What mechanism carries multicast traffic between remote sites and supports encryption?
which purpose does a northbound API serve in a controller-based networking architecture?
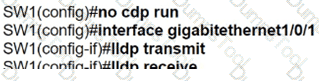
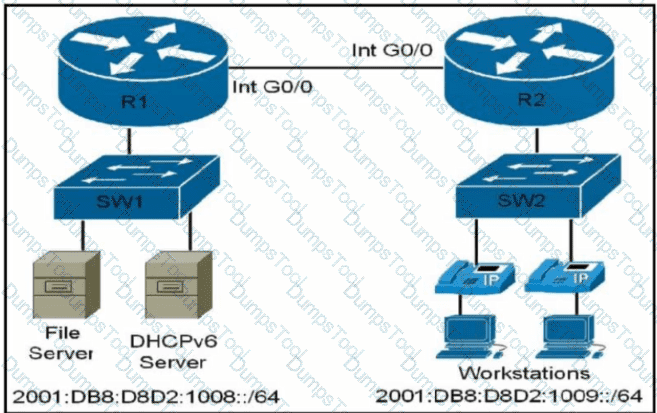
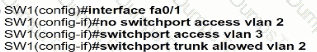
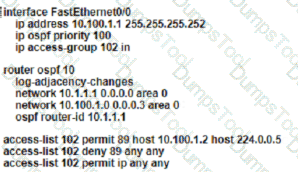
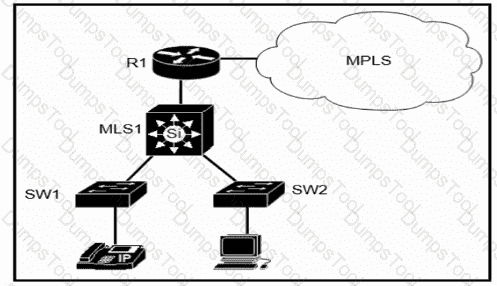
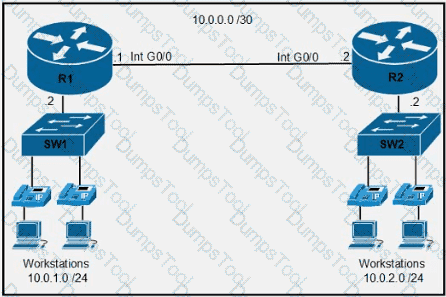
Refer to the exhibit.
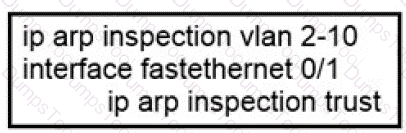
If the network environment is operating normally, which type of device must be connected to interface FastEthernet 0/1?
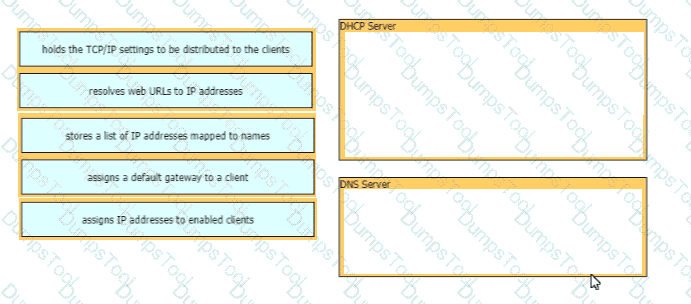
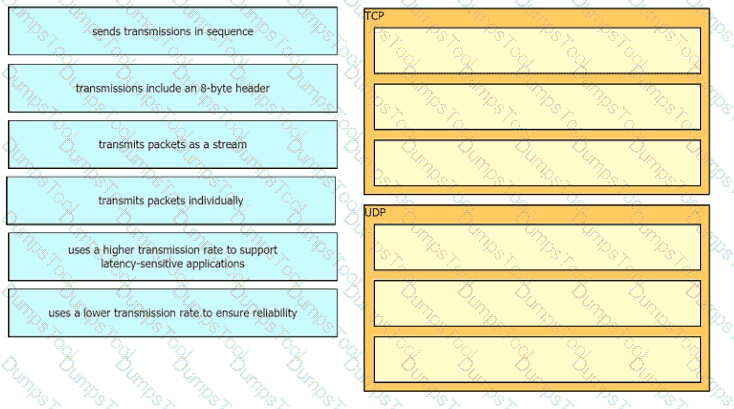
Drag and drop the functions from the left onto the correct network components on the right
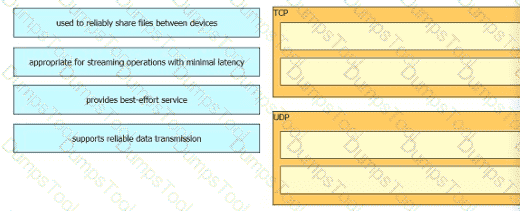
How do TCP and UDP differ in the way they provide reliability for delivery of packets?
What uses HTTP messages to transfer data to applications residing on different hosts?
What protocol allows an engineer to back up 20 network router configurations globally while using the copy function?
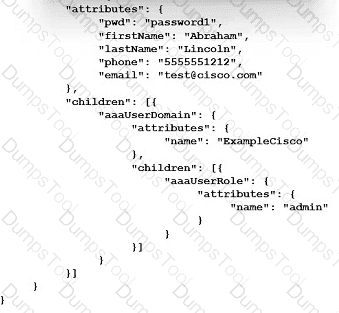
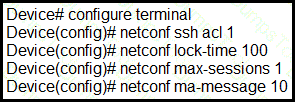
Refer to the exhibit.
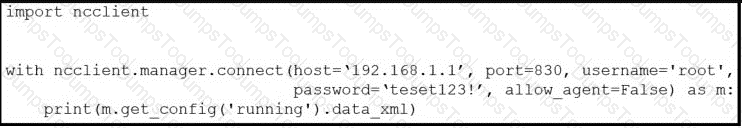
After running the code in the exhibit, which step reduces the amount of data that the NETCONF server returns to the NETCONF client, to only the interface ' s configuration?
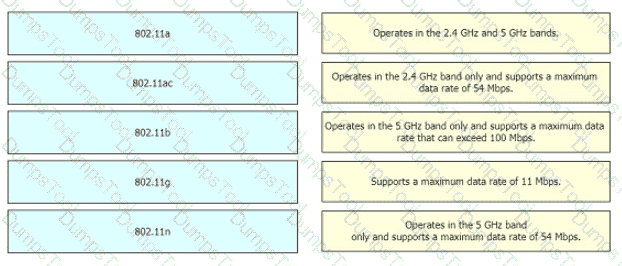
Drag and drop the 802.11 wireless standards from the left onto the matching statements on the right
Which switch technology establishes a network connection immediately when it is plugged in?
Which QoS Profile is selected in the GUI when configuring a voice over WLAN deployment?
In which way does a spine-and-leaf architecture allow for scalability in a network when additional access ports are required?
When DHCP is configured on a router, which command must be entered so the default gateway is automatically distributed?
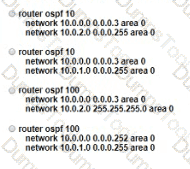
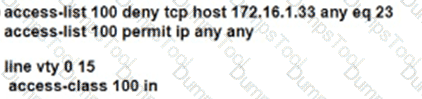
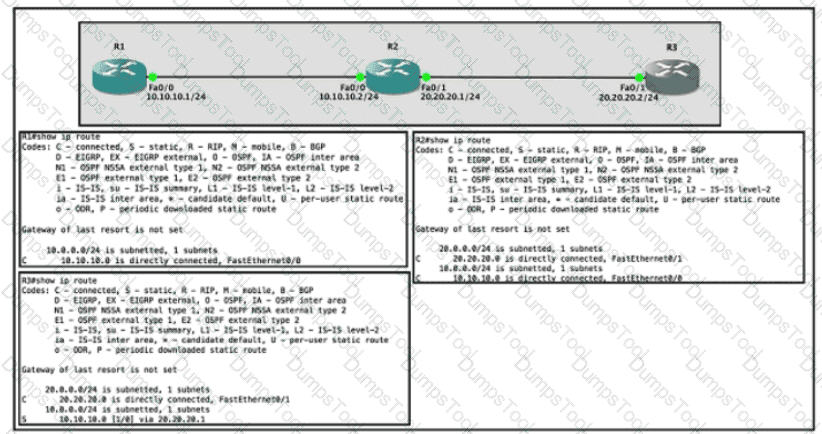
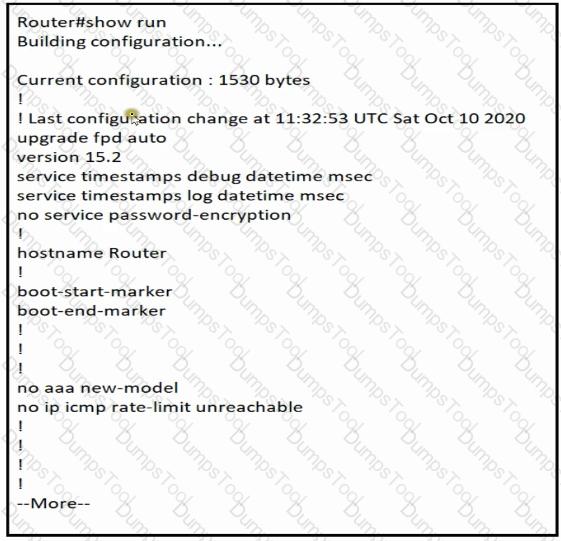
Refer to the exhibit.
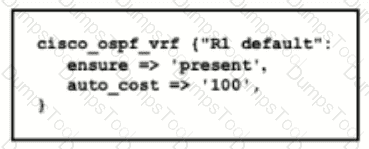
Which type of configuration is represented in the output?
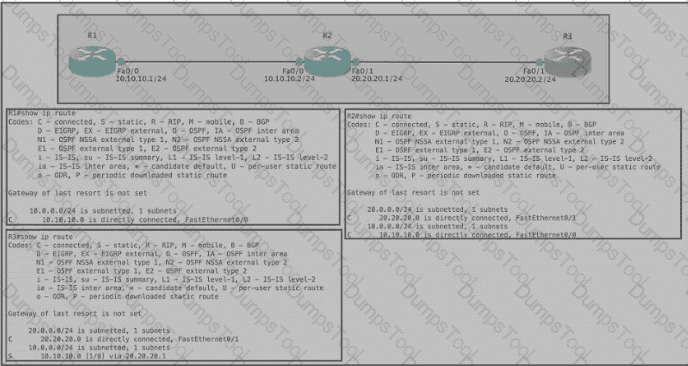
Refer to the exhibit. Router R1 Fa0/0 is unable to ping router R3 Fa0/1. Which action must be taken on router R1 to resolve the configuration issue?
Which two minimum parameters must be configured on an active interface to enable OSPFv2 to operate? (Choose two)
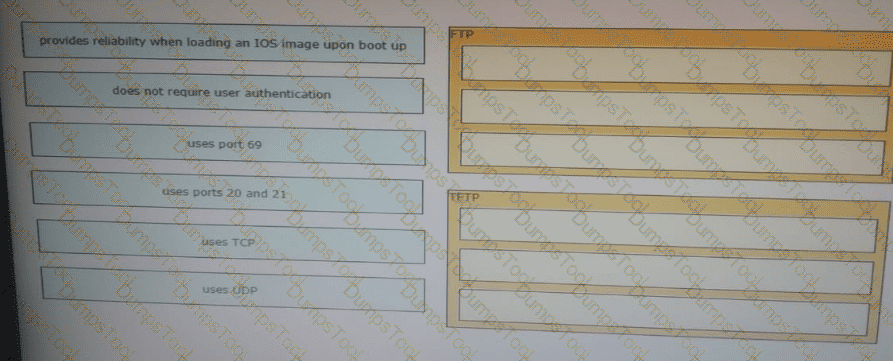
Drag and drop the descriptions of file-transfer protocols from the left onto the correct protocols on the right.
Refer to the exhibit.
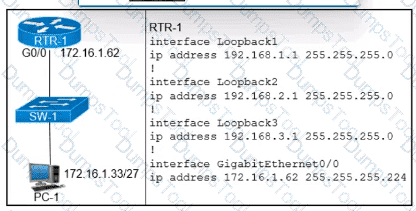
Which configuration for RTR-1 denies SSH access from PC-1 to any RTR-1 interface and allows all other traffic?
A)
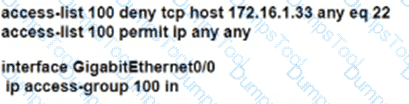
B)
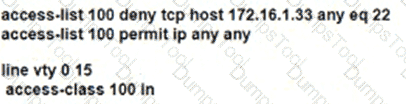
C)
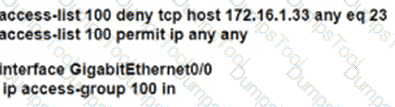
D)
Which two features introduced in SNMPv2 provide the ability to retrieve large amounts of data in one request
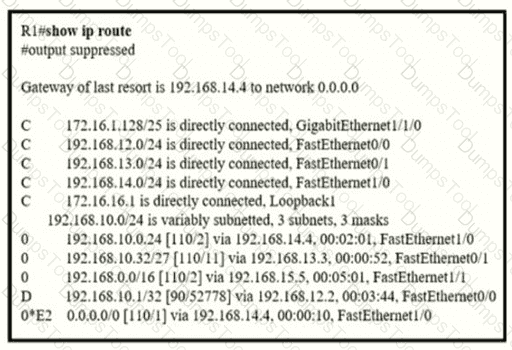
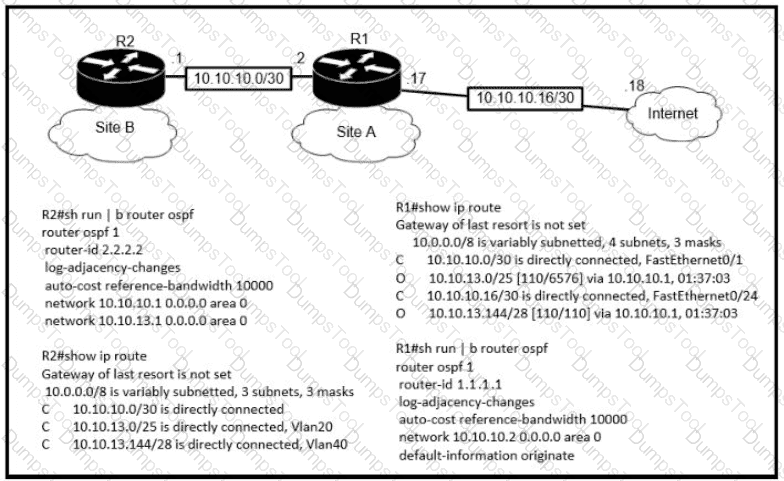
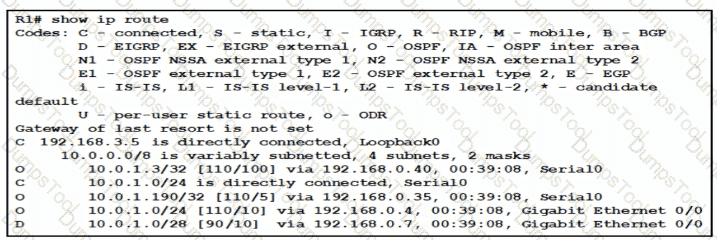
Refer to the exhibit.
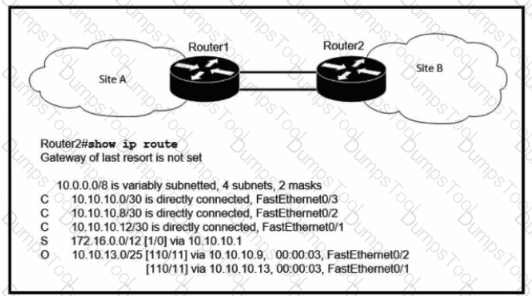
User traffic originating within site 0 is failing to reach an application hosted on IIP address 192.168.0.10. Which is located within site A What is determined by the routing table?
When a WPA2-PSK WLAN is configured in the Wireless LAN Controller, what is the minimum number of characters that is required in ASCII format?
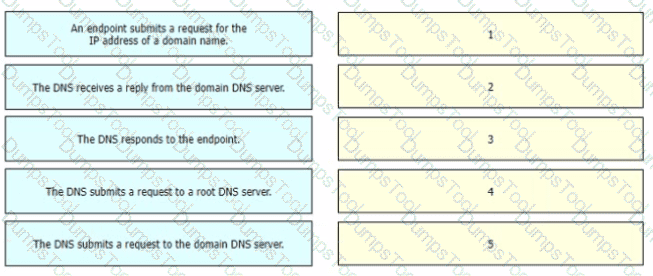
Drag and drop the steps in a standard DNS lookup operation from the left into the order on the right.
