An organization must manage ongoing firmware updates for redundant controllers in the network. They will use Cisco Catalyst Center for deployment and visibility. The current environment uses centralized and distributed management approaches. Automation and reporting are critical to minimize operational workload. Which method must be used to manage structured update processes and monitor progress throughout the update cycle?
Refer to the exhibit.
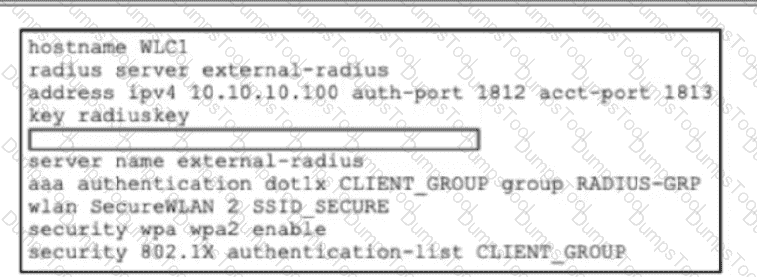
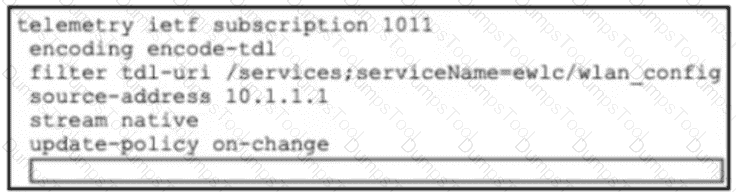
A network administrator is working on a WLC to enable user access for contractor desktops using WPA2-Enterprise using EAP-TTLS. The administrator verified the external authentication configuration and now must test network connectivity. Which code snippet must be added to the box in the code to complete the configuration on the WLC that supports authentication with an external server?
Which new attribute does IEEE 802.11ax introduce when used in wireless local area networks?
Refer to the exhibit.
import requests
import json
API_ENDPOINT = "https://your-api-server.com/api/v1/devices/wireless"
AUTH_TOKEN = "YOUR_SECRET_API_TOKEN"
headers = {
"Accept": "application/json",
"Authorization": f"Bearer {AUTH_TOKEN}"
}
print("Fetching wireless inventory from the API...")
try:
response = requests.get(API_ENDPOINT, headers=headers, timeout=10)
response.raise_for_status()
wireless_inventory_list = response.json()
print("Successfully retrieved and parsed device data.\n")
print("--- Wireless Device Summary ---")
if isinstance(wireless_inventory_list, list) and wireless_inventory_list:
for device in wireless_inventory_list:
mac = device.get("macAddress", "N/A")
ip = device.get("ipAddress", "N/A")
print(f"Device Found - > MAC: {mac}, IP: {ip}")
else:
print("No wireless devices were found in the inventory.")
except requests.exceptions.RequestException as e:
print(f"Error during API request: {e}")
except json.JSONDecodeError:
print("Error: Failed to parse the response from the API. It is not valid JSON.")
A Cisco engineer is analyzing how a dictionary interacts with key-value pairs in a Python script that processes device records collected from a wireless controller. The engineer reviews the construction of the script to interpret the sequence used for data extraction. Which element performs the interaction within the script?
An IT team is deploying Meraki APs at a remote branch and must ensure that they are automatically assigned to the correct network in the Meraki dashboard. The branch is scheduled to receive 20 new APs, and site connectivity to headquarters was set up. Before shipping the APs, the team must make sure that each one is claimed by the intended network for management and monitoring. Which deployment action must they take before physically connecting the APs?
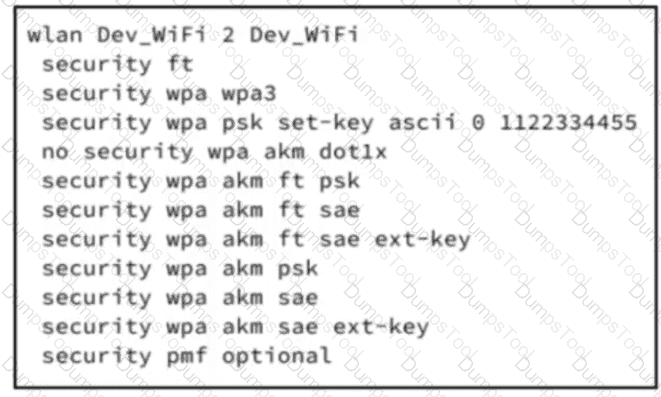
Refer to the exhibit. A startup company has recently moved to new offices and performed a full network refresh. The application development team requested a high-speed reliable wireless network to use for testing real-time applications. Although, the wireless network is Wi-Fi 7 enabled, the wireless clients are connecting using lower speeds. Which configuration must be applied on the WLC to increase throughput?
