Which of the following is not a common network layer in a midsize campus network?
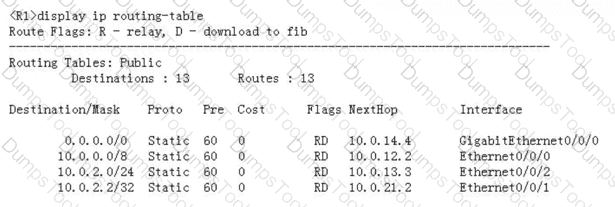
According to the command output shown in the figure, which of the following statements are true?
Which of the following authentication modes does/do not require a user name and a password?
(The IP addresses of VLANIF interfaces on the same switch must be different.)
Which of the following BIDs cannot be contained in a configuration BPDU sent by a switch?
On an STP-enabled switch, a port in the Learning state can transition to the Forwarding state only after the Forward Delay timer expires.
When a switch port receives a frame that does not carry a VLAN tag, it must add a PVID to the frame.
Which of the following states indicates that the OSPF neighbor relationship has been established?
In RSTP mode, both alternate and backup ports cannot forward user traffic and cannot receive, process, and send BPDU.
Which of the following are advantages of stacking and CSS (Cluster Switch System) technologies?
(The administrator performs the configuration shown in the figure on a router, and a host is connected to Gi/0/0 of the router. Which of the following statements is true about the IP address obtained by the host through DHCP?)
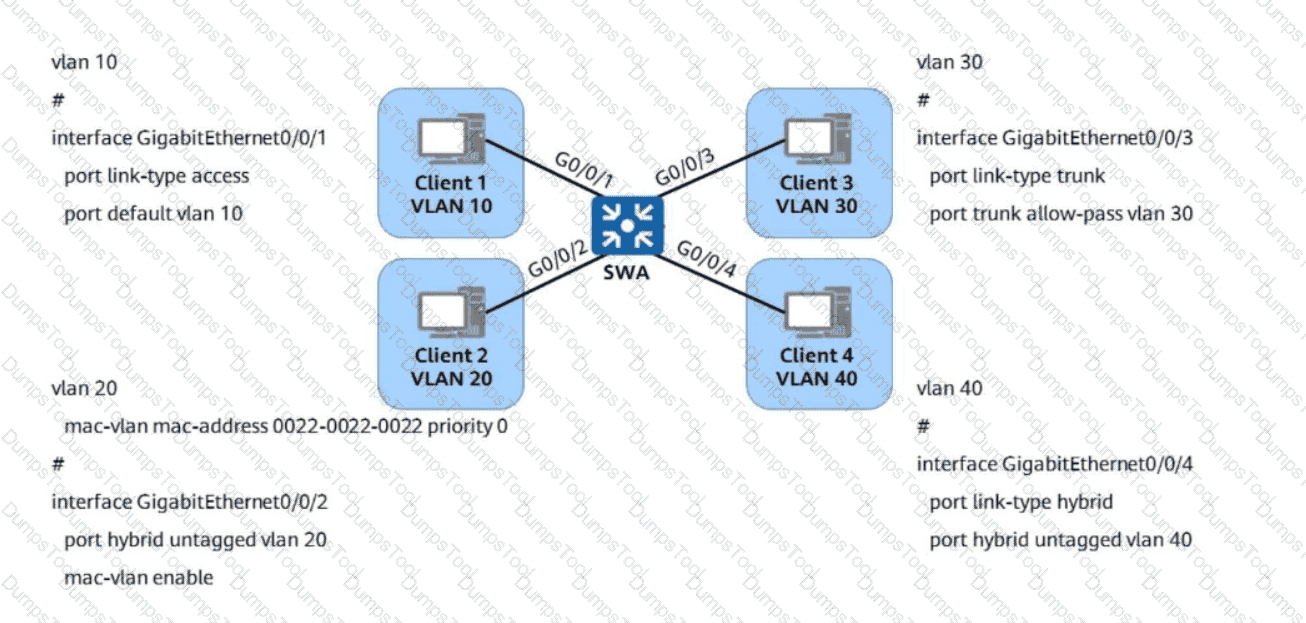
Refer to the following VLAN configurations on a Huawei switch. Which of the following statements are true?