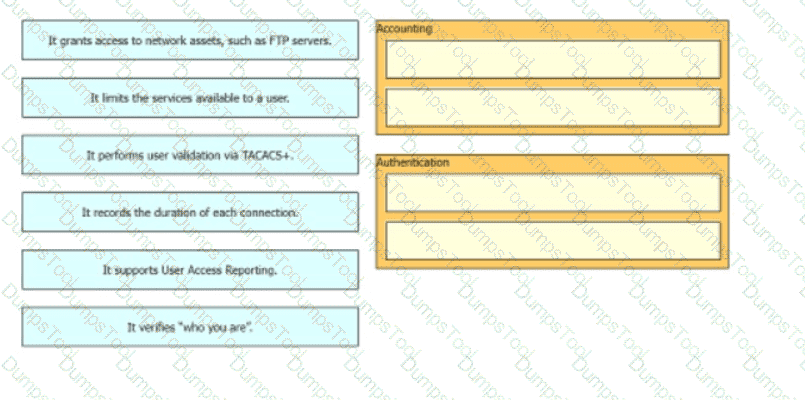
Drag and drop the statement about AAA services from the left to the corresponding AAA services on the right.
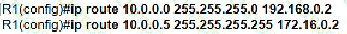
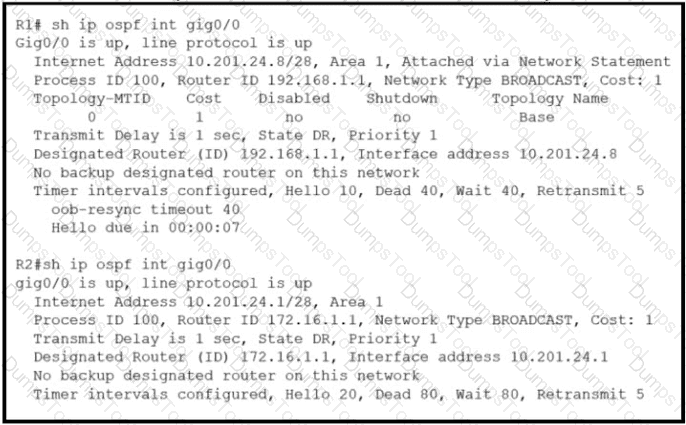
Refer to the exhibit.
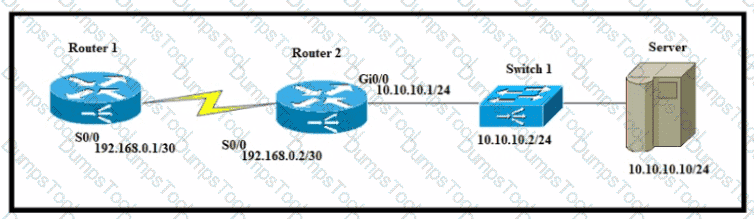
A network engineer must configure router R1 with a host route to the server. Which command must the engineer configure?
What does the implementation of a first-hop redundancy protocol protect against on a network?
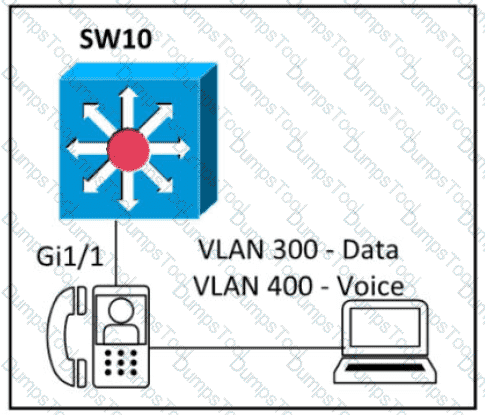
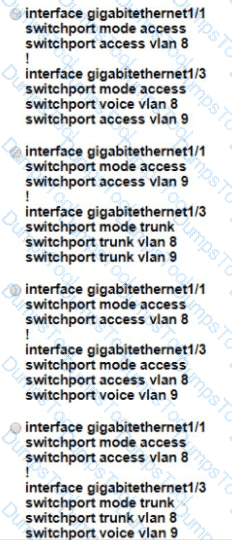
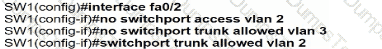
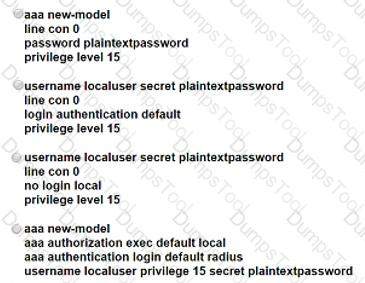
Refer to the exhibit.
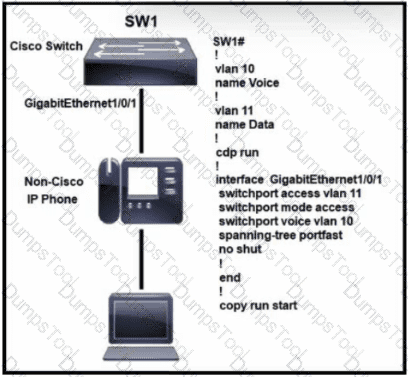
A multivendor network exists and the company is implementing VoIP over the network for the first time.
A)

B)
C)
D)
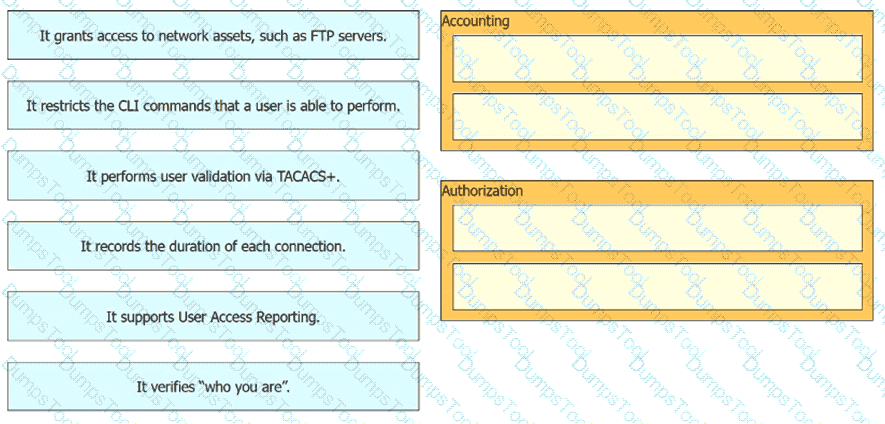
Drag and drop the statements about AAA services from the left onto the corresponding AAA services on the right Not all options are used.
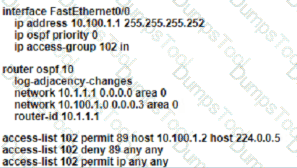
Refer to the exhibit.
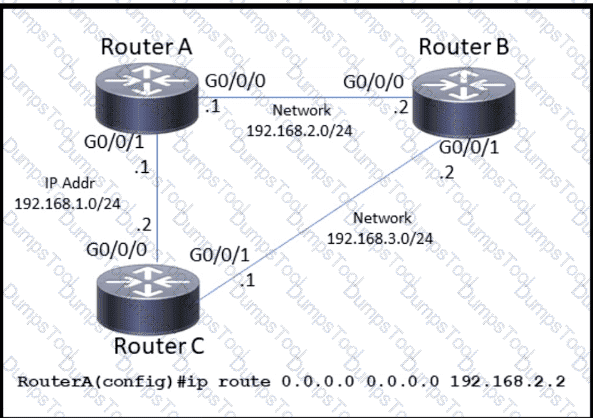
Which command must enable a floating default route on router A?
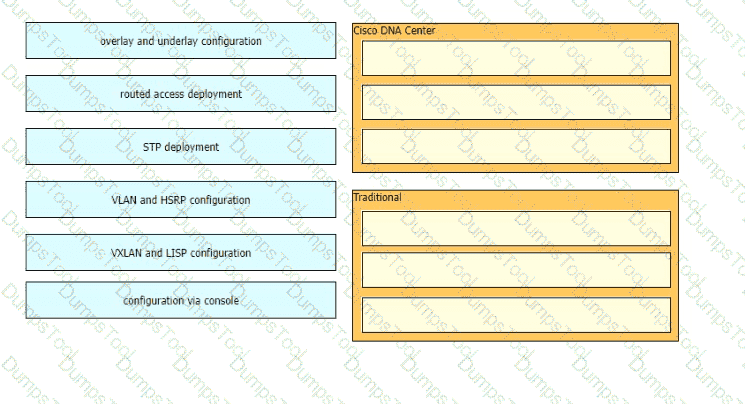
Drag and drop the use cases for device-management technologies from the left onto the corresponding.
Refer to the exhibit.
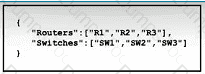
What is represented by " R1 " and " SW1 " within the JSON output?
What is the advantage of separating the control plane from the data plane within an SDN network?
To improve corporate security, an organization is planning to implement badge authentication to limit access to the data center. Which element of a security program is being deployed?
What is the purpose of using First Hop Redundancy Protocol on a specific subnet?
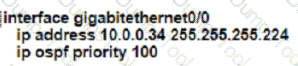
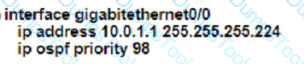
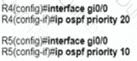
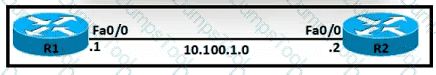
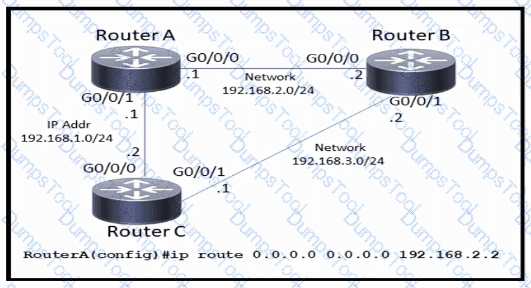
Refer to the exhibit.
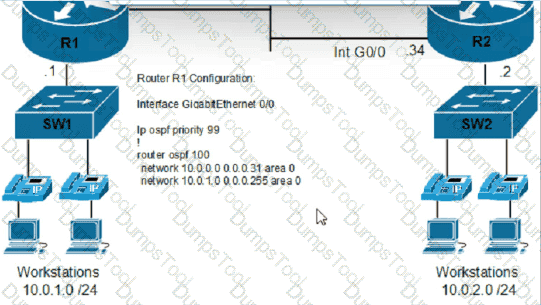
An engineer must configure router R2 so it is elected as the DR on the WAN subnet. Which command sequence must be configured?
A)
B)
C)
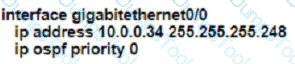
D)
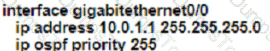
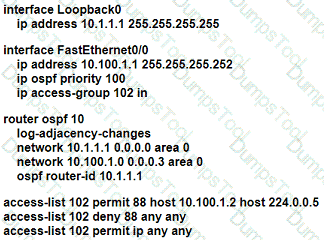
Refer to the exhibit.
The image server and client A are running an application that transfers an extremely high volume of data between the two. An engineer is configuring a dedicated circuit between R1 and R2. Which set of commands must the engineer apply to the routers so that only traffic between the image server and client A is forces to use the new circuit?
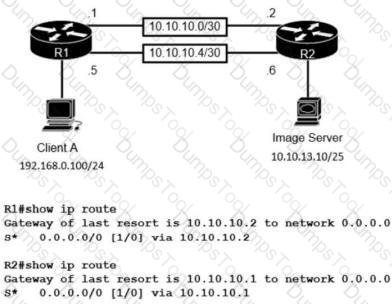
Refer to the exhibit.
Which next-hop IP address has the least desirable metric when sourced from R1?
Refer to the exhibit.
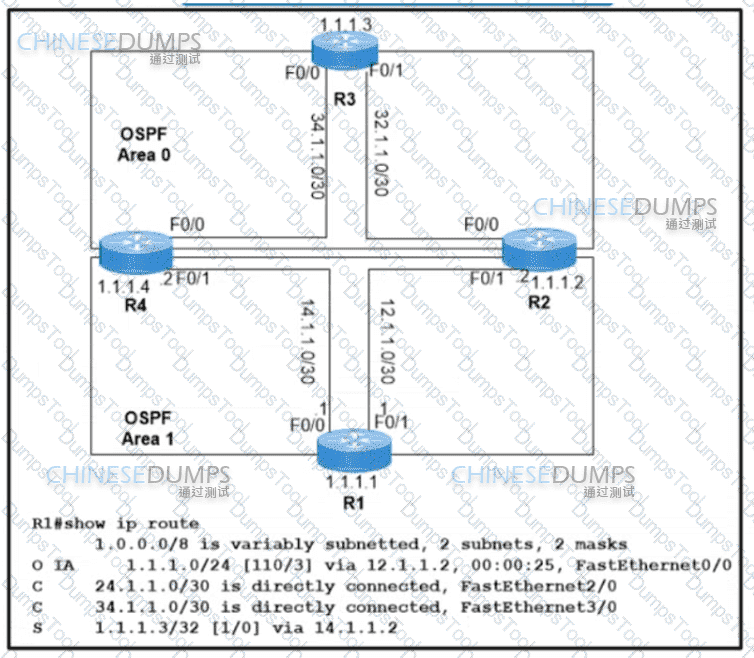
Which two values does router R1 use to identify valid routes for the R3 loopback address 1.1.1.3/32? (Choose two.)
A Cisco engineer at a new branch office is configuring a wireless network with access points that connect to a controller that is based at corporate headquarters Wireless client traffic must terminate at the branch office and access-point survivability is required in the event of a WAN outage Which access point mode must be selected?
Refer to the exhibit.
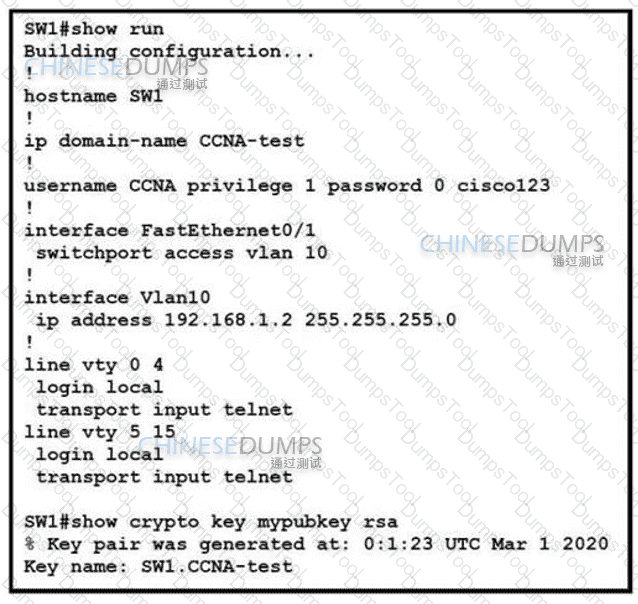
An engineer is updating the management access configuration of switch SW1 to allow secured, encrypted remote configuration. Which two commands or command sequences must the engineer apply to the switch? (Choose two.)
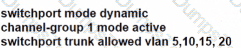
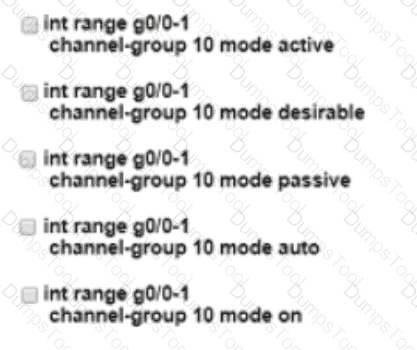
Refer to the exhibit.
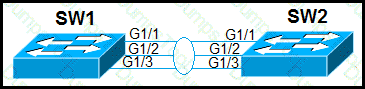
Which configuration establishes a Layer 2 LACP EtherChannel when applied to both switches?
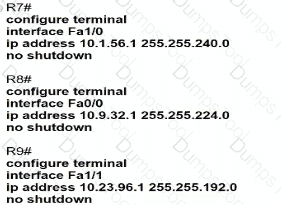
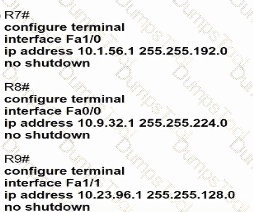
Refer to the exhibit.
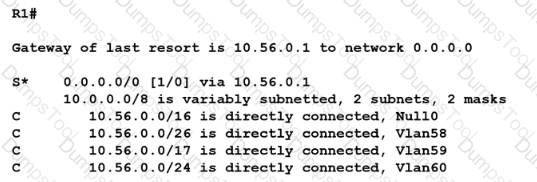
When router R1 receives a packet with destination IP address 10.56.0 62. through which interface does it route the packet?
