Secure Shell (SSH) is a protocol that uses encryption and authentication mechanisms to implement network services, such as secure access and file transfer, securely over an insecure network. Which of the following protocols use SSH? (Select all that apply)
Both SNMP Trap and Inform Request are used by managed devices to send alarms to the NMS. Inform Request requires an acknowledgment from the NMS, whereas Trap does not.
After the root bridge is elected on an STP network, which of the following parameters may be compared by ports on non-root bridge nodes to elect the root port? (Select all that apply)
On the OSPF network shown in the figure, all IP addresses can communicate with each other. Then the following configurations are added on R1:
[R1] acl 3000
[R1-acl4-advance-3000] rule deny ip source 10.0.1.1 0.0.0.0
[R1-acl4-advance-3000] rule deny ip source 10.1.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip source 10.3.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip
[R1-acl4-advance-3000] quit
[R1] traffic classifier test
[R1-classifier-test] if-match acl 3000
[R1-classifier-test] quit
[R1] traffic behavior test
[R1-behavior-test] permit
[R1-behavior-test] quit
[R1] traffic policy test
[R1-trafficpolicy-test] classifier test behavior test
[R1-trafficpolicy-test] quit
[R1] interface GE 0/0/1
[R1-GE0/0/1] traffic-policy test outbound
[R1-GE0/0/1] quit
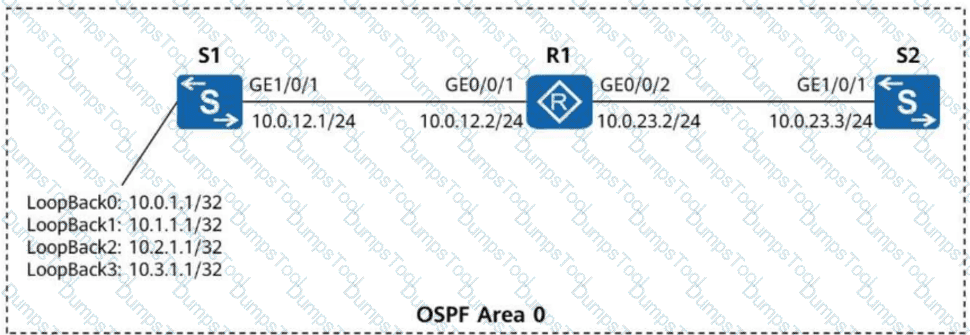
Which IP addresses of S1 can successfully ping 10.0.23.3? (Select all that apply)
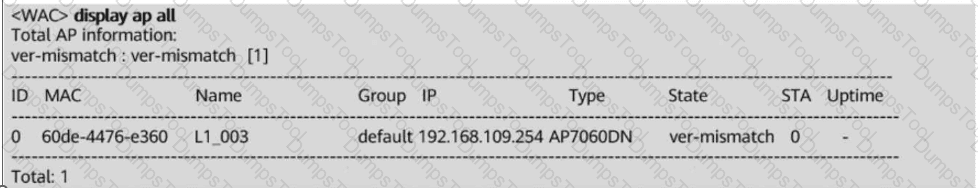
In the WAC + Fit AP networking, an AP fails to go online. The output of the display ap all command run on the WAC is shown below. According to the command output, which of the following is the possible cause of the AP’s failure to go online?
When a Huawei network device functions as an FTP server, which of the following are possible causes of an FTP client failing to log in to the FTP server? (Select all that apply)
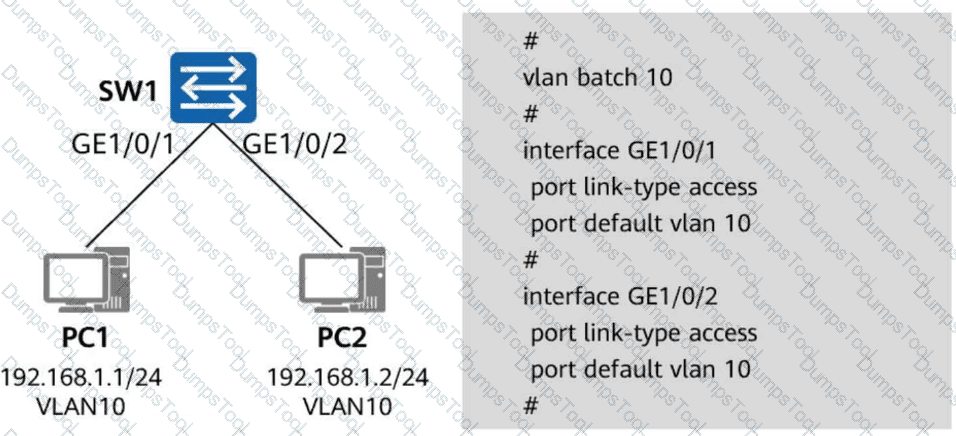