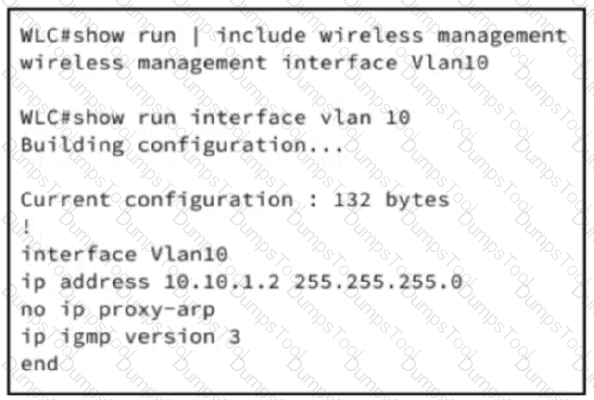
Refer to the exhibit.
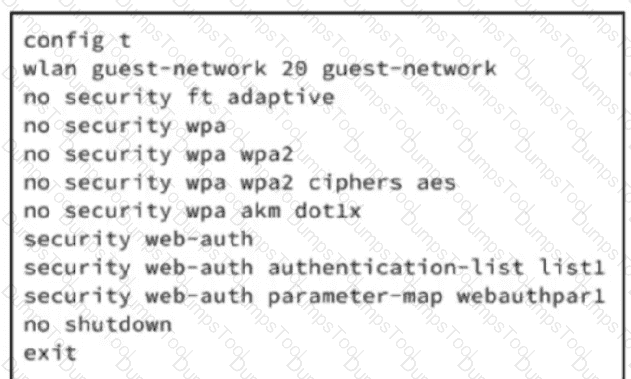
An engineer must configure wireless guest networking for a deployment at site A, which requires support for guest VLAN assignment and assignment for wlan guest-network 20. The controller will provide network segregation and restrict access to internal resources. Based on the configuration commands, which action meets the requirements?
Which Cisco technology leverages machine learning methods and a cloud learning platform that helps to identify critical issues?
A network engineer has been tasked with migrating the management mode of a Cisco 9176 AP named "Cisco-AP053540555" in a large enterprise wireless deployment. The AP is currently managed by a Cisco Catalyst 9800 Series WLC, but the organization is transitioning to Meraki cloud management for centralized control and monitoring. To complete this migration, the engineer needs to change the AP's management mode to Meraki with force and noprompt to skip validations using the CLI on the wireless controller. What command must the engineer use?
Which hierarchy in a YANG data modeling approach describes a relationship in the context of NETCONF device configuration?
Which feature does bridge mode provide in a Cisco wireless mesh architecture?
An organization must manage ongoing firmware updates for redundant controllers in the network. They will use Cisco Catalyst Center for deployment and visibility. The current environment uses centralized and distributed management approaches. Automation and reporting are critical to minimize operational workload. Which method must be used to manage structured update processes and monitor progress throughout the update cycle?
Which solution enables a seamless user experience when roaming in a wireless network?
What is the main benefit of using AI Enhanced RRM on the Cisco Catalyst 9800 wireless controller?
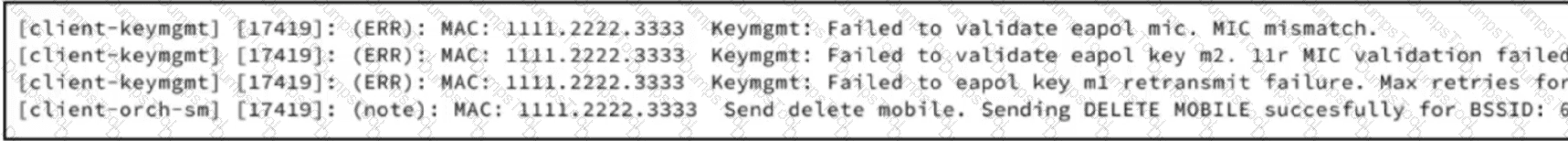
Refer to the exhibit. A network engineer must create a PSK WLAN that will be anchored to the DMZ. After this WLAN is created, users cannot connect to it. Based on the output from the RA trace, which action must the engineer take to resolve the issue?
Which Cisco Ultra-Reliable Wireless Backhaul process enables devices to establish a reliable connection with the next AP along their path before losing connectivity to the current one in a wireless network during roaming?
A network administrator at a marketing company manages a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The WLAN named XYZ-Guest is set up for visitors, and the administrator wants to implement a web authentication (WebAuth) portal using an external server to manage guest access. To ensure seamless and secure guest authentication, the controller must be configured to use an external WebAuth server for the WLAN. The administrator must configure the XYZ-Guest WLAN to use an external WebAuth server with a parameter map named webauth-ext. Which set of Cisco IOS XE commands must be used?
Which process enables seamless Layer 2 handoff in a wireless network during roaming?
Exhibit:
Refer to the exhibit. An organization wants to use Cisco Spaces for location analytics, and an engineer is setting up the Cisco Catalyst 9800 WLC to send location data. The Spaces connector has already been configured and is operational on the WLC. The engineer must now configure the controller to forward telemetry data to the correct Spaces cloud endpoint using TLS to complete the integration. Which CLI command must be added to the box in the code?
Refer to the exhibit.]
An engineer is setting up a new WLC in a branch office. The IT security policy states that all management access must use encrypted protocols, administrators will connect remotely, and network scans will be run to check for any noncompliant management protocol exposure. Which action must the engineer take to achieve the required management access policy?