Which VMware platform does Cisco ACI integrate with to provide enhanced visibility, provide policy integration and deployment, and implement security policies with access lists?
A hacker initiated a social engineering attack and stole username and passwords of some users within a company. Which product should be used as a solution to this problem?
Which Cisco security solution gives the most complete view of the relationships and evolution of Internet domains IPs, and flies, and helps to pinpoint attackers' infrastructures and predict future threat?
Which CoA response code is sent if an authorization state is changed successfully on a Cisco IOS device?
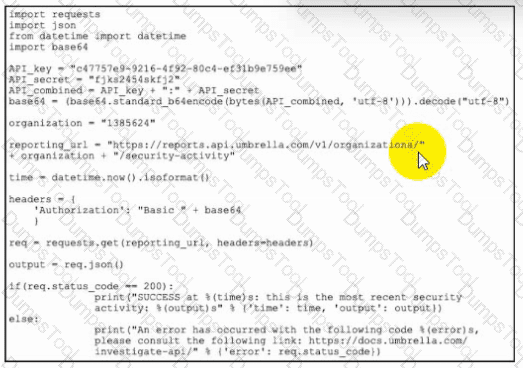
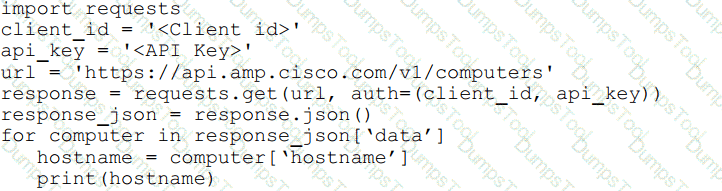
Refer to the exhibit. Which task is the Python script performing by using the Cisco Umbrella API?
Which action configures the IEEE 802.1X Flexible Authentication feature lo support Layer 3 authentication mechanisms?
Which feature within Cisco Umbrella allows for the ability to inspect secure HTTP traffic?
An organization has a requirement to collect full metadata information about the traffic going through their AWS cloud services They want to use this information for behavior analytics and statistics Which two actions must be taken to implement this requirement? (Choose two.)
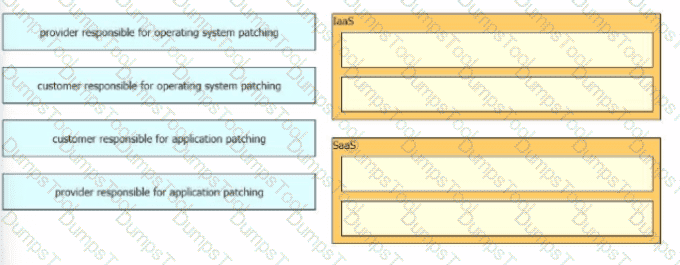
An organization is selecting a cloud architecture and does not want to be responsible for patch management of the operating systems. Why should the organization select either Platform as a Service or Infrastructure as a Service for this environment?
A Cisco FTD engineer is creating a new IKEv2 policy called s2s00123456789 for their organization to allow for additional protocols to terminate network devices with. They currently only have one policy established and need the new policy to be a backup in case some devices cannot support the stronger algorithms listed in the primary policy. What should be done in order to support this?
A company is experiencing exfiltration of credit card numbers that are not being stored on-premise. The
company needs to be able to protect sensitive data throughout the full environment. Which tool should be used
to accomplish this goal?
What provides the ability to program and monitor networks from somewhere other than the DNAC GUI?
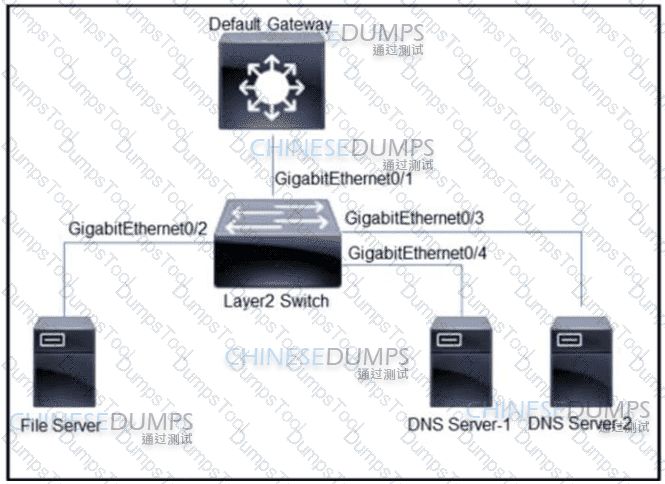
Refer to the exhibit. All servers are in the same VLAN/Subnet. DNS Server-1 and DNS Server-2 must communicate with each other, and all servers must communicate with default gateway multilayer switch. Which type of private VLAN ports should be configured to prevent communication between DNS servers and the file server?
