What are the roles of 802.1X authenticators and authentication servers?
The authenticator stores the user account database, while the server stores access policies.
The authenticator supports only EAP, while the authentication server supports only RADIUS.
The authenticator is a RADIUS client and the authentication server is a RADIUS server.
The authenticator makes access decisions and the server communicates them to the supplicant.
In the 802.1X network access control model, the roles of the authenticator and the authentication server are distinct yet complementary. The authenticator acts as a RADIUS client, which is a network device, like a switch or wireless access point, that directly interfaces with the client machine (supplicant). The authentication server, typically a RADIUS server, is responsible for verifying the credentials provided by the supplicant through the authenticator. This setup helps in separating the duties where the authenticator enforces authentication but does not decide on the validity of the credentials, which is the role of the authentication server.
From which solution can ClearPass Policy Manager (CPPM) receive detailed information about client device type OS and status?
ClearPass Onboard
ClearPass Access Tracker
ClearPass OnGuard
ClearPass Guest
ClearPass Policy Manager (CPPM) can receive detailed information about client device type, OS, and status from ClearPass OnGuard. ClearPass OnGuard is part of the ClearPass suite and provides posture assessment and endpoint health checks. It gathers detailed information on the status and security posture of devices trying to connect to the network, such as whether antivirus software is up to date, which operating system is running, and other details that characterize the device's compliance with the network's security policies.
What is a vulnerability of an unauthenticated Dime-Heliman exchange?
A hacker can replace the public values exchanged by the legitimate peers and launch an MITM attack.
A brute force attack can relatively quickly derive Diffie-Hellman private values if they are able to obtain public values
Diffie-Hellman with elliptic curve values is no longer considered secure in modem networks, based on NIST recommendations.
Participants must agree on a passphrase in advance, which can limit the usefulness of Diffie- Hell man in practical contexts.
The vulnerability of an unauthenticated Diffie-Hellman exchange, particularly when it comes to the risk of a man-in-the-middle (MITM) attack, is a significant concern. In this scenario, a hacker can intercept the public values exchanged between two legitimate parties and substitute them with their own. This allows the attacker to decrypt or manipulate the messages passing between the two original parties without them knowing. This answer is based on the fundamental principles of how Diffie-Hellman key exchange works and its vulnerabilities without authentication mechanisms. Reference materials from cryptographic textbooks and security protocols detail these vulnerabilities, such as those found in standards and publications by organizations like NIST.
What is a correct guideline for the management protocols that you should use on ArubaOS-Switches?
Disable Telnet and use TFTP instead.
Disable SSH and use https instead.
Disable Telnet and use SSH instead
Disable HTTPS and use SSH instead
In managing ArubaOS-Switches, the best practice is to disable less secure protocols such as Telnet and use more secure alternatives like SSH (Secure Shell). SSH provides encrypted connections between network devices, which is critical for maintaining the security and integrity of network communications. This guideline is aligned with general security best practices that prioritize the use of protocols with strong, built-in encryption mechanisms to prevent unauthorized access and ensure data privacy.
Device A is contacting https://arubapedia.arubanetworks.com. The web server sends a certificate chain. What does the browser do as part of validating the web server certificate?
It makes sure that the key in the certificate matches the key that DeviceA uses for HTTPS.
It makes sure the certificate has a DNS SAN that matches arubapedia.arubanetworks.com
It makes sure that the public key in the certificate matches DeviceA's private HTTPS key.
It makes sure that the public key in the certificate matches a private key stored on DeviceA.
When a device like Device A contacts a secure website and receives a certificate chain from the server, the browser's primary task is to validate the web server's certificate to ensure it is trustworthy. Part of this validation includes checking that the certificate contains a DNS Subject Alternative Name (SAN) that matches the domain name of the website being accessed—in this case, arubapedia.arubanetworks.com. This ensures that the certificate was indeed issued to the entity operating the domain and helps prevent man-in-the-middle attacks where an invalid certificate could be presented by an attacker. The DNS SAN check is critical because it directly ties the digital certificate to the domain it secures, confirming the authenticity of the website to the user's browser.
A user is having trouble connecting to an AP managed by a standalone Mobility Controller (MC). What can you do to get detailed logs and debugs for that user's client?
In the MC CLI, set up a control plane packet capture and filter for the client's IP address.
In the MC CLI, set up a data plane packet capture and filter for the client's MAC address.
In the MC UI’s Traffic Analytics dashboard, look for the client's IP address.
In the MC UI’s Diagnostics > Logs pages, add a "user-debug" log setting for the client's MAC address.
