A vulnerability scan report has revealed that a user has generated traffic to the website example.com (10.10.10.10) using a weak SSL/TLS version supported by the HTTPS web server.
What can the firewall administrator do to block all outdated SSL/TLS versions on any HTTPS web server to prevent possible attacks on user traffic?
An administrator applied a block-all IPS profile for client and server targets to secure the server, but the database team reported the application stopped working immediately after.
How can an administrator apply IPS in a way that ensures it does not disrupt existing applications in the network?
Refer to the exhibit, which shows a partial troubleshooting command output.
An administrator is extensively using IPsec on FortiGate. Many tunnels show information similar to the output shown in the exhibit.
What can the administrator conclude?
A user reports that their computer was infected with malware after accessing a secured HTTPS website. However, when you check the FortiGate logs, you see that FortiGate did not detect the website as insecure, despite having an SSL certificate and the correct profiles applied on the policy.
How can you ensure that FortiGate can analyze encrypted HTTPS traffic on a website?
Refer to the exhibit, which shows an OSPF network.
Which configuration must the administrator apply to optimize the OSPF database?
An administrator wants to scale the IBGP sessions and optimize the routing table in an IBGP network.
Which parameter should the administrator configure?
Refer to the exhibit, which shows the ADVPN network topology and partial BGP configuration.
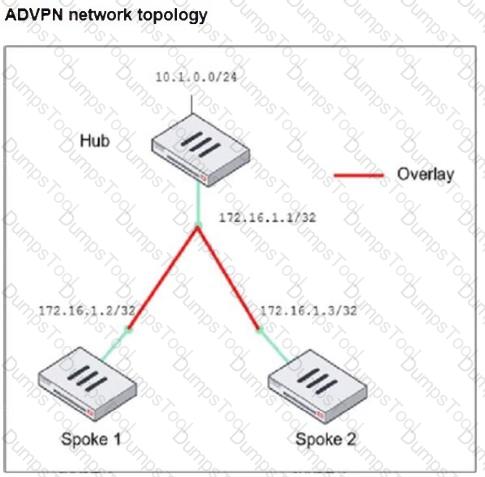
Which two parameters must an administrator configure in the config neighbor range for spokes shown in the exhibit? (Choose two.)
The IT department discovered during the last network migration that all zero phase selectors in phase 2 IPsec configurations impacted network operations.
What are two valid approaches to prevent this during future migrations? (Choose two.)
Which two options should you consider to scale performance using an additional FortiGate?
Which two recommendations prevent invalid paths when using zero phase 2 selectors?
How can you automate updates to firewall policies using a daily updated IP block list?
An administrator is designing an ADVPN network for a large enterprise with spokes that have varying numbers of internet links. They want to avoid a high number of routes and peer connections at the hub.
Which method should be used to simplify routing and peer management?
You are using Virtual eXtensible LAN (VXLAN) extensively on FortiGate. Which specialized acceleration hardware must you use to improve FortiGate performance? (Choose one answer)
Refer to the exhibit.
The partial output of an OSPF command is shown. While checking the OSPF status of FortiGate, you receive the output shown in the exhibit. Based on the output, which two statements about FortiGate are correct? (Choose two answers)
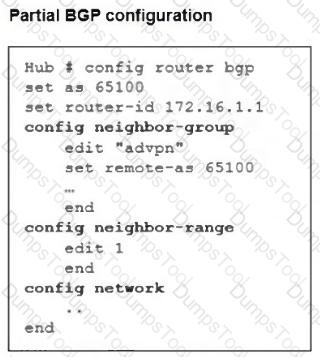
Refer to the exhibits.
The configuration of a user ' s Windows PC, which has a default MTU of 1500 bytes, along with FortiGate interfaces set to an MTU of 1000 bytes, and the results of PC1 pinging server 172.16.0.254 are shown.
Why is the user in Windows PC1 unable to ping server 172.16.0.254 and is seeing the message: Packet needs to be fragmented but DF set?
Refer to the exhibit.
A LAN interface connected from FortiGate to two FortiSwitch devices is shown.
Which two statements about the LAN interface connection shown in the exhibit are correct? (Choose two.)
Refer to the exhibit, which shows the packet capture output of a three-way handshake between FortiGate and FortiManager Cloud.
What two conclusions can you draw from the exhibit? (Choose two.)
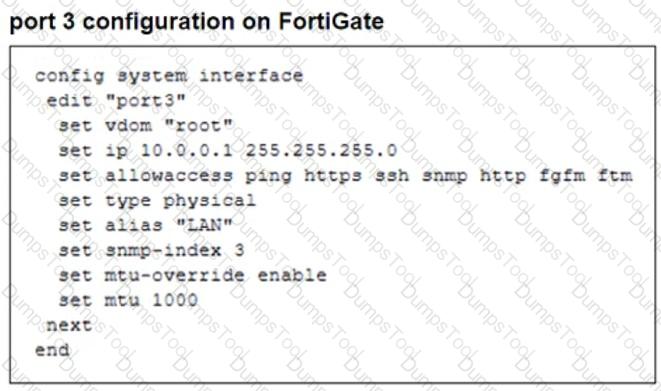
Refer to the exhibit, which contains a partial VPN configuration.
What can you conclude from this VPN IPsec phase 1 configuration?
Refer to the exhibit, which contains the partial output of an OSPF command.
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in the exhibit.
What two conclusions can the administrator draw? (Choose two.)
Which action should you take after applying a block-all IPS profile that caused applications to stop working?
During the maintenance window, an administrator must sniff all the traffic going through a specific firewall policy, which is handled by NP6 interfaces. The output of the sniffer trace provides just a few packets.
Why is the output of sniffer trace limited?
Which three approaches can successfully deploy advanced initial configurations?