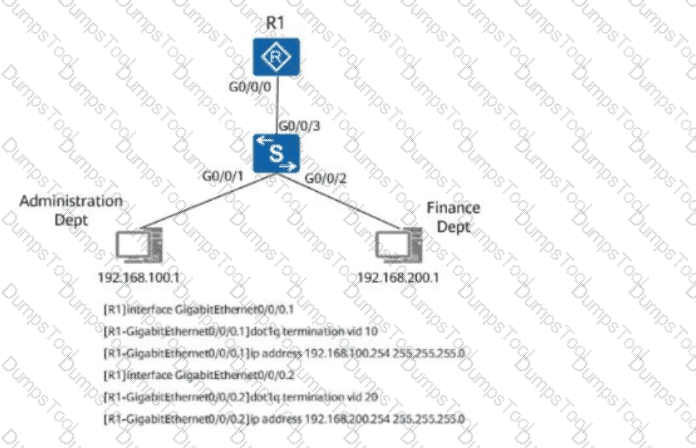
According to the one-armed routing configurations shown in the figure, even if ARP proxy is disabled on the sub-interface of R1, the Administration Dept and Finance Dept can still communicate with each other.
(You can run the " pwd " and " dir " commands on the Versatile Routing Platform (VRP) to view file information in the current directory.)
An administrator wishes to configure a floating static route. In order to successfully achieve this, which operation should be performed?
Which of the following statements regarding static routing and dynamic routing is incorrect?
Which of the following are true about the Ethernet data frame with the " Length/Type " field being 0x0806?
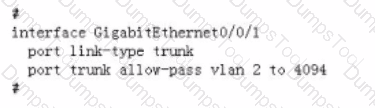
Refer to the following configuration of GigabitEthernet0/0/1 on the switch. For which VLAN does the switch forward untagged data frames?
interface GigabitEthernet0/0/1
port link-type trunk
port trunk pvid vlan 10
port trunk allow-pass vlan 10 20 30 40
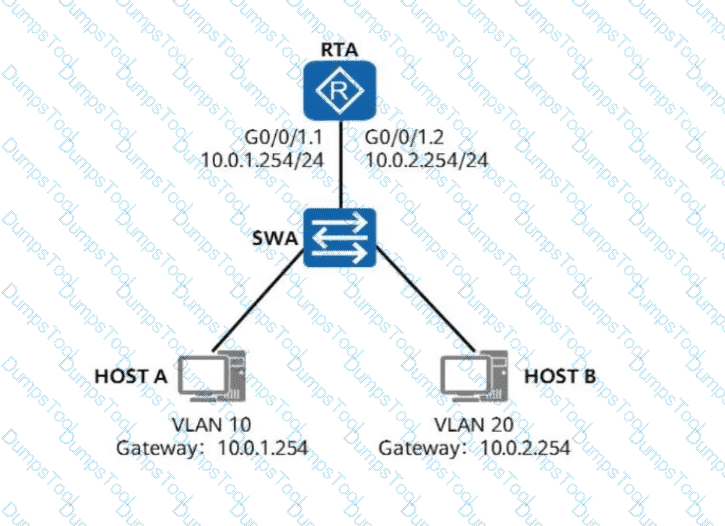
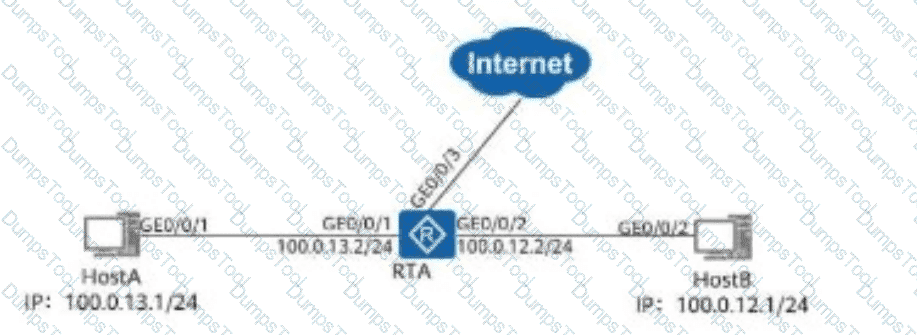
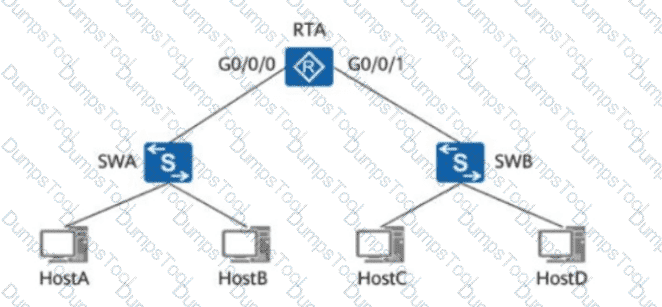
On the network shown in the figure, HOST A and HOST B are required to communicate with each other across VLANs through one-armed routing. To satisfy this requirement, which of the
