A company has HPE Aruba Networking APs running AOS-10 and managed by HPE Aruba Networking Central. The company also has AOS-CX switches. The security team wants you to capture traffic from a particular wireless client. You should capture this client’s traffic over a 15-minute time period and then send the traffic to them in a PCAP file. What should you do?
You have configured an AOS-CX switch to implement 802.1X on edge ports. Assume ports operate in the default auth-mode. VolP phones are assigned to the
"voice" role and need to send traffic that is tagged for VLAN 12.
Where should you configure VLAN 12?
A company needs you to integrate HPE Aruba Networking ClearPass Policy Manager (CPPM) with HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one task you should do to prepare?
A company already uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as the RADIUS server for authenticating wireless clients with 802.1X. Now you are setting up 802.1X on AOS-CX switches to authenticate many of those same clients on wired connections. You decide to copy CPPM's wireless 802.1X service and then edit it with a new name and enforcement policy. What else must you change for authentication to work properly?
You have installed an HPE Aruba Networking Network Analytic Engine (NAE) script on an AOS-CX switch to monitor a particular function.
Which additional step must you complete to start the monitoring?
A company uses both HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one way integrating the two solutions can help the company implement Zero Trust Security?
A company has a variety of HPE Aruba Networking solutions, including an HPE Aruba Networking infrastructure and HPE Aruba Networking ClearPass Policy
Manager (CPPM). The company passes traffic from the corporate LAN destined to the data center through a third-party SRX firewall. The company would like to
further protect itself from internal threats.
What is one solution that you can recommend?
You are setting up HPE Aruba Networking SSE to prohibit users from uploading and downloading files from Dropbox. What is part of the process?
A company wants to turn on Wireless IDS/IPS infrastructure and client detection at the high level on HPE Aruba Networking APs. The company does not want to
enable any prevention settings.
What should you explain about HPE Aruba Networking recommendations?
Refer to the exhibit:
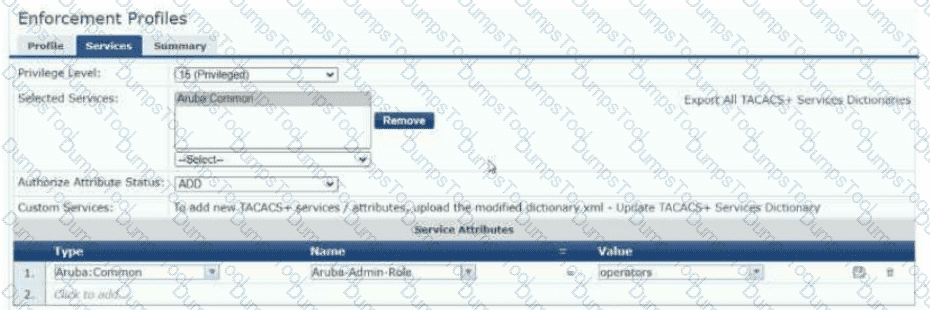
The exhibit shows the TACACS+ enforcement profile that HPE Aruba Networking ClearPass Policy Manager (CPPM) assigns to a manager. When this manager logs into an AOS-CX switch, what does the switch do?
You need to create a rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) role mapping policy that references a ClearPass Device Insight Tag.
Which Type (namespace) should you specify for the rule?
You have set up a mirroring session between an AOS-CX switch and a management station, running Wireshark. You want to capture just the traffic sent in the
mirroring session, not the management station's other traffic.
What should you do?
A company has HPE Aruba Networking APs and AOS-CX switches, as well as HPE Aruba Networking ClearPass. The company wants CPPM to have HTTP User-
Agent strings to use in profiling devices.
What can you do to support these requirements?
