During the Port Scan phase what could the Warning level error "No results returned from probe." mean?
As a first step in horizontal discovery, which of the following is where the Shazzam probe is placed in a request?
Which of the choices are types of temporary variables in a discovery pattern?
Choose 2 answers
Which of the following properties define the maximum overall size for the returned payload that comes from patterns?
Which of the choices below best represent key capabilities of a ServiceNow ITOM Enterprise solution? (Choose two.)
Which selections are necessary to create a custom horizontal pattern to discover a computer operating system?
On the ECC Queue, sensor records have a Queue value of ___________ and probe records have a Queue value of ___________.
A discovery runs against a Windows Server returning the following attribute values for the first time:
name = WindowsSN1 serial_number = 12321
A subsequent discovery is ran against a different Windows Server returning the following attribute values: name = WindowsSN2
serial_number = 12321
With only base system CI Identifiers configured, which of the following is true?
What pattern operation allows the transfer of a file from the MID Server to a target?
When designing steps with operations requiring variables, it is best practice to do what?
Which metrics comprise the Completeness KPI for CMDB Health? (Choose two.)
Which of the following are the results of executing the WMI Query?
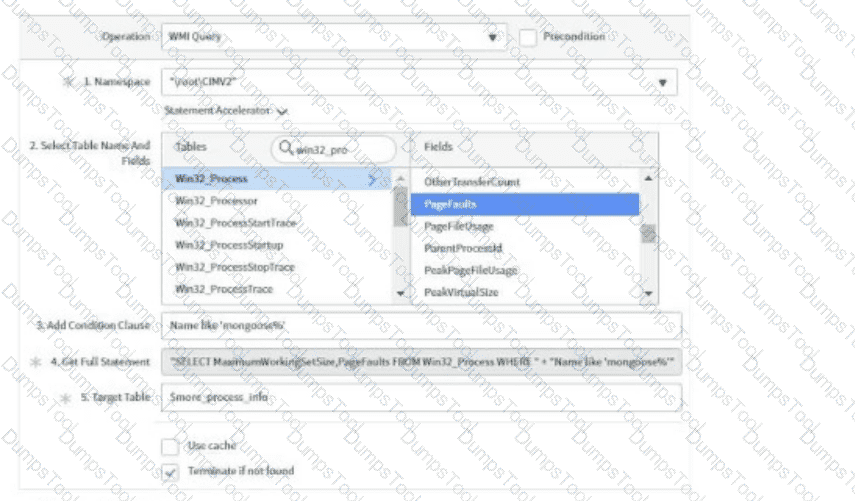
Choose 3 answers
Which of the following must be configured to allow a MID Server to access servers using WinRM?
Which of the following fields are editable from a Merge Table pattern operation?
Choose 3 answers
A Discovery Schedule contains a /24 subnet IP Range and a Shazzam batch size of 5000. How many times will a Shazzam probe be launched during discovery?
With multiple CI data sources, which choice is the best for determining which source can update a CI attribute?
After running Discovery and viewing the ECC Queue tab, what are some of the displayed default fields? (Choose three.)
Which of the following must be configured to allow a MID Server to access servers using WinRM? (Choose two.)
What would you see in the Discovery pattern log that you would not see in the ECC Queue?
From an SNMP Query pattern operation, which of the choices are valid Variable Types? (Choose two.)
What entry point type must a horizontal pattern have to execute from a process classifier?