following commands needs to be performed on G0/0/1.1 of RTA?
Which of the following authentication methods are supported for Telnet users?
A routing entry contains multiple fields. Which of the following statements about these fields is false?
A Layer 2 ACL can match information such as the source MAC address, destination MAC address, source IP address, and destination IP address.
For an STP-enabled switch, a port in any state can transition to the Disabled state.
Assuming that an administrator is running the command shown in the figure on an AR2200 router, which of the following statements about the configuration is true?
< Huawei > reset saved-configuration
Warning: The action will delete the saved configuration in the device.
The configuration will be erased to reconfigure. Continue? [Y/N]:
(ICMP packets do not contain port numbers. Therefore, NAPT cannot be used.)
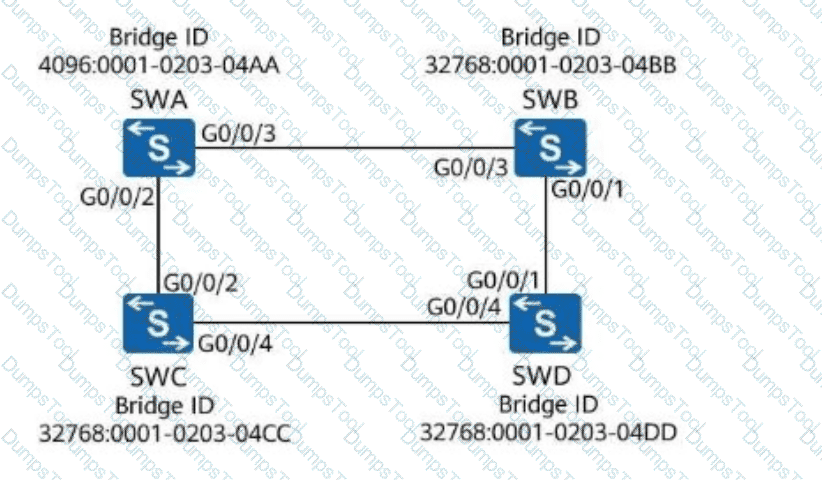
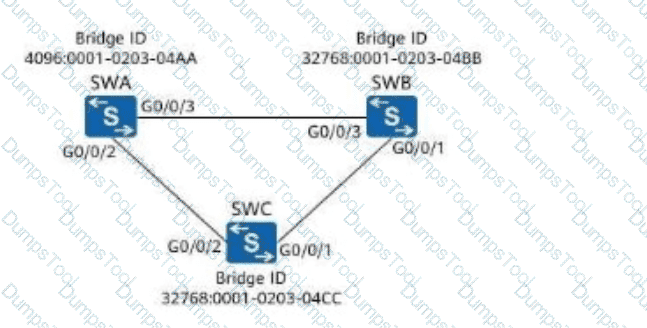
As shown in the figure, all switches run STP. Assume that the path cost of all ports is 200. What is the root path cost contained in the configuration BPDU received by G0/0/4 on SWD?