Which advantage does the network assurance capability of Cisco DNA Center provide over traditional campus management?
What is the purpose of using First Hop Redundancy Protocol in a specific subnet?
Refer to the exhibit.
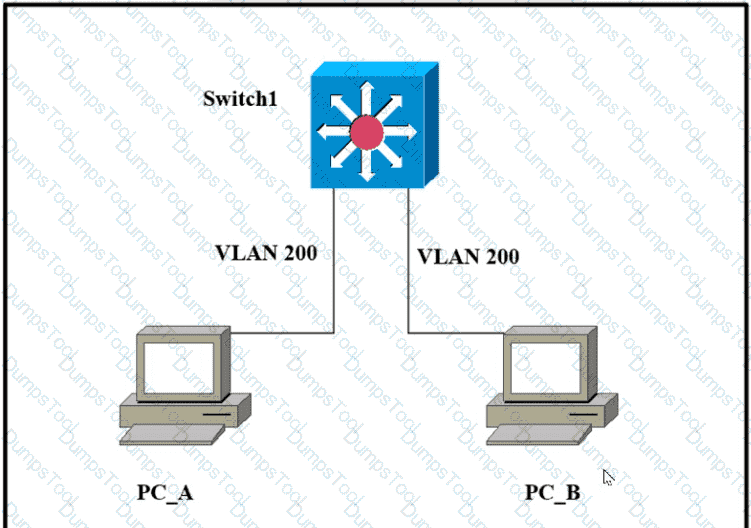
Which outcome is expected when PC_A sends data to PC_B?
A frame that enters a switch fails the Frame Check Sequence. Which two interface counters are incremented? (Choose two)
What is the difference regarding reliability and communication type between TCP and UDP?
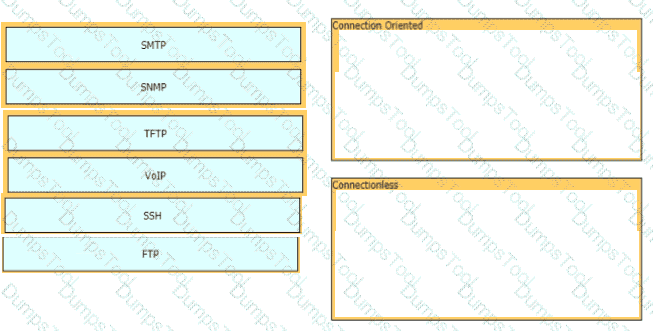
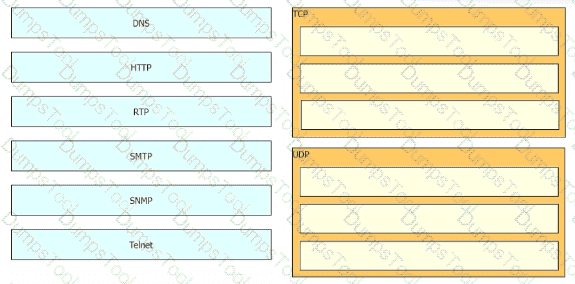
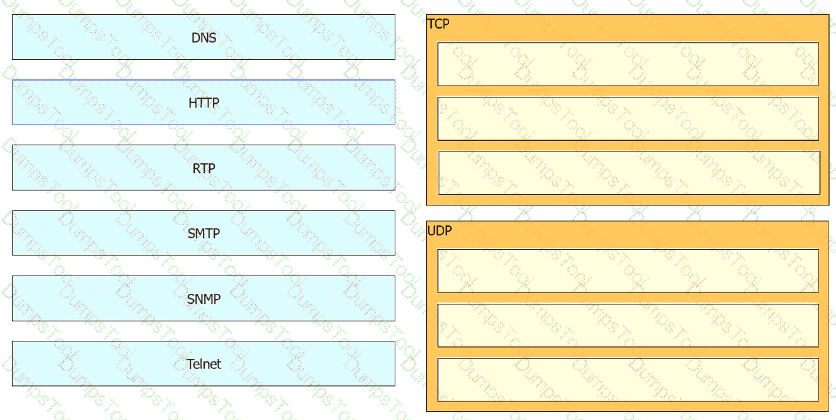
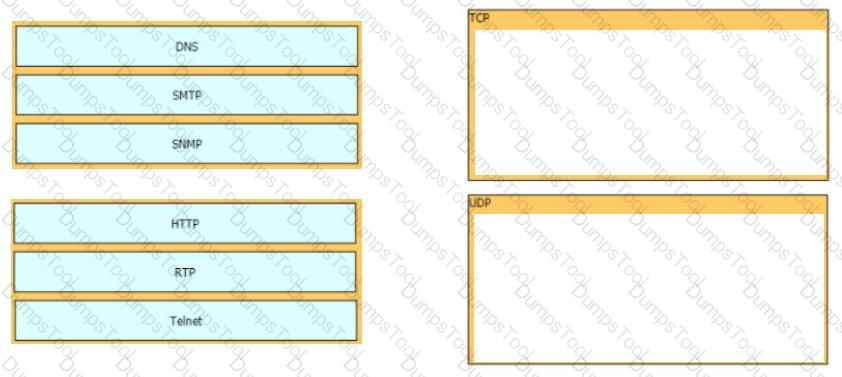
Drag and drop the network protocols from the left onto the correct transport services on the right.
Which network allows devices to communicate without the need to access the Internet?
A network architect is deciding whether to implement Cisco autonomous access points or lightweight access points. Which fact about firmware updates must the architect consider? Unlike lightweight access points, which require
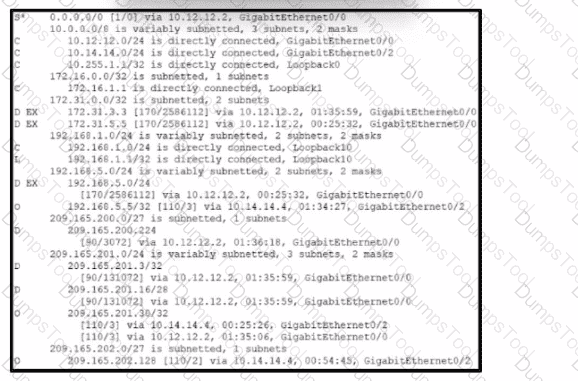
Refer to the exhibit. Four load-balancing servers are reachable through this router; however, the company is removing all static and default routes on the router.
Server 1 - 10.12.14.14
Server 2 - 192.168.4.4
Server 3 - 209.165.200.5
Server 4 - 209.165.201.26
Which server will handle all traffic after the policy changes take effect?
Which technology is appropriate for communication between an SDN controller and applications running over the network?
Which mode must be used to configure EtherChannel between two switches without using a negotiation protocol?
Refer to the exhibit.
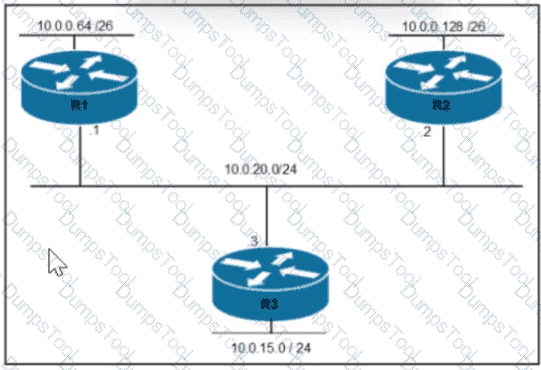
Router R1 is added to the network and configured with the 10.0.0.64/26 and 10.0.20.0/24 subnets However traffic destined for the LAN on R3 is not accessible. Which command when executed on R1 defines a static route to reach the R3 LAN?
A)

B)
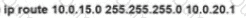
C)
Which interface is used to send traffic to the destination network?
10.174.208.210/28 [110/2708] via G0/21
10.174.208.210/28 [110/25445] via G0/20
10.174.208.210/28 [120/1] via G0/12
10.174.208.210/28 [120/4] via G0/16
A network engineer is implementing a corporate SSID for WPA3-Personal security with a PSK. Which encryption cipher must be configured?
Which interface IP addressss serves as the tunnel source for CAPWAP packets froin the WLC to an AP?
Which event has occurred if a router sends a notice level message to a syslog server?
Which set of actions satisfies the requirement for multifactor authentication?
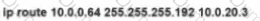
Refer to the exhibit.
An architect is managing a wireless network with APs from several branch offices connecting to the WLC in the data center. There is a new requirement for a single WLAN to process the client data traffic without sending it to the WLC. Which action must be taken to complete the request?
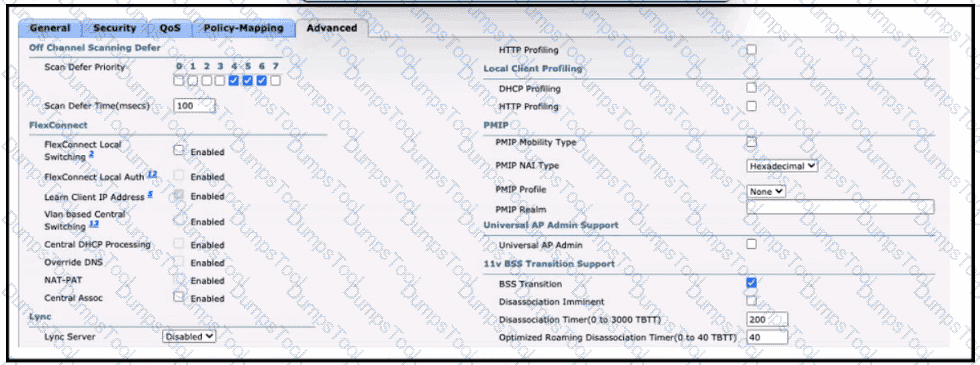
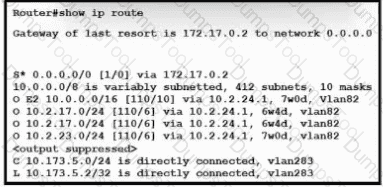
Refer to the exhibit. OSPF neighbors routers A, B, C, and D are sending a route for 10.227.150.160/27. When the current route for 10.227.150.160/27 becomes unavailable, which cost will router Y use to route traffic to 10.227.150.160/27?
Which group of channels in the 802.11b/g/n/ax 2.4 GHz frequency bands are non-overlapping channels?
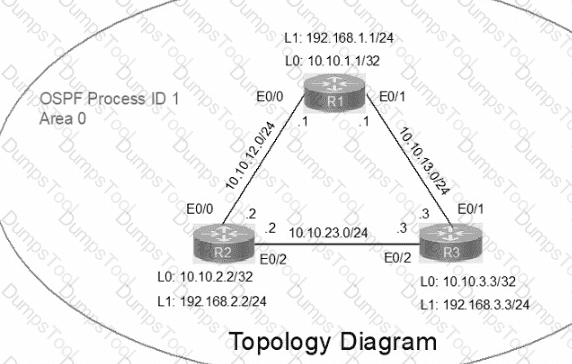
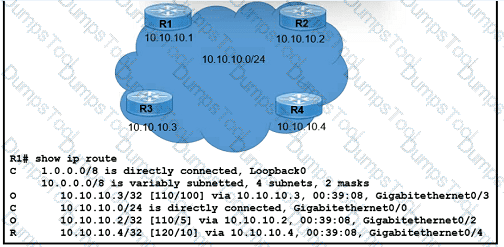
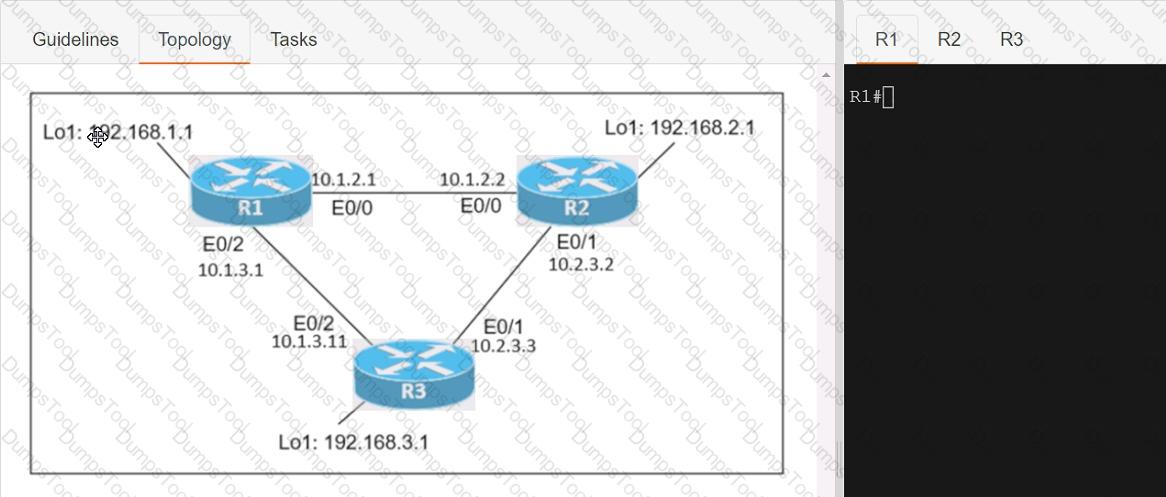
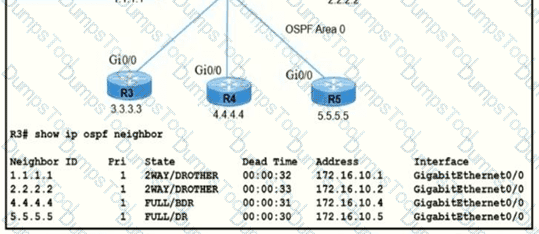
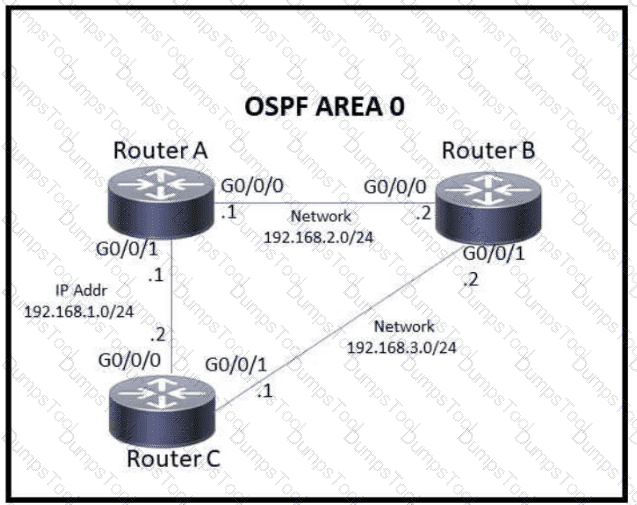
IP connectivity between the three routers is configured. OSPF adjacencies must be established.
1. Configure R1 and R2 Router IDs using the interface IP addresses from the link that is shared between them.
2. Configure the R2 links with a max value facing R1 and R3. R2 must become the DR. R1 and R3 links facing R2 must remain with the default OSPF configuration for DR election. Verify the configuration after clearing the OSPF process.
3. Using a host wildcard mask, configure all three routers to advertise their respective Loopback1 networks.
4. Configure the link between R1 and R3 to disable their ability to add other OSPF routers.
Connectivity between four routers has been established. IP connectivity must be configured in the order presented to complete the implementation. No dynamic routing protocols are included.
1. Configure static routing using host routes to establish connectivity from router R3 to the router R1 Loopback address using the source IP of 209.165.200.230.
2. Configure an IPv4 default route on router R2 destined for router R4.
3. Configure an IPv6 default router on router R2 destined for router R4.

Which two protocols are supported on service-port interfaces? (Choose two.)
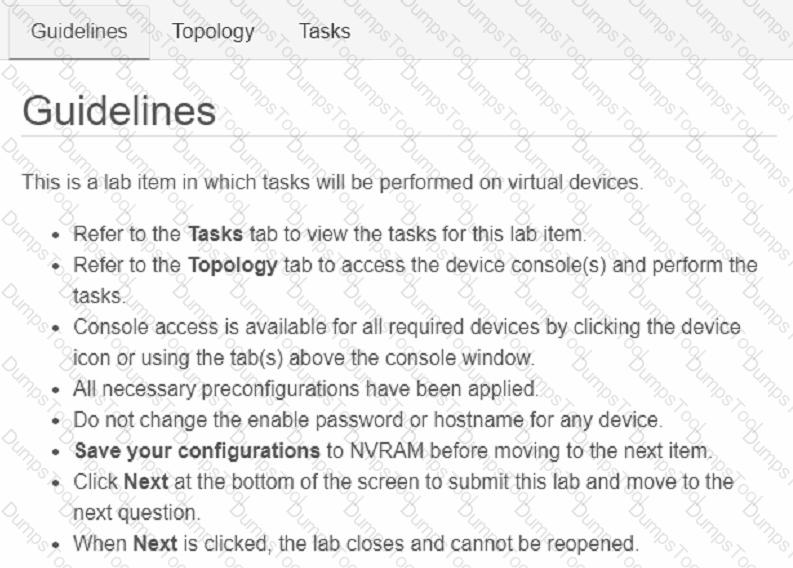
Drag and drop the IPv4 network subnets from the left onto the correct usable host ranges on the right
Which device controls the forwarding of authentication requests for users when connecting to the network using a lightweight access point?
