especially if they are embedded in the hardware or firmware of the loT devices.
Option C: Performing periodic risk assessments of loT is a necessary way to identify and evaluate the risk factors related to loT, but it does not enable mitigation of the risk factors, which is the action-oriented and solution-focused approach. Risk assessment is an analytical and descriptive process that may not provide the specific and effective measures to address or mitigate the risk factors, especially if they are complex or dynamic.
Option D: Performing secure code reviews is a useful way to verify and improve the security and quality of the software of the loT devices and systems, but it does not enable mitigation of the risk factors related to loT, which may involve more than just the software aspect. The risk factors related to loT may also include the hardware, firmware, network, communication, data, andintegration aspects, which may not be covered or resolved by the code reviews. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 214.
Which of the following process controls BEST mitigates the risk of an employee issuing fraudulent payments to a vendor?
Performing credit verification of third-party vendors prior to payment
Conducting system access reviews to ensure least privilege and appropriate access
Performing regular reconciliation of payments to the check registers
Enforcing segregation of duties between the vendor master file and invoicing
Enforcing segregation of duties between the vendor master file and invoicing is the best process control to mitigate the risk of an employee issuing fraudulent payments to a vendor. This is because segregation of duties is a key internal control that prevents or detects errors, fraud, orabuse by ensuring that no single person can perform incompatible or conflicting tasks. The vendor master file is a database that contains the information and settings for each vendor, such as name, address, bank account, payment terms, etc. Invoicing is the process of generating and sending bills to the vendors for the goods or services they provide. If the same person can access and modify the vendor master file and issue invoices, he or she could create fictitious vendors, alter vendor information, or generate false or duplicate invoices, and then divert the payments to his or her own account. By segregating these duties, the organization can reduce the opportunity and likelihood of such fraudulent activities. According to the CRISC Review Manual 2022, segregation of duties is one of the key IT control objectives and practices1. According to the web search results, segregation of duties between the vendor master file and invoicing is a common and recommended control to prevent vendor fraud
Which of the following MOST effectively limits the impact of a ransomware attack?
Cyber insurance
Cryptocurrency reserve
Data backups
End user training
The most effective way to limit the impact of a ransomware attack is to have data backups. Data backups are copies of the data that are stored in a separate location or device, and can be used to restore the data in case of a loss or corruption. Data backups can help to recover the data that is encrypted or deleted by the ransomware, and to avoid paying the ransom to the attackers. Data backups also help to reduce the downtime and disruption caused by the ransomware attack, and to maintain the business continuity and availability of the data. Cyber insurance, cryptocurrency reserve, and end user training are not the most effective ways to limit the impact of a ransomware attack, as they may not prevent or recover the data loss, and may incur additional costs or risks for the enterprise. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.1.1.1, page 2281
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 657.
Which of the following is MOST important for senior management to review during an acquisition?
Risk appetite and tolerance
Risk framework and methodology
Key risk indicator (KRI) thresholds
Risk communication plan
The most important factor for senior management to review during an acquisition is the risk appetite and tolerance of the target organization. The risk appetite and tolerance reflect the amount and type of risk that an organization is willing to accept in pursuit of its objectives. By reviewing the risk appetite and tolerance of the target organization, senior management can determine if they are compatible with their own, and if the acquisition will create any significant risk exposure or opportunity for the acquiring organization. Risk framework and methodology, key risk indicator (KRI) thresholds, and risk communication plan are other factors that may be reviewed, but they are not as important as the risk appetite and tolerance. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
As part of an overall IT risk management plan, an IT risk register BEST helps management:
align IT processes with business objectives.
communicate the enterprise risk management policy.
stay current with existing control status.
understand the organizational risk profile.