Which of the following statements about static routes on Huawei devices is false?
After a switch restarts, static MAC address entries saved on the switch remain in the MAC address table.
When the header length of an IPv4 data packet is 20B and the total packet length is 1500B, what is the valid payload of the packet?
If AAA authentication is used on Huawei devices and the remote server does not respond, the authentication can be performed on network devices.
Refer to the following configuration of an interface on a switch. What is the PVID of the interface?
interface GigabitEthernet0/0/1
port hybrid tagged vlan 2 to 3 100
port hybrid untagged vlan 4 6
The LACP priority is shown in the figure. Switch A and Switch B adopt link aggregation in LACP mode, all interfaces are added to the link aggregation group (LAG), and the maximum number of active ports is set to 3.
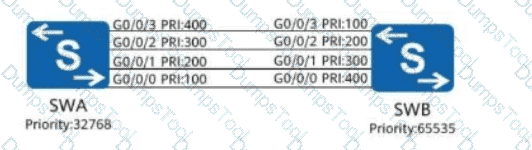
Which port of Switch A is NOT an active port?
Options:
Which of the following statements is true about an STP-enabled port in Forwarding state?
For multiple paths to the same destination network, the router needs to compare the preference values of the paths. If the preference values are the same, the router selects the paths based on the cost value.
(Which of the following methods can be used to assign service VLANs during campus network planning?)
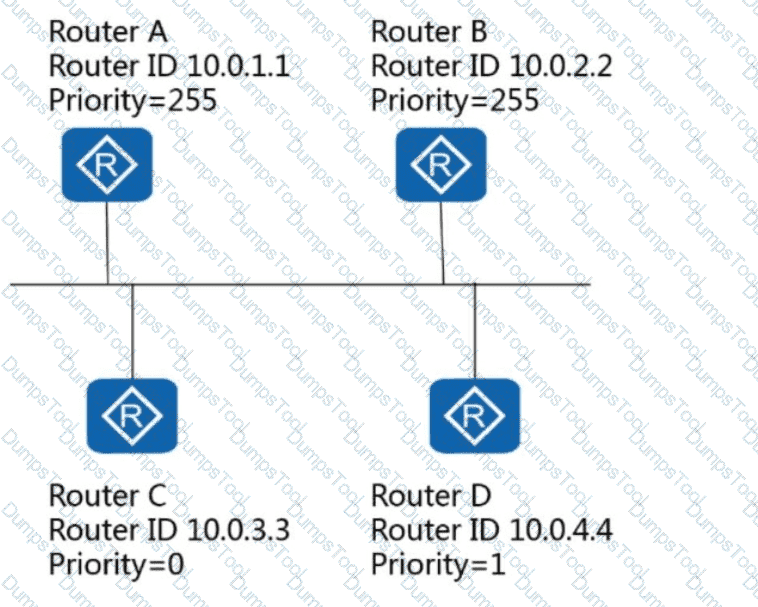
Assuming that OSPF has been enabled on all routers in the following figure, which router is the BDR on this network?
In a broadcast address, all host bits are set to 1, and a broadcast address can be used as a host address.
OSPF allows for " multiple " processes. By default, OSPF selects a process whose number is _____.
