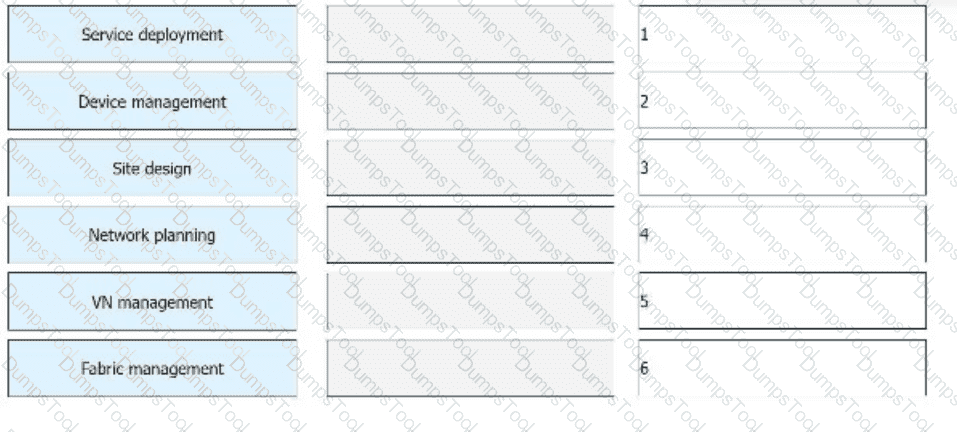
To deploy a virtual campus network using iMaster NCE-Campus, the following steps are performed. From top to bottom, sort the steps in the order in which they occur during network deployment and management.
The channelized sub-interface and FlexE technologies both can be used to implement network slicing, but the application scenarios of the two technologies are slightly different. Which of the following statements about the two technologies are correct?
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects and manage network devices.
Which of the following HTTP methods is used to configure the value of a network device’s managed object?
The Ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is _____ IRB forwarding. (Capitalize the first letter.)
Refer to the figure.
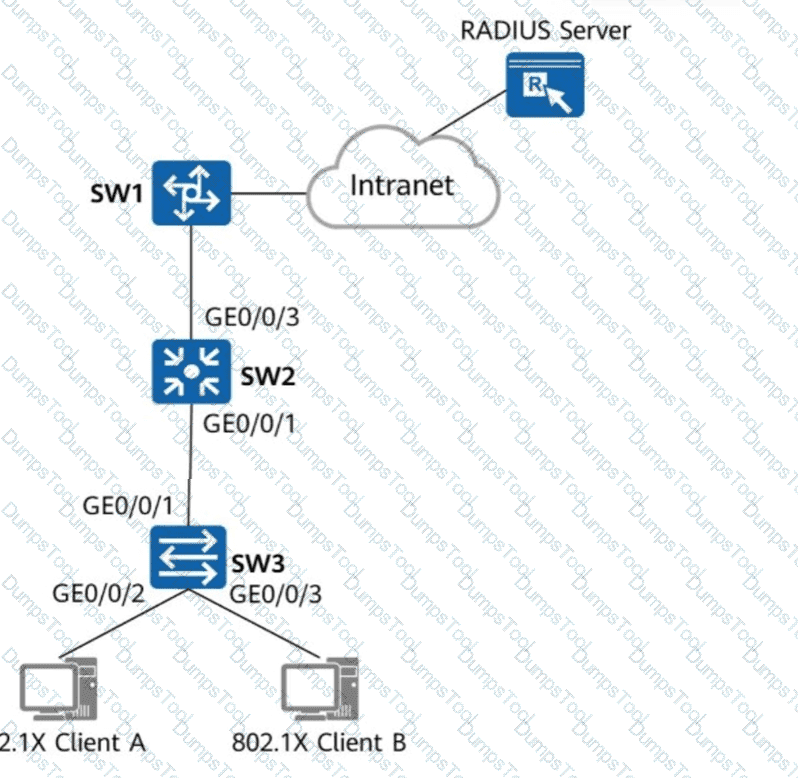
Which of the following steps are mandatory to enable 802.1X authentication on GE0/0/2 and GE0/0/3 of SW3 and configure a RADIUS server to authenticate and deliver network access rights to users?
During the configuration of L3VPNv4 over SRv6 BE, if an RR is deployed in the SR domain, which command must be run on the RR to ensure that the PEs at both ends can correctly learn VPNv4 routes?
Which of the following parameters is not included in an IPsec security association (SA)?
A VGMP packet is encapsulated with a UDP header and a VGMP header. By default, a VGMP packet uses UDP port _____.
