In some scenarios, an anonymous account can be used for authentication. What are the correct descriptions of the following options for the anonymous account?? (Multiple choice)
Traditional network single--The strategy is difficult to cope with the current complex situations such as diversified users, diversified locations, diversified terminals, diversified applications, and insecure experience.
Regarding the enhanced mode in HTTP Flood source authentication, which of the following descriptions are correct? Multiple choices
The administrator has made the following configuration:
1. The signature set Protect_ all includes the signature ID3000, and the overall action of the signature set is to block.
2. The action of overwriting signature ID3000 is an alarm.
The results of the RBL black and white list query on the firewall are as follows:
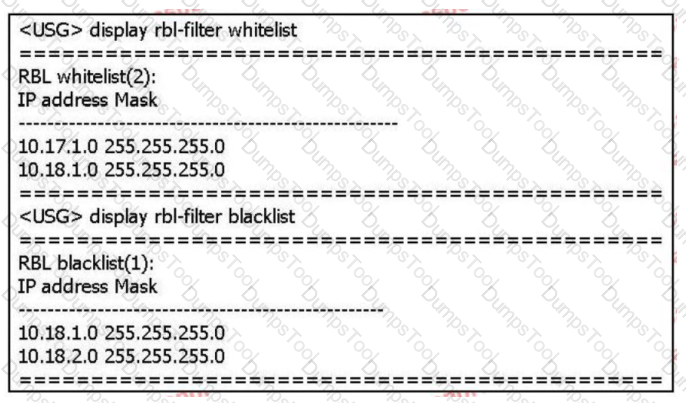
Based on the above information only, which of the following statements is correct? (multiple choice)
Information security is the protection of information and information systems to prevent unauthorized access, use, leakage, interruption, modification, damage, and to improve
For confidentiality, integrity and availability. ,
If you use a normal account for authentication, which of the following descriptions is wrong?
Which of the following options is wrong for the description of the cleaning center?
The anti-tampering technology of Huawei WAF products is based on the cache module. Suppose that when user A visits website B, website B has page tampering.
Signs: The workflow for the WAF tamper-proof module has the following steps:.
① WAF uses the pages in the cache to return to the client;
②WAF compares the watermark of the server page content with the page content in the cache
③Store the content of the page in the cache after learning
④ When the user accesses the Web page, the WAF obtains the page content of the server
⑤WAF starts the learning mode to learn the page content of the user's visit to the website;
For the ordering of these steps, which of the following options is correct?
In the WLAN wireless access scenario, which of the following network security technologies belong to user access security? (Multiple choice)
About the hardware SACG Certification deployment scenarios, which of the following descriptions are correct? (Multiple choice)
There are three roles in the XMPP protocol: server, gateway, and client. Corresponding to the free mobility solution: Agile Controller-Campus as For the server, Huawei USG6000 series firewall acts as the gateway; the agile switch acts as the client.
Regarding the trigger mechanism of 802.1X authentication, which of the following descriptions is correct? (multiple choice)
Regarding the description of keywords, which of the following is correct? (multiple choice)
The status code in the HTTP response message indicates the type of the response message, and there are many possible values. Which of the following status codes represents the client request
The resource does not exist?
Which of the following options is not a challenge brought by mobile office?
When you suspect that the company's network has been attacked by hackers, you have carried out a technical investigation. Which of the following options does not belong to the behavior that occurred in the early stage of the attack?
Which of the following options belong to the upgrade method of the anti-virus signature database of Huawei USG6000 products? (multiple choice)
Huawei NIP6000 products provide carrier-class high-reliability mechanisms from multiple levels to ensure the stable operation of equipment.
Which of the following options belong to the network reliability? (multiple choice)
Server Fault information collection tool Server Collector, which of the following does collected information items not include?
Which of the following options is not a scenario supported by Free Mobility?
In centralized networking, database,SM server,SC server\ AE Servers are centrally installed in the corporate headquarters. This networking method is suitable for companies with a wide geographical distribution of users and a large number of users.
