An administrator is configuring a new profiling policy in Cisco ISE for a printer type that is missing from the profiler feed The logical profile Printers must be used in the authorization rule and the rule must be hit. What must be done to ensure that this configuration will be successful^
When creating a policy within Cisco ISE for network access control, the administrator wants to allow different access restrictions based upon the wireless SSID to which the device is connecting. Which policy condition must be used in order to accomplish this?
A network engineer is in the predeployment discovery phase of a Cisco ISE deployment and must discover the network. There is an existing network management system in the network.
Which type of probe must be configured to gather the information?
Which permission is common to the Active Directory Join and Leave operations?
A policy is being created in order to provide device administration access to the switches on a network. There is a requirement to ensure that if the session is not actively being used, after 10 minutes, it will be disconnected. Which task must be configured in order to meet this requirement?
An engineer is configuring a guest password policy and needs to ensure that the password complexity requirements are set to mitigate brute force attacks. Which two requirement complete this policy? (Choose two)
An administrator adds a new network device to the Cisco ISE configuration to authenticate endpoints to the network. The RADIUS test fails after the administrator configures all of the settings in Cisco ISE and adds the proper configurations to the switch. What is the issue"?
An engineer deploys Cisco ISE and must configure Active Directory to then use information from Active Directory in an authorization policy. Which two components must be configured, in addition to Active Directory groups, to achieve this goat? (Choose two )
Refer to the exhibit.

Which switch configuration change will allow only one voice and one data endpoint on each port?
What should be considered when configuring certificates for BYOD?
An endpoint certificate is mandatory for the Cisco ISE BYOD
Which CLI command must be configured on the switchport to immediately run the MAB process if a non-802.1X capable endpoint connects to the port?
A network engineer must enforce access control using special tags, without re-engineering the network design. Which feature should be configured to achieve this in a scalable manner?
Which two features must be used on Cisco ISE to enable the TACACS. feature? (Choose two)
Which two responses from the RADIUS server to NAS are valid during the authentication process? (Choose two)
An administrator must provide wired network access to unidentified Cisco devices that fail 802.1X authentication. Cisco ISE profiling services must be configured to gather Cisco Discovery Protocol and LLDP endpoint information from a Cisco switch. These configurations were performed:
• configured switches to accept SNMP queries from Cisco ISE
• enabled Cisco Discovery Protocol and LLDP on the switches
• added the switch as a NAD to Cisco ISE
What must be enabled to complete the configuration?
An administrator must deploy the Cisco Secure Client posture agent to employee endpoints that access a wireless network by using URL redirection in Cisco ISE. The compliance module must be downloaded from Cisco and uploaded to the Cisco ISE client provisioning resource. What must be used to upload the compliance module?
The Cisco Wireless LAN Controller and guest portal must be set up in Cisco ISE. These configurations were performed:
• configured all the required Cisco Wireless LAN Controller configurations
• added the wireless controller to Cisco ISE network devices
• created an endpoint identity group
• configured credentials to be sent by email
• configured the SMTP server
• configured an authorization profile with redirection to the guest portal and redirected the access control list
• configured an authentication policy for MAB users
• created an authorization policy
Which two components would be required to complete the configuration? (Choose two.)
ESTION NO: 100
An organization wants to improve their BYOD processes to have Cisco ISE issue certificates to the BYOD endpoints. Currently, they have an active certificate authority and do not want to replace it with Cisco ISE. What must be configured within Cisco ISE to accomplish this goal?
An administrator wants to configure network device administration and is trying to decide whether to use TACACS* or RADIUS. A reliable protocol must be used that can check command authorization Which protocol meets these requirements and why?
An engineer is configuring 802.1X and wants it to be transparent from the users' point of view. The implementation should provide open authentication on the switch ports while providing strong levels of security for non-authenticated devices. Which deployment mode should be used to achieve this?
What sends the redirect ACL that is configured in the authorization profile back to the Cisco WLC?
An engineer must use Cisco ISE profiler services to provide network access to Cisco IP phones that cannot support 802.1X. Cisco ISE is configured to use the access switch device sensor information — system-description and platform-type — to profile Cisco IP phones and allow access.
Which two protocols must be configured on the switch to complete the configuration? (Choose two.)
A network engineer is configuring Cisco TrustSec and needs to ensure that the Security Group Tag is being transmitted between two devices Where in the Layer 2 frame should this be verified?
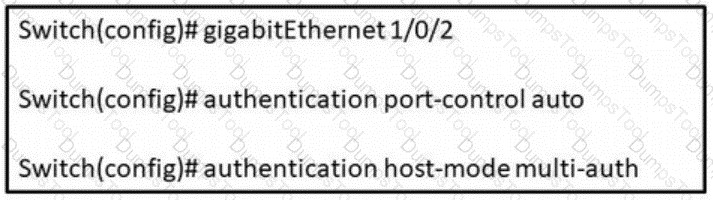
Refer to the exhibit. In which scenario does this switch configuration apply?