During the migration test, which of the following indicates that the test is completed?
A network administrator needs to retrieve a token ID from iMaster NCE using the following Python code:
import requests
nbi_name = " demol3@north.com "
nbi_pwd = " qqcOVcVel@ "
host = " 139.9.213.72 "
port = " 18002 "
URI = " /controller/v2/tokens "
post_token_url = " https:// " + host + " : " + port + URI
headers_post = { ' Content-Type ' : ' application/json ' , ' Accept ' : ' application/json ' }
r = requests.post(post_token_url, headers=headers_post, json={ " userName " : nbi_name, " password " : nbi_pwd}, verify=incorrect)
Which of the following statements is incorrect?
In the firewall hot standby scenario, when VGMP works in load balancing mode, which of the following functions must be enabled on the firewalls to prevent the return traffic from being discarded because it does not match any session entry in the case of inconsistent forward and return paths?
Which of the following is the type of northbound API used by iMaster NCE-WAN?
If the number of MAC addresses learned on an interface enabled with port security reaches the upper limit, which of the following actions may the switch take?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following statements about the functions of BGP EVPN Type 3 routes is incorrect?
When a client invokes the iMaster NCE-Campus RESTful API, it sends an HTTP request. The server then returns the status code 401.
Which of the following errors has occurred?
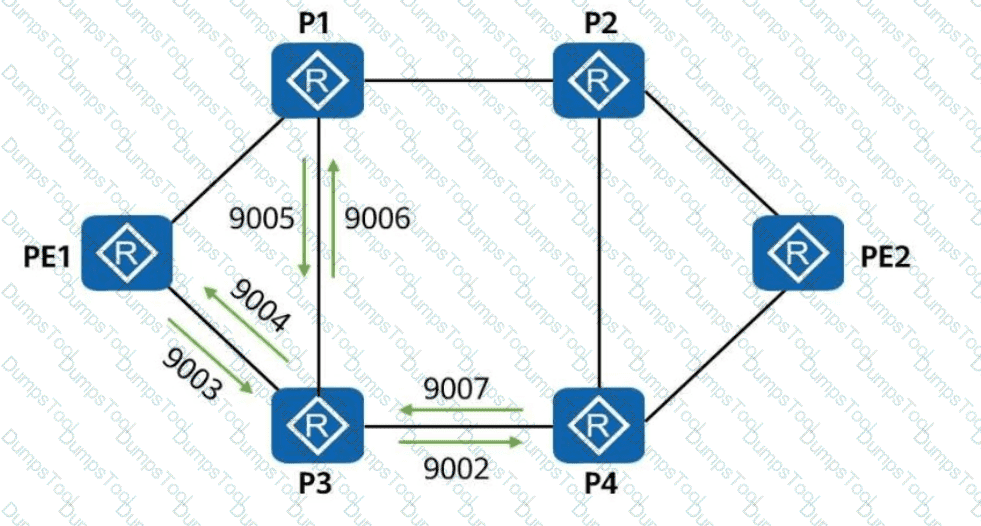
On the network shown in the figure, OSPF-based SR-MPLS TE is enabled on all routers. Which of the following adjacency labels are allocated by P3?
Port isolation can be deployed on an Ethernet network to implement both Layer 2 communication and Layer 3 isolation, making the networking more flexible.
On a VXLAN-based virtualized campus network, BGP EVPN can be used as the control plane protocol. Which of the following EVPN route types are not used in the virtualized campus network scenario?
An LSR supports various label retention modes. Which of the following statements regarding the liberal mode are correct?
In Huawei Open Programmability System (OPS), /ifm/interfaces/interface is the URL used to identify a device ' s managed object.
MPLS is located between the data link layer and network layer in the TCP/IP protocol stack and can provide services for all network layer protocols.
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, run the command on the VTEP to view BGP EVPN routes. The route entries shown in the following figure are displayed. Which of the following statements about these routing entries are correct?
Network (EthTagId/IP Prefix/IP PrefixLen)
NextHop
* > i 0:172.16.2.0:24 1.1.1.2
* > i 0:172.16.13.0:24 1.1.1.2
* > i 0:192.168.122.0:30 1.1.1.2
Which of the following statements is incorrect about intranet security design for a large or medium-sized virtualized campus network?
Huawei Open Programmability System (OPS) provides openness and programmability capabilities for network devices and enables users to perform secondary development. To facilitate script completion, Huawei OPS provides the Python script template in which the OPSConnection class is created. The member function for creating device resources is def post(self, uri, req_data).