An organization received a large amount of SPAM messages over a short time period. In order to take action on the messages, it must be determined how harmful the messages are and this needs to happen dynamically.
What must be configured to accomplish this?
What is the process In DevSecOps where all changes In the central code repository are merged and synchronized?
An engineer is configuring guest WLAN access using Cisco ISE and the Cisco WLC. Which action temporarily gives guest endpoints access dynamically while maintaining visibility into who or what is connecting?
An engineer enabled SSL decryption for Cisco Umbrella intelligent proxy and needs to ensure that traffic is inspected without alerting end-users. Which action accomplishes this goal?
With which components does a southbound API within a software-defined network architecture communicate?
Which network monitoring solution uses streams and pushes operational data to provide a near real-time view
of activity?
Which action configures the IEEE 802.1X Flexible Authentication feature to support Layer 3 authentication mechanisms?
A switch with Dynamic ARP Inspection enabled has received a spoofed ARP response on a trusted interface.
How does the switch behave in this situation?
For a given policy in Cisco Umbrella, how should a customer block websites based on a custom list?
An engineer is trying to decide whether to use Cisco Umbrella, Cisco CloudLock, Cisco Stealthwatch, or Cisco AppDynamics Cloud Monitoring for visibility into data transfers as well as protection against data exfiltration Which solution best meets these requirements?
How does Cisco Workload Optimization portion of the network do EPP solutions solely performance issues?
Which solution is more secure than the traditional use of a username and password and encompasses at least two of the methods of authentication?
When web policies are configured in Cisco Umbrella, what provides the ability to ensure that domains are blocked when they host malware, command and control, phishing, and more threats?
Which ID store requires that a shadow user be created on Cisco ISE for the admin login to work?
Which Cisco platform provides an agentless solution to provide visibility across the network including encrypted traffic analytics to detect malware in encrypted traffic without the need for decryption?
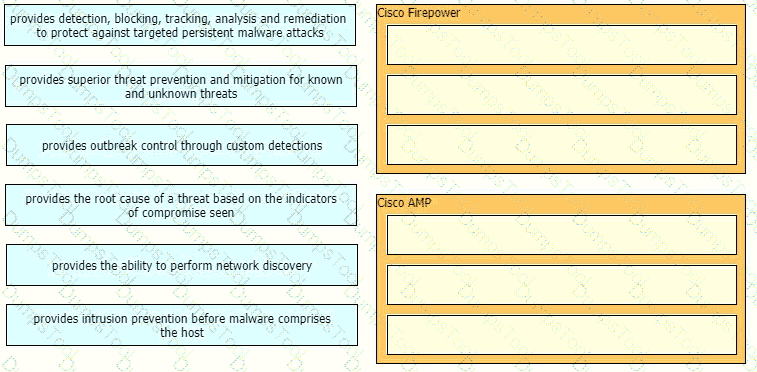
Drag and drop the capabilities of Cisco Firepower versus Cisco AMP from the left into the appropriate category on the right.
A security engineer is tasked with configuring TACACS on a Cisco ASA firewall. The engineer must be able to access the firewall command line interface remotely. The authentication must fall back to the local user database of the Cisco ASA firewall. AAA server group named TACACS-GROUP is already configured with TACACS server IP address 192.168.10.10 and key C1sc0512222832!. Which configuration must be done next to meet the requirement?
Which ASA deployment mode can provide separation of management on a shared appliance?
An engineer enabled SSL decryption for Cisco Umbrella intelligent proxy and needs to ensure that traffic is inspected without alerting end-users.
Which feature is used in a push model to allow for session identification, host reauthentication, and session termination?
Which firewall mode does a Cisco Adaptive Security Appliance use to inspect Layer 2 traffic?
Which security solution uses NetFlow to provide visibility across the network, data center, branch
offices, and cloud?
Refer to the exhibit.
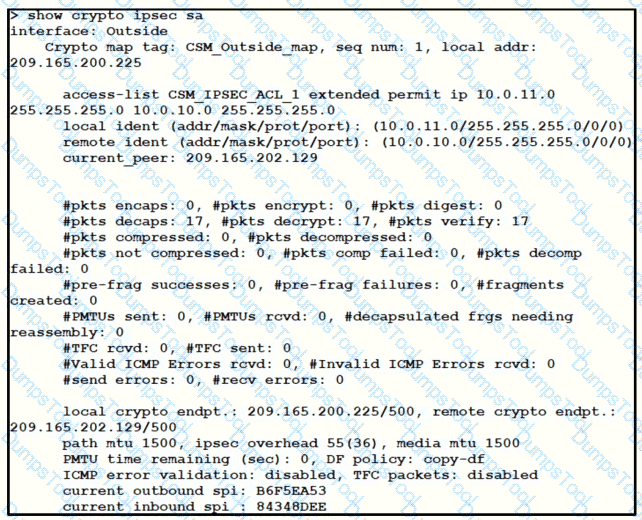
Traffic is not passing through IPsec site-to-site VPN on the Firepower Threat Defense appliance. What is causing this issue?