When troubleshooting connectivity issues for a user connecting to an AP managed by a standalone Mobility Controller (MC) in an AOS-8 architecture, detailed logs and debugs specific to the user’s client are essential. The MC provides several tools for capturing logs and debugging information, including packet captures and user-specific debug logs.
Option D, "In the MC UI’s Diagnostics > Logs pages, add a ‘user-debug’ log setting for the client's MAC address," is correct. The "user-debug" feature in the MC allows administrators to enable detailed debugging for a specific client by specifying the client’s MAC address. This generates logs related to the client’s authentication, association, role assignment, and other activities, which are critical for troubleshooting connectivity issues. The Diagnostics > Logs pages in the MC UI provide a user-friendly way to configure this setting and view the resulting logs.
Option A, "In the MC CLI, set up a control plane packet capture and filter for the client's IP address," is incorrect because control plane packet captures are used to capture management traffic (e.g., between the MC and APs or other controllers), not user traffic. Additionally, the client may not yet have an IP address if connectivity is failing, making an IP-based filter less effective.
Option B, "In the MC CLI, set up a data plane packet capture and filter for the client's MAC address," is a valid troubleshooting method but is not the best choice for getting detailed logs. Data plane packet captures are useful for analyzing user traffic (e.g., to see if packets are being dropped), but they do not provide the same level of detailed logging as the "user-debug" feature, which includes authentication and association events.
Option C, "In the MC UI’s Traffic Analytics dashboard, look for the client's IP address," is incorrect because the Traffic Analytics dashboard is used for monitoring application usage and traffic patterns, not for detailed troubleshooting of a specific client’s connectivity issues. Additionally, if the client cannot connect, it may not have an IP address or generate traffic visible in the dashboard.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"To troubleshoot issues for a specific wireless client, you can enable user-specific debugging using the ‘user-debug’ feature. In the Mobility Controller UI, navigate to Diagnostics > Logs, and add a ‘user-debug’ log setting for the client’s MAC address. This will generate detailed logs for the client, including authentication, association, and role assignment events, which can be viewed in the Logs page. For example, to enable user-debug for a client with MAC address 00:11:22:33:44:55, add the setting ‘user-debug 00:11:22:33:44:55’." (Page 512, Troubleshooting Wireless Clients Section)
Additionally, the guide notes:
"While packet captures (control plane or data plane) can be useful for analyzing traffic, the ‘user-debug’ feature provides more detailed logs for troubleshooting client-specific issues, such as failed authentication or association problems." (Page 513, Debugging Tools Section)
What is the purpose of an Enrollment over Secure Transport (EST) server?
It acts as an intermediate Certification Authority (CA) that signs end-entity certificates.
It helps admins to avoid expired certificates with less management effort.
It provides a secure central repository for private keys associated with devices' digital certif-icates.
It provides a more secure alternative to private CAs at less cost than a public CA.
EST (Enrollment over Secure Transport) is a protocol designed to streamline the certificate management process. It enables automated and secure enrollment, renewal, and revocation of digital certificates, which significantly reduces the management overhead typically associated with digital certificates. With EST, administrators can more easily manage certificates' lifecycle, ensuring that expired certificates are promptly replaced or renewed without significant manual intervention.
What is one way that WPA3-PerSonal enhances security when compared to WPA2-Personal?
WPA3-Perscn3i is more secure against password leaking Because all users nave their own username and password
WPA3-Personai prevents eavesdropping on other users' wireless traffic by a user who knows the passphrase for the WLAN.
WPA3-Personai is more resistant to passphrase cracking Because it requires passphrases to be at least 12 characters
WPA3-Personal is more complicated to deploy because it requires a backend authentication server
WPA3-Personal enhances security over WPA2-Personal by implementing individualized data encryption. This feature, known as Wi-Fi Enhanced Open, provides each user's session with a unique encryption key, even if they are using the same network passphrase. This prevents an authenticated user from eavesdropping on the traffic of other users on the same network, thus enhancing privacy and security.
You are checking the Security Dashboard in the Web Ul for your ArubaOS solution and see that Wireless Intrusion Prevention (WIP) has discovered a rogue radio operating in ad hoc mode with open security. What correctly describes a threat that the radio could pose?
It could open a backdoor into the corporate LAN for unauthorized users.
It is running in a non-standard 802.11 mode and could effectively jam the wireless signal.
It is flooding the air with many wireless frames in a likely attempt at a DoS attack.
It could be attempting to conceal itself from detection by changing its BSSID and SSID frequently.
A rogue radio operating in ad hoc mode with open security can pose several threats to a network. Ad hoc networks allow direct device-to-device communication without centralized control. If such a radio is present within or near a corporate environment, it can potentially be used to create a peer-to-peer network that bypasses corporate security controls, effectively acting as a backdoor into the corporate network for unauthorized users or devices. This can lead to a breach of data security and unauthorized access to network resources.
