HPE6-A84 Question Includes: Single Choice Questions: 60,
A customer wants CPPM to authenticate non-802.1X-capable devices. An admin has created the service shown in the exhibits below:
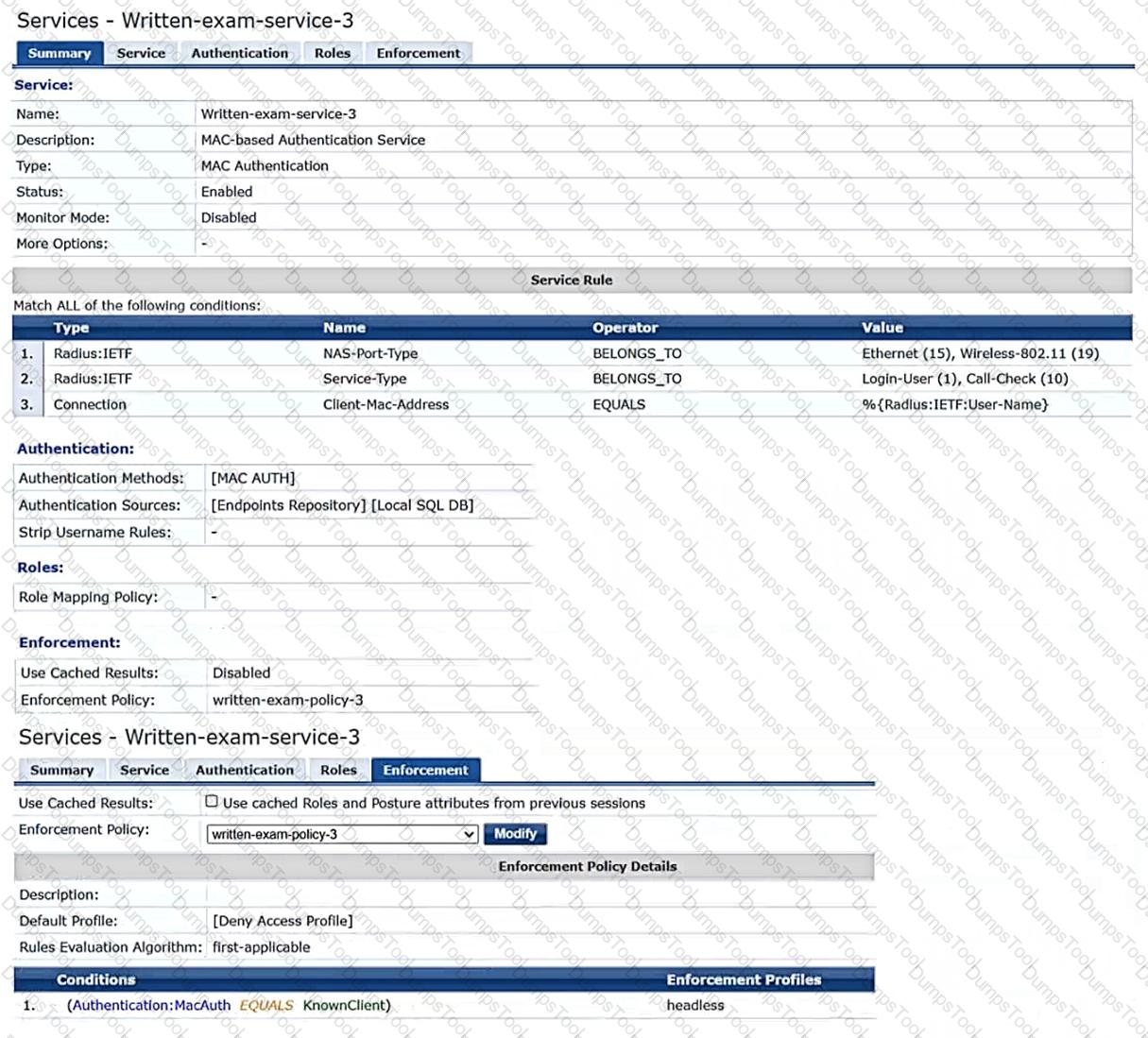
What is one recommendation to improve security?
You want to use Device Insight tags as conditions within CPPM role mapping or enforcement policy rules.
What guidelines should you follow?
You are setting up Aruba ClearPass Policy Manager (CPPM) to enforce EAP-TLS authentication with Active Directory as the authentication source. The company wants to prevent users with disabled accounts from connecting even if those users still have valid certificates.
As the first part of meeting these criteria, what should you do to enable CPPM to determine where accounts are enabled in AD or not?
You are designing an Aruba ClearPass Policy Manager (CPPM) solution for a customer. You learn that the customer has a Palo Alto firewall that filters traffic between clients in the campus and the data center.
Which integration can you suggest?
Refer to the scenario.
A customer has an AOS10 architecture that is managed by Aruba Central. Aruba infrastructure devices authenticate clients to an Aruba ClearPass cluster.
In Aruba Central, you are examining network traffic flows on a wireless IoT device that is categorized as “Raspberry Pi” clients. You see SSH traffic. You then check several more wireless IoT clients and see that they are sending SSH also.
You want a fast way to find a list of all the IoT clients that have used SSH.
What step can you take?
Customers Passed
HP HPE6-A84
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted HP Exam HPE6-A84 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
HP ACA - Network Security HPE6-A84 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing HP ACA - Network Security HPE6-A84 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool HPE6-A84 Aruba Certified Network Security Expert Written Exam Practice Questions is enormous and unmatched!
DumpsTool products focus each and every aspect of the HPE6-A84 certification exam. You’ll find them absolutely relevant to your needs.
DumpsTool’s products are absolutely exam-oriented. They contain HPE6-A84 study material that is Q&As based and comprises only the information that can be asked in actual exam. The information is abridged and up to the task, devoid of all irrelevant and unnecessary detail. This outstanding content is easy to learn and memorize.
DumpsTool offers a variety of products to its clients to cater to their individual needs. DumpsTool Study Guides, HPE6-A84 Exam Dumps, Practice Questions answers in pdf and Testing Engine are the products that have been created by the best industry professionals.
The money back guarantee is the best proof of our most relevant and rewarding products. DumpsTool’s claim is the 100% success of its clients. If they don’t succeed, they can take back their money.
DumpsTool HPE6-A84 Testing Engine delivers you practice tests that have been made to introduce you to the real exam format. Taking these tests also helps you to revise the syllabus and maximize your success prospects.
Yes. DumpsTool’s concentration is to provide you with the state of the art products at affordable prices. Round the year, special packages and discounted prices are also introduced.