Drag and drop the security responsibilities from the left onto the corresponding cloud service models on the right.
Which system facilitates deploying microsegmentation and multi-tenancy services with a policy-based container?
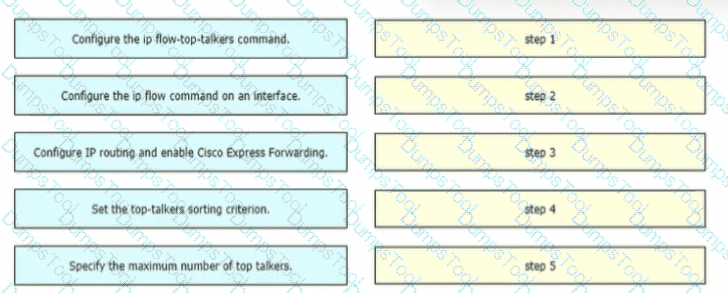
A network engineer is configuring NetFlow top talkers on a Cisco router Drag and drop the steps in the process from the left into the sequence on the right
A web hosting company must upgrade its older, unsupported on-premises servers. The company wants a cloud solution in which the cloud provider is responsible for:
Server patching
Application maintenance
Data center security
Disaster recovery
Which type of cloud meets the requirements?
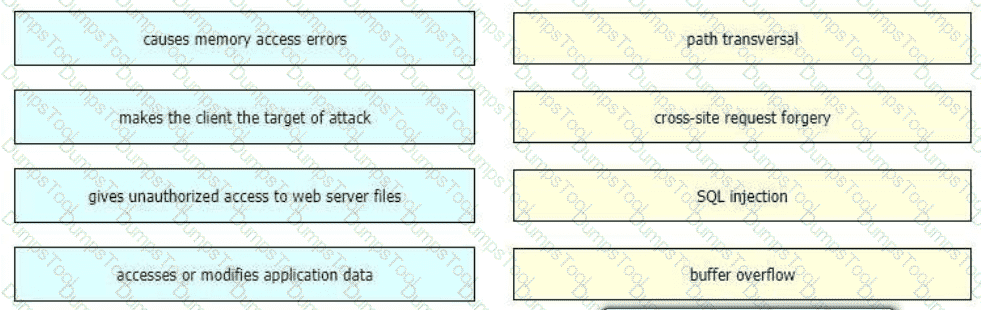
Drag and drop the exploits from the left onto the type of security vulnerability on the right.
Which two services must remain as on-premises equipment when a hybrid email solution is deployed? (Choose two)
A Cisco Secure Email Gateway network administrator has been tasked to use a newly installed service to help create policy based on the reputation verdict. During testing, it is discovered that the Secure Email Gateway is not dropping files that have an undetermined verdict. What is causing this issue?
Which two global commands must the network administrator implement to limit the attack surface of an internet-facing Cisco router? (Choose two.)
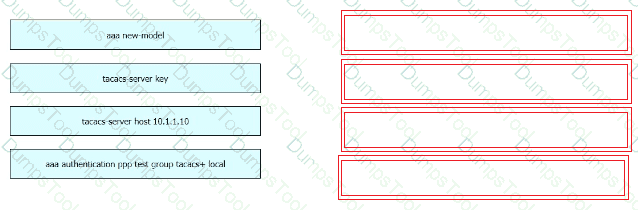
Refer to the exhibit.
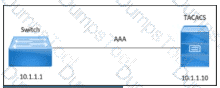
An engineer must configure a Cisco switch to perform PPP authentication via a TACACS server located at IP address 10.1.1.10. Authentication must fall back to the local database using the username LocalUser and password C1Sc0451069341l if the TACACS server is unreachable.
Drag and drop the commands from the left onto the corresponding configuration steps on the right.
After deploying a Cisco ESA on your network, you notice that some messages fail to reach their destinations.
Which task can you perform to determine where each message was lost?
Which cloud model is a collaborative effort where infrastructure is shared and jointly accessed by several organizations from a specific group?
Which two capabilities of Integration APIs are utilized with Cisco Catalyst Center? (Choose two.)
Which capability is exclusive to a Cisco AMP public cloud instance as compared to a private cloud instance?
With Cisco AMP for Endpoints, which option shows a list of all files that have been executed in your
environment?