Refer to the exhibit.
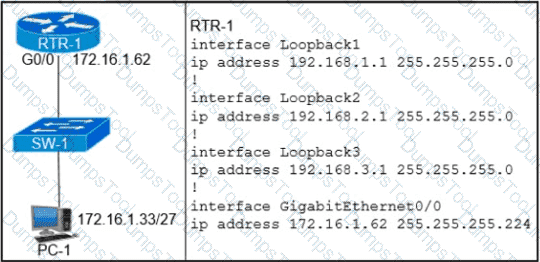
Which configuration on RTR-1 denies SSH access from PC-1 to any RTR-1 interface and allows all other traffic?
What are two benefits of controller-based networking compared to traditional networking?
Which IP addressss is used when an administrator must open a web-based management session with a lightweight AP?
Refer to the exhibit. What is the value of the administrative distance for the default gateway?
What is the operating mode and role of a backup port on a shared LAN segment in Rapid PVST+?
Refer to the exhibit.
PC A is communicating with another device at IIP address 10.227.225.255. Through which router does router Y route the traffic?
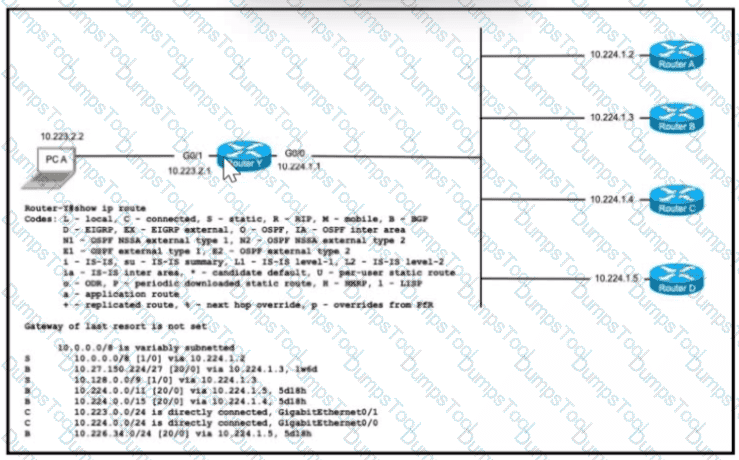
Refer to the exhibit.
A network administrator configures the CPE to provide internet access to the company headquarters. Traffic must be load-balanced via ISP1 and ISP2 to ensure redundancy.
Which two command sets must be configured on the CPE router? (Choose two.)
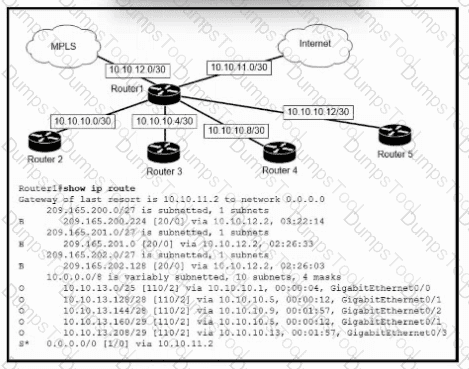
Refer to the exhibit. To which device does Router1 send packets that are destined to host 10.10.13.165?
A network administrator must enable DHCP services between two sites. What must be configured for the router to pass DHCPDISCOVER messages on to the server?
Which IPv6 address block sends packets to a group address rather than a single address?
When using Rapid PVST+, which command guarantees the switch is always the root bridge for VLAN 200?
Which configuration ensures that the switch is always the root for VLAN 750?
Refer to the exhibit.
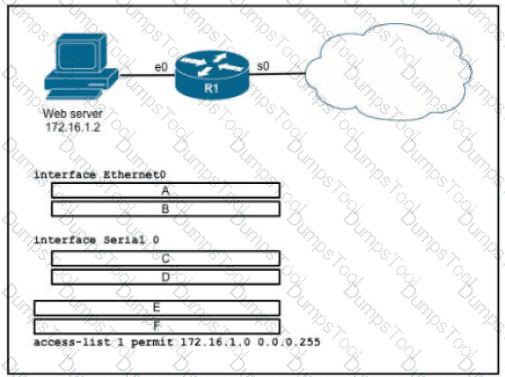
An engineer is configuring the router to provide static NAT for the webserver Drag and drop the configuration commands from the left onto the letters that correspond to its position in the configuration on the right.
Which protocol does an IPv4 host use to obtain a dynamically assigned IP address?
Which command automatically generates an IPv6 address from a specified IPv6 prefix and MAC address of an interface?
Which resource is able to be shared among virtual machines deployed on the same physical server?
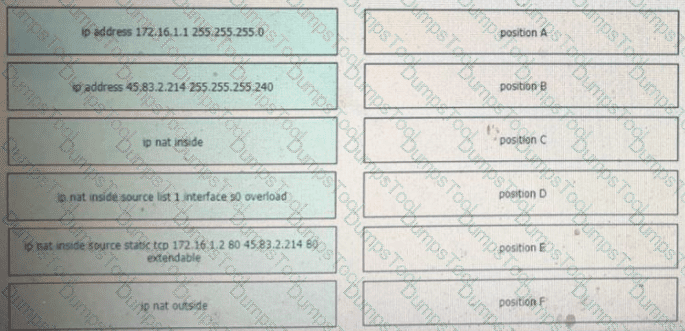
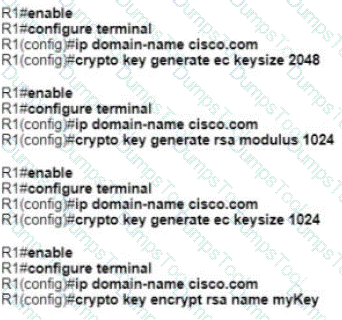
Refer to exhibit.
Which statement explains the configuration error message that is received?
Which device tracks the state of active connections in order to make a decision to forward a packet through?
An organization has decided to start using cloud-provided services. Which cloud service allows the organization to install its own operating system on a virtual machine?
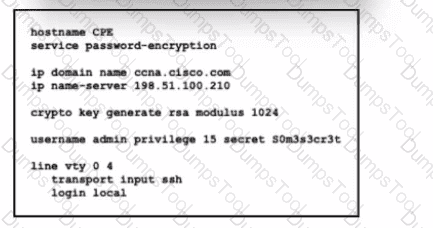
Refer to the exhibit. An engineer executed the script and added commands that were not necessary for SSH and must now remove the commands. Which two commands must be executed to correct the configuration? (Choose two.)
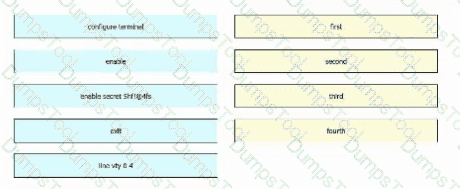
An engineer is configuring en encrypted password for the enable command on a router where the local user database has already been configured. Drag and drop the configuration commands froin the let into the correct sequence on the right. Not all commends are used.
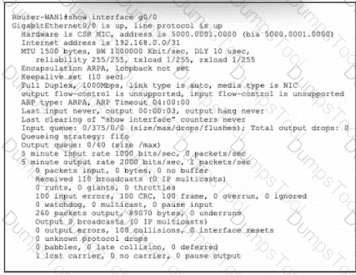
Refer to the exhibit. Router-WAN1 has a new connection via Gi0/0 to the ISP. Users running the web applications indicate that connectivity is unstable to the internet. What is causing the interface issue?

Refer to the exhibit. The loopback IP of R3 has been learned via the two interfaces on R1. R1 is configured with a reference bandwidth of 10 Gbps. Based on the metric calculations, which next hop IP would be used for outgoing routing?
Refer to the exhibit.
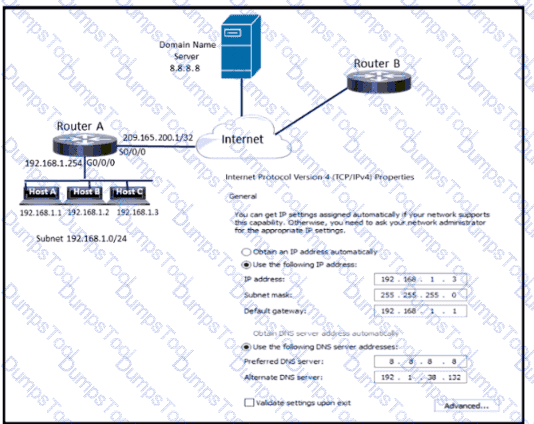
Which configuration parameter is preventing host C from reaching the internet?
Drag and drop the AAA terms from the left onto the descriptions on the right.
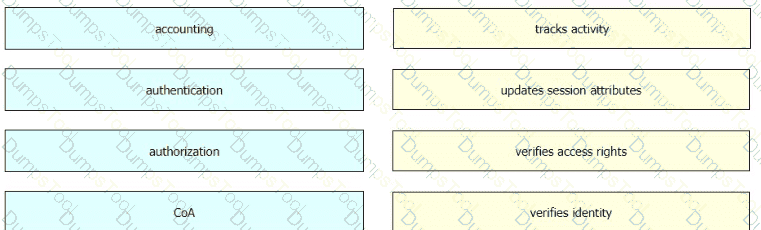
Drag and drop the AAA features froin the left onto the corresponding AAA security services on the right Not all options are used.
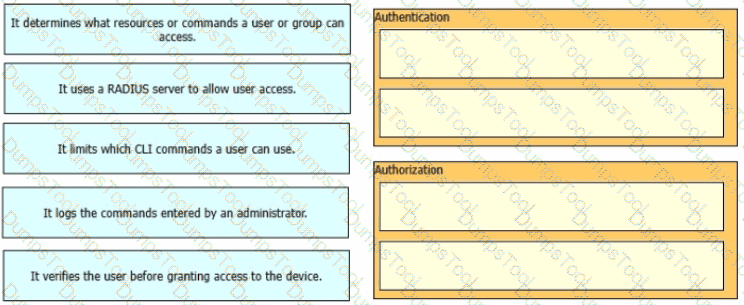
Refer to the exhibit.
The network engineer is configuring a new WLAN and is told to use a static password for authentication instead of the RADIUS servers. Which additional set of tasks must the engineer perform to complete the configuration?
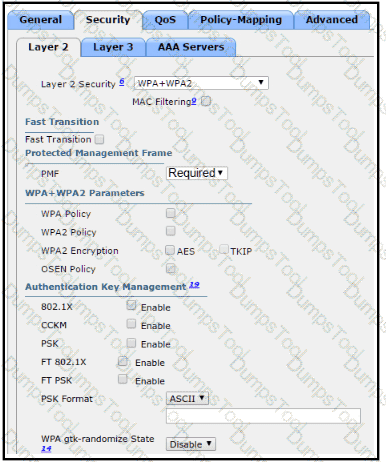
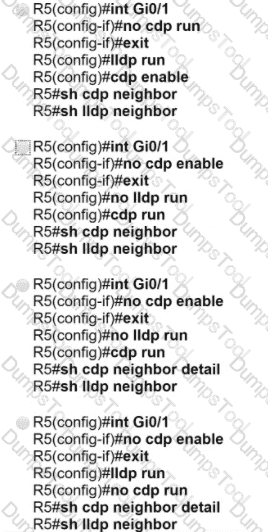
Refer to the exhibit.
A new VLAN and switch are added to the network. A remote engineer configures OldSwitch and must ensure that the configuration meets these requirements:
• accommodates current configured VLANs
• expands the range to include VLAN 20
• allows for IEEE standard support for virtual LANs
Which configuration on the NewSwitch side of the link meets these requirements?
A)
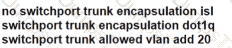
B)
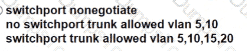
C)
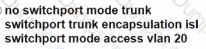
D)
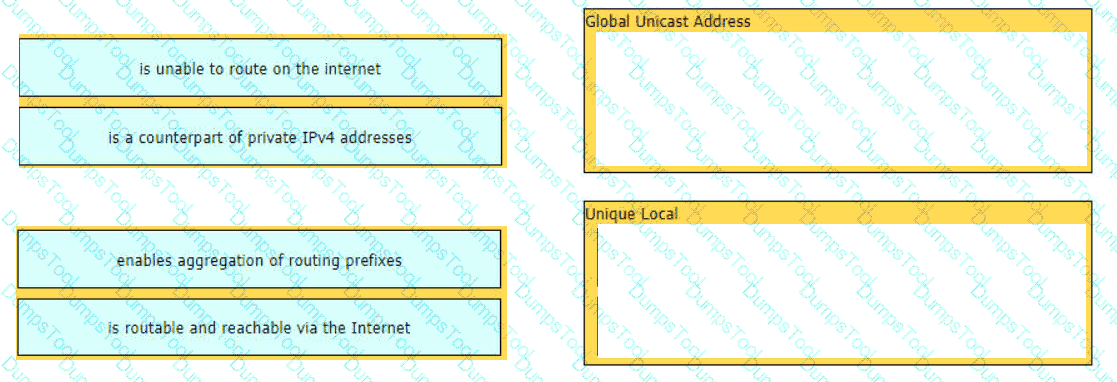
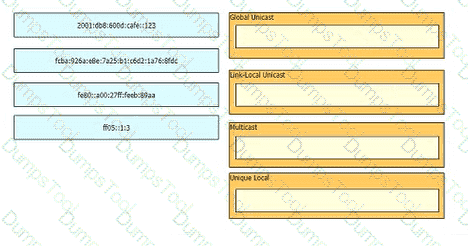
Drag and drop the characteristic from the left onto the IPv6 address type on the right.
Which interface is used to send traffic to the destination network?
10.90.207.87/26 [110/1912] via F0/7
10.90.207.87/26 [110/28968] via F0/6
10.90.207.87/26 [120/14] via F0/4
10.90.207.87/26 [120/11] via F0/5
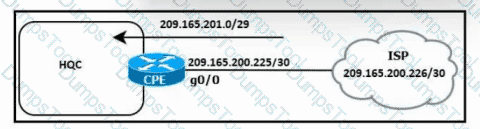
Refer to the exhibit. HQC needs to use a configuration that:
Handles up to 150,000 concurrent connections
Minimizes consumption of public IP addresssses
Which configuration meets the requirements?
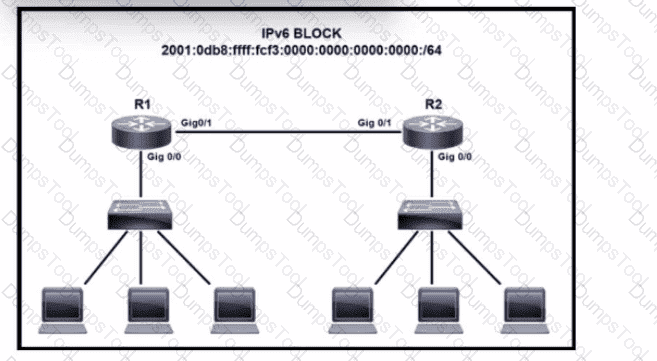
Refer to the exhibit. IPv6 is being Implemented within the enterprise. The command Ipv6 unlcast-routing is configure. Interlace GlgO/0 on R1 must be configured to provide a dynamic assignment using the assigned IPv6 block Which command accomplishes this task?
Where are the real-time control functions processed in a split MAC architecture?
A network engineer is configuring a switch so that it is remotely reachable via SSH. The engineer has already configured the host name. Which additional command must the engineer configure before entering the command to generate the RSA key?
Which function generally performed by a traditional network device is replaced by a software-defined controller?
An engineer must configure the IPv6 address 2001:0db8:0000:0000:0700:0003:400F:572B on the serial0/0 interface of the HQ router and wants to compress it for easier configuration. Which command must be issued on the router interface?
Refer to the exhibit.
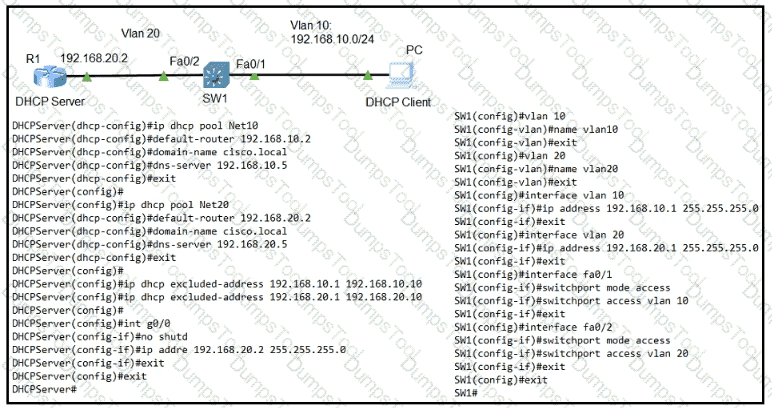
The DHCP server is configured with a DHCP pool for each of the subnets represented. Which command must be configured on switch SW1 to allow DHCP clients on VLAN 10 to receive dynamic IP addresssses froin the DHCP server?
