According to IIA guidance, which of the following are typical physical and environmental IT controls?
An internal auditor discusses user-defined default passwords with the database administrator. Such passwords will be reset as soon as the user logs in for the first time, but the initial value of the password is set as "123456." Which of the following are the auditor and the database administrator most likely discussing in this situation?
Which of the following best describes meaningful recommendations for corrective actions?
If an organization has a high amount of working capital compared to the industry average, which of the following is most likely true?
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized data?
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized cate?
With regard to project management, which of the following statements about project crashing is true?
Which of the following bring-your-own-device (BYOD) practices is likely to increase the risk of Infringement on local regulations, such as copyright or privacy laws?
In an organization that produces chocolate, the leadership team decides that the organization will open a milk production facility for its milk chocolate. Which of the following strategies have the organization chosen?
Which of the following would be the strongest control to prevent unauthorized wireless network access?
Which of the following actions should an internal auditor take to clean the data obtained for analytics purposes?
An organization discovered fraudulent activity involving the employee time-tracking system. One employee regularly docked in and clocked out her co-worker friends on their days off, inflating their reported work hours and increasing their wages. Which of the following physical authentication devices would be most effective at disabling this fraudulent scheme?
An organization prepares a statement of privacy to protect customers' personal information. Which of the following might violate the privacy principles?
Internal audit discovered that several loads of pellets were deleted from the scaling database and consequently had no sales invoices, significantly affecting financial statements. An investigation revealed that technicians had deleted the pellet loads accidentally, with no evidence of fraud. Which of the following actions should management implement first?
Which of the following Issues would be a major concern for internal auditors when using a free software to analyze a third-party vendor's big data?
At an organization that uses a periodic inventory system, the accountant accidentally understated the organization s beginning inventory. How would the accountant's accident impact the income statement?
Which would provide the board with the highest level of assurance regarding whether an internal audit function can achieve its objectives?
Which of the following is on example of a smart device security control intended to prevent unauthorized users from gaining access to a device's data or applications?
While auditing an organization's customer call center, an internal auditor notices that Key performance indicators show a positive trend, despite the fact that there have been increasing customer complaints over the same period. Which of the following audit recommendations would most likely correct the cause of this inconsistency?
An internal audit activity is piloting a data analytics model, which aims to identify anomalies in payments to vendors and potential fraud indicators. Which of the following would be the most appropriate criteria for assessing the success of the piloted model?
Which of the following scenarios would require the chief audit executive (CAE) to change the internal audit plan and seek approval for the changes from the board?
A company produces water buckets with the following costs per bucket:
Direct labor = 82
Direct material = $5
Fixed manufacturing = 83.50
Variable manufacturing = 82.50
The water buckets are usually sold for $15. However, the company received a special order for 50.000 water buckets at 311 each.
Assuming there is adequate manufacturing capacity and ail other variables are constant , what is the relevant cost per unit to consider when deciding whether to accept this special order at the reduced price?
Management is designing its disaster recovery plan. In the event that there is significant damage to the organization's IT systems this plan should enable the organization to resume operations at a recovery site after some configuration and data restoration. Which of the following is the ideal solution for management in this scenario?
Which of the following is a benefit from the concept of Internet of Things?
Which of the following is a disadvantage in a centralized organizational structure?
If the chief audit executive (CAE) observes that an international wire was approved to transfer funds to a country embargoed by the government, which of the following would be the most appropriate first step for the CAE to take?
Which of the following should be established by management during implementation of big data systems to enable ongoing production monitoring?
Which of the following data privacy concerns can be attributed specifically to blockchain technologies?
When preparing the annual internal audit plan, which of the following should the chief audit executive (CAE) consider to optimize efficiency and effectiveness?
An internal audit function did not conform with the Global Internal Audit Standards in only one of many engagements, as the engagement was performed with a lack of adequate knowledge of the subject matter. Which of the following is appropriate in relation to declaring conformance with the Standards?
Which of the following best describes the purpose of fixed manufacturing costs?
How can the concept of relevant cost help management with behavioral analyses?
According to Maslow’s hierarchy of needs theory, which of the following best describes a strategy where a manager offers an assignment to a subordinate specifically to support his professional growth and future advancement?
An Internal auditor is using data analytics to focus on high-risk areas during an engagement. The auditor has obtained data and is working to eliminate redundancies in the data. Which of the following statements is true regarding this scenario?