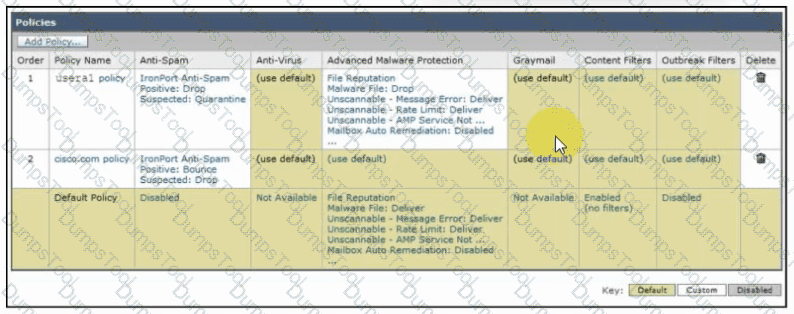
Refer to the exhibit. An engineer must configure an incoming mail policy so that each email sent from usera1@example.com to a domain of @cisco.com is scanned for antispam and advanced malware protection. All other settings will use the default behavior. What must be configured in the incoming mail policy to meet the requirements?
What must be configured in Cisco ISE to enforce reauthentication of an endpoint session when an endpoint is
deleted from an identity group?
Refer to the exhibit.
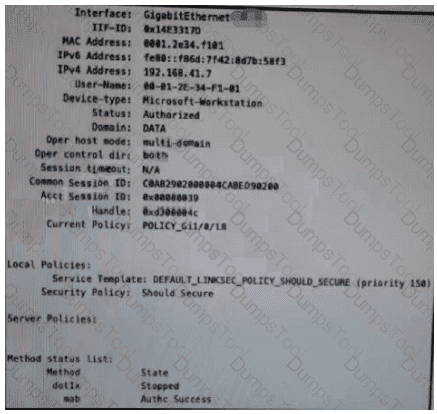
Which configuration item makes it possible to have the AAA session on the network?
Which parameter is required when configuring a Netflow exporter on a Cisco Router?
Email security has become a high-priority task for a security engineer at a large multi-national organization due to ongoing phishing campaigns. To help control this, the engineer has deployed an Incoming Content Filter with a URL reputation of (-10.00 to -6.00) on the Cisco Secure Email Gateway. Which action will the system perform to disable any links in messages that match the filter?
A network engineer has been tasked with adding a new medical device to the network. Cisco ISE is being used as the NAC server, and the new device does not have a supplicant available. What must be done in order to securely connect this device to the network?
Which VPN technology supports a multivendor environment and secure traffic between sites?
An engineer needs to add protection for data in transit and have headers in the email message Which configuration is needed to accomplish this goal?
Which two capabilities of Integration APIs are utilized with Cisco DNA center? (Choose two)
Which technology must be used to implement secure VPN connectivity among company branches over a
private IP cloud with any-to-any scalable connectivity?
Which service allows a user export application usage and performance statistics with Cisco Application Visibility
and control?
Which two request of REST API are valid on the Cisco ASA Platform? (Choose two)
Which solution allows an administrator to provision, monitor, and secure mobile devices on Windows and Mac computers from a centralized dashboard?
An engineer must configure Cisco AMP for Endpoints so that it contains a list of files that should not be executed by users. These files must not be quarantined. Which action meets this configuration requirement?
Which type of API is being used when a controller within a software-defined network architecture dynamically
makes configuration changes on switches within the network?
Which two products are used to forecast capacity needs accurately in real time? (Choose two.)
In which two customer environments is the Cisco Secure Web Appliance Virtual connector traffic direction method selected? (Choose two.)
An engineer integrates Cisco FMC and Cisco ISE using pxGrid Which role is assigned for Cisco FMC?
What provides total management for mobile and PC including managing inventory and device tracking, remote view, and live troubleshooting using the included native remote desktop support?
Which metric is used by the monitoring agent to collect and output packet loss and jitter information?
Refer to the exhibit.
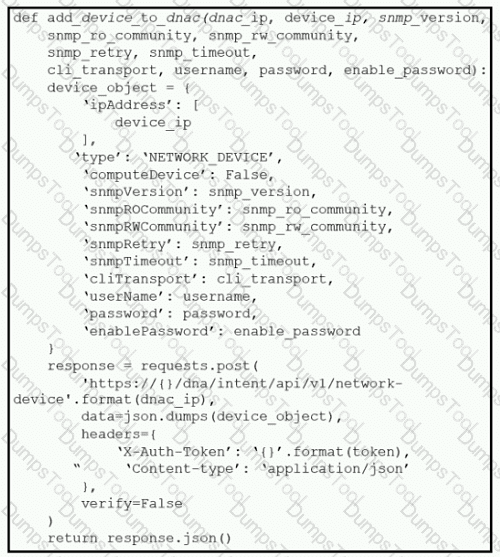
What is the result of this Python script of the Cisco DNA Center API?