Refer to the exhibit. A network engineer is configuring a wirelesss LAN with Web Passthrough Layer 3 Web Policy. Which action must the engineer take to complete the configuration?
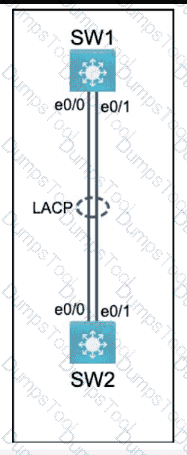
Physical connectivity is implemented between the two Layer 2 switches,
and the network connectivity between them must be configured.
I . Configure an LACP EtherChanneI and number it as 44; configure it
between switches SWI and SW2 using interfaces EthernetO/O and
Ethernet0/1 on both sides. The LACP mode must match on both ends.
2. Configure the EtherChanneI as a trunk link.
3. Configure the trunk link with 802. Iq tags.
4. Configure VLAN ' MONITORING ' as the untagged VLAN of the
EtherChannel.
==================
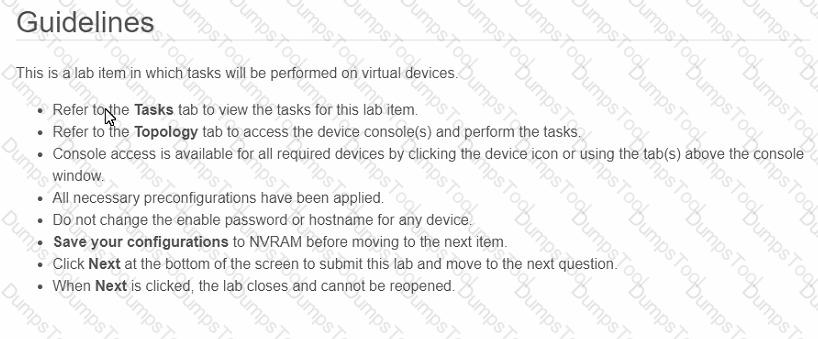
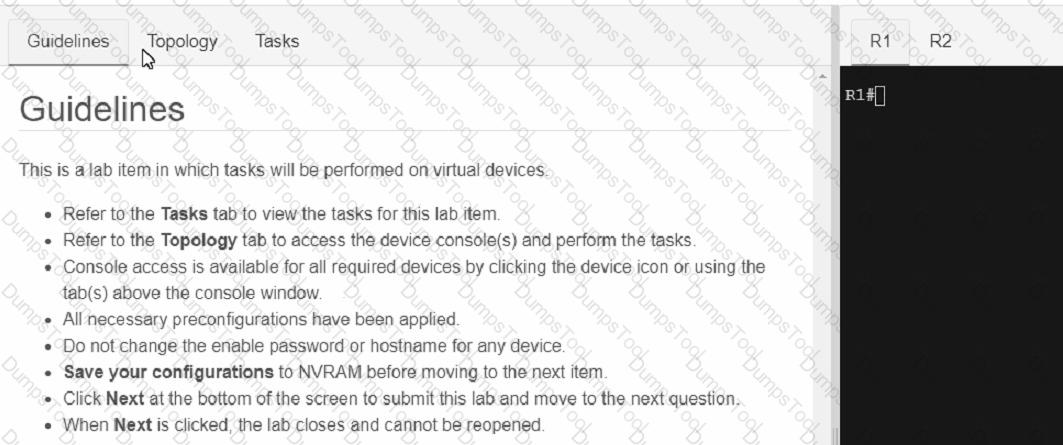
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using
the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
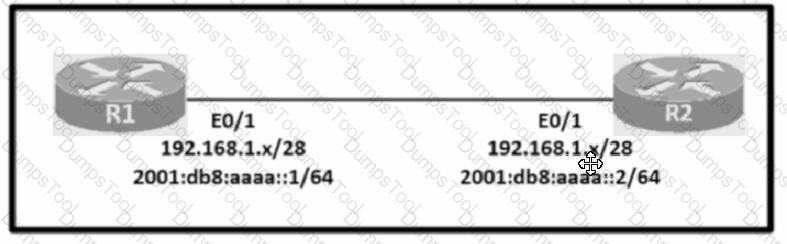
Configure IPv4 and IPv6 connectivity between two routers. For IPv4, use a /28 network from the 192.168.1.0/24 private range. For IPv6, use the first /64 subnet from the 2001:0db8:aaaa::/48 subnet.
1. Using Ethernet0/1 on routers R1 and R2, configure the next usable/28 from the 192.168.1.0/24 range. The network 192.168.1.0/28 is unavailable.
2. For the IPv4 /28 subnet, router R1 must be configured with the first usable host address.
3. For the IPv4 /28 subnet, router R2 must be configured with the last usable host address.
4. For the IPv6 /64 subnet, configure the routers with the IP addressing provided from the topology.
5. A ping must work between the routers on the IPv4 and IPv6 address ranges.
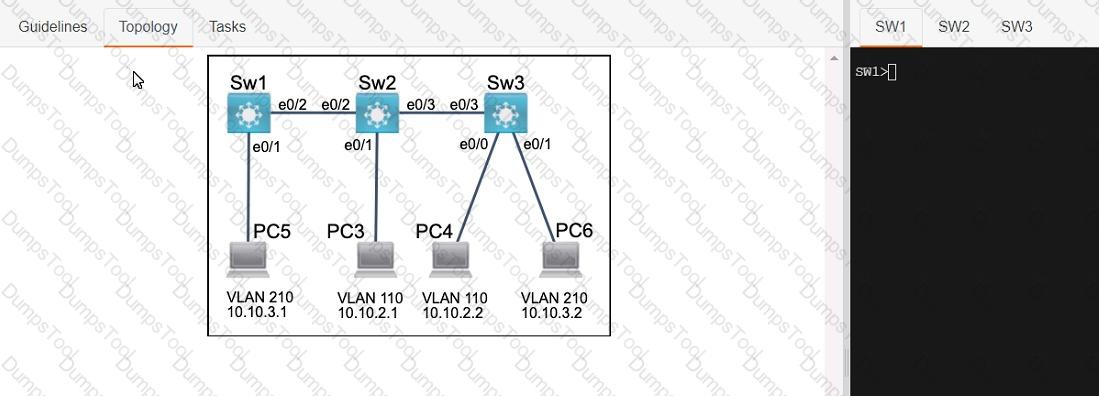
Three switches must be configured for Layer 2 connectivity. The company requires only the designated VLANs to be configured on their respective switches and permitted accross any links between switches for security purposes. Do not modify or delete VTP configurations.
The network needs two user-defined VLANs configured:
VLAN 110: MARKETING
VLAN 210: FINANCE
1. Configure the VLANs on the designated switches and assign them as access ports to the interfaces connected to the PCs.
2. Configure the e0/2 interfaces on Sw1 and Sw2 as 802.1q trunks with only the required VLANs permitted.
3. Configure the e0/3 interfaces on Sw2 and Sw3 as 802.1q trunks with only the required VLANs permitted.
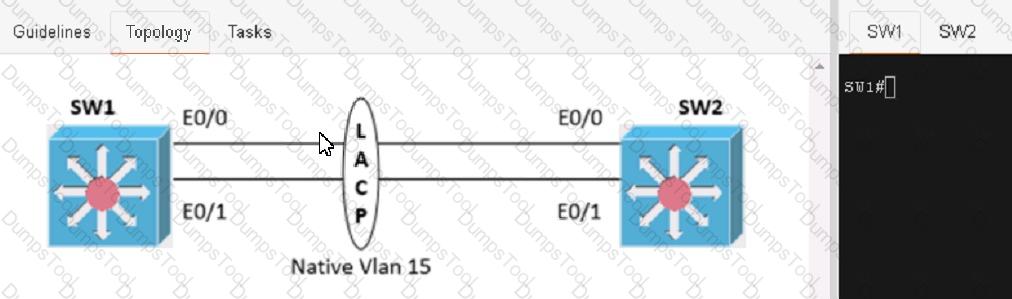
Physical connectivity is implemented between the two Layer 2 switches, and the network connectivity between them must be configured
1. Configure an LACP EtherChannel and number it as 1; configure it between switches SW1 and SVV2 using interfaces Ethernet0/0 and Ethernet0/1 on both sides. The LACP mode must match on both ends
2 Configure the EtherChannel as a trunk link.
3. Configure the trunk link with 802.1 q tags.
4. Configure the native VLAN of the EtherChannel as VLAN 15.
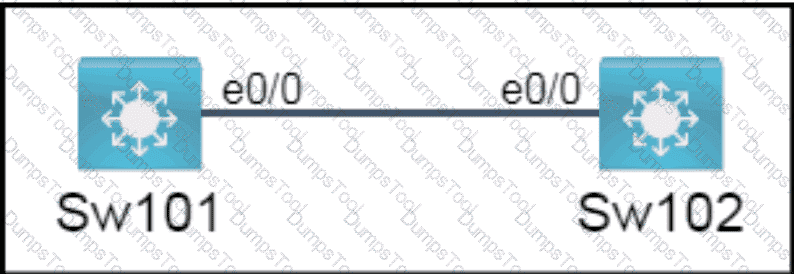
All physical cabling is in place. A company plans to deploy 32 new sites.
The sites will utilize both IPv4 and IPv6 networks.
1 . Subnet 172.25.0.0/16 to meet the subnet requirements and maximize
the number of hosts
Using the second subnet
• Assign the first usable IP address to e0/0 on Sw1O1
• Assign the last usable IP address to e0/0 on Sw102
2. Subnet to meet the subnet requirements and maximize
the number of hosts
c Using the second subnet
• Assign an IPv6 GUA using a unique 64-Bit interface identifier
on e0/0 on Sw101
• Assign an IPv6 GUA using a unique 64-Bit interface identifier
on eO/O on swi02
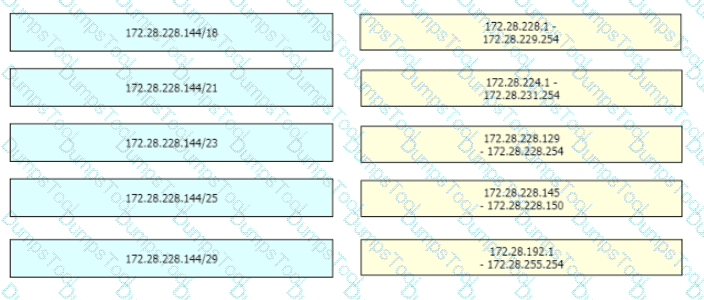
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using
the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
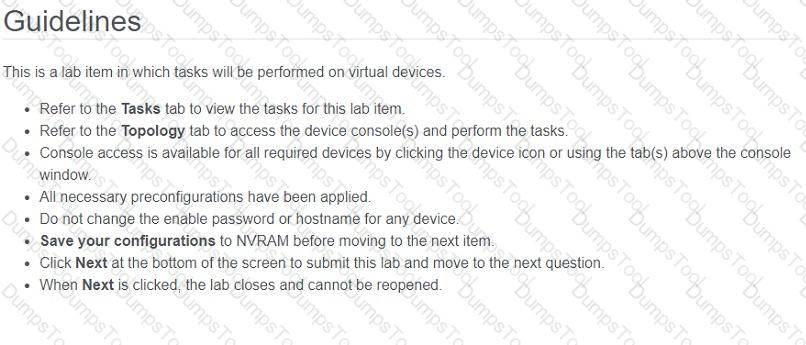
All physical cabling between the two switches is installed. Configure the network connectivity between the switches using the designated VLANs and interfaces.
1. Configure VLAN 100 named Compute and VLAN 200 named Telephony where required for each task.
2. Configure Ethernet0/1 on SW2 to use the existing VLAN named Available.
3. Configure the connection between the switches using access ports.
4. Configure Ethernet0/1 on SW1 using data and voice VLANs.
5. Configure Ethemet0/1 on SW2 so that the Cisco proprietary neighbor discovery protocol is turned off for the designated interface only.
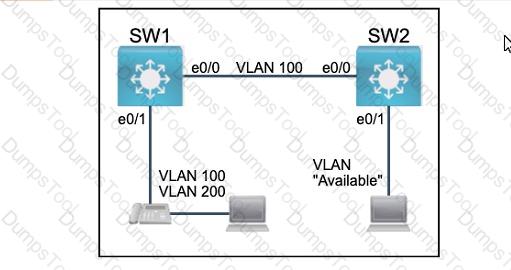
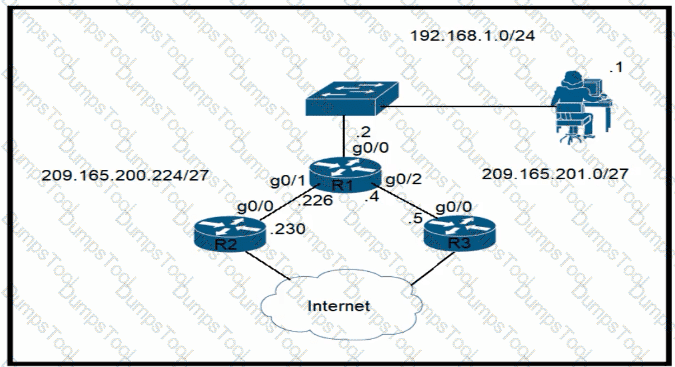
All physical cabling is in place. Router R4 and PCI are fully configured and
inaccessible. R4 ' s WAN interfaces use .4 in the last octet for each subnet.
Configurations should ensure that connectivity is established end-to-end.
1 . Configure static routing to ensure RI prefers the path through R2 to
reach only PCI on R4 ' s LAN
2. Configure static routing that ensures traffic sourced from RI will take
an alternate path through R3 to PCI in the event of an outage along
the primary path
3. Configure default routes on RI and R3 to the Internet using the least number of hops
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using
the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
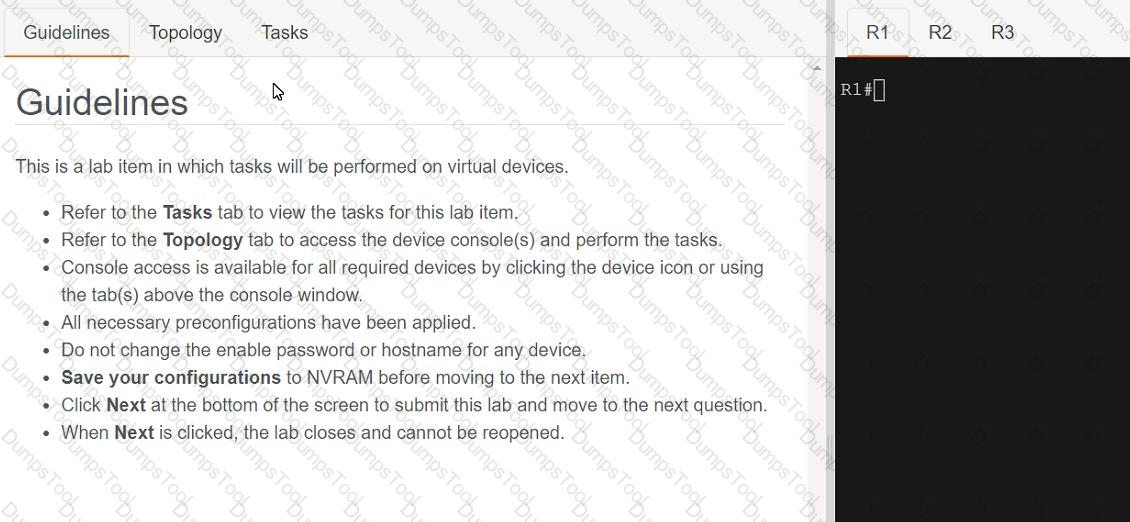
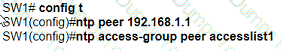
Connectivity between three routers has been established, and IP services must be configured jn the order presented to complete the implementation Tasks assigned include configuration of NAT, NTP, DHCP, and SSH services.
1. All traffic sent from R3 to the R1 Loopback address must be configured for NAT on R2. All source addresses must be translated from R3 to the IP address of Ethernet0/0 on R2, while using only a standard access list named NAT To verify, a ping must be successful to the R1 Loopback address sourced from R3. Do not use NVI NAT configuration.