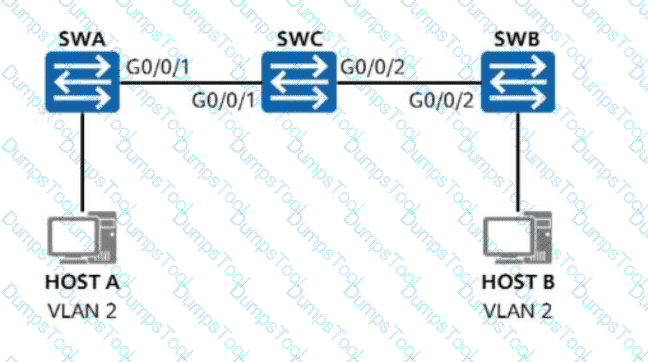
On the network shown in the figure, VLAN 2 is created on SWA and SWB, and interfaces connected to hosts are access ports added to VLAN 2. G0/0/1 on SWA and G0/0/2 on SWB are trunk interfaces allowing all VLANs. What additional configuration is needed on SWC to ensure communication between Host A and Host B?
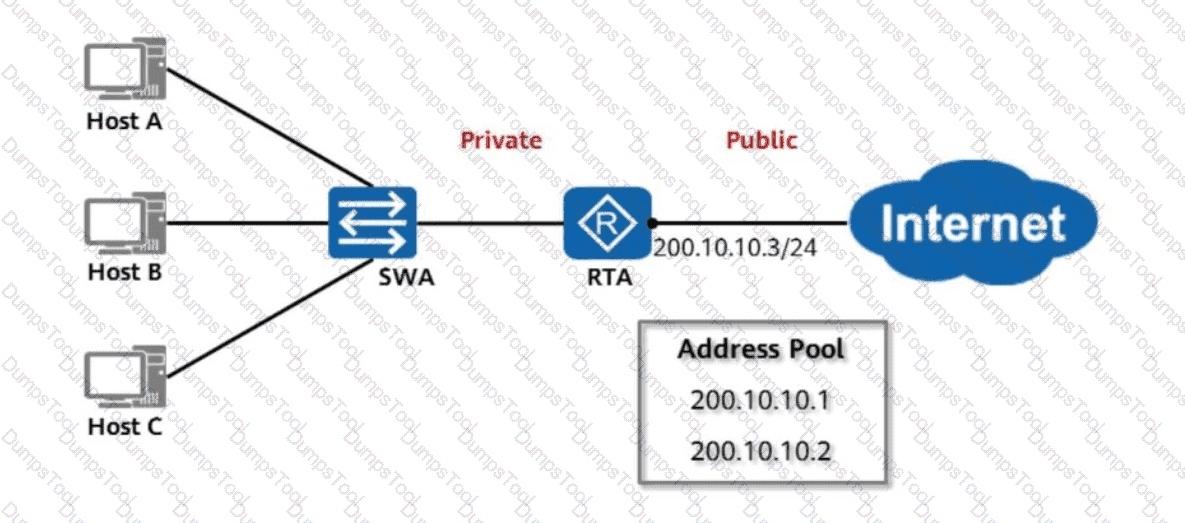
As shown in the figure, RTA uses NAT and has an address pool configured to implement many-to-many non-NAPT address translation, so that hosts on the private network can access the public network. Assume that the address pool has only two public IP addresses, which are translated for Host A and Host B. If Host C wants to access the public network, which of the following statements is true?
The users who log on the router through Telnet are not permitted to configure an IP address. What is the possible reason?
Which of the following information is used by a VLANIF interface to determine whether to perform Layer 2 forwarding or Layer 3 forwarding?
The network administrator performs the configuration shown in the following figure on RTA. If a user needs to be authenticated in the authentication domain named huawei, which of the following statements is true?