An administrator is establishing a new site-to-site VPN connection on a Cisco IOS router. The organization
needs to ensure that the ISAKMP key on the hub is used only for terminating traffic from the IP address of
172.19.20.24. Which command on the hub will allow the administrator to accomplish this?
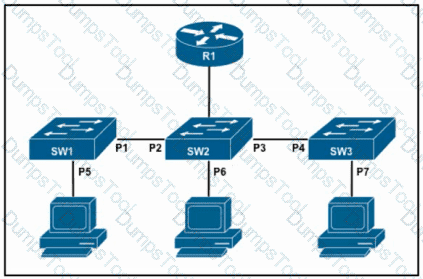
Refer to the exhibit. The DHCP snooping database resides on router R1, and dynamic ARP inspection is configured only on switch SW2. Which ports must be configured as untrusted so that dynamic ARP inspection operates normally?
Which posture assessment requirement provides options to the client for remediation and requires the
remediation within a certain timeframe?
Which Cisco ASA Platform mode disables the threat detection features except for Advanced Threat Statistics?
For which two conditions can an endpoint be checked using ISE posture assessment? (Choose two)
Which command is used to log all events to a destination colector 209.165.201.107?
An engineer is implementing NTP authentication within their network and has configured both the client and server devices with the command ntp authentication-key 1 md5 Cisc392368270. The server at 1.1.1.1 is attempting to authenticate to the client at 1.1.1.2, however it is unable to do so. Which command is required to enable the client to accept the server’s authentication key?
Which Cisco solution integrates industry-leading artificial intelligence and machine learning analytics and an assurance database to review the security posture and maintain visibility of an organization’s cloud environment?
Which solution supports high availability in routed or transparent mode as well as in northbound and
southbound deployments?
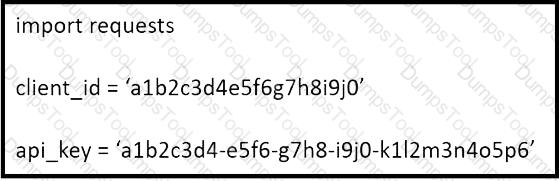
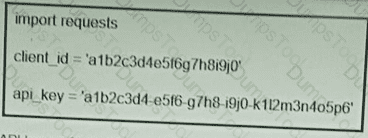
Refer to the exhibit.
What will happen when the Python script is executed?
An engineer must modify a policy to block specific addresses using Cisco Umbrella. The policy is created already and is actively u: of the default policy elements. What else must be done to accomplish this task?
How does Cisco Stealthwatch Cloud provide security for cloud environments?
An engineer configures new features within the Cisco Umbrella dashboard and wants to identify and proxy traffic that is categorized as risky domains and may contain safe and malicious content. Which action accomplishes these objectives?
When a next-generation endpoint security solution is selected for a company, what are two key
deliverables that help justify the implementation? (Choose two.)
Which API technology with SDN architecture is used to communicate with a controller and network devices such as routers and switches?
Refer to the exhibit.
What does the API key do while working with https://api.amp.cisco.com/v1/computers?
Which two request methods of REST API are valid on the Cisco ASA Platform? (Choose two.)
Which term describes when the Cisco Firepower downloads threat intelligence updates from Cisco Talos?
An organization is trying to improve their Defense in Depth by blocking malicious destinations prior to a
connection being established. The solution must be able to block certain applications from being used within the network. Which product should be used to accomplish this goal?
Which key feature of Cisco ZFW is unique among other Cisco IOS firewall solutions?
Which technology must De used to Implement secure VPN connectivity among company branches over a private IP cloud with any-to-any scalable connectivity?
An organization uses Cisco FMC to centrally manage multiple Cisco FTD devices. The default management
port conflicts with other communications on the network and must be changed. What must be done to ensure
that all devices can communicate together?
Which two kinds of attacks are prevented by multifactor authentication? (Choose two)
Refer to the exhibit. What function does the API key perform while working with https://api.amp.cisco.com/v1/computers?
An engineer has enabled LDAP accept queries on a listener. Malicious actors must be prevented from quickly
identifying all valid recipients. What must be done on the Cisco ESA to accomplish this goal?
Which method is used to deploy certificates and configure the supplicant on mobile devices to gain access to
network resources?
Which two Cisco ISE components must be configured for BYOD? (Choose two.)
A company identified a phishing vulnerability during a pentest. What are two ways the company can protect employees from the attack? (Choose two.)
Which two criteria must a certificate meet before the WSA uses it to decrypt application traffic? (Choose two.)
Which type of API is being used when a security application notifies a controller within a software-defined network architecture about a specific security threat?