NO: 188
During a 802 1X deployment, an engineer must identify failed authentications without causing problems for the connected endpoint. Which command will successfully achieve this''
An engineer is creating a new authorization policy to give the endpoints access to VLAN 310 upon successful authentication The administrator tests the 802.1X authentication for the endpoint and sees that it is authenticating successfully What must be done to ensure that the endpoint is placed into the correct VLAN?
A network administrator is configuring authorization policies on Cisco ISE There is a requirement to use AD group assignments to control access to network resources After a recent power failure and Cisco ISE rebooting itself, the AD group assignments no longer work What is the cause of this issue?
An engineer is assigned to enhance security across the campus network. The task is to enable MAB across all access switches in the network. Which command must be entered on the switch to enable MAB?
An engineer is working with a distributed deployment of Cisco ISE and needs to configure various network probes to collect a set of attributes from the endpoints on the network. Which node should be used to accomplish this task?
An administrator must block access to BYOD endpoints that were onboarded without a certificate and have been reported as stolen in the Cisco ISE My Devices Portal. Which condition must be used when configuring an authorization policy that sets DenyAccess permission?
An engineer is working with a distributed deployment of Cisco ISE and needs to configure various network probes to collect a set of attributes from the used to accomplish this task?
An engineer is configuring web authentication and needs to allow specific protocols to permit DNS traffic. Which type of access list should be used for this configuration?
An administrator must configure Cisco ISE to send CoA requests to a Cisco switch using SNMP. These configurations were already performed:
enabled SNMP on the switch
added the switch to Cisco ISE
configured a network device profile
configured the NAD port detection method
configured the operation to be performed on the switch port
configured an authorization profile
Which two configurations must be performed to send the CoA requests? (Choose two.)
An administrator is configuring a switch port for use with 802 1X What must be done so that the port will allow voice and multiple data endpoints?
An administrator made changes in Cisco ISE and needs to apply new permissions for endpoints that have already been authenticated by sending a CoA packet to the network devices. Which IOS command must be configured on the devices to accomplish this goal?
A user reports that the RADIUS accounting packets are not being seen on the Cisco ISE server.
Which command is the user missing in the switch’s configuration?
An adminístrator is migrating device administration access to Cisco ISE from the legacy TACACS+ solution that used only privilege 1 and 15 access levels. The organization requires more granular controls of the privileges and wants to customize access levels 2-5 to correspond with different roles and access needs. Besides defining a new shell profile in Cisco ISE. what must be done to accomplish this configuration?
What allows an endpoint to obtain a digital certificate from Cisco ISE during a BYOD flow?
While configuring Cisco TrustSec on Cisco IOS devices the engineer must set the CTS device ID and password in order for the devices to authenticate with each other. However after this is complete the devices are not able to property authenticate What issue would cause this to happen even if the device ID and passwords are correct?
An administrator has added a new Cisco ISE PSN to their distributed deployment. Which two features must the administrator enable to accept authentication requests and profile the endpoints correctly, and add them to their respective endpoint identity groups? (Choose two )
Which RADIUS attribute is used to dynamically assign the inactivity active timer for MAB users from the Cisco ISE node'?
An administrator is attempting to join a new node to the primary Cisco ISE node, but receives the error message "Node is Unreachable". What is causing this error?
An engineer is configuring sponsored guest access and needs to limit each sponsored guest to a maximum of two devices. There are other guest services in production that rely on the default guest types. How should this configuration change be made without disrupting the other guest services currently offering three or more guest devices per user?
An administrator needs to connect ISE to Active Directory as an external authentication source and allow the proper ports through the firewall. Which two ports should be opened to accomplish this task? (Choose two)
A new employee just connected their workstation to a Cisco IP phone. The network administrator wants to ensure that the Cisco IP phone remains online when the user disconnects their Workstation from the corporate network Which CoA configuration meets this requirement?
An administrator needs to allow guest devices to connect to a private network without requiring usernames and passwords. Which two features must be configured to allow for this? (Choose two.)
An administrator enables the profiling service for Cisco ISE to use for authorization policies while in closed mode. When the endpoints connect, they receive limited access so that the profiling probes can gather information and Cisco ISE can assign the correct profiles. They are using the default values within Cisco ISE. but the devices do not change their access due to the new profile. What is the problem'?
What are two requirements of generating a single signing in Cisco ISE by using a certificate provisioning portal, without generating a certificate request? (Choose two )
What must match between Cisco ISE and the network access device to successfully authenticate endpoints?
