A Kubernetes administrator has been tasked with deploying a new cluster to AWS. The administrator has received the following requirements for this deployment:
Region us-east-1
AMI rhel8.6What is a requirement for deploying a new cluster in AWS?
When deploying an NKP cluster onto air-gapped, pre-provisioned servers, Konvoy Image Builder is utilized to prepare the servers to become NKP cluster nodes.
What does the konvoy-image upload command do as a part of this preparation process?
A Platform Engineer needs to create an NKP cluster on vSphere infrastructure, using the vSphere provisioning method. The cluster needs to have 3 worker node pools:
First node pool should consist of 6 worker nodes
Second node pool should consist of 3 worker nodes
Third node pool should consist of 3 worker nodesAdditionally, the worker nodes in the first node pool should be set to 10 CPUs, the second node pool workers should be set to 8 CPUs, and the third node pool workers should be set to 6 CPUs. What is the proper way to create the NKP cluster using the NKP CLI?
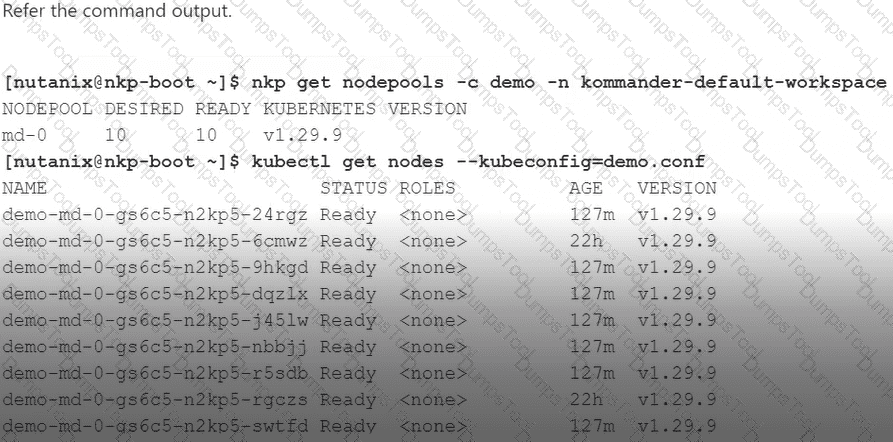
The Platform Engineer needs to expand an NKP Pro demo cluster due to workload capacity constraints. The demo cluster has 150 vCPUs available to it from a licensing standpoint. Each worker node has 8 vCPUs and each control plane node has 4 vCPUs.
Which two options are valid for expanding the demo cluster and remaining compliant with licensing? (Choose two.)
A Platform Engineer is preparing machine images for NKP through the NIB or KIB process. What is the purpose of doing this?
There is a private registry for the NKP deployment and the company has an NKP Ultimate license. A Platform Engineer is using the Podman tool and is already logged in. Now, the engineer needs to send the private registry with the NKP Catalog Applications.
What command should the engineer use?
A Cloud Engineer is deploying an NKP management cluster and plans to deploy multiple NKP workload clusters from it. The management cluster will be on Nutanix infrastructure, but the NKP workload clusters may be deployed in multiple provisioning environments, such as:
Nutanix
AWS
AzureWhen the engineer deploys an NKP workload cluster in AWS, which two default behaviors will be performed by NKP on this newly-deployed cluster? (Choose two.)
A Platform Engineer has deployed NKP and wants to utilize its OOB data storage feature.
What should the engineer enable to support backups within the NKP environment?
A Cloud Engineer is deploying an NKP cluster into an AWS environment. By default, when deploying NKP on AWS infrastructure, it generates the supporting infrastructure necessary for the cluster (VPC, subnets, ELBs). However, the AWS team has insisted that the NKP cluster be deployed on existing AWS infrastructure. How can the engineer meet this requirement?
A company has a new DevOps team that needs to be provided cloud native computing resources. This team will need to have access to multiple NKP clusters for development, testing and validation of an in-house application. However, they also need to be restricted to a specific namespace and a consistent level of access across the clusters within this namespace so that they do not adversely impact the environment of other user groups or the clusters themselves.
As a part of this consideration, the new team also needs to be limited to the amount of storage, CPU and memory they can consume on the clusters. A Platform Engineer has been tasked with providing the appropriate level of access to the team on these multiple NKP clusters.
How should the engineer best accomplish this task?
A Platform Engineer is deploying an NKP cluster within an air-gapped AWS environment. However, after an infrastructure planning session with the network team, it’s been determined that the default CIDR block range that is used by pods on NKP clusters is already in use in their environment.
How can the engineer ensure there are no collisions between NKP pod traffic and the existing network using that subnet range?
A Platform Engineer manages an NKP environment and is preparing a machine image to become an NKP cluster node. Which statement is correct regarding the default node preparation process?
A Platform Engineer has been tasked with backing up and restoring a production environment to ensure persistent data is available during a disaster at a primary site. What is recommended for backup and restore production use cases?