Which of the following attributes of data are cybersecurity controls primarily designed to protect?
An internal auditor has completed the fieldwork of an assurance engagement on the organization's business continuity. The most significant finding is that business requirements were left up to the IT function to decide and implement. As a result, the time to recovery for some critical systems following a disruption is too long, while recovery time of non-critical systems is needlessly prioritized at a significant cost. Which of the following is the most appropriate recommendation to include in the engagement report?
Which of the following IT-related activities is most commonly performed by the second line of defense?
Which of the following statements is true regarding the management-by-objectives (MBO) approach?
An organization with global headquarters in the United States has subsidiaries in eight other nations. If the organization operates with an ethnocentric attitude, which of the following statements is true?
While conducting an audit of the accounts payable department, an internal auditor found that 3% of payments made during the period under review did not agree with the submitted invoices. Which of the following key performance indicators (KPIs) for the department would best assist the auditor in determining the significance of the test results?
According to lIA guidance on IT, which of the following plans would pair the identification of critical business processes with recovery time objectives?
An internal auditor observed that the organization's disaster recovery solution will make use of a cold site in a town several miles away. Which of the following is likely to be a characteristic of this disaster recover/ solution?
The finance department of an organization recently undertook an asset verification exercise. The internal audit function scheduled a review of the IT department’s operations, which includes verifying the existence of computers distributed and their assignment. Can the internal audit function consider relying on the asset verification work performed by the finance department?
Which of the following storage options would give the organization the best chance of recovering data?
Which of the following scenarios would cause a chief audit executive (CAE) to immediately discontinue using any statements that would indicate conformance with the Global Internal Audit Standards in an audit report?
Which of the following would be a concern related to the authorization controls utilized for a system?
An organization with a stable rating, as assessed by International rating agencies, has issued a bond not backed by assets or collateral. Payments of the interests and the principal to bondholders are guaranteed by the organization. Which type of bond did the organization issue?
Which of the following controls would be most efficient to protect business data from corruption and errors?
For employees, the primary value of implementing job enrichment is which of the following?
A manufacturer ss deciding whether to sell or process materials further. Which of the following costs would be relevant to this decision?
With regard to project management, which of the following statements about project crashing Is true?
An organization has an agreement with a third-party vendor to have a fully operational facility, duplicate of the original site and configured to the organization's needs, in order to quickly recover operational capability in the event of a disaster, Which of the following best describes this approach to disaster recovery planning?
Which of the following would an organization execute to effectively mitigate and manage risks created by a crisis or event?
Which of the following describes how human resources can best assist in recruitment efforts for the internal audit function?
Which of the following is true regarding reporting on the quality assurance and improvement program (QAIP)?
According to 11A guidance on IT, which of the following are indicators of poor change management?
1. Inadequate control design.
2. Unplanned downtime.
3. Excessive troubleshooting .
4. Unavailability of critical services.
Which of the following would most likely serve as a foundation for individual operational goats?
During disaster recovery planning, the organization established a recovery point objective. Which of the following best describes this concept?
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization's network incurred by this environment?
An internal auditor discovered that the organization was not in full compliance with a regulatory labeling requirement for one of its products. The responsible manager indicated that the current product labeling has been in use for several years without any problems. If discovered, this regulatory breach could result in significant fines for the organization. What should be the chief audit executive's next course of action?
An intruder posing as the organization's CEO sent an email and tricked payroll staff into providing employees' private tax information. What type of attack was perpetrated?
According to 11A guidance on it; which of the following statements is true regarding websites used in e-commerce transactions?
Which of the following accounting methods is an investor organization likely to use when buying 40 percent of the stock of another organization?
The internal audit function conducted an engagement on maintenance operations of a construction organization and identified several issues of medium importance. The head of maintenance proposed an improvement plan with deadlines and personnel responsible. The internal audit function issued the final report to senior management. Senior management was dissatisfied with the report as they believed that improvement plan deadlines should be considerably shorter. Which of the following should the internal audit function change in the reporting process?
During a payroll audit, the internal auditor is assessing the security of the local area network of the payroll department computers. Which of the following IT controls should the auditor test?
According to IIA guidance on IT, which of the following would be considered a primary control for a spreadsheet to help ensure accurate financial reporting?
Which of the following best describes the chief audit executive's responsibility for assessing the organization's residual risk?
Which of the following IT disaster recovery plans includes a remote site dessgnated for recovery with available space for basic services, such as internet and
telecommunications, but does not have servers or infrastructure equipment?