Which of the following statements about 802.1X authentication are correct?
iMaster NCE-WAN is the core component of the Huawei SD-WAN Solution and is responsible for SD-WAN network management and service orchestration.
In Huawei SD-WAN Solution, which of the following tunneling technologies is used to establish data channels?
Which of the following can be used to transmit traffic to a VXLAN network and implement intra-subnet communication on the same VXLAN network?
New IS-IS TLVs are used to carry IPv6 addresses and reachability information to support IPv6 route processing and calculation.
Which of the following statements does not cause the flapping of a VRRP group?
There are multiple SR-MPLS TE tunnel protection mechanisms. FRR (Fast Reroute) constructs a virtual node to convert multiple identical route advertisement nodes into a single route advertisement node, and then computes the backup next hop of the virtual node based on the TI-LFA algorithm. In this way, traffic can be quickly switched when a fault occurs.
What is the name of this protection mechanism?
Which of the following commands are mandatory for configuring an OSPF-based SR-MPLS TE tunnel? (Select All that Apply)
BGP Link State (BGP-LS) introduces a new NLRI into BGP. The NLRI carries link, node, topology prefix, and other information, and is also referred to as the link state NLRI.
What can be determined from the following figure?
< R1 > display ipv6 routing-table protocol isis
Public Routing Table : ISIS
Summary Count: 6
ISIS Routing Table ' s Status : < Active >
Summary Count: 6
Destination : 3000:FDEA::4
NextHop : FE80::2E0:FCFF:FE98:2577
Cost : 20
Interface : GigabitEthernet0/0/1
PrefixLength : 128
Preference : 15
Protocol : ISIS-L2
Flags : D
Which of the following are application optimization functions in the Huawei SD-WAN Solution?
When you configure a virtualized campus network on iMaster NCE-Campus, Fit APs can immediately go online after you add them to iMaster NCE-Campus.
In the firewall hot standby scenario, which of the following status information can be backed up between the active and standby firewalls?
NETCONF provides a set of mechanisms for managing network devices. What layers can NETCONF be conceptually partitioned into?
A network administrator runs the display telemetry destination command on a device to check information about a destination group that sampled data is sent to. The command output is as follows. Which of the following statements is incorrect?
[~CE-telemetry-sensor-group-Sensor1]display telemetry destination
Dest-name Dest-addr Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20000 RESOLVED - GRPC
An SRv6 Policy can be either statically configured on a device, or be delivered to a device after being dynamically generated by the controller.
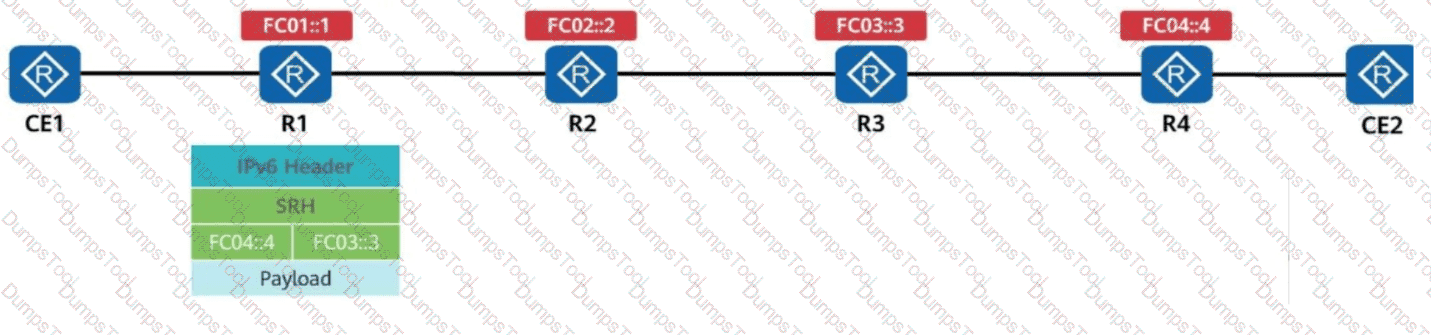
R1 receives a common IPv6 packet from the CE and generates a packet carrying the SRH (Segment Routing Header), as shown in the figure. The packet is forwarded along the path R1 → R2 → R3 → R4. Identify the node type of each device based on their role in SRv6 processing.
Which of the following commands needs to be run in the BGP view to enable a VPN instance to advertise IP routes to the BGP-EVPN address family?
Which of the following technologies can be used to isolate users in the same VLAN?