2. Configure R1 as an NTP server and R2 as a client, not as a peer, using the IP address of the R1 Ethernet0/2 interface. Set the clock on the NTP server for midnight on January 1, 2019.
3. Configure R1 as a DHCP server for the network 10.1.3.0/24 in a pool named TEST. Using a single command, exclude addresses 1-10 from the range. Interface Ethernet0/2 on R3 must be issued the IP address of 10.1.3.11 via DHCP.
4. Configure SSH connectivity from R1 to R3, while excluding access via other remote connection protocols. Access for user root and password Cisco must be set on router R3 using RSA and 1024 bits. Verify connectivity using an SSH session from router R1 using a destination address of 10.1.3.11. Do NOT modify console access or line numbers to accomplish this task.
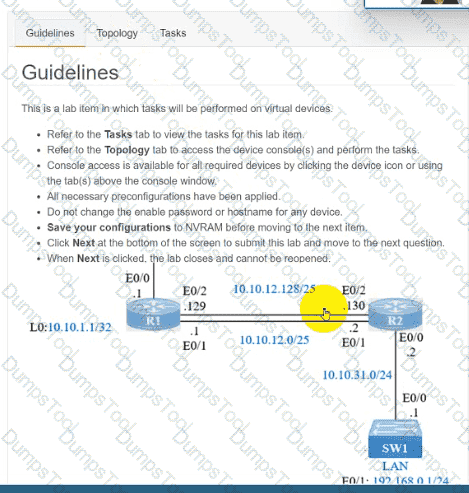
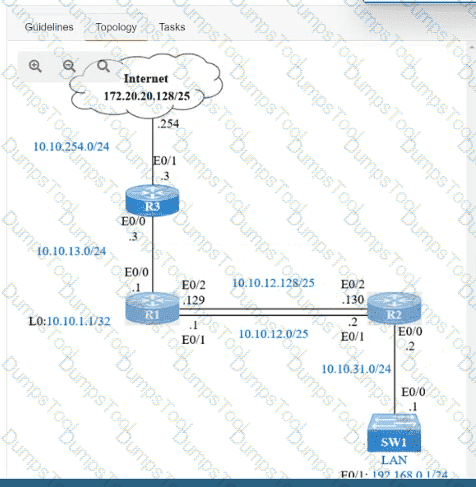
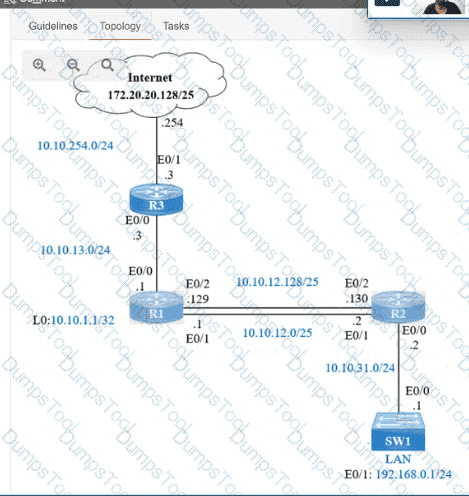
IP connectivity and OSPF are preconfigured on all devices where necessary. Do not make any changes to the IP addressing or OSPF. The company policy uses connected interfaces and next hops when configuring static routes except for load balancing or redundancy without floating static. Connectivity must be established between subnet 172.20.20.128/25 on the Internet and the LAN at 192.168.0.0/24 connected to SW1:
1. Configure reachability to the switch SW1 LAN subnet in router R2.
2. Configure default reachability to the Internet subnet in router R1.
3. Configure a single static route in router R2 to reach to the Internet subnet considering both redundant links between routers R1 and R2. A default route is NOT allowed in router R2.
4. Configure a static route in router R1 toward the switch SW1 LAN subnet where the primary link must be through Ethernet0/1. and the backup link must be through Ethernet0/2 using a floating route. Use the minimal administrative distance value when required.
Which cable type must be used to interconnect one switch using 1000 BASE-SX GBIC modules and another switch using 1000 BASE-SX SFP modules?
Refer to the exhibit.
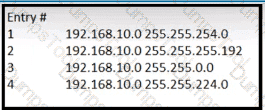
Which entry is the longest prefix match for host IP address 192.168.10.5?
A packet from a company s branch office is destined to host 172.31.0.1 at headquarters. The sending router has three possible matches in its routing table for the packet prefixes: 172.31.0.0/16, 172.31.0.0/24, and 172.31.0.0/25. How does the router handle the packet?
Refer to the exhibit.
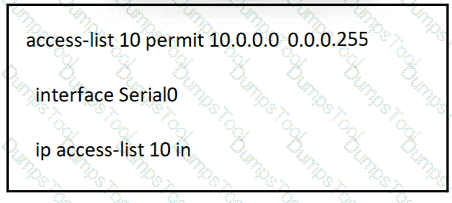
A network administrator must permit traffic from the 10.10.0.0/24 subnet to the WAN on interface Serial0. What is the effect of the configuration as the administrator applies the command?
Refer to the exhibit.
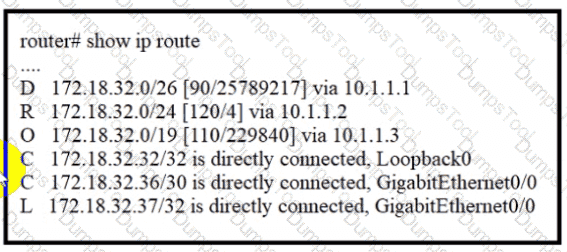
A packet sourced from 172.18.33.2 is destined for 172.18.32.38. Where does the router forward the packet?
Which type of port is used to connect to the wired network when an autonomous AP maps two VLANs to its WLANs?
Refer to the exhibit.
How many objects are present in the given JSON-encoded data?
Drag and drop the TCP/IP protocols from the left onto their primary transmission protocols on the right.
Refer to the exhibit.
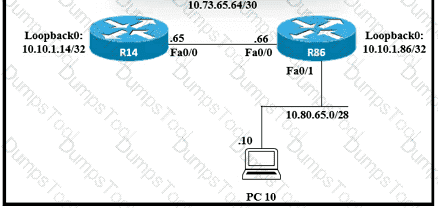
Router R14 is in the process of being configured. Which configuration must be used to establish a host route to PC 10?
An engineer must configure a core router with a floating static default route to the backup router at 10.200.0.2.
What must be considered for a locally switched FlexConnect AP if the VLANs that are used by the AP and client access are different?
A network analyst is tasked with configuring the date and time on a router using EXEC mode. The date must be set to January 1. 2020 and the time must be set to 12:00 am. Which command should be used?
Refer to the exhibit.
A network engineer must configure NETCONF. After creating the configuration, the engineer gets output from the command show line but not from show running-config. Which command completes the configuration?
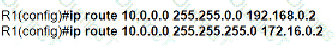
Refer to the exhibit.
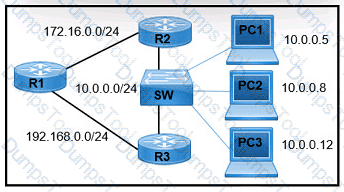
A network engineer must configure R1 so that it sends all packets destined to the 10.0.0.0/24 network to R3, and all packets destined to PCI to R2. Which configuration must the engineer implement?
A)
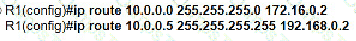
B)
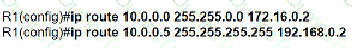
C)
D)
Refer to the exhibit
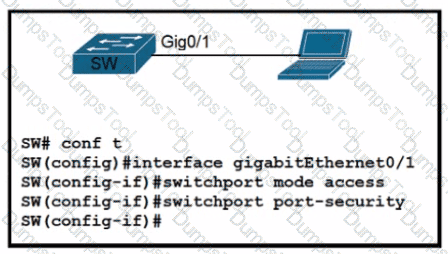
A network engineer started to configure port security on a new switch. These requirements must be met:
* MAC addresses must be learned dynamically
* Log messages must be generated without disabling the interface when unwanted traffic is seen
Which two commands must be configuredd to complete this task " ? (Choose two)
Which IP header field is changed by a Cisco device when QoS marking is enabled?
Refer to the exhibit.
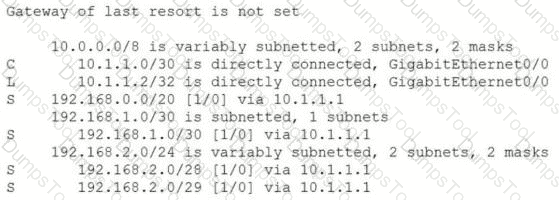
An engineer is checking the routing table in the main router to identify the path to a server on the network. Which route does the router use to reach the server at 192.168.2.2?
Which protocol must be implemented to support separate authorization and authentication solutions for wireless APs?
Refer to the exhibit.
An IPv6 address must be obtained automatically on the LAN interface on R1 Which command must be implemented to accomplish the task?
What is a reason to configure a trunk port that connects to a WLC distribution port?
What provides connection redundancy increased bandwidth and load sharing between a wireless LAN controller and a Layer 2 switch?
When the active router in an HSRP group fails, what router assumes the role and forwards packets?
How do AAA operations compare regarding user identification, user services and access control?
Which unified access point mode continues to serve wireless clients after losing connectivity to the Cisco Wireless LAN Controller?
Refer to the exhibit.
If R1 receives a packet destined to 172.161.1, to which IP address does it send the packet?
Drag and drop the TCP/IP protocols from the left onto the transmission protocols on the right
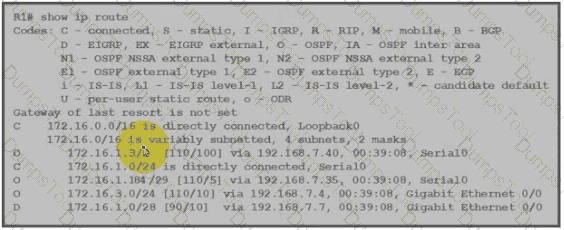
Refer to the exhibit.
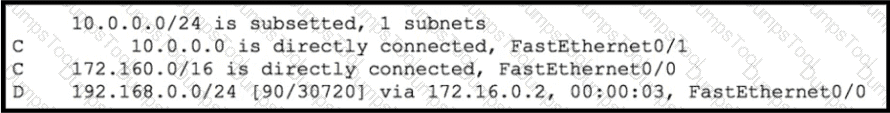
Which route type does the routing protocol Code D represent in the output?
Refer to the exhibit.
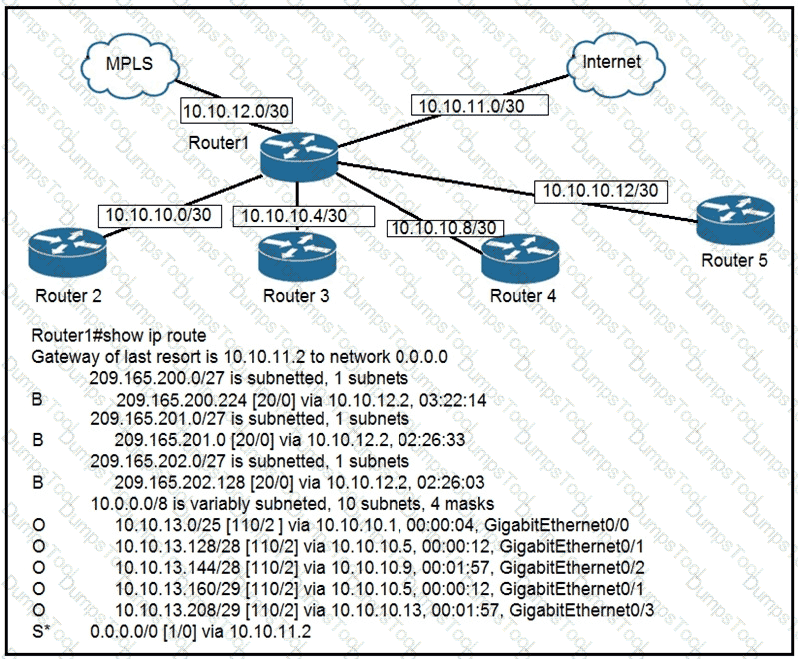
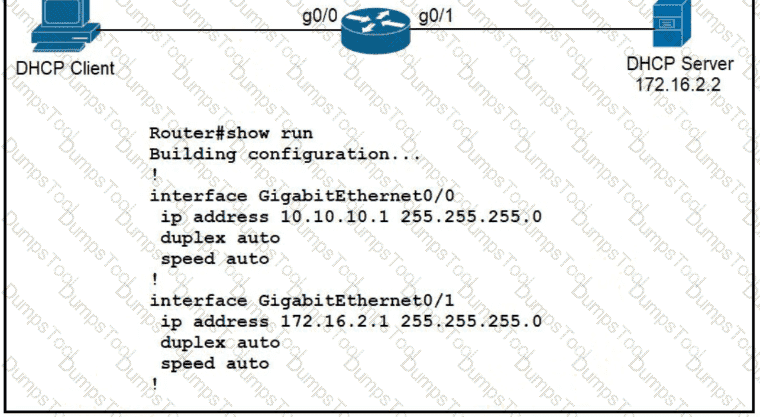
To which device does Router1 send packets that are destined to host 10.10.13.165?
How does a Cisco Unified Wireless network respond to Wi-Fi channel overlap?
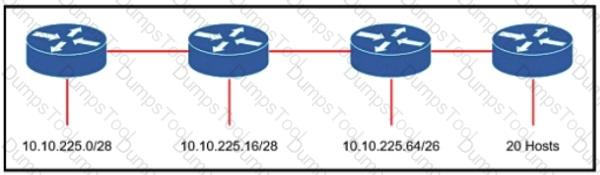
Refer to the exhibit. An engineer must add a subnet for a new office that will add 20 users to the network. Which IPv4 network and subnet mask combination does the engineer assign to minimize wasting addresses?
What are two reasons for an engineer to configure a floating static route? (Choose two)
When OSPF learns multiple paths to a network, how does it select a route?
In QoS, which prioritization method is appropriate for interactive voice and video?
Refer to the exhibit.
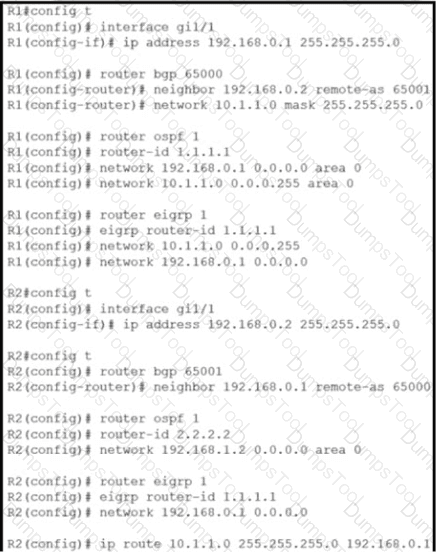
Router R2 is configured with multiple routes to reach network 10 1.1 0/24 from router R1. What protocol is chosen by router R2 to reach the destination network 10.1 1 0/24?
Refer to the exhibit.
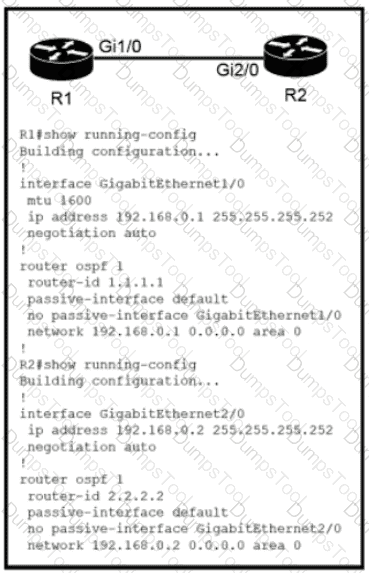
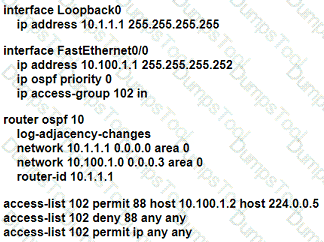
Which configuration issue is preventing the OSPF neighbor relationship from being established between the two routers?
Refer to the exhibit.
An engineer must configure GigabitEthernet1/1 to accommodate voice and data traffic Which configuration accomplishes this task?

What is the effect when loopback interfaces and the configured router ID are absent during the OSPF Process configuration?
Which two components are needed to create an Ansible script that configures a VLAN on a switch? (Choose two.)
A network administrator needs to aggregate 4 ports into a single logical link which must negotiate layer 2 connectivity to ports on another switch. What must be configured when using active mode on both sides of the connection?
Which goal is achieved by the implementation of private IPv4 addressing on a network?
Refer to the exhibit.
