Where do you configure the list of Endpoint Servers (or load balancers) to which a DLP Agent can report?
What should an incident responder select in the Enforce management console to remediate multiple incidents simultaneously?
A DLP administrator determines that the \SymantecDLP\Protect\Incidents folder on the Enforce server contains. BAD files dated today, while other. IDC files are flowing in and out of the \Incidents directory. Only .IDC files larger than 1MB are turning to .BAD files.
What could be causing only incident data smaller than 1MB to persist while incidents larger than 1MB change to .BAD files?
A divisional executive requests a report of all incidents generated by a particular region, summarized by department.
What does the DLP administrator need to configure to generate this report?
Which statement accurately describes where Optical Character Recognition (OCR) On-Premises DLP Core components must be installed?
Which option correctly describes the two-tier installation type for Symantec DLP?
A DLP administrator is attempting to add a new Network Discover detection server from the Enforce management console. However, the only available options are Network Monitor and Endpoint servers.
What should the administrator do to make the Network Discover option available?
A DLP administrator has added several approved endpoint devices as exceptions to an Endpoint Prevent policy that blocks the transfer of sensitive data. However, data transfers to these devices are still being blocked.
What is the first action an administrator should take to enable data transfers to the approved endpoint devices?
A DLP administrator is checking the System Overview in the Enforce management console, and all of the detection servers are showing as “unknown”. The Vontu services are up and running on the detection servers. Thousands of .IDC files are building up in the Incidents directory on the detection servers. There is good network connectivity between the detection servers and the Enforce server when testing with the telnet command.
How should the administrator bring the detection servers to a running state in the Enforce management console?
Which tool must a DLP administrator run to certify the database prior to upgrading DLP?
What is one difference between Exact Data Matching (EDM) and Exact Match Data Identifiers (EMDI)?
Which two detection technology options run on the DLP agent? (Choose two.)
Which of the following actions can you implement ONLY as a Smart Response rule (and not as an automates response rule)?
A DLP administrator needs to stop the PacketCapture process on a detection server. Upon inspection of the Server Detail page, the administrator discovers that all processes are missing from the display.
What are the processes missing from the Server Detail page display?
A DLP administrator created a new agent configuration for an Endpoint server. However, the endpoint agents fail to receive the new configuration.
What is one possible reason that the agent fails to receive the new configuration?
Which two detection technology options ONLY run on a detection server? (Choose two.)
Refer to the exhibit.
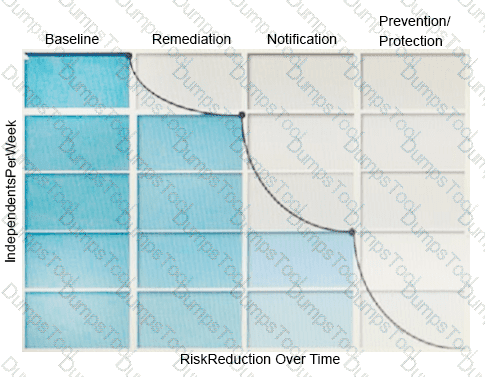
What activity should occur during the baseline phase, according to the risk reduction model?
Why is it important for an administrator to utilize the grid scan feature?
Which two Infrastructure-as-a-Service providers are supported for hosting Cloud Prevent for Office 365? (Choose two.)
What are two (2) reasons an administrator should utilize a manual configuration to determine the endpoint location? (Choose two.)
What is the Symantec recommended order for stopping Symantec DLP services on a Windows Enforce server?
A customer needs to integrate information form DLP incidents into external Governance, Risk, and Compliance dashboards.
Which feature should a third-party component integrate with to provide dynamic reporting, create custom incident remediation processes, or support business processes?
Which product is able to replace a confidential document residing on a file share with a marker file explaining why the document was removed?
Which detection server is available from Symantec as a hardware appliance?
Why would an administrator set the Similarity Threshold to zero when testing and tuning a Vector Machine Learning (VML) profile?