Which CLI command is used to enable URL filtering support for shortened URLs on the Cisco Secure Email Gateway?
Which statement describes a traffic profile on a Cisco Next Generation Intrusion Prevention System?
Which function is performed by certificate authorities but is a limitation of registration authorities?
What are the components of endpoint protection against social engineering attacks?
What do tools like Jenkins, Octopus Deploy, and Azure DevOps provide in terms of application and
infrastructure automation?
Which two deployment model configurations are supported for Cisco FTDv in AWS? (Choose two)
How does the Cisco WSA enforce bandwidth restrictions for web applications?
Which method of attack is used by a hacker to send malicious code through a web application to an unsuspecting user to request that the victim's web browser executes the code?
A network administrator is configuring a role in an access control policy to block certain URLs and selects the "Chat and instant Messaging" category. which reputation score should be selected to accomplish
this goal?
What is the function of the crypto is a kmp key cisc406397954 address 0.0.0.0 0.0.0.0 command when establishing an IPsec VPN tunnel?
Which two protocols must be configured to authenticate end users to the Cisco WSA? (Choose two.)
While using Cisco Secure Firewall's Security Intelligence policies, which two criteria is blocking based upon? (Choose two.)
How does Cisco Umbrella protect clients when they operate outside of the corporate network?
An engineer needs a solution for TACACS+ authentication and authorization for device administration.
The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to
use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
Which action must be taken in the AMP for Endpoints console to detect specific MD5 signatures on endpoints and then quarantine the files?
Refer to the exhibit.
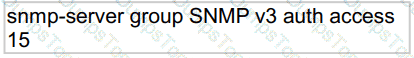
What does the number 15 represent in this configuration?
Which two are valid suppression types on a Cisco Next Generation Intrusion Prevention System? (Choose two)
Which two characteristics of messenger protocols make data exfiltration difficult to detect and prevent?
(Choose two)
Which security solution is used for posture assessment of the endpoints in a BYOD solution?
Which factor must be considered when choosing the on-premise solution over the cloud-based one?
An engineer must modify a policy to block specific addresses using Cisco Umbrella. The policy is created already and is actively used by devices, using many of the default policy elements.
What else must be done to accomplish this task?
Refer to the exhibit.
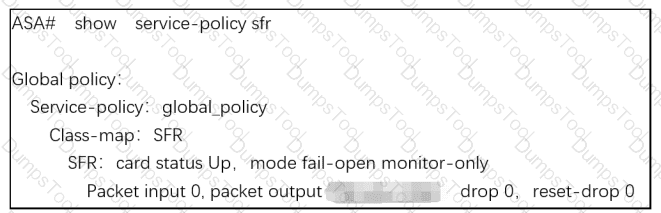
What are two indications of the Cisco Firepower Services Module configuration?
(Choose two.)
A network engineer must configure a Cisco Secure Email Gateway to prompt users to enter two forms of information before gaining access. The Secure Email Gateway must also join a cluster machine using preshared keys. What must be configured to meet these requirements?
During a recent security audit a Cisco IOS router with a working IPSEC configuration using IKEv1 was flagged for using a wildcard mask with the crypto isakmp key command The VPN peer is a SOHO router with a dynamically assigned IP address Dynamic DNS has been configured on the SOHO router to map the dynamic IP address to the host name of vpn sohoroutercompany.com In addition to the command crypto isakmp key Cisc425007536 hostname vpn.sohoroutercompany.com what other two commands are now required on the Cisco IOS router for the VPN to continue to function after the wildcard command is removed? (Choose two)
An administrator is trying to determine which applications are being used in the network but does not want the
network devices to send metadata to Cisco Firepower. Which feature should be used to accomplish this?
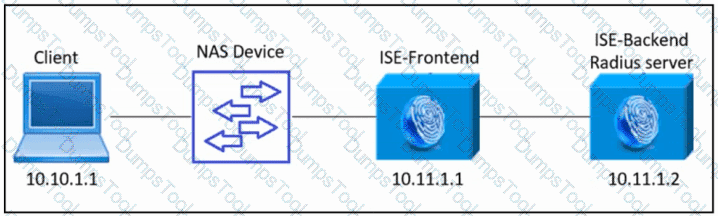
Refer to the exhibit. An engineer must configure a new Cisco ISE backend server as a RADIUS server to provide AAA for all access requests from the client to the ISE-Frontend server.
Which Cisco ISE configuration must be used?
An administrator configures a new destination list in Cisco Umbrella so that the organization can block specific domains for its devices. What should be done to ensure that all subdomains of domain.com are blocked?
A security engineer must create a policy based on the reputation verdict of a file from a Cisco Secure Email Gateway. The file with an undetermined verdict must be dropped. Which action must the security engineer take to meet the requirement?