In the figure, both PC1 and PC2 belong to VLAN 10. Interface GE1/0/1 on SW1 is a trunk interface with the default PVID, and interface GE1/0/2 on SW1 is an access interface in VLAN 10. Which of the following statements are true about the forwarding of data frames between PC1 and PC2? (Select all that apply)
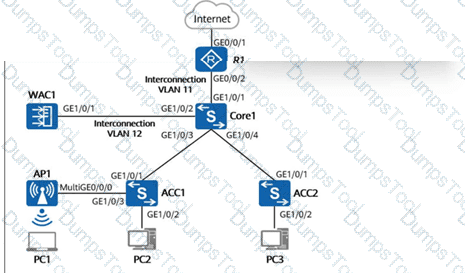
On the campus network shown in the figure below, the core switch Core1 functions as a Layer 3 gateway and as a DHCP server to dynamically assign IP addresses to AP1, PC1, PC2, and PC3. The network below Core1 is a Layer 2 network. WAC1 and R1 are connected to Core1 at Layer 3. AP1 goes online through VLAN 100. The wireless service VLAN is VLAN 101, and the wired service VLANs for PC2 and PC3 are VLAN 102 and VLAN 103, respectively. Additionally, the direct forwarding mode is used for wireless traffic forwarding. If no additional VLANs are allowed on device interfaces, which of the following VLANs must be allowed on GE1/0/1 of ACC1? (Select all that apply)
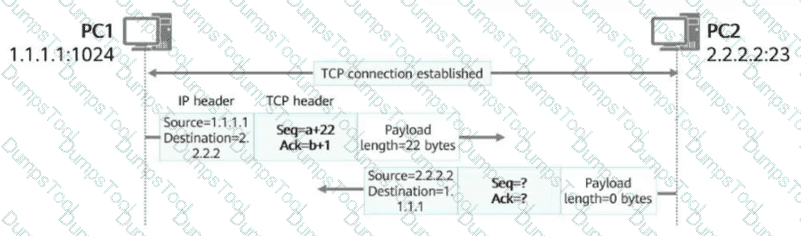
In the figure, a TCP connection has been established between PC1 and PC2. After PC1 sends a data segment to PC2, which of the following is the acknowledgment number in the packet returned by PC2?
In the leader AP networking architecture, the leader AP functions as a WAC and uses the CAPWAP protocol to uniformly manage and configure Fit APs.
In the STP topology shown in the figure, all links have the same path cost, and SW1 is the root bridge. Which of the following ports will become designated ports? (Select all that apply)
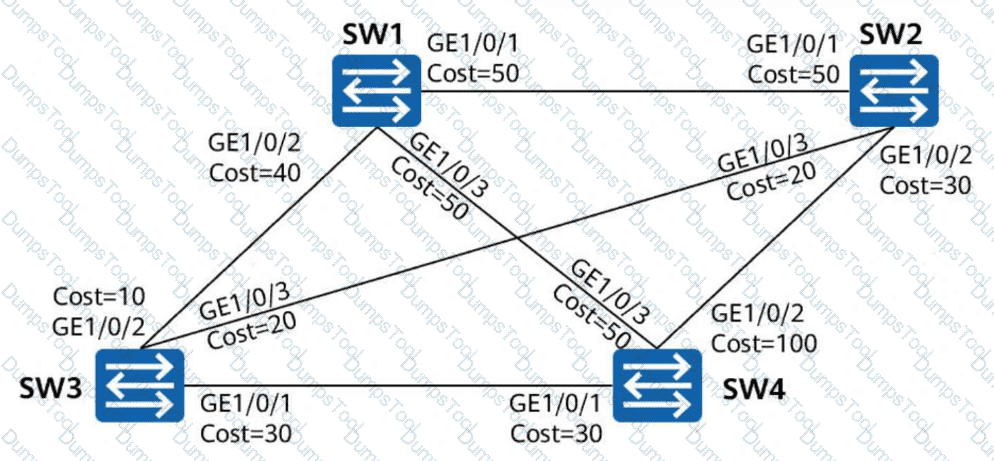
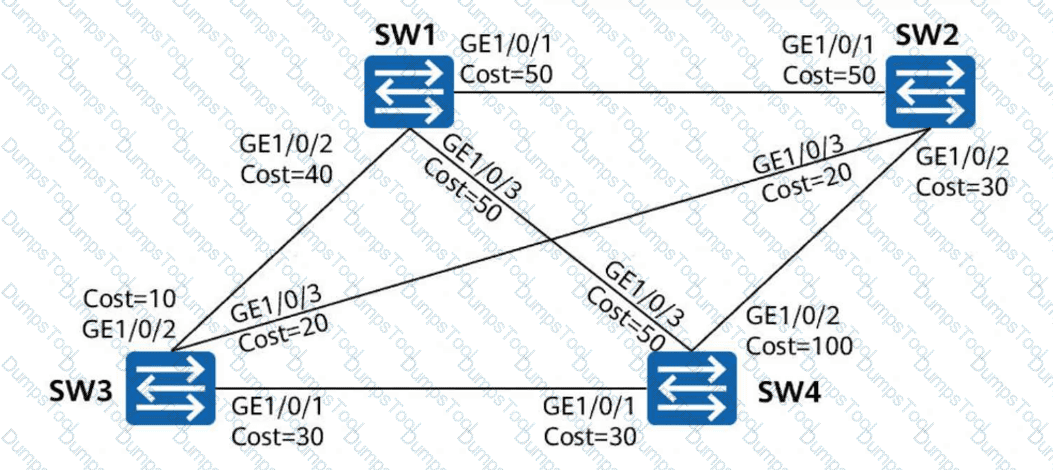
On the switched network shown in the figure, STP is enabled on all devices. SW1 is the root bridge. The port costs are shown in the figure. Other parameters retain the default values. After the network is stable, which of the following paths is used by SW1 to send traffic to SW4?
If a network device has both a static route and a direct route to network 10.1.1.0/24, it uses the direct route preferentially.