/ifm/interfaces/interface in Huawei Open Programmability System (OPS) is the URL used to identify a device ' s managed object.
Which MPLS label will be used by PE2 for forwarding traffic to 10.0.1.1 based on the following SR-MPLS database?
Given Data (LSDB Information):
Prefix-SID: 100
SRGB Base: 40000
In the small and midsize campus network design based on the Huawei CloudCampus Solution, when over 100 branches need to communicate with each other, which of the following interconnection networking models is recommended?
Which of the following inter-AS MPLS L3VPN solutions does not require MPLS to run between ASBRs?
Which of the following statements about prefix segments and adjacency segments are correct?
SR-MPLS is enabled on all routers. The label information encapsulated by R1 into a data packet is shown in the figure.
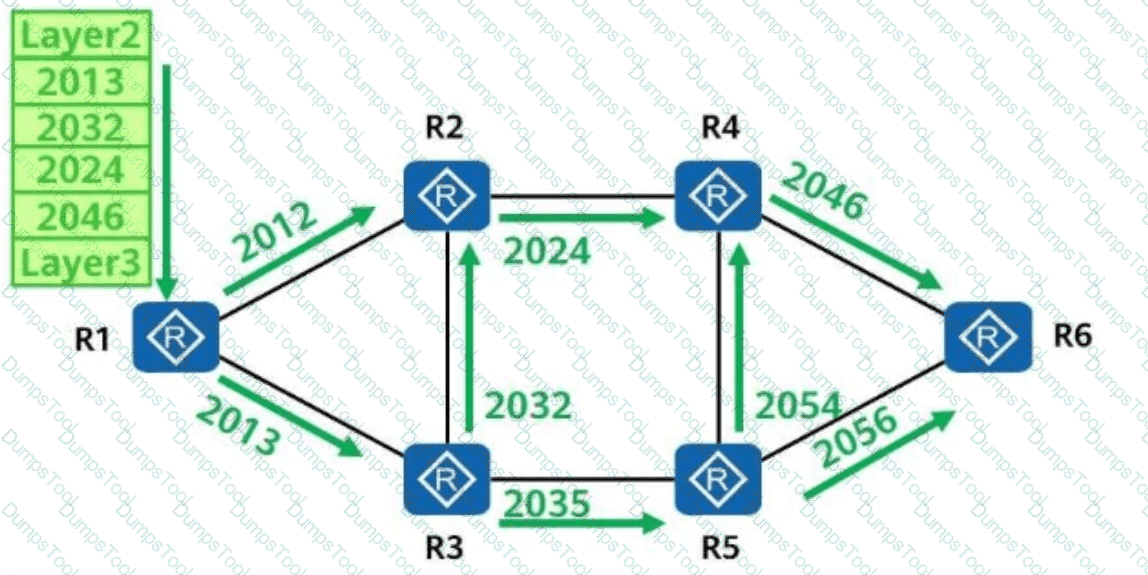
Which of the following is the forwarding path of the data packet?
The free mobility function is deployed on the iMaster NCE-Campus on a campus network. Which of the following information should an administrator pay attention to?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following BGP EVPN routes is used to advertise MAC addresses, ARP entries, and IRB routes?
BGP EVPN can be used as the VXLAN control plane protocol to completely prevent traffic flooding, such as broadcast ARP packets, on the VXLAN network.
Which of the following roles is NOT a core role in Huawei ' s Free Mobility solution?
An engineer often remotely logs in to the device to check the device status. The engineer can use the Python Paramiko and telnetlib libraries to implement automatic remote login through Python scripts. The remote login implemented using telnetlib is more secure.
On a router, SRv6 is enabled, and the configurations shown below are performed. Which of the following statements about the configurations are correct?
[Router-segment-routing-ipv6] locator srv6_locator1 ipv6-prefix 2001:DB8:ABCD::/64 static 32
A network administrator runs the display telemetry subscription command on a device to check telemetry subscription information. The command output is as follows. Which of the following statements is incorrect?
[~CE] display telemetry subscription
Sub name : Sub1
Sensor group:
Sensor-name Sample-interval(ms) State
Sensor1 1000 RESOLVED
Destination group:
Dest-name Dest-IP Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20030 RESOLVED - GRPC
Sub state : PASSIVE
Total subscription number is : 1
Refer to the following command output on the router R3. Which of the following statements are correct?