Refer to the exhibit.
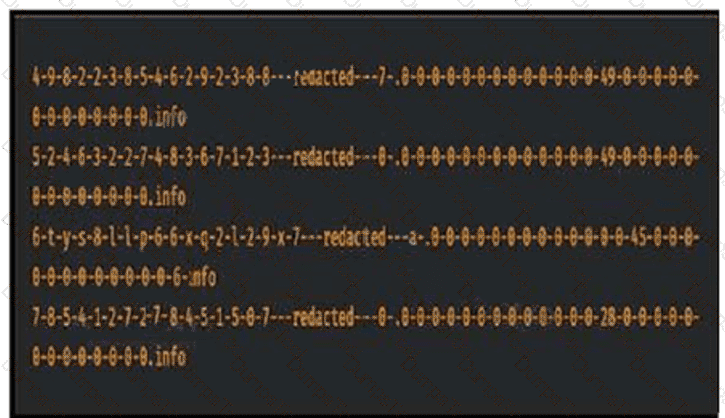
Consider that any feature of DNS requests, such as the length off the domain name
and the number of subdomains, can be used to construct models of expected behavior to which
observed values can be compared. Which type of malicious attack are these values associated with?
Which baseline form of telemetry is recommended for network infrastructure devices?
An engineer must deploy a Cisco Secure Web Appliance. Antimalware scanning must use the Outbreak Heuristics antimalware category on files identified as malware before performing any other processes. What must be configured on the Secure Web Appliance to meet the requirements?
An organization has DHCP servers set up to allocate IP addresses to clients on the LAN. What must be done to ensure the LAN switches prevent malicious DHCP traffic while also distributing IP addresses to the correct endpoints?
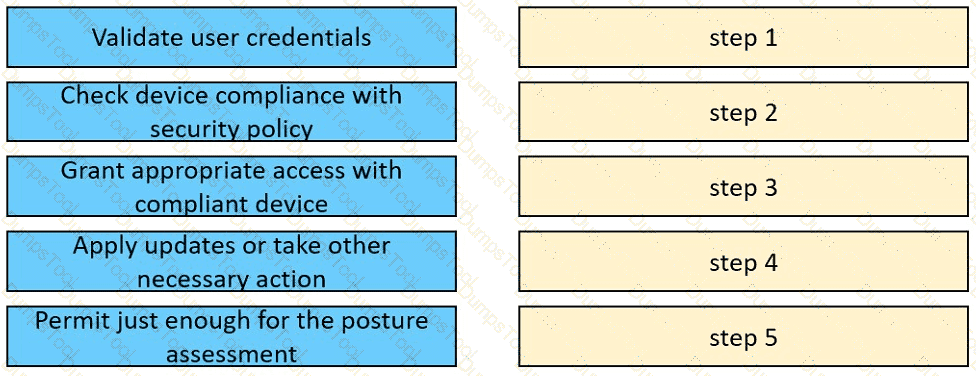
Drag and drop the posture assessment flow actions from the left into a sequence on the right.
A network administrator is setting up Cisco FMC to send logs to Cisco Security Analytics and Logging (SaaS). The network administrator is anticipating a high volume of logging events from the firewalls and wants lo limit the strain on firewall resources. Which method must the administrator use to send these logs to Cisco Security Analytics and Logging?
An engineer is configuring Cisco Secure Endpoint to enhance security by preventing the execution of certain files by users. The engineer needs to ensure that the specific executable file name Cisco_Software_0505446151.exe is blocked from running while never being quarantined. What must the engineer configure to meet the requirement?
Which policy is used to capture host information on the Cisco Firepower Next Generation Intrusion Prevention
System?
Which feature is supported when deploying Cisco ASAv within AWS public cloud?
A network administrator needs a solution to match traffic and allow or deny the traffic based on the type of application, not just the source or destination address and port used. Which kind of security product must the network administrator implement to meet this requirement?
When planning a VPN deployment, for which reason does an engineer opt for an active/active FlexVPN
configuration as opposed to DMVPN?
An engineer is implementing Cisco CES in an existing Microsoft Office 365 environment and must route inbound email to Cisco CE.. record must be modified to accomplish this task?
Refer to the exhibit.
