(Which of the following is not an advantage of Huawei CloudCampus solution?)
(The egress zone is the boundary between a campus network and external networks, including the Internet and WAN. It bridges the intranet and extranet and protects the security of the campus network. Which of the following are requirements for egress zone design?)
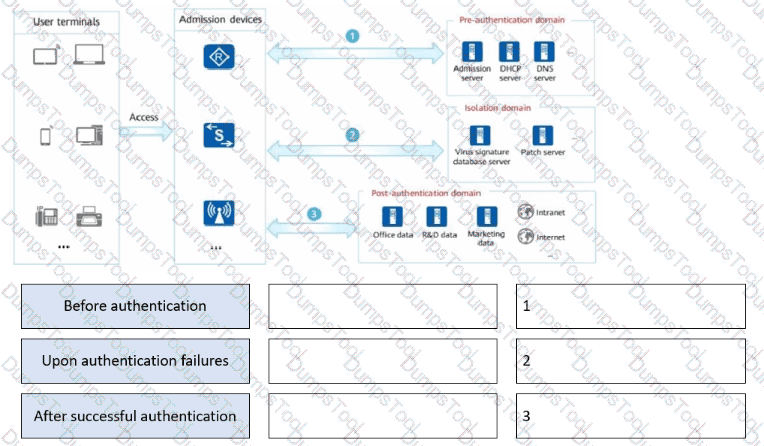
Drag the user authentication results to the corresponding network access rights.
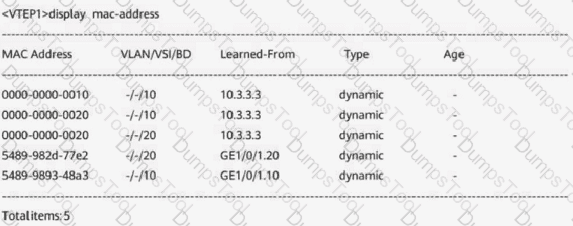
(The following figure shows the MAC address table of a Layer 2 VXLAN gateway. Which of the following statements are true?Choose all that apply.)
(MAC address learning of a static VXLAN tunnel depends on exchange of packets, such as ARP packets, between hosts.)
(On a campus network, which of the following address allocation modes is recommended to facilitate management of devices such as servers, print servers, and video surveillance devices?)
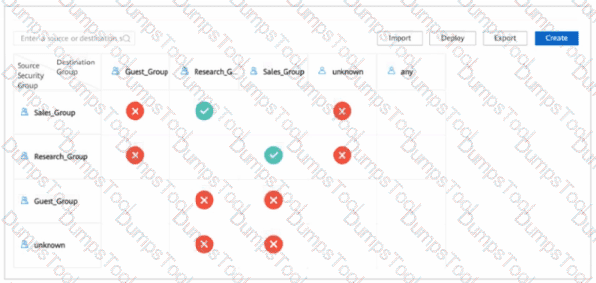
(The following figure shows a policy control matrix on a virtualized network deployed using iMaster NCE-Campus. Which of the following statements about the policy control matrix are true?Choose all that apply.)
(On a CloudCampus virtualized campus network, service data enters different VNs from physical networks through edge nodes and the VN that the data will enter is determined by the VLANs to which users belong. Which of the following statements about dynamic VLAN authorization isfalse?)
(If the number of MAC addresses learned on an interface enabled with port security reaches the upper limit, which of the following actions may the switch take?)
(During WLAN planning and design, channels 1, 6, and 11 are recommended on the 2.4 GHz frequency band, and channels 1, 5, 9, and 13 are recommended in high-density scenarios. On the 5 GHz frequency band, it is recommended that high-frequency and low-frequency channels of adjacent APs be staggered to prevent overlapping.)
(When a network device sends a registration request to iMaster NCE-Campus, which of the following is the destination port number?)
(On a campus network, iMaster NCE-Campus is used to deploy two VNs: R&D VN and marketing VN, users in these two VNs belong to two security groups, respectively. The campus network requires R&D personnel and sales personnel to communicate with each other. To meet this requirement, which of the following tasks does a network administrator need to perform?)
(When you configure a virtualized campus network on iMaster NCE-Campus, creating a virtual network is equivalent to creating a VPN instance to isolate different services.)
(In the Huawei CloudCampus Solution, which of the following provisioning modes isnot supportedby firewalls?)
(iMaster NCE-Campus provides independent working interfaces on different planes: management plane and service plane. You can log in to each plane through a specific IP address and port number. The port number of the service plane is _____.)
(On a VXLAN-based virtualized campus network, terminals communicate with each other through VXLAN tunnels. When the campus network needs to communicate with external networks, the data must pass through border nodes.)
(When configuring access authentication, you need to define the items authorized to users in the authorization result. Which of the following items does not need to be defined?)
(On a virtualized network deployed using iMaster NCE-Campus, which of the following methods can be used by a network administrator during VN creation to create user network segments?)
(Which of the following is used to implement inter-subnet communication on a VXLAN network and allow access from a VXLAN network to an external non-VXLAN network?)
(Which of the following statements about authentication profile configuration is true?)
(When advertising routes, BGP EVPN uses EVPN Router's MAC Extended Community to carry the Router MAC field of a VTEP.)
(Refer to the following route queried using a command on the VTEP. Which of the following statements about the route are true?)
[VTEP] display bgp evpn all routing-table mac-route 0:48:b0d5-9dc7-3c41:32:172.16.1.173
BGP local router ID : 1.1.1.1
Local AS number : 100
Total routes of Route Distinguisher(1:3): 1
BGP routing table entry information of 0:48:b0d5-9dc7-3c41:32:172.16.1.173:
Imported route.
Label information (Received/Applied): 3 2/NULL
From: 0.0.0.0 (0.0.0.0)
Route Duration: 1d00h15m21s
Direct Out-interface:
Original nexthop: 1.1.1.1
Qos information : 0x0
Ext-Community: RT <0:2>, RT <0:3>, Tunnel Type
AS-path Nil, origin incomplete, pref-val 0, valid, local, best, select, pre 0
Route Type: 2 (MAC Advertisement Route)
Ethernet Tag ID: 0
MAC Address/Len: b0d5-9dc7-3c41/48, IP Address/Len: 172.16.1.173/32, ESI: 0000.0000.0000.0000.0000
Advertised to such peers:
1.1.1.2
(Refer to the following figure.
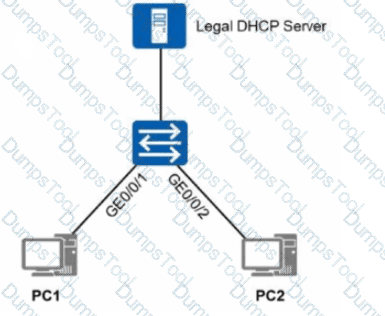
Which of the following solutions can be used to prevent users from accessing the network using statically configured IP addresses?)
(Which of the following statements about configuring user access authentication is false?)
(Which of the following encryption algorithms isnot supportedby IPsec VPN?)