Refer to the Exhibit:
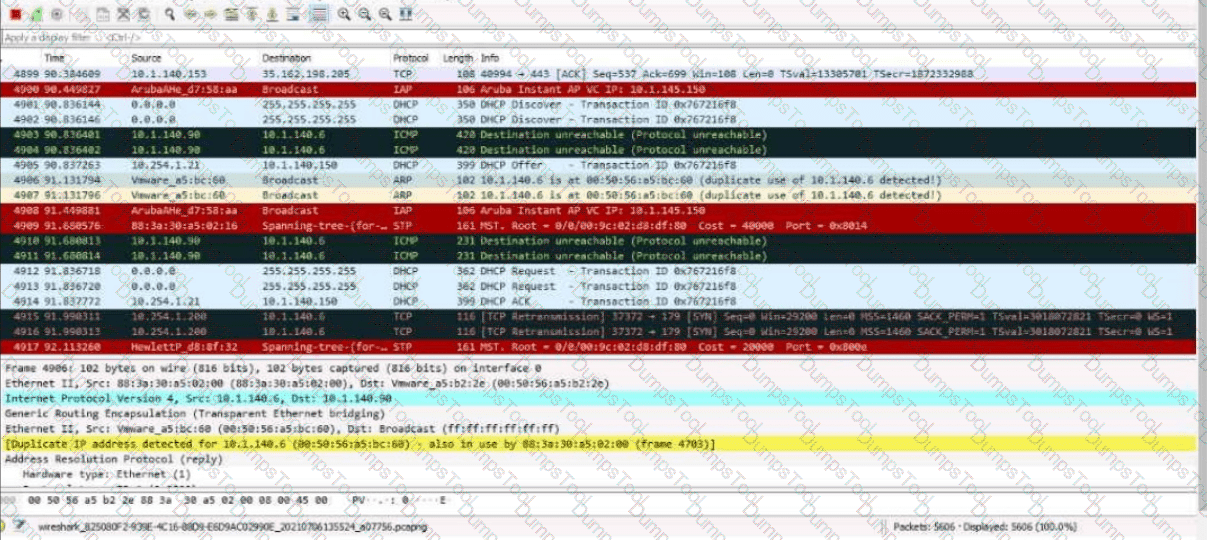
These packets have been captured from VLAN 10. which supports clients that receive their IP addresses with DHCP.
What can you interpret from the packets that you see here?
These packets have been captured from VLAN 10, which supports clients that receive their IP addresses with DHCP. What can you interpret from the packets that you see here?
A company has AOS-CX switches and HPE Aruba Networking APs, which run AOS-10 and bridge their SSIDs. Company security policies require 802.1X on all edge ports, some of which connect to APs. How should you configure the auth-mode on AOS-CX switches?
A company wants HPE Aruba Networking ClearPass Policy Manager (CPPM) to respond to Syslog messages from its Palo Alto Next Generation Firewall (NGFW)
by quarantining clients involved in security incidents.
Which step must you complete to enable CPPM to process the Syslogs properly?
A company wants to apply a standard configuration to all AOS-CX switch ports and have the ports dynamically adjust their configuration based on the identity of
the user or device that connects. They want to centralize configuration of the identity-based settings as much as possible.
What should you recommend?
A security team needs to track a device's communication patterns and identify patterns such as how many destinations the device is accessing.
Which Aruba solution can show this information at a glance?
You are using Wireshark to view packets captured from HPE Aruba Networking infrastructure, but you’re not sure that the packets are displaying correctly. In which circumstance does it make sense to configure Wireshark to ignore protection bits with the IV for the 802.11 protocol?
A company is using HPE Aruba Networking Central SD-WAN Orchestrator to establish a hub-spoke VPN between branch gateways (BGWs) at 1444 site and
VPNCs at multiple data centers.
What is part of the configuration that admins need to complete?
You have enabled "rogue AP containment" in the Wireless IPS settings for a company’s HPE Aruba Networking APs. What form of containment does HPE Aruba Networking recommend?
A company wants to use the HPE Aruba Networking ClearPass OnGuard agent to assign posture to clients.
How do you define the conditions by which a client receives a particular posture?
A company has AOS-CX switches and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company wants switches to implement 802.1X
authentication to CPPM and download user roles.
What is one task that you must complete on the switches to support this use case?
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI security settings, Security Analysis is On, the Data Source is ClearPass Device Insight, and Enable Posture Assessment is On. You see that a device has a Risk Score of 90.
What can you know from this information?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as a TACACS+ server to authenticate managers on its AOS-CX switches. The company wants CPPM to control which commands managers are allowed to enter.
Which service must you add to the managers' TACACS+ enforcement profile?
The security team needs you to show them information about MAC spoofing attempts detected by HPE Aruba Networking ClearPass Policy Manager (CPPM).