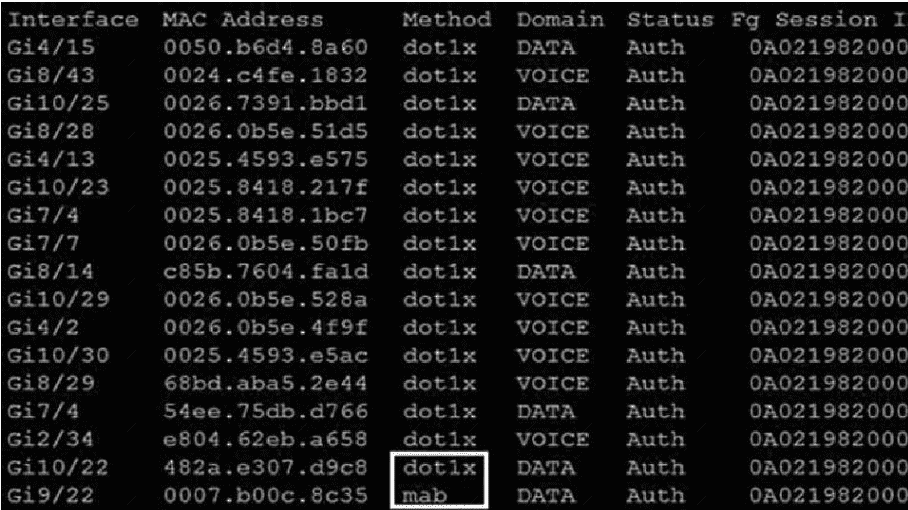
Which command was used to generate this output and to show which ports are
authenticating with dot1x or mab?
A network engineer is configuring DMVPN and entered the crypto isakmp key cisc0380739941 address 0.0.0.0 command on hostA. The tunnel is not being established to hostB. What action is needed to authenticate the VPN?
Which type of DNS abuse exchanges data between two computers even when there is no direct connection?
What is the role of an endpoint in protecting a user from a phishing attack?
What is the default action before identifying the URL during HTTPS inspection in Cisco Secure Firewall Threat Defense software?
An engineer implements Cisco CloudLock to secure a Microsoft Office 365 application in the cloud. The engineer must configure protection for corporate files in case of any incidents. Which two actions must be taken to complete the implementation? (Choose two.)
Which suspicious pattern enables the Cisco Tetration platform to learn the normal behavior of users?
Which Cisco Umbrella package supports selective proxy for Inspection of traffic from risky domains?
Drag and drop the VPN functions from the left onto the description on the right.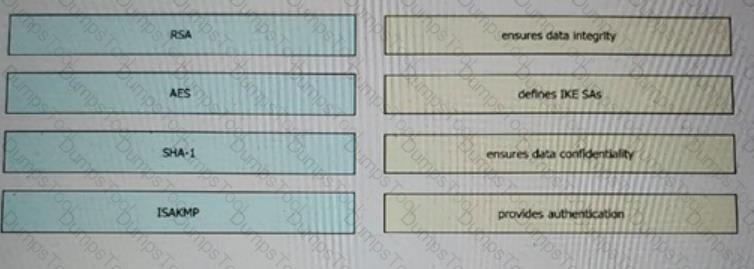
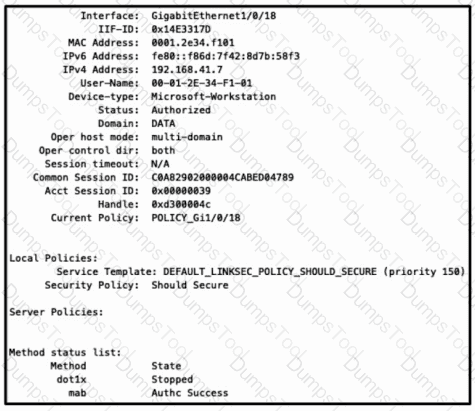
Refer to the exhibit. Which configuration item makes it possible to have the AAA session on the network?
In which situation should an Endpoint Detection and Response solution be chosen versus an Endpoint Protection Platform?
A company identified a phishing vulnerability during a pentest What are two ways the company can protect employees from the attack? (Choose two.)
Which product allows Cisco FMC to push security intelligence observable to its sensors from other products?
A Cisco Secure Cloud Analytics administrator is setting up a private network monitor sensor to monitor an on-premises environment. Which two pieces of information from the sensor are used to link to the Secure Cloud Analytics portal? (Choose two.)
A Cisco AMP for Endpoints administrator configures a custom detection policy to add specific MD5 signatures The configuration is created in the simple detection policy section, but it does not work What is the reason for this failure?
When network telemetry is implemented, what is important to be enabled across all network infrastructure devices to correlate different sources?
An administrator configures a Cisco WSA to receive redirected traffic over ports 80 and 443. The organization requires that a network device with specific WSA integration capabilities be configured to send the traffic to the WSA to proxy the requests and increase visibility, while making this invisible to the users. What must be done on the Cisco WSA to support these requirements?
Using Cisco Firepower’s Security Intelligence policies, upon which two criteria is Firepower block based?
(Choose two)
Which CLI command is used to enable URL filtering support for shortened URLs on the Cisco ESA?