An IT risk register is a document that is used as a risk management tool to identify, analyze, and track the potential risks related to the use of information technology within an organization. An IT risk register helps management to understand the organizational risk profile, which is a comprehensive and structured representation of the risks that the organization faces. The risk profile helps the organization to understand its risk exposure, appetite, and tolerance, and to align its risk management strategy with its business objectives and context. The risk register is an essential input for creating and updating the risk profile, as it provides the data and analysis ofthe risks that need to be prioritized and addressed12. The other options are not the best answers, as they are either not directly shown or derived from the IT risk register. Aligning IT processes with business objectives is a goal of IT governance, which may be influenced by the IT risk register, but not solely determined by it. Communicating the enterprise risk management policy is a responsibility of the senior management and the board of directors, which may use the IT risk register as a reference, but not as the main source. Staying current with existing control status is a function of IT audit and assurance, which may rely on the IT risk register as a basis, but not as the only evidence. References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana; Complete Guide to IT Risk Management | CompTIA
Which of the following describes the relationship between Key risk indicators (KRIs) and key control indicators (KCIS)?
KCIs are independent from KRIs KRIs.
KCIs and KRIs help in determining risk appetite.
KCIs are defined using data from KRIs.
KCIs provide input for KRIs
Key risk indicators (KRIs) are metrics that provide information on the level of exposure to a given risk. Key control indicators (KCIs) are metrics that measure the performance or effectiveness of a control in mitigating a risk. KCIs provide input for KRIs, because they help to assess the residual risk after applying the control. For example, if the KRI is the number of security incidents, and the KCI is the percentage of incidents detected by the intrusion prevention system (IPS), then the KCI provides input for the KRI by showing how well the IPS is reducing the risk of security breaches. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
The MAIN purpose of a risk register is to:
document the risk universe of the organization.
promote an understanding of risk across the organization.
enable well-informed risk management decisions.
identify stakeholders associated with risk scenarios.
The main purpose of a risk register is to enable well-informed risk management decisions by providing a comprehensive and up-to-date record of all the identified risks, their analysis, and their responses. A risk register is a tool that helps to document, monitor, and communicate the status and outcome of risk management activities. A risk register also facilitates the review and evaluation of the effectiveness of risk management processes and controls. Documenting the risk universe, promoting an understanding of risk,and identifying stakeholders are possible benefits of a risk register, but they are not the main purpose. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1.3, page 531
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 640.
Which of the following stakeholders define risk tolerance for an enterprise?
IT compliance and IT audit
Regulators and shareholders
The board and executive management
Enterprise risk management (ERM)
Role of the Board and Executive Management:
The board of directors and executive management are responsible for setting the overall strategic direction of the organization, including its risk tolerance.
They have the authority and oversight necessary to define the levels of risk that the organization is willing to accept in pursuit of its objectives.
Defining Risk Tolerance:
Risk tolerance refers to the acceptable level of variation in performance relative to the achievement of objectives. It is essentially the degree of risk the organization is willing to endure.
The board and executive management establish risk tolerance based on the organization ' s strategic goals, capacity to absorb losses, and regulatory requirements.
Importance of Senior Leadership:
Senior leadership ' s involvement ensures that risk tolerance is aligned with the organization ' s overall strategy and risk appetite.
It provides a top-down approach to risk management, ensuring consistency and alignment across the organization.
Comparing Other Stakeholders:
IT Compliance and IT Audit:These functions are responsible for monitoring and ensuring adherence to policies but do not set risk tolerance.
Regulators and Shareholders:They influence risk management practices through external pressures but do not define risk tolerance directly.
Enterprise Risk Management (ERM):ERM frameworks support the implementation of risk management but the actual definition of risk tolerance comes from the board and executive management.
References:
The CRISC Review Manual discusses how senior management, including the board, is responsible for defining risk tolerance and ensuring it aligns with the organization ' s risk appetite (CRISC Review Manual, Chapter 1: Governance, Section 1.10 Risk Appetite, Tolerance, and Capacity) .
Which of the following practices would be MOST effective in protecting personality identifiable information (Ptl) from unauthorized access m a cloud environment?