You have a network with AOS-CX switches for which HPE Aruba Networking ClearPass Policy Manager (CPPM) acts as the TACACS+ server. When an admin authenticates, CPPM sends a response with:
Aruba-Priv-Admin-User = 1
TACACS+ privilege level = 15What happens to the user?
The user receives auditors access.
The user receives no access.
The user receives administrators access.
The user receives operators access.
HPE Aruba Networking AOS-CX switches support TACACS+ for administrative authentication, where ClearPass Policy Manager (CPPM) can act as the TACACS+ server. When an admin authenticates, CPPM sends a TACACS+ response that includes attributes such as the TACACS+ privilege level and vendor-specific attributes (VSAs) like Aruba-Priv-Admin-User.
In this scenario, CPPM sends:
TACACS+ privilege level = 15: In TACACS+, privilege level 15 is the highest level and typically grants full administrative access (equivalent to a superuser or administrator role).
Aruba-Priv-Admin-User = 1: This Aruba-specific VSA indicates that the user should be granted the highest level of administrative access on the switch.
On AOS-CX switches, the privilege level 15 maps to the administrator role, which provides full read-write access to all switch functions. The Aruba-Priv-Admin-User = 1 attribute reinforces this by explicitly assigning the admin role, ensuring the user has unrestricted access.
Option A, "The user receives auditors access," is incorrect because auditors typically have read-only access, which corresponds to a lower privilege level (e.g., 1 or 3) on AOS-CX switches.
Option B, "The user receives no access," is incorrect because the authentication was successful, and CPPM sent a response granting access with privilege level 15.
Option D, "The user receives operators access," is incorrect because operators typically have a lower privilege level (e.g., 5 or 7), which provides limited access compared to an administrator.
The HPE Aruba Networking AOS-CX 10.12 Security Guide states:
"When using TACACS+ for administrative authentication, the switch interprets the privilege level returned by the TACACS+ server. A privilege level of 15 maps to the administrator role, granting full read-write access to all switch functions. The Aruba-Priv-Admin-User VSA, when set to 1, explicitly assigns the admin role, ensuring the user has unrestricted access." (Page 189, TACACS+ Authentication Section)
Additionally, the HPE Aruba Networking ClearPass Policy Manager 6.11 User Guide notes:
"ClearPass can send the Aruba-Priv-Admin-User VSA in a TACACS+ response to specify the administrative role on Aruba devices. A value of 1 indicates the admin role, which provides full administrative privileges." (Page 312, TACACS+ Enforcement Section)
You have detected a Rogue AP using the Security Dashboard Which two actions should you take in responding to this event? (Select two)
There is no need to locale the AP If you manually contain It.
This is a serious security event, so you should always contain the AP immediately regardless of your company's specific policies.
You should receive permission before containing an AP. as this action could have legal Implications.
For forensic purposes, you should copy out logs with relevant information, such as the time mat the AP was detected and the AP's MAC address.
There is no need to locate the AP If the Aruba solution is properly configured to automatically contain it.
When responding to the detection of a Rogue AP, it's important to consider legal implications and to gather forensic evidence:
You should receive permission before containing an AP (Option C), as containing it could disrupt service and may have legal implications, especially if the AP is on a network that the organization does not own.
For forensic purposes, it is essential to document the event by copying out logs with relevant information, such as the time the AP was detected and the AP's MAC address (Option D). This information could be crucial if legal action is taken or if a detailed analysis of the security breach is required.
Automatically containing an AP without consideration for the context (Options A and E) can be problematic, as it might inadvertently interfere with neighboring networks and cause legal issues. Immediate containment without consideration of company policy (Option B) could also violate established incident response procedures.
What is one practice that can help you to maintain a digital chain or custody In your network?
Enable packet capturing on Instant AP or Moodily Controller (MC) datepath on an ongoing basis
Enable packet capturing on Instant AP or Mobility Controller (MC) control path on an ongoing basis.
Ensure that all network infrastructure devices receive a valid clock using authenticated NTP
Ensure that all network Infrastructure devices use RADIUS rather than TACACS+ to authenticate managers
To maintain a digital chain of custody in a network, a crucial practice is to ensure that all network infrastructure devices receive a valid clock using authenticated Network Time Protocol (NTP). Accurate and synchronized time stamps are essential for creating reliable and legally defensible logs. Authenticated NTP ensures that the time being set on devices is accurate and that the time source is verified, which is necessary for correlating logs from different devices and for forensic analysis.