Which of the following types of date analytics would be used by a hospital to determine which patients are likely to require remittance for additional treatment?
According to 11A guidance on IT, which of the following spreadsheets is most likely to be considered a high-risk user-developed application?
Which of the following best describes the type of control provided by a firewall?
Which of the following would be most likely found in an internal audit procedures manual?
Which of the following statements describes the typical benefit of using a flat organizational structure for the internal audit activity, compared to a hierarchical structure?
According to IIA guidance, which of the following statements is true regarding analytical procedures?
Which type of bond sells at a discount from face value, then increases in value annually until it reaches maturity and provides the owner with the total payoff?
According to IIA guidance, which of the following statements is true regarding penetration testing?
The board is considering outsourcing the internal audit function to an external service provider. Which of the following would always remain the responsibility of the organization?
What is the first step an internal audit function should take to define its organizational structure, deliverables, communication protocols, and resourcing model?
How should a chief audit executive learn about emerging risk areas in an organization?
An internal auditor for a pharmaceutical company as planning a cybersecurity audit and conducting a risk assessment. Which of the following would be considered the most significant cyber threat to the organization?
According to IIA guidance on IT, which of the following strategies would provide the most effective access control over an automated point-of-sale system?
Which of the following is classified as a product cost using the variable costing method?
1. Direct labor costs.
2. Insurance on a factory.
3. Manufacturing supplies.
4. Packaging and shipping costa.
A large retail customer made an offer to buy 10,000 units at a special price of $7 per unit. The manufacturer usually sells each unit for $10. Variable manufacturing costs are $5 per unit and fixed manufacturing costs are $3 per unit. For the manufacturer to accept the offer, which of the following assumptions needs to be true?
Based on lest results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
Which of the following is a primary driver behind the creation and prloritteation of new strategic Initiatives established by an organization?
The internal auditor concluded there was a high likelihood that a significant wind farm development, worth $200 million, would be delayed from its approved schedule. As a result, electricity production would not start on time, leading to considerable financial penalties. Which of the following should be added to the observation to support its clarity and completeness?
Which of the following performance measures disincentives engaging in earnings management?
Which of the following authentication device credentials is the most difficult to revoke when an employee's access rights need to be removed?
Which of the following statements is accurate when planning for an external quality assurance assessment of the internal audit function?
Which of the following organization structures would most likely be able to cope with rapid changes and uncertainties?
An organization suffered significant damage to its local: file and application servers as a result of a hurricane. Fortunately, the organization was able to recover all information backed up by its overseas third-party contractor. Which of the following approaches has been used by the organization?
An internal auditor reviewed Finance Department records to obtain a list of current vendor addresses. The auditor then compared the vendor addresses to a record of employee addresses maintained by the Payroll Department Which of the following types of data analysis did the auditor perform?
Which of the following best describes a transformational leader, as opposed to a transactional leader?
According to IIA guidance, which of the following statements is true with regard to workstation computers that access company information stored on the network?
A chief audit executive (CAE) is developing a strategic plan for the internal audit function. In the last two years, the organization has faced significant IT risks, but the internal audit function has not been able to audit those areas due to a lack of knowledge. How could the CAE address this in the strategic plan?
A third party who provides payroll services to the organization was asked to create audit or “read-only 1 functionalities in their systems. Which of the following statements is true regarding this request?
The chief audit executive hired a consultant to update the internal audit function’s methodologies. Which of the following would best ensure that the internal audit function will adhere to the updated methodologies?
When determining the level of physical controls required for a workstation, which of the following factors should be considered?
Which of the following is most appropriately placed in the financing section of an organization's cash budget?
Which of the following controls is the most effective for ensuring confidentially of transmitted information?
Which of the following application controls is the most dependent on the password owner?
An organization has a declining inventory turnover but an Increasing gross margin rate, Which of the following statements can best explain this situation?
Which of the following statements is true regarding the term "flexible budgets" as it is used in accounting?
In a final audit report, internal auditors drafted the following management action plan with a due date of the last day of the calendar year:
"Plan: A bank reconciliation template has been updated to address issues with formulas incorrectly calculating variances."
Which critical element of the action plan is missing?
During the second half of the audit year, the chief audit executive (CAE) identified significant negative variances to the approved audit budget required to complete the internal audit plan. Which of the following actions should the CAE take?