What should you do?
A port-access role for AOS-CX switches has this policy applied to it:
plaintext
Copy code
port-access policy mypolicy
10 class ip zoneC action drop
20 class ip zoneA action drop
100 class ip zoneB
The classes have this configuration:
plaintext
Copy code
class ip zoneC
10 match tcp 10.2.0.0/16 eq https
class ip zoneA
10 match ip any 10.1.0.0/16
class ip zoneB
10 match ip any 10.0.0.0/8
The company wants to permit clients in this role to access 10.2.12.0/24 with HTTPS. What should you do?
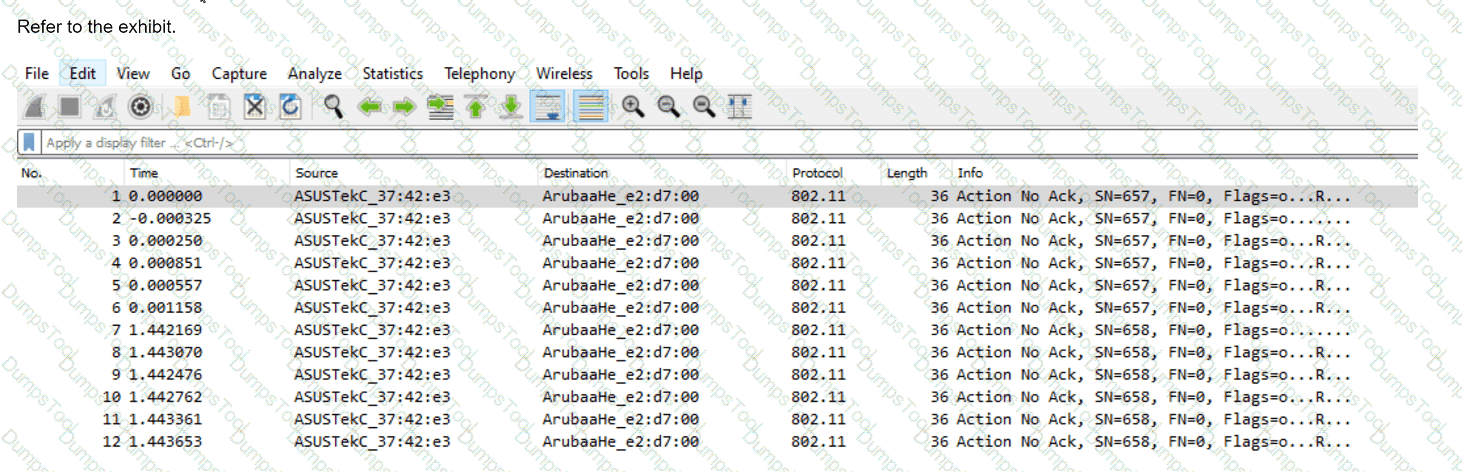
You have downloaded a packet capture that you generated on HPE Aruba Networking Central. When you open the capture in Wireshark, you see the output shown in the
exhibit.
What should you do in Wireshark so that you can better interpret the packets?
A company assigns a different block of VLAN IDs to each of its access layer AOS-CX switches. The switches run version 10.07. The IDs are used for standard
purposes, such as for employees, VolP phones, and cameras. The company wants to apply 802.1X authentication to HPE Aruba Networking ClearPass Policy
Manager (CPPM) and then steer clients to the correct VLANs for local forwarding.
What can you do to simplify setting up this solution?
What is a typical use case for using HPE Aruba Networking ClearPass Onboard to provision devices?
You are helping an organization deploy HPE Aruba Networking SSE. What is one reason to recommend that the company install agents on remote users' devices?
A company is implementing a client-to-site VPN based on tunnel-mode IPsec.
Which devices are responsible for the IPsec encapsulation?
You are setting up HPE Aruba Networking SSE to detect threats as remote users browse the internet.
What is part of this process?
A company is using HPE Aruba Networking Central SD-WAN Orchestrator to establish a hub-spoke VPN between branch gateways (BGWs) at 1164 site and VPNCs at multiple data centers. What is part of the configuration that admins need to complete?
A company has HPE Aruba Networking Central-managed APs. The company wants to block all clients connected through the APs from using YouTube.
Which steps should you take?