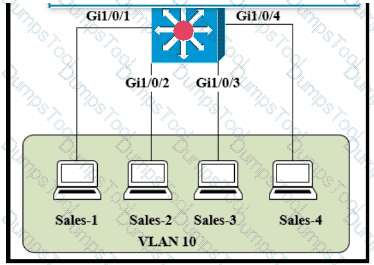
The entire contents of the MAC address table are shown. Sales-4 sends a data frame to Sales-1.
What does the switch do as it receives the frame from Sales-4?
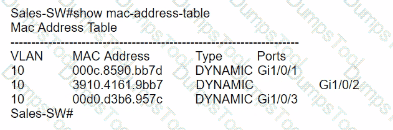
Drag and drop the Cisco Wireless LAN Controller security settings from the left onto the correct security mechanism categories on the right.
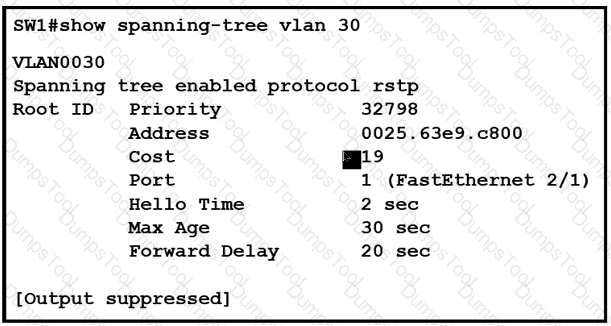
Refer to the exhibit.
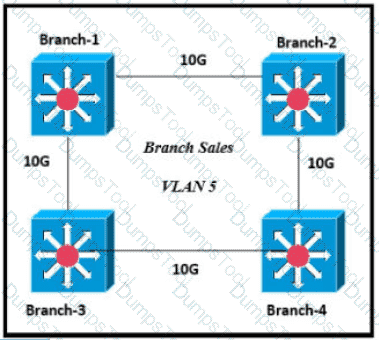
Only four switches are participating in the VLAN spanning-tree process.
Branch-1 priority 614440
Branch-2: priority 39082416
Branch-3: priority 0
Branch-4: root primary
Which switch becomes the permanent root bridge for VLAN 5?
Refer to the exhibit.
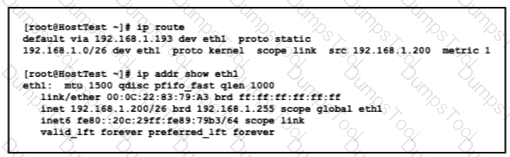
Drag and drop the networking parameters from the left onto the correct values on the right.
If a switch port receives a new frame while it is actively transmitting a previous frame, how does it process the frames?
An office has 8 floors with approximately 30-40 users per floor What command must be configured on the router Switched Virtual Interface to use address space efficiently?
Refer to the exhibit.
R5 is the current DR on the network, and R4 is the BDR. Their interfaces are flapping, so a network engineer wants the OSPF network to elect a different DR and BDR. Which set of configurations must the engineer implement?
A)
B)
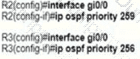
C)
D)
After installing a new Cisco ISE server, which task must the engineer perform on the Cisco WLC to connect wireless clients on a specific VLAN based on their credentials?
An engineer configured an OSPF neighbor as a designated router. Which state verifies the designated router is in the proper mode?
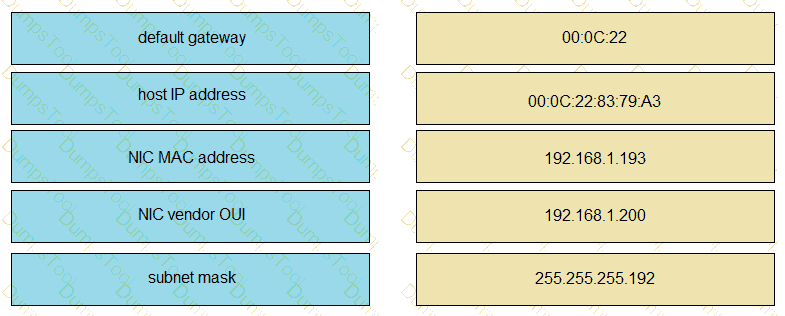
Refer to the exhibit.
What action establishes the OSPF neighbor relationship without forming an adjacency?
Refer to the exhibit.
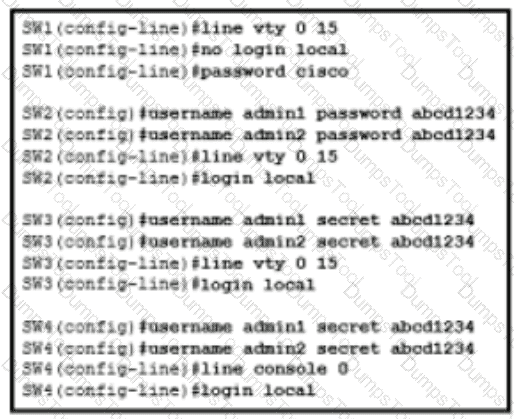
An administrator configures four switches for local authentication using passwords that are stored in a cryptographic hash. The four switches must also support SSH access for administrators to manage the network infrastructure. Which switch is configured correctly to meet these requirements?
Refer to the exhibit.
Router R1 Fa0/0 is unable ping router R3 Fa0/1.
Which action must be taken in router R1 to help resolve the configuration issue?
Which configuration management mechanism uses TCP port 22 by default when communicating with managed nodes?
Router A learns the same route from two different neighbors, one of the neighbor routers is an OSPF neighbor and the other is an EIGRP neighbor. What is the administrative distance of the route that will be installed in the routing table?
What are two similarities between UTP Cat 5e and Cat 6a cabling? (Choose two.)
What is the primary different between AAA authentication and authorization?
On workstations running Microsoft Windows, which protocol provides the default gateway for the device?
Refer to the exhibit.
The default-information originate command is configured under the R1 OSPF configuration After testing workstations on VLAN 20 at Site B cannot reach a DNS server on the Internet Which action corrects the configuration issue?
A Cisco IP phone receive untagged data traffic from an attached PC. Which action is taken by the phone?
A network administrator must to configure SSH for remote access to router R1 The requirement is to use a public and private key pair to encrypt management traffic to and from the connecting client.
Which configuration, when applied, meets the requirements?
Drag the descriptions of IP protocol transmissions from the left onto the IP traffic types on the right.
Which technology can prevent client devices from arbitrarily connecting to the network without state remediation?
When a WLAN with WPA2 PSK is configured in the Wireless LAN Controller GUI which format is supported?
Which action does the router take as it forwards a packet through the network?
Refer to the exhibit.
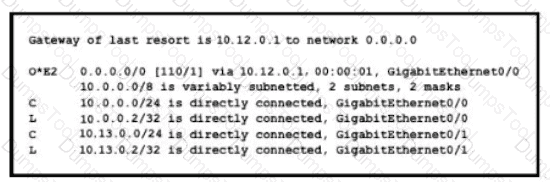
If configuring a static default route on the router with the ip route 0.0.0.0 0.0.0.0 10.13.0.1 120 command how does the router respond?
A network engineer must create a diagram of a multivendor network. Which command must be configured on the Cisco devices so that the topology of the network can be mapped?
Refer to the exhibit.
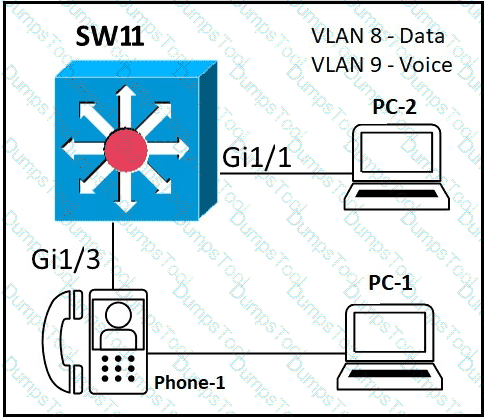
An administrator must configure interfaces Gi1/1 and Gi1/3 on switch SW1. PC-1 and PC-2 must be placed in the Data VLAN and Phone-1 must be placed in the Voice VLAN Which configuration meets these requirements?
Which protocol does an access point use to draw power from a connected switch?
Refer to the exhibit.
Traffic sourced from the loopback0 Interface is trying to connect via ssh to the host at 10.0.1.15. What Is the next hop to the destination address?
An administrator must use the password complexity not manufacturer-name command to prevent users from adding “cisco” as a password. Which command must be issued before this command?
Refer to the exhibit.
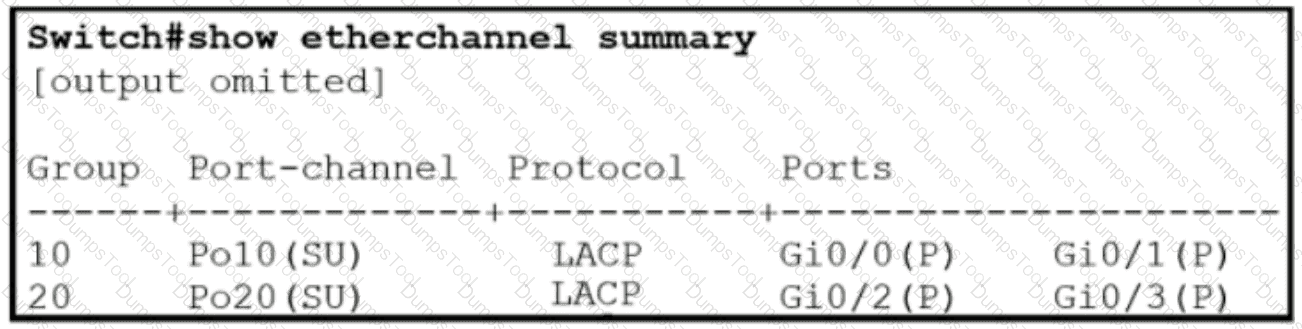
Which two commands were used to create port channel 10? (Choose two )
Drag and drop the IPv6 addresses from the left onto the corresponding address types on the right.
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.
An implementer is preparing hardware for virtualization to create virtual machines on a host. What is needed to provide communication between hardware and virtual machines?
Refer to the exhibit.
Which minimum configuration items are needed to enable Secure Shell version 2 access to R15?
A)
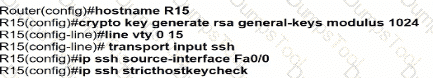
B)

C)
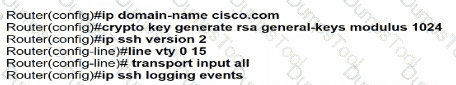
D)
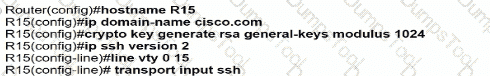
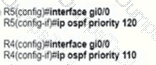
Refer to the exhibit.
Which action must be taken to ensure that router A is elected as the DR for OSPF area 0?
Which QoS traffic handling technique retains excess packets in a queue and reschedules these packets for later transmission when the configured maximum bandwidth has been surpassed?
An engineer must configure traffic for a VLAN that is untagged by the switch as it crosses a trunk link. Which command should be used?
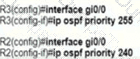
Refer to the exhibit.
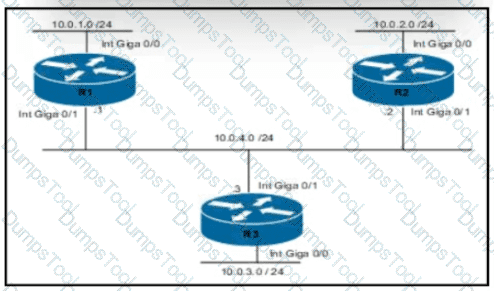
Routers R1 and R3 have the default configuration The router R2 priority is set to 99 Which commands on R3 configure it as the DR in the 10.0.4.0/24 network?
Refer to the exhibit.
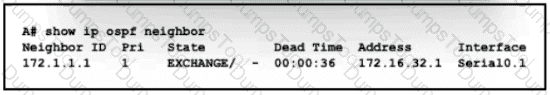
An engineer assumes a configuration task from a peer Router A must establish an OSPF neighbor relationship with neighbor 172.1.1.1 The output displays the status of the adjacency after 2 hours. What is the next step in the configuration process for the routers to establish an adjacency?
Refer to the exhibit.
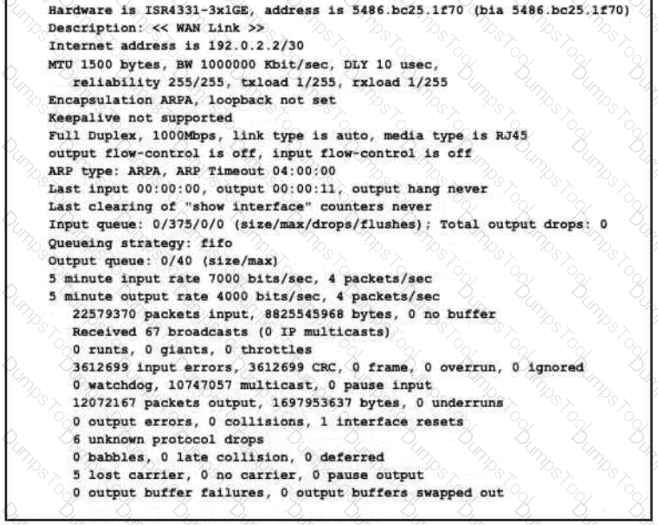
What is a reason for poor performance on the network interface?
Which value is the unique identifier that an access point uses to establish and maintain wireless connectivity to wireless network devices?
Refer to the exhibit.
What are two conclusions about this configuration? {Choose two.)
A network administrator enabled port security on a switch interface connected to a printer. What is the next configuration action in order to allow the port to learn the MAC address of the printer and insert it into the table automatically?
Refer to the exhibit.
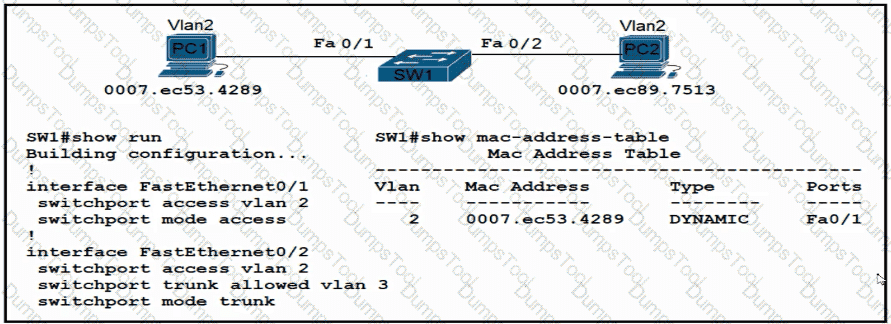
An engineer has started to configure replacement switch SW1. To verify part of the configuration, the engineer issued the commands as shown and noticed that the entry for PC2 is missing. Which change must be applied to SW1 so that PC1 and PC2 communicate normally?
A)

B)

C)
D)
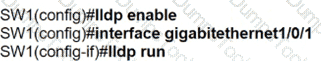
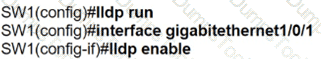
Refer to the exhibit.
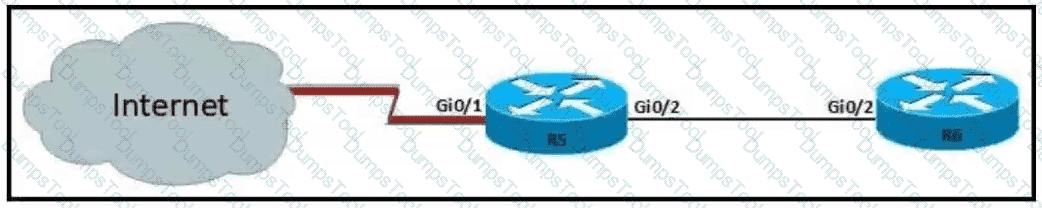
For security reasons, automatic Neighbor Discovery must be disabled on the R5 Gi0/1 interface. These tasks must be completed:
• Disable all Neighbor Discovery methods on R5 interface GiO/1.
• Permit Neighbor Discovery on R5 interface GiO/2.
• Verify there are no dynamically learned neighbors on R5 interface Gi0/1.
• Display the IP address of R6*s interface Gi0/2.
Which configuration must be used?
Why would VRRP be implemented when configuring a new subnet in a multivendor environment?
Refer to the exhibit.
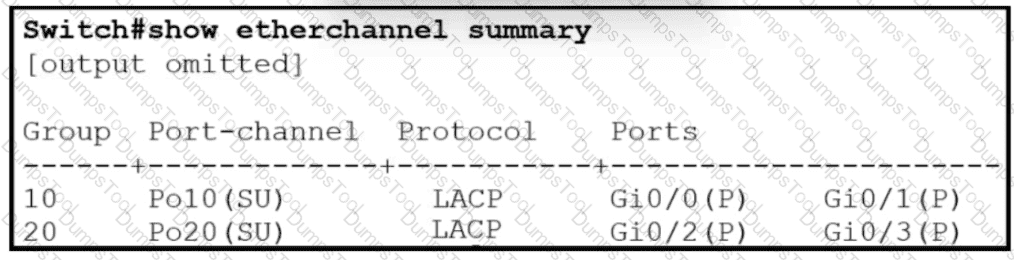
Which two commands when used together create port channel 10? (Choose two.)