An administrator has been trying to deploy an initial AHV-based NKP cluster in a dark site (no Internet connectivity) environment using the command shown in the question.
nkp create cluster nutanix \
--cluster-name=$CLUSTER_NAME \
--control-plane-prism-element-cluster=$PE_NAME \
--worker-prism-element-cluster=$PE_NAME \
--control-plane-subnets=$SUBNET_ASSOCIATED_WITH_PE \
--worker-subnets=$SUBNET_ASSOCIATED_WITH_PE \
--control-plane-endpoint-ip=$AVAILABLE_IP_FROM_SAME_SUBNET \
--csi-storage-container=$NAME_OF_YOUR_STORAGE_CONTAINER \
--endpoint=$PC_ENDPOINT_URL \
--control-plane-vm-image=$NAME_OF_OS_IMAGE_CREATED_BY_NKP_CLI \
--worker-vm-image=$NAME_OF_OS_IMAGE_CREATED_BY_NKP_CLI \
--registry-url=${REGISTRY_URL} \
--registry-mirror-username=${REGISTRY_USERNAME} \
--registry-mirror-password=${REGISTRY_PASSWORD} \
--kubernetes-service-load-balancer-ip-range $START_IP-$END_IP \
--self-managed
Which missing attribute needs to be added in order for the deployment?
A dev team needed to optimize their logging system to be more robust, because the CPU and memory limits were insufficient, which caused delays in log collection and processing during times of high demand.
After a deep performance analysis, they decided to increase the CPU limits from 1 to 4 and the memory from 1000Mi to 4Gi.
Which ConfigMap should the development team run with custom resource requests and limit values for fluentd?
A Platform Engineer works for a service provider and needs to establish access and authentication for multiple clients into an NKP cluster. Each client has their own LDAP source that should be used for authentication into the cluster.
How would this be accomplished?
A Platform Engineer is getting started with NKP and has created a bastion host with all needed prerequisites.
How should the engineer install Kommander?
A Platform Engineer is deploying NKP into a highly secure vSphere environment. The NKP cluster will be air-gapped, and must also be FIPS compliant. The OS platform to be used for NKP cluster nodes is RHEL.
What must the engineer do to properly prep an OS image and have it be deployed as a FIPS compliant NKP cluster node?
NKP cluster nodes require a disk for some of its deployed components, outside of an application’s persistent volume requirements. What are these components and where are they deployed?
At a national defense company, protecting sensitive data is their top priority. With the increase in cyber-attacks, they have decided to implement an air-gapped Kubernetes environment to manage their critical applications, ensuring that no information could leak to the outside. The Kubernetes environment has three clusters deployed for their applications with centralized management. What type of licensing is required to enable this environment?
A Cloud Engineer would like to configure an NKP cluster that is running in the cloud to dynamically expand and compact its resource capacity for running container workloads. This will help ensure efficient use of resources without impacting online retail transaction performance that is increasingly hitting unpredictable spikes and lulls.
Which autoscaling method does NKP use and how does it scale?
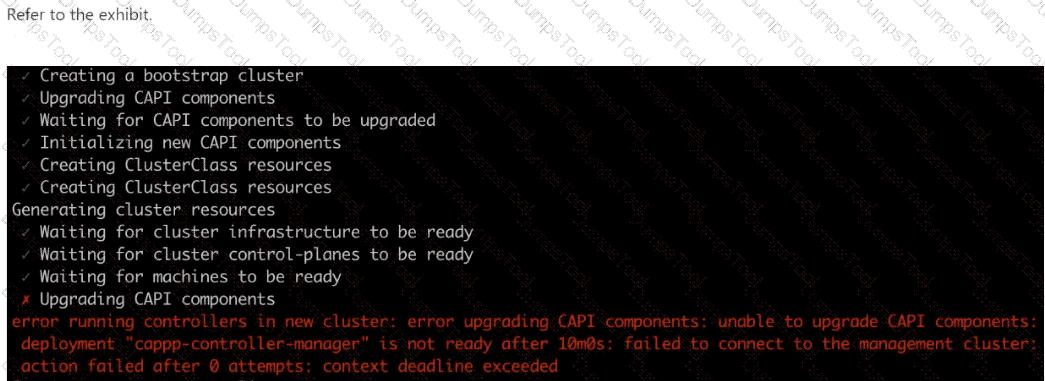
An administrator is provisioning an NKP cluster. After the VM creation task, the error shown in the exhibit is produced.
What could be the reason?
A Platform Engineer is attaching existing Kubernetes clusters to NKP, but a particular Kubernetes Amazon EKS cluster is getting errors with application deployments. These errors are related to persistent volumes. What could be the issue, and what can the engineer do?
A Platform Engineer is preparing an AWS instance using KIB for becoming an NKP cluster node. During the process, the source AMI is successfully cloned, and multiple preparation steps have occurred against the cloned AMI, such as gathering OS-release facts and uploading image bundles to it. However, the process encounters an error and ultimately fails. What is one troubleshooting step the engineer can perform that may help identify the root cause of the issue?
A company has enabled auto-scaling within an NKP cluster. What is the behavior for auto-scaling?
A company has standardized on NKP for their Kubernetes platform and needs to deploy their first cluster with the following requirements:
Dark site ready
Custom Service CIDR Block
Custom Pod CIDR Block
Hosted on Nutanix AHV ClusterWhich tool would the administrator use to perform the deployment?