SPLK-3001 Question Includes: Single Choice Questions: 97, Multiple Choice Questions: 2,
Enterprise Security’s dashboards primarily pull data from what type of knowledge object?
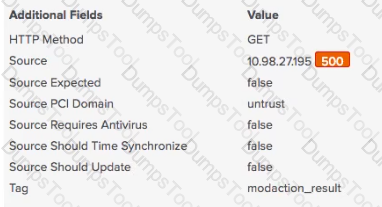
What kind of value is in the red box in this picture?
Which of the following actions would not reduce the number of false positives from a correlation search?
When investigating, what is the best way to store a newly-found IOC?
A newly built custom dashboard needs to be available to a team of security analysts In ES. How is It possible to Integrate the new dashboard?
Customers Passed
Splunk SPLK-3001
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted Splunk Exam SPLK-3001 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
Splunk Splunk Enterprise Security Certified Admin SPLK-3001 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing Splunk Splunk Enterprise Security Certified Admin SPLK-3001 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool SPLK-3001 Splunk Enterprise Security Certified Admin Exam Practice Questions is enormous and unmatched!
The Splunk SPLK-3001 Exam, also known as the Splunk Enterprise Security Certified Admin exam, assesses your expertise in event processing, normalization, settings, threat intelligence, and protocol intelligence configuration within Splunk Enterprise Security.
The Splunk SPLK-3001 exam is ideal for experienced Splunk platform administrators who want to specialize in security. Security professionals looking to elevate their careers as Splunk ES administrators can also benefit from this certification.
The SPLK-3001 exam covers a broad range of Splunk ES functionalities, including data ingestion, threat intelligence management, incident review, and security posture assessments.
No formal prerequisites exist for taking the SPLK-3001 exam. However, strong foundational knowledge of Splunk administration and security concepts is highly recommended.
The Splunk SPLK-3001 exam consists of 48 multiple-choice questions.
The duration of the Splunk SPLK-3001 exam is minutes.
Yes, you need to achieve a passing score of 70% or higher to earn the Splunk SPLK-3001 certification.
Dumpstool offers a variety of study materials for the Splunk Enterprise Security Certified Admin Certification Exam, including SPLK-3001 PDF questions, practice exams, and a study guide. These study materials provide SPLK-3001 real questions and detailed explanations to help you understand the concepts and prepare for the exam effectively.
Yes, Dumpstool offers a success guarantee and a money-back guarantee. If you do not pass the exam on your first attempt after using our SPLK-3001 questions and answers, you can request a full refund. This demonstrates our confidence in the quality of our SPLK-3001 exam questions and study guides.
Yes, Dumpstool offers a free demo of the Splunk SPLK-3001 questions and answers. You can access a sample of the SPLK-3001 practice questions to see the quality and effectiveness of our SPLK-3001 study guides before making a purchase. This allows you to make an informed decision about investing in our materials.