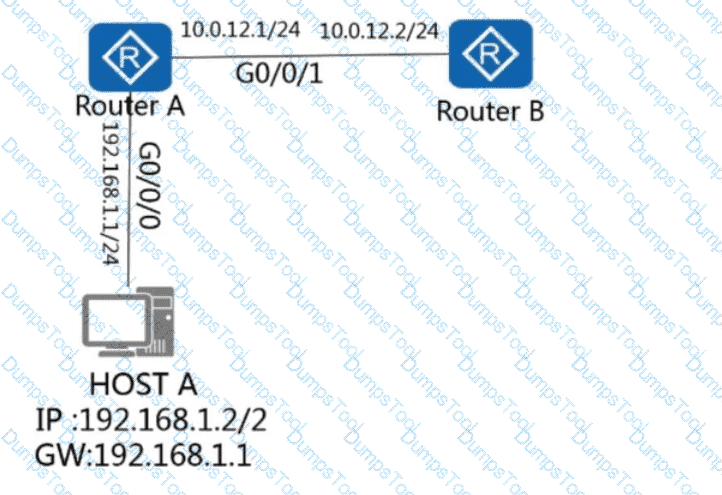
On the network shown in the figure, host A logs in to router A through Telnet and obtains the configuration file of router B through FTP on the remote CLI. How many TCP connections exist on router A?
An ACL rule is as follows. Which of the following IP addresses can be matched by the permit rule?
rule 5 permit ip source 10.0.2.0 0.0.254.255
Which of the following configurations can prevent Host A and Host B from communicating with each other?
Which of the following traffic can be filtered by an advanced ACL on a Huawei device?
The following figure shows the MAC address table of a switch.
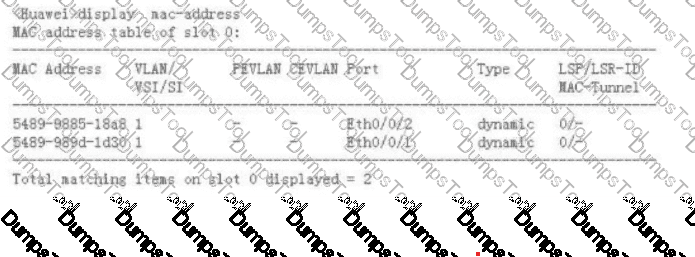
Assuming that the switch receives a data frame with the destination MAC address 5489-9885-18a8 from Eth0/0/2, which of the following statements is true?
Options:
When a host uses the stateless address autoconfiguration solution to obtain an IPv6 address, the host cannot obtain the DNS server address.
If PPP authentication fails, which type of packet will be sent to the authenticated peer by the authenticator?
Assume that an OSPF-enabled router has no loopback interface configured. What would be used as the router ID?
Which of the following is the default value of the Router Dead Interval field in OSPF Hello packets on a broadcast network?
NAPT differentiates IP addresses of different users based on protocol ID in TCP, UDP, or IP packets.
(Network Functions Virtualization (NFV) implements software-based network application deployment.)
On an STP-enabled switch, a port in the forwarding state can receive BPDU packets.
Refer to the following IP routing table on the router R1. If R1 sends a data packet with the destination IP address 10.0.2.2, which of the following interfaces will R1 use to send the packet?
The following figure shows the configuration of a sub-interface on a router. For which VLAN does the sub-interface receive tagged data frames?
(The IPv6 address architecture does not include which of the following address types?)
Refer to the following configuration of an interface on a switch. For which VLAN does the interface remove VLAN tags before forwarding data frames?
interface GigabitEthernet0/0/1
port link-type trunk
port trunk pvid vlan 10
port trunk allow-pass vlan 10 20 30 40
UDP does not guarantee data transmission reliability and does not provide packet sorting and traffic control functions. It is suitable for the traffic that has low requirements for data transmission reliability, but high requirements for the transmission speed and delay.
Which statement is true regarding the following command?
ip route-static 10.0.12.0 255.255.255.0 192.168.1.1
When a host uses the IP address 192.168.1.2 to access the Internet, NAT must be performed.
On a network running STP, the root switch is elected only by comparing switch priorities. On a network running RSTP, both the priorities and MAC addresses of switches will be compared for electing the root switch.