On which port does Cisco ISE present the Admin certificate for posture and client provisioning?
Which port does Cisco ISE use for native supplicant provisioning of a Windows laptop?
A Cisco ISE engineer is creating a certificate authentication profile to be used with machine authentication for the network. The engineer wants to be able to compare the user-presented certificate with a certificate stored in Active Directory. What must be done to accomplish this?
A network engineer is in the predeployment discovery phase o! a Cisco ISE deployment and must discover the network. There is an existing network management system in the network. Which type of probe must be configured to gather the information?
An engineer is assigned to enhance security across the campus network. The task is to enable MAB across all access switches in the network. Which command must be entered on the switch to enable MAB?
An organization has a fully distributed Cisco ISE deployment When implementing probes, an administrator must scan for unknown endpoints to learn the IP-to-MAC address bindings. The scan is complete on one FPSN. but the information is not available on the others. What must be done to make the information available?
An engineer is configuring a new Cisco ISE node. Context-sensitive information must be shared between the Cisco ISE and a Cisco ASA. Which persona must be enabled?
A Cisco device has a port configured in multi-authentication mode and is accepting connections only from hosts assigned the SGT of SGT_0422048549 The VLAN trunk link supports a maximum of 8 VLANS What is the reason for these restrictions?
A network administrator changed a Cisco ISE deployment from pilot to production and noticed that the JVM memory utilization increased significantly. The administrator suspects this is due to replication between the nodes What must be configured to minimize performance degradation?
An administrator is manually adding a device to a Cisco ISE identity group to ensure that it is able to access the network when needed without authentication Upon testing, the administrator notices that the device never hits the correct authorization policy line using the condition EndPoints LogicalProfile EQUALS static_list Why is this occurring?
A company manager is hosting a conference. Conference participants must connect to an open guest SSID and only use a preassigned code that they enter into the guest portal prior to gaining access to the network. How should the manager configure Cisco ISE to accomplish this goal?
Which RADIUS attribute is used to dynamically assign the Inactivity active timer for MAB users from the Cisco ISE node?
A network administrator adds network access devices to Cisco ISE. After a security breach, the management team mandates that all network devices must comply with certain standards. All network devices must authenticate through Cisco ISE. Some devices use nondefault CoA ports.
What must be configured in Cisco ISE?
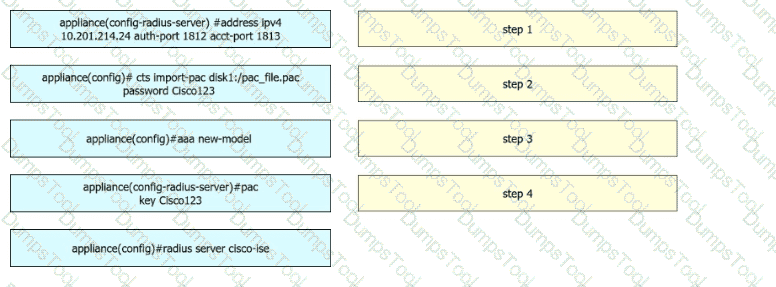
A security engineer configures a Cisco Catalyst switch to use Cisco TrustSec. The engineer must define the PAC key to authenticate the switch to Cisco IISE. Drag and drop the commands from the left into sequence on the right. Not all options are used.
A Cisco ISE administrator must restrict specific endpoints from accessing the network while in closed mode. The requirement is to have Cisco ISE centrally store the endpoints to restrict access from. What must be done to accomplish this task''
An administrator must provide network access to legacy Windows endpoints with a specific device type and operating system version using Cisco ISE profiler services. The ISE profiler services and access switches must be configured to identify endpoints using the dhcp-class-identifier and parameters-request-list attributes from the DHCP traffic. These configurations were performed:
enabled the DHCP probe in Cisco ISE
configured the Cisco ISE PSN interface to receive DHCP packets
configured the attributes in custom profiling conditions
configured a custom profiling policy
configured an authorization rule with permit access
Which action completes the configuration?
An administrator is configuring a Cisco WLC for web authentication Which two client profiling methods are enabled by default if the Apply Cisco ISE Default Settings check box has been selected'? (Choose two.)
A network administrator is configuring a new access switch to use with Cisco ISE for network access control. There is a need to use a centralized server for the reauthentication timers. What must be configured in order to accomplish this task?
An engineer is configuring static SGT classification. Which configuration should be used when authentication is disabled and third-party switches are in use?
Which two actions occur when a Cisco ISE server device administrator logs in to a device? (Choose two)
NO: 37
In which two ways can users and endpoints be classified for TrustSec?
(Choose Two.)
An engineer is configuring a virtual Cisco ISE deployment and needs each persona to be on a different node. Which persona should be configured with the largest amount of storage in this environment?