In the terminal security management, the black and white list mode is used to check the terminal host software installation status. Which of the following situations is a compliant behavior?
The relationship between user groups and accounts in user management is stored in a tree on the Agile Controller-Campus. An account belongs to only one user group.
Consistent with the corporate organizational structure: If the OU (OnizbonUnit) structure stored in the AD/LDAP server is consistent with the corporate organizational structure, users are stored Under 0OU, when the Agile Controller-Campus synchronizes AD/LDAP server accounts, which synchronization method can be used?
Use hardware SACG Access control,,In hardware SACG View the results of the conversation table on the deduction.
Which of the following statements are correct? (Multiple choice)
In a centralized networking, the database, SM server, SC server, and AE server are all centrally installed in the corporate headquarters. This networking method is suitable. It is used for enterprises with a wide geographical distribution of users and a large number of users.
The administrator of a certain enterprise wants employees of Yangzhi to visit the shopping website during working hours. So a URL filtering configuration file is configured to divide the predefined
The shopping website in the category is selected as blocked. But employee A can still use the company's network to shop online during lunch break. Then what are the following possible reasons
some?
In the campus network, employees can use 802.1X, Portal,MAC Address or SACG Way to access. Use different access methods according to different needs to achieve the purpose of user access control.
When a guest needs to access the network through an account, which of the following methods can be used to access? (Multiple choice)
Agile Controller-Campus The department includes four parts of the management center(MC)Business manager(SM)And business controller(SC)And client network access equipment (NAD)As a component of the solution, it is linked with the service controller to realize user access control and free mobility.
Regarding the definition of WIPS/WIDS, which of the following statements is correct?
Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
Which of the following options are relevant to Any Office The description of the solution content is correct? (Multiple choice)
In Huawei USG6000 products, IAE provides an integrated solution, all content security detection functions are integrated in a well-designed
In the high-performance engine. Which of the following is not the content security detection function supported by this product?
Which of the following iterations is correct for the description of the management center?
Which of the following options is for Portal The statement of the gateway access process is correct?
Location refers to the end user's use AC-Campus The terminal environment when accessing the controlled network office. Which of the following options is correct for the description of the place?
In the visitor reception hall of a company, there are many temporary terminal users, and the administrator hopes that users do not need to provide any account numbers and passwords. access Internet. Which of the following authentication methods can be used for access?
Deploying on Windows platform, using SQL Server database About the HA function of Agile Cotoller-Campus, which of the following descriptions Is it correct? (multiple choice)
The user needs of a university are as follows:
1. The environment is large, and the total number of two-way traffic can reach 800M. Huawei USG6000 series firewall is deployed at its network node.
2. The intranet is divided into student area, server area, etc., users are most concerned about the security of the server area to avoid attacks from various threats.
3. At the same time, some pornographic websites in the student area are prohibited.
The external network has been configured as an untrust zone and the internal network has been configured as a trust zone on the firewall. How to configure the firewall to meet the above requirements?
155955cc-666171a2-20fac832-0c042c0415
For SYIN Flood attacks, TCP source authentication and TCP proxy can be used for defense. Which of the following descriptions is correct?
Regarding traditional firewalls, which of the following statements are correct? (multiple choice)
When configuring the antivirus software policy, if you set"The required antivirus software violation level is not installed or running"for"generally"And check"out Now serious violation of the rules prohibits access to the network"Options. When the user uses Any office Certify, The certification is passed, but the result of the security check Can the user access the network when the virus software is not turned on?
Since the sandbox can provide a virtual execution environment to detect files in the network, the sandbox can be substituted when deploying security equipment
Anti-Virus, IPS, spam detection and other equipment.
What equipment do Policy Center supported servers include? (Choose 3 answers)
When the -aa command is used on the access control device to test the connectivity with the Radius server, the running result shows success, but the user cannot Normal access, the possible reason does not include which of the following options?
In the deployment of Huawei NIP6000 products, only port mirroring can be used for streaming replication.