Which statement accurately describes the behavior of a Flow Network Security policy operating in Monitor mode?
An administrator uses Nutanix Flow to secure a three-tier application (Web, App, and Database tiers). After observing the traffic, they find that: The Web tier communicates with the App tier over HTTP (port 80) The App tier communicates with the Database tier over TCP port 1433 The Database tier does not initiate connections The Web tier receives inbound HTTP traffic from the corporate DMZ on port 8080 No other traffic should be allowed What should the administrator do to document and then securely apply these flows in Nutanix Flow?
In a Nutanix deployment, when is the Network Controller automatically enabled?
An administrator has a VPC with a single active gateway node that successfully peers with an external router using a single BGP GW and session. To eliminate a single point of failure, the administrator deploys a second BGP gateway to the VPC. After the second gateway is added and shows a healthy state, the external router still only sees a single BGP session. What is the most likely reason for the second session not being established on the external router?
An administrator has configured a VPC and associated a NAT external network. A virtual machine connected to a subnet within this VPC is required to be accessible externally. What action must the administrator take to accomplish this?
A VPC admin creates a policy to allow traffic between two IP subnets but forgets to enable reverse direction. What happens in this scenario?
An administrator creates an Isolation Policy in Prism Central to prevent communication between the Prod and Staging environments. The policy is in Enforce mode... but VMs in the two environments can still communicate. Which configuration issue most likely explains why the Isolation Policy is not blocking the traffic?
A customer wants to extend a VLAN subnet to a remote data center using VTEP. The administrator configures a Subnet Extension which shows UP in the Prism Interface, yet traffic fails to pass. Which setting is most likely misconfigured?
An administrator needs to ensure all web traffic (HTTP/HTTPS) from a specific subnet (10.100.20.0/24) is redirected through a third-party virtual firewall inside the VPC for Layer 7 inspection before reaching the internet. The firewall VM has an IP of 10.100.30.5 and is connected to a different subnet. What should be done to enforce this specific traffic path?
An administrator plans to upgrade the Network Controller in a Flow Virtual Networking deployment. The environment includes multiple AHV clusters managed by Prism Central. Which prerequisite must be verified before upgrading the Network Controller?
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
An administrator needs to make a web server VM, which is inside a private VPC overlay subnet, accessible from the external network. The administrator assigns a Floating IP to the VM, but the service is still unreachable from the outside. What is a likely reason for this failure?
Which step is required before placing the Flow Network Security software bundle on a local web server?
An administrator has deployed a microsegmentation policy in Nutanix Flow that allows certain VM traffic based on Active Directory (AD) user group membership. Users in a specific AD group report they are unable to access the VMs, while other users can connect without issues. The administrator suspects the problem is related to identity-based policy mapping. What should the administrator do to troubleshoot and resolve the access issue related to the identity-based policy?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
An administrator observes a Network Controller Unreachable alert in Prism Central for a specific AHV cluster. All other management tasks for the cluster from Prism Central are succeeding and the cluster itself reports a healthy status. Which step is the most appropriate to investigate the cause of this specific alert?
When setting up a Network Function VM for Service Insertion, an administrator needs to configure the vNICs that will be used for redirecting traffic. What is the correct configuration for the vNICs on the Network Function VM?
What entity is automatically created on the cluster hosting Prism Central when Microsegmentation is enabled?
Which policy is used to isolate a compromised VM in the most efficient way possible?
In Nutanix Flow, which action transitions a security policy from observing traffic to actively enforcing the rules?
An administrator finds that App tier VMs cannot connect to the Database tier on port 3306, and Flow logs show the traffic is being denied by a security policy. The Web tier communicates normally. What should the administrator do to allow the App tier to access the Database tier?
Refer to Exhibit:
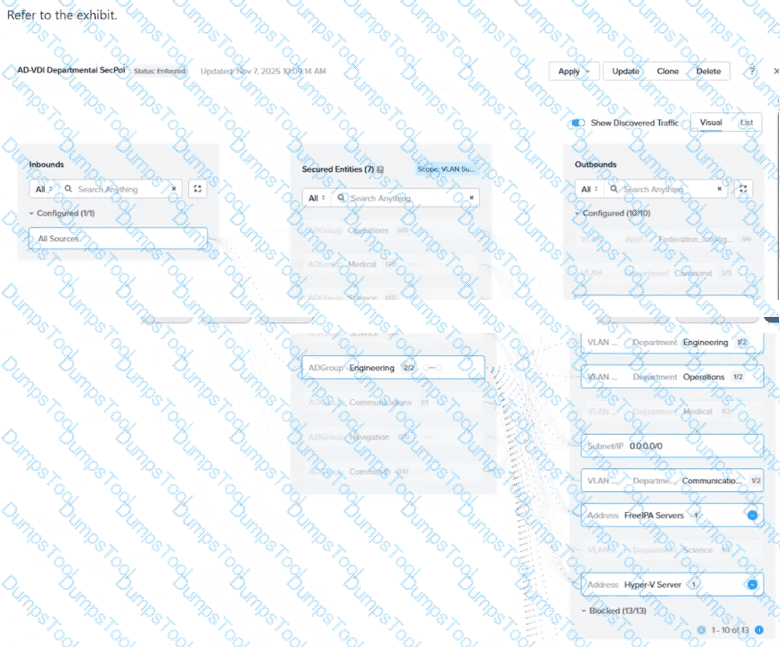
In the AD-VDI Departmental SecPol policy shown in the exhibit, ADGroup: Engineering is configured as a secured entity in a VDI Security Policy. Prism Central shows 2 / 2 active sessions under this group, but the administrator confirms that three Engineering users are currently logged in to persistent VDI desktops. The third user's VM shows no ADGroup assignment in its VM details in Prism Central, even after the user has successfully logged in. All three users are members of the same AD group, and the Domain Controller event logs confirm a successful interactive login for the third user. Which condition explains why the third user's VM is not being assigned the ADGroup: Engineering category?
An administrator is responsible for managing user access to a Nutanix cluster... configure custom user roles... What is the first step in configuring and managing user roles for a Nutanix cluster?