What is a use case for tunneling traffic between an Aruba switch and an AruDa Mobility Controller (MC)?
applying firewall policies and deep packet inspection to wired clients
enhancing the security of communications from the access layer to the core with data encryption
securing the network infrastructure control plane by creating a virtual out-of-band-management network
simplifying network infrastructure management by using the MC to push configurations to the switches
Tunneling traffic between an Aruba switch and an Aruba Mobility Controller (MC) allows for the centralized application of firewall policies and deep packet inspection to wired clients. By directing traffic through the MC, network administrators can implement a consistent set of security policies across both wired and wireless segments of the network, enhancing overall network security posture.
What is a guideline for creating certificate signing requests (CSRs) and deploying server Certificates on ArubaOS Mobility Controllers (MCs)?
Create the CSR online using the MC Web Ul if your company requires you to archive the private key.
if you create the CSR and public/private Keypair offline, create a matching private key online on the MC.
Create the CSR and public/private keypair offline If you want to install the same certificate on multiple MCs.
Generate the private key online, but the public key and CSR offline, to install the same certificate on multiple MCs.
Creating the Certificate Signing Request (CSR) and the public/private keypair offline is recommended when deploying server certificates on multiple ArubaOS Mobility Controllers (MCs). This method enhances security by minimizing the exposure of private keys. By creating and handling these components offline, administrators can maintain better control over the keys and ensure their security before deploying them across multiple devices. This approach also simplifies the management of certificates on multiple controllers, as the same certificate can be installed more securely and efficiently.
You need to implement a WPA3-Enterprise network that can also support WPA2-Enterprise clients. What is a valid configuration for the WPA3-Enterprise WLAN?
CNSA mode disabled with 256-bit keys
CNSA mode disabled with 128-bit keys
CNSA mode enabled with 256-bit keys
CNSA mode enabled with 128-bit keys
In an Aruba network, when setting up a WPA3-Enterprise network that also supports WPA2-Enterprise clients, you would typically configure the network to operate in a transitional mode that supports both protocols. CNSA (Commercial National Security Algorithm) mode is intended for networks that require higher security standards as specified by the US National Security Agency (NSA). However, for compatibility with WPA2 clients, which do not support CNSA requirements, you would disable CNSA mode. WPA3 can use 256-bit encryption keys, which offer a higher level of security than the 128-bit keys used in WPA2.
What is one way that Control Plane Security (CPSec) enhances security for the network?
It protects management traffic between APs and Mobility Controllers (MCs) from eavesdropping.
It prevents Denial of Service (DoS) attacks against Mobility Controllers' (MCs') control plane.
It protects wireless clients' traffic, tunneled between APs and Mobility Controllers, from eavesdropping.
It prevents access from unauthorized IP addresses to critical services, such as SSH, on Mobility Controllers (MCs).
Control Plane Security (CPSec) is a feature in HPE Aruba Networking’s AOS-8 architecture that secures the communication between Access Points (APs) and Mobility Controllers (MCs). The control plane includes management traffic, such as AP registration, configuration updates, and heartbeat messages, which are critical for the operation of the wireless network.
Option A, "It protects management traffic between APs and Mobility Controllers (MCs) from eavesdropping," is correct. CPSec uses certificate-based authentication and encryption (IPSec tunnels) to secure the control plane communication between APs and MCs. This ensures that management traffic, which includes sensitive information like configuration data and AP status, is encrypted and protected from eavesdropping by unauthorized parties on the network.
Option B, "It prevents Denial of Service (DoS) attacks against Mobility Controllers' (MCs') control plane," is incorrect. While CPSec enhances security by authenticating APs and encrypting traffic, it is not specifically designed to prevent DoS attacks. DoS attacks against the control plane are mitigated by other features, such as rate limiting or firewall policies on the MC.
Option C, "It protects wireless clients' traffic, tunneled between APs and Mobility Controllers, from eavesdropping," is incorrect. CPSec protects the control plane (management traffic), not the data plane (client traffic). Client traffic in a tunneled architecture (e.g., GRE tunnels) is protected by the client’s wireless encryption (e.g., WPA3), not CPSec.
Option D, "It prevents access from unauthorized IP addresses to critical services, such as SSH, on Mobility Controllers (MCs)," is incorrect. CPSec does not control access to services like SSH on the MC. Access to such services is managed by other features, such as access control lists (ACLs) or management authentication settings on the MC.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"Control Plane Security (CPSec) enhances network security by protecting the management traffic between Access Points (APs) and Mobility Controllers (MCs). When CPSec is enabled, the control plane communication is secured using certificate-based authentication and IPSec encryption, preventing eavesdropping and ensuring that only authorized APs can communicate with the MC. This protects sensitive management data, such as AP configuration and status updates, from being intercepted." (Page 392, CPSec Overview Section)
Additionally