< R3 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:26 UTC-08:00
Description: HUAWEI, AR Series, Tunnel0/0/0 Interface
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.2/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.3.3 (LoopBack0), destination 10.0.1.1
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
As shown in the following figure, OSPF is deployed on a campus network to implement network interconnection, and Area 1 is deployed as an NSSA. To enable R1 to access R4’s loopback interface address, an engineer imports a direct route to R4’s OSPF process. Which of the following statements about this scenario are correct?
[R4-ospf-1] import-route direct
Loopback0: 10.1.4.4/32
In OSPFv3, which of the following types of LSAs can be flooded in the entire AS?
The TTL field encapsulated in the MPLS label header can prevent infinite loops of MPLS packets. Which of the following statements regarding the TTL field are correct?
An SR-MPLS Policy needs to divert service traffic to a tunnel for forwarding. If traffic from various services is destined for the same address, which of the following traffic diversion modes is recommended to ensure the quality of each service?
Among NETCONF operations, the < config > operation may contain an operation attribute, which is used to specify an operation type for configuration data. Which of the following operation attributes is incorrect?
iMaster NCE-Campus provides the terminal identification function to display the terminal type, operating system, and manufacturer information.
Which of the following items are included in static information collection and analysis?
The RR (Route Reflector) is critical to the Huawei SD-WAN Solution, and its deployment mode varies based on the scenario. In which of the following modes can an RR be deployed?
What can be determined from the following IS-IS peer output?
Peer information for ISIS(1):
Peer System ID: ee8c.a0c2.baf3
Interface: GE0/0/0
State: Up
HoldTime: 7s
Type: L1
PRI: 64
MT IDs supported: 0(UP), 2(UP)
Local MT IDs: 0, 2
Area Address(es): 49.0022
Peer IP Address(es): 10.1.34.1
Peer IPv6 Address(es): FE80::2E0:FCFF:FE98:2576
Which of the following statements about static VXLAN tunnel configuration are correct?
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. To facilitate script compilation, Huawei OPS provides the Python script template. In the Python script template, what are the contents of the Content-type and Accept fields in the header of an HTTP request packet?
To enhance reliability, you can deploy Huawei iMaster NCE-WAN controllers in active/standby mode. Which of the following IP addresses must be configured to be the same for the active and standby controllers so that the controllers can be accessed properly? (Select All that Apply)
In the Huawei CloudCampus Solution, which of the following deployment modes are supported by Huawei switches?
In the firewall hot standby scenario, in which of the following conditions will the local device proactively send VGMP packets?
Which of the following technologies can be used to measure performance based on actual service traffic in Huawei ' s CloudWAN solution?
Free mobility implements policy management and permission control based on users ' VLAN IDs and IP addresses.
This figure shows an SRv6 (Segment Routing over IPv6) packet. If the Destination Address field in the IPv6 basic header is FC04::4, the value of the SL (Segment Left) field in the SRv6 header should be ____. (Enter only digits.)
Which of the following methods can be used to establish IPsec SAs? (Select All that Apply)
In addition to indicating priority, the DSCP value can also indicate the drop probability. Which of the following DSCP values is set with the highest drop probability?
Which of the following statements about SR-MPLS Policy path planning are correct?
When an NVE encapsulates a data frame into a VXLAN packet, information of which of the following protocols is encapsulated between the outer IP header and the VXLAN header?
During WLAN planning and design, channels 1, 6, and 11 are recommended on the 2.4 GHz frequency band, and channels 1, 5, 9, and 13 are recommended in high-density scenarios. On the 5 GHz frequency band, it is recommended that high-frequency and low-frequency channels of adjacent APs be staggered to prevent overlapping.
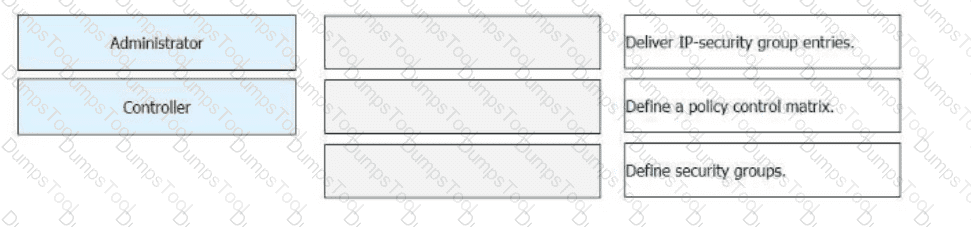
Free mobility is deployed on a campus network through iMaster NCE-Campus. During this deployment, which of the following steps are performed by administrators and which are automatically performed by iMaster NCE-Campus? Drag the administrators and iMaster NCE-Campus icons on the left to the corresponding steps on the right.