Apply data classification policy
Utilize encryption with logical access controls
Require logical separation of company data
Obtain the right to audit
The most effective practice in protecting personally identifiable information (PII) from unauthorized access in a cloud environment is to utilize encryption with logical access controls. Encryption is a technique that transforms the data into an unreadable or unintelligible form, making it inaccessible or unusable by unauthorized parties. Logical access controls are the mechanisms or rules that regulate who can access, view, modify, or delete the data, based on their identity, role, or privilege. By utilizing encryption with logical access controls, the PII can be protected from unauthorized access, disclosure, or theft, both in transit and at rest, in a cloud environment. The other options are not as effective as utilizing encryption with logical access controls, as they are related to the classification, separation, or audit of the data, not the protection or security of the data. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
An engineer has been assigned to conduct data restoration after a server storage failure. However, the procedure was not successful. Which of the following is the MOST probable cause of this situation?
Failure to test the disaster recovery plan (DRP)
Failure to prepare a business continuity plan (BCP)
Insufficient data captured in the business impact analysis (BIA)
Insufficient definition of the recovery point objective (RPO)
The RPO defines how much data loss is acceptable during system failure. If not clearly defined, restoration may skip key data, leading to incomplete recovery. ISACA guidelines highlight that alignment of RPO/RTO with business objectives is critical for viable DR planning
An unauthorized individual has socially engineered entry into an organization ' s secured physical premises. Which of the following is the BEST way to prevent future occurrences?
Employ security guards.
Conduct security awareness training.
Install security cameras.
Require security access badges.
Social engineering is a technique that involves manipulating or deceiving people into performing actions or divulging information that may compromise the security of an organization or its data12.
Entry into an organization’s secured physical premises is a form of physical access that allows an unauthorized individual to access, steal, or damage the organization’s assets, such as equipment, documents, or systems34.
The best way to prevent future occurrences of social engineering entry into an organization’s secured physical premises is to conduct security awareness training, which is an educational program that aims to equip the organization’s employees with the knowledge and skills they need to protect the organization’s data and sensitive information from cyber threats, such as hacking, phishing, or other breaches56.
Security awareness training is the best way because it helps the employees to recognize and resist the common and emerging social engineering techniques, such as tailgating,impersonation, or pretexting, that may be used by the attackers to gain physical access to the organization’s premises56.
Security awareness training is also the best way because it fosters a culture of security and responsibility among the employees, and encourages them to follow the best practices andpolicies for physical security, such as locking the doors, verifying the identity of visitors, or reporting any suspicious activities or incidents56.
The other options are not the best way, but rather possible measures or controls that may supplement or enhance the security awareness training. For example:
Employing security guards is a measure that involves hiring or contracting professional personnel who are trained and authorized to monitor, patrol, and protect the organization’s premises from unauthorized access or intrusion78. However, this measure is not the best way because it may not be sufficient or effective to prevent or deter all types of social engineering attacks, especially if the attackers are able to bypass, deceive, or coerce the security guards78.
Installing security cameras is a control that involves using electronic devices that capture and record the visual images of the organization’s premises, and provide evidence or alerts of any unauthorized access or activity . However, this control is not the best way because it is reactive rather than proactive, and may not prevent or stop the social engineering attacks before they cause any harm or damage to the organization .
Requiring security access badges is a control that involves using physical or electronic cards that identify and authenticate the employees or authorized visitors who are allowed to enter the organization’s premises, and restrict or deny the access to anyone else . However, this control is not the best way because it may not be foolproof or reliable to prevent or detect the social engineering attacks, especially if the attackers are able to steal, forge, or clone the security access badges . References =
1: What is Social Engineering? | Types & Examples of Social Engineering Attacks1
2: Social Engineering: What It Is and How to Prevent It | Digital Guardian2
3: What is physical Social Engineering and why is it important? - Integrity3603
4: What Is Tailgating (Piggybacking) In Cyber Security? - Wlan Labs4
5: What Is Security Awareness Training and Why Is It Important? - Kaspersky5
6: Security Awareness Training - Cybersecurity Education Online | Proofpoint US6
7: Security Guard - Wikipedia7
8: Security Guard Services - Allied Universal8
Security Camera - Wikipedia
Security Camera Systems - The Home Depot
Access Badge - Wikipedia
Access Control Systems - HID Global
An organization is implementing Internet of Things (IoT) technology to control temperature and lighting in its headquarters. Which of the following should be of GREATEST concern?
Insufficient network isolation
Lack of interoperability between sensors
Insecure data transmission protocols
Impact on network performance
IoT devices often lack strong built-in security, and CRISC stresses that the most serious risk isinsufficient network isolation, because it exposes the entire enterprise network. If IoT devices are placed on the same network as business systems, an attacker who compromises an IoT device can move laterally to critical assets. This significantly increases the risk of a major security incident. Insecure transmission protocols are a concern but can be mitigated with encryption layers. Sensor interoperability and performance issues are operational problems but do not pose major security threats. Proper segmentation, isolation, and VLAN separation are the most critical controls for IoT risk reduction.
An organization recently received an independent security audit report of its cloud service provider that indicates significant control weaknesses. What should be done NEXT in response to this report?
Migrate all data to another compliant service provider.
Analyze the impact of the provider ' s control weaknesses to the business.
Conduct a follow-up audit to verify the provider ' s control weaknesses.
Review the contract to determine if penalties should be levied against the provider.
An independent security audit report is a document that provides an objective and comprehensive assessment of the security posture and practices of a cloud service provider (CSP), based on a set of standards, criteria, or frameworks1. An independent security audit report can help an organization to evaluate the risks and benefits of using a CSP, and to ensure that the CSP meets the organization’s security and compliance requirements2.
If an organization receives an independent security audit report of its CSP that indicates significant control weaknesses, the next step that should be done in response to this report is to analyze the impact of the provider’s control weaknesses to the business. This means that the organization should:
Identify and prioritize the business processes, functions, or objectives that depend on or are affected by the CSP’s services
Assess the potential consequences and likelihood of the control weaknesses leading to security incidents, breaches, or losses
Estimate the financial, operational, reputational, or legal impacts of the security incidents, breaches, or losses
Compare the impacts with the organization’s risk appetite and tolerance, and determine the level of risk exposure and acceptance
Communicate the results of the analysis to the relevant stakeholders and decision-makers3
References = What is a Security Audit?, Cloud Security Audit: A 10-Step Checklist, Independent security audits are essential for cloud service providers. Here’s why
Which of the following is the MOST useful information for prioritizing risk mitigation?
Cost of risk mitigation
Asset criticality
Acceptable risk level
Business impact assessment
Business Impact Assessment (BIA):
BIA identifies and evaluates the potential effects of interruptions to critical business operations. It helps determine the priority of risk mitigation efforts based on the potential impact on business functions.
BIA provides detailed information on which processes and systems are most critical to the organization ' s operations and their respective impact levels.
Prioritizing Risk Mitigation:
The results of a BIA guide decision-makers in prioritizing which risks to address first based on their potential to disrupt critical business operations.
Risks that could cause significant operational, financial, or reputational damage are prioritized higher.
Comparing Other Factors:
Cost of Risk Mitigation:Important but secondary to understanding the impact on business operations.
Asset Criticality:Relevant but typically part of the BIA process.
Acceptable Risk Level:Defines the threshold but does not prioritize specific risks.
References:
The CRISC Review Manual discusses how BIA facilitates risk prioritization by identifying critical processes and their impacts (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.7 Business Impact Analysis).
When developing risk treatment alternatives for a Business case, it is MOST helpful to show risk reduction based on:
cost-benefit analysis.
risk appetite.
regulatory guidelines
control efficiency
Cost-benefit analysis is the most helpful tool to show risk reduction based on when developing risk treatment alternatives for a business case, because it compares the expected costs and benefits of each alternative and helps to select the most optimal and feasible one. Cost-benefit analysis also helps to justify the investment and resources required for the risk treatment plan and to demonstrate the value and return of the risk reduction. The other options are not the most helpful tools, although they may also be considered when developing risk treatment alternatives. Risk appetite, regulatory guidelines, and control efficiency are examples of factors or criteria that influence the selection of risk treatment alternatives, but they do not show the risk reduction based on the alternatives. References = CRISC: Certified in Risk & Information Systems Control Sample Questions

TESTED 03 Jun 2026
Copyright © 2014-2026 DumpsTool. All Rights Reserved