During her annual performance review, a sales manager admits that she experiences significant stress due to her job but stays with the organization because of the high bonuses she earns. Which of the following best describes her primary motivation to remain in the job?
Which of the following characteristics applies to an organization that adopts a flat structure?
An internal auditor identified a database administrator with an incompatible dual role. Which of the following duties should not be performed by the identified administrator?
Which of the following performance measures includes both profits and investment base?
Which of the following parties is most likely to be responsible for maintaining the infrastructure required to prevent the failure of a real-time backup of a database?
Following an evaluation of an organization's IT controls, an internal auditor suggested improving the process where results are compared against the input. Which of the following IT controls would the Internal auditor recommend?
Which of the following network types should an organization choose if it wants to allow access only to its own personnel?
An internal auditor found the following information while reviewing the monthly financial statements for a wholesaler of safety glasses: Opening inventory: 1,000 units at $2 per unit; Purchased: 5,000 units at $3 per unit; Sold: 3,000 units at $7 per unit. The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
Which observations should the chief audit executive include in the executive summary of the final engagement communication?
Which of the following items represents the first thing that should be done with obtained dote in the data analytics process?
As part of internal audit's risk assessment, a chief audit executive is determining certain factors as part of planning the areas to audit within an organization that makes silicon chips. Which of the following would be considered a subjective factor as part of the risk assessment?
An organization uses the management-by-objectives method whereby employee performance is based on defined goals. Which of the following statements is true regarding this approach?
A financial institution receives frequent and varied email requests from customers for funds to be wired out of their accounts. Which verification activity would best help the institution avoid falling victim to phishing?
Which of the following physical security controls is able to serve as both a detective and preventive control?
Which of the following situations best applies to an organisation that uses a project, rather than a process, to accomplish its business activities?
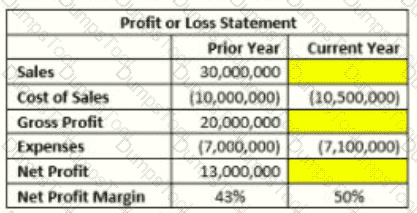
The manager of the sales department wants to Increase the organization's net profit margin by 7% (from 43% in the prior year to 50% in the current year). Given the information provided in the table below, what would be the targeted sales amount for the current year?
An internal audit uncovered high-risk issues that needed to be addressed by the organization. During the exit conference, the audit team discussed the high-risk issues with the manager responsible for addressing them. How should the chief audit executive respond if the manager agrees to correct the issues identified during the audit?
When auditing the account receivables for the first time, an internal auditor noted that the finance team had not—over many accounting periods—reviewed the accounts receivables for debts that could no longer be collected. How should the auditor proceed?
While conducting' audit procedures at the organization's data center an internal auditor noticed the following:
- Backup media was located on data center shelves.
- Backup media was organized by date.
- Backup schedule was one week in duration.
The system administrator was able to present restore logs.
Which of the following is reasonable for the internal auditor to conclude?
An organization's board of directors is particularly focused on positioning, the organization as a leader in the industry and beating the competition. Which of the following strategies offers the greatest alignment with the board's focus?
For which of the following scenarios would the most recent backup of the human resources database be the best source of information to use?
A company records income from an investment in common stock when it does which of the following?
Focus An organization has decided to have all employees work from home. Which of the following network types would securely enable this approach?
Which of these instances accurately describes the responsibilities for big data governance?
Which of the following should be included in a data privacy poky?
1. Stipulations for deleting certain data after a specified period of time.
2. Guidance on acceptable methods for collecting personal data.
3. A requirement to retain personal data indefinitely to ensure a complete audit trail,
4. A description of what constitutes appropriate use of personal data.
A new chief audit executive (CAE) reviews long overdue audit recommendations, which have been repeatedly reported to senior management but have not been implemented, and is unsure which issues should be escalated to the board. Which of the following would serve as the best guide in this scenario?
A bond that matures after one year has a face value of S250,000 and a coupon of $30,000. if the market price of the bond is 5265,000, which of the following would be the market interest rate?
Which of the following physical access control is most likely to be based on ’’something you have" concept?
A chief audit executive (CAE) is calculating the available internal audit resource hours while planning the annual internal audit plan. The CAE needs to calculate the total number of hours available for audits. Which of the following should be deducted in order to have time available only for engagements?
Which of the following intangible assets is considered to have an indefinite life?
According to IIA guidance, which of the following statements is true regarding communication of engagement results?