Refer to the exhibit.
Users need to connect to the wireless network with IEEE 802.11r-compatible devices. The connection must be maintained as users travel between floors or to other areas in the building What must be the configuration of the connection?
Refer to the exhibit.
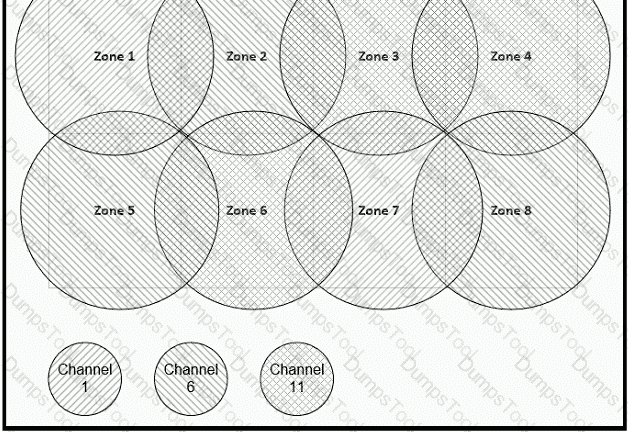
Between which zones do wireless users expect to experience intermittent connectivity?
Refer to the exhibit.
Router R1 currently is configured to use R3 as the primary route to the Internet, and the route uses the default administrative distance settings. A network engineer must configure R1 so that it uses R2 as a backup, but only if R3 goes down. Which command must the engineer configure on R1 so that it correctly uses R2 as a backup route, without changing the administrative distance configuration on the link to R3?
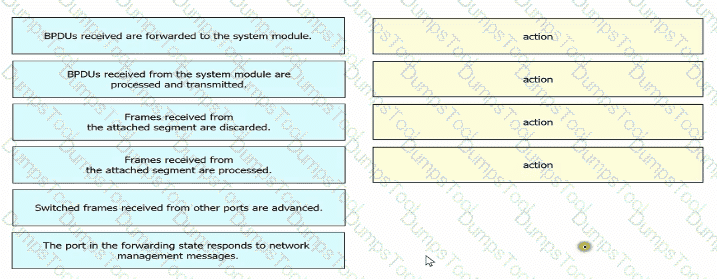
Drag and drop the Rapid PVST+ forwarding state actions from the loft to the right. Not all actions are used.
Which two practices are recommended for an acceptable security posture in a network? (Choose two)
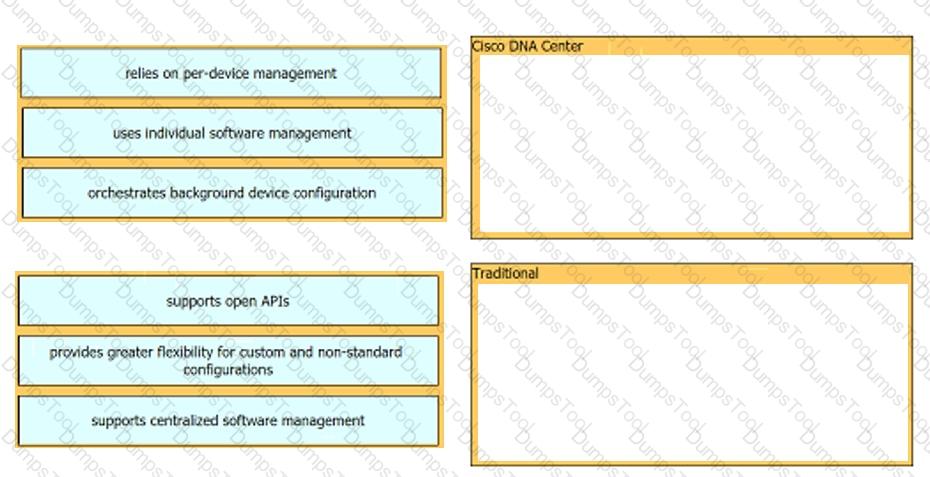
Drag and drop each characteristic of device-management technologies from the left onto the deployment type on the right.
While examining excessive traffic on the network, it is noted that all incoming packets on an interface appear to be allowed even though an IPv4 ACL is applied to the interface.
Which two misconfigurations cause this behavior? (Choose two)
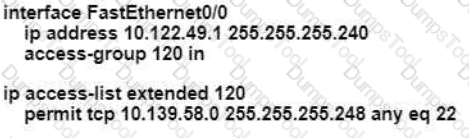
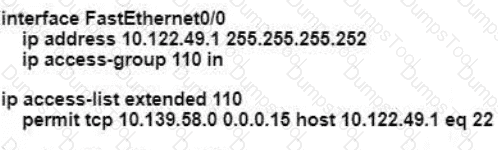
An engineer is configuring remote access to a router from IP subnet 10.139.58.0/28. The domain name, crypto keys, and SSH have been configured. Which configuration enables the traffic on the destination router?
A)
B)
C)
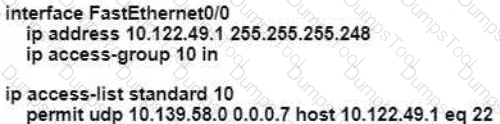
D)
Which two wireless security standards use Counter Mode with Cipher Block Chaining Message Authentication Code Protocol for encryption and data integrity ' ? (Choose two.)
Which action implements physical access control as part of the security program of an organization?
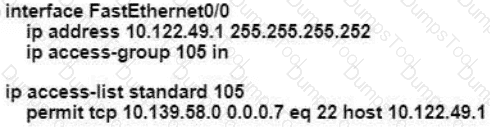
Refer to the exhibit.
An engineer is configuring a new router on the network and applied this configuration. Which additional configuration allows the PC to obtain its IP address from a DHCP server?
Refer to the exhibit.
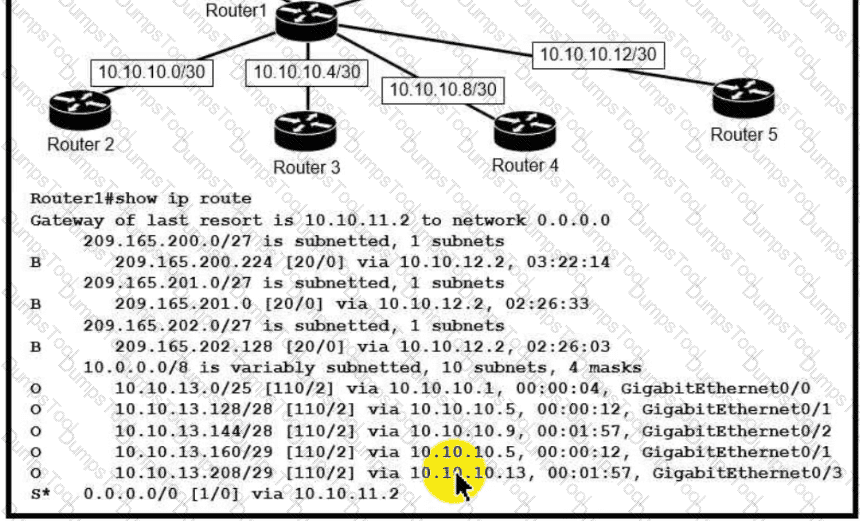
Which next-hop IP address does Routed use for packets destined to host 10 10.13.158?
A network engineer is installing an IPv6-only capable device. The client has requested that the device IP address be reachable only from the internal network. Which type of IPv6 address must the engineer assign?

Refer to the exhibit. Each router must be configured with the last usable IP address in the subnet. Which configuration fulfills this requirement?

A network engineer is replacing the switches that belong to a managed-services client with new Cisco Catalyst switches. The new switches will be configured for updated security standards, including replacing Telnet services with encrypted connections and doubling the modulus size from 1024. Which two commands must the engineer configure on the new switches? (Choose two.)
After a recent security breach and a RADIUS failure, an engineer must secure the console port of each enterprise router with a local username and password. Which configuration must the engineer apply to accomplish this task?
Refer to the exhibit.
An OSPF neighbor relationship must be configured using these guidelines:
• R1 is only permitted to establish a neighbor with R2
• R1 will never participate in DR elections
• R1 will use a router-id of 10.1.1.1
Which configuration must be used?
A)
B)
C)
D)
Refer to the exhibit.
Which command must be issued to enable a floating static default route on router A?
An engineer is configuring switch SW1 to act an NTP server when all upstream NTP server connectivity fails. Which configuration must be used?
A)
B)
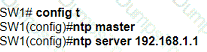
C)
D)
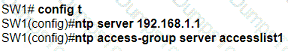
Drag and drop the QoS terms from the left onto the descriptions on the right.
Refer to the exhibit.
Which plan must be Implemented to ensure optimal QoS marking practices on this network?
Refer to the exhibit.
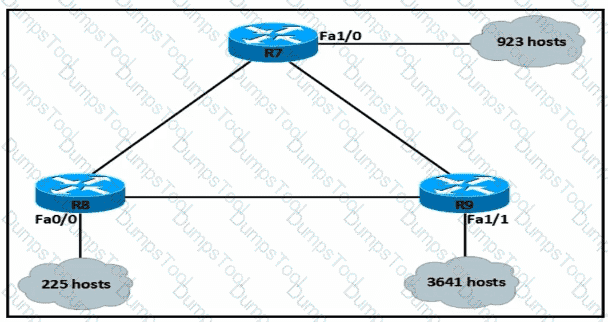
An IP subnet must be configured on each router that provides enough addresses for the number of assigned hosts and anticipates no more than 10% growth for new hosts. Which configuration script must be used?
A)
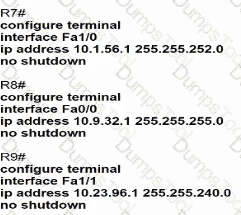
B)
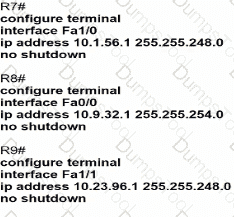
C)
D)
What provides centralized control of authentication and roaming In an enterprise network?
Refer to the exhibit.

Traffic that is flowing over interface TenGigabitEthernet0/0 experiences slow transfer speeds. What is the reason for the issue?
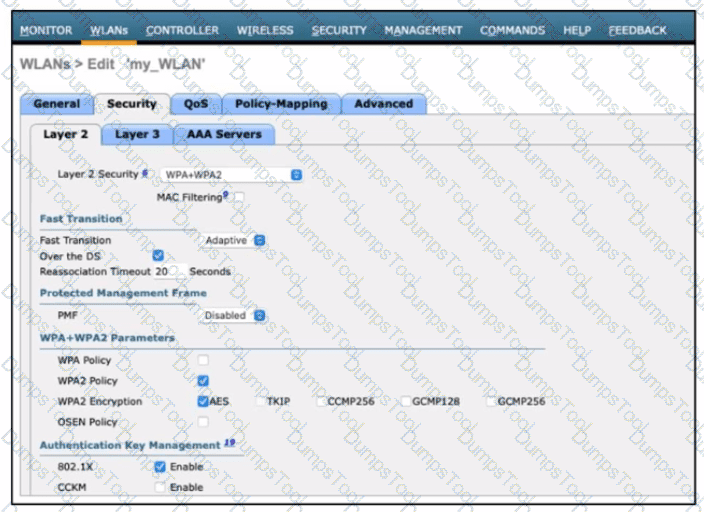
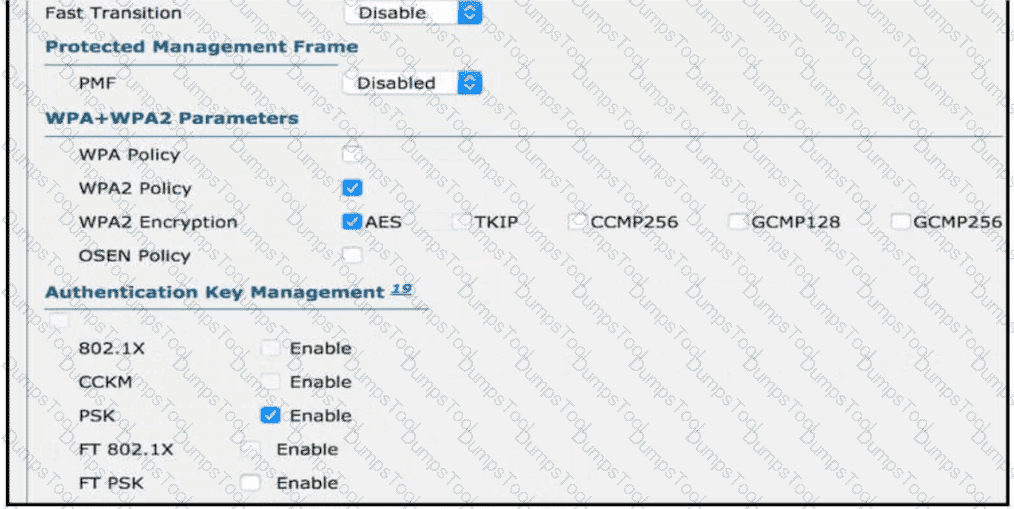
Refer to the exhibit.

What must be configured to enable 802.11w on the WLAN?
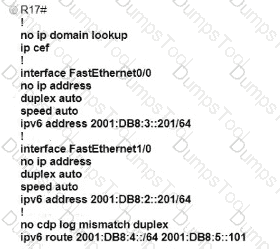
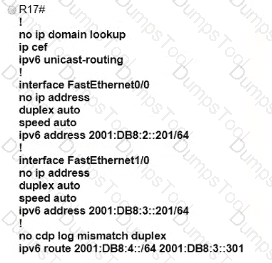
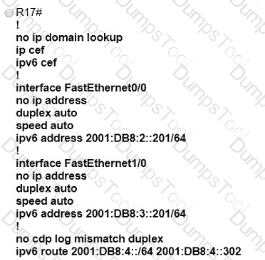
Refer to the exhibit.
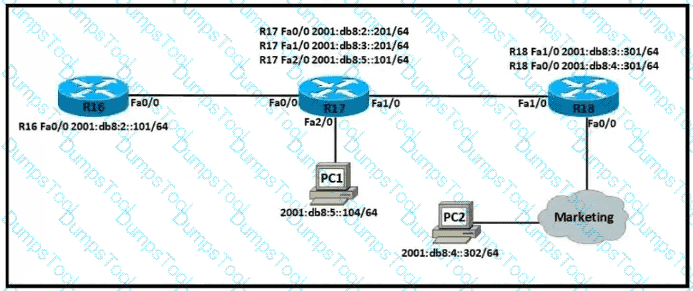
Which IPv6 configuration is required for R17 to successfully ping the WAN interface on R18?
A)
B)
C)
D)

Refer to the exhibit.
Load-balanced traffic is coming in from the WAN destined to a host at 172.16.1.190. Which next-hop is used by the router to forward the request?
Refer to the exhibit.
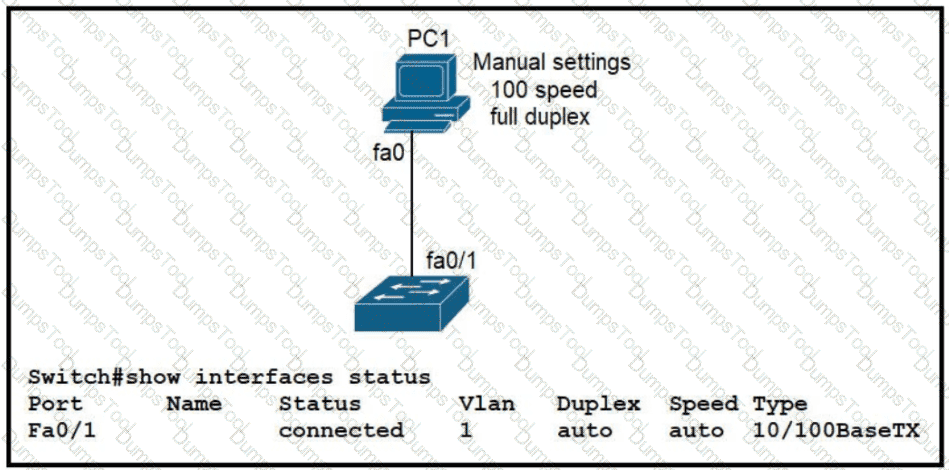
The link between PC1 and the switch is up. but it is performing poorly. Which interface condition is causing the performance problem?
Refer to the exhibit. An engineer is asked to configure router R1 so that it forms an OSPF single-area neighbor relationship with R2. Which command sequence must be implemented to configure the router?