In RSTP, an edge port becomes a common STP port after receiving a configuration BPDU.
By referring to the information about an interface on R1 shown in the figure, which of the following statements is true?
[R1]display interface g0/0/0
GigabitEthernet0/0/0 current state : Administratively DOWN
Line protocol current state : DOWN
For STP, the Message Age in the configuration BPDUs sent by the root bridge is 0.
When a router is powered on, the router reads the configuration file saved in the default save directory to get itself initialized. If the configuration file does not exist in the default save directory, what does the router use to initialize itself?
On the network shown in the figure, G0/0/0 and G0/0/1 of RTA connect to two different network segments, and RTA is the gateway between the two networks. Given this, the MAC address from which of the following needs to be obtained using an ARP Request message before HostA sends data to HostC?
Which of the following commands can switch a view from the system view to the user view?
A network administrator wishes to assign an IP address to a router interface G0/0/0. Which of the following IP addresses can be assigned?
What is the protocol of the Router Advertisement (RA) packet, which is used in IPv6 stateless address auto-configuration?
When an AP and an AC are located on different Layer 3 networks, which of the following methods is recommended for the AP when discovering the AC?
After switches are virtualized into one logical switch using stacking or CSS, an inter-chassis Eth-Trunk can be deployed to improve network reliability.
VLAN 4095 is reserved for system use and VLAN 1 cannot be deleted on Huawei switches.
Refer to the following commands run on GigabitEthernet0/0/1 and GigabitEthernet0/0/2. Which of the following statements are true?
Refer to the following configuration of an interface on a switch. For which VLAN does the interface transmit tagged data frames?
interface GigabitEthernet0/0/1
port hybrid tagged vlan 2 to 3 100
port hybrid untagged vlan 4 6
(Which of the following statements is true about active interface election for an Eth-Trunk in LACP mode?)
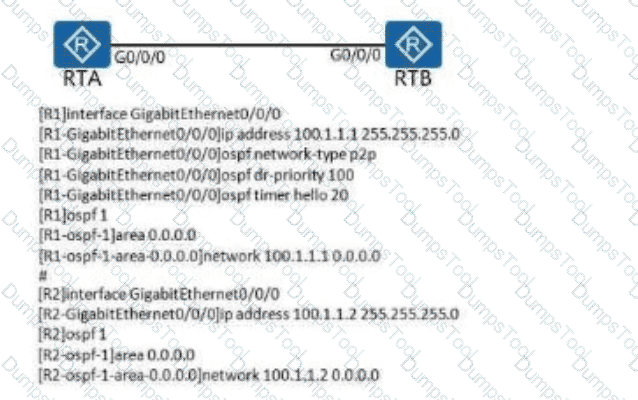
Refer to the graphic, which of the following statements is true about OSPF topology and configuration?
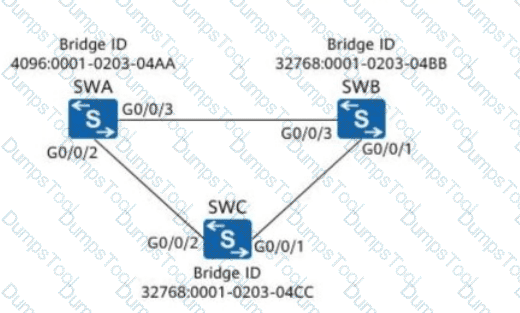
On the network shown in the following figure, assuming that SWA, SWB, and SWC retain factory defaults, which of the following ports will be selected as a designated port?
The Priority field in a VLAN tag can be used to identify the priority of a data frame. What is the value range of the field?
A switch needs to forward a frame with the destination MAC address 5489-98EC-F011. Refer to the display mac-address command output. Which of the following statements is true?
Which of the following are basic parameters for configuring a static route?
As shown in the figure, which of the following ports will be in a blocking state?
According to OSI reference model, which layer is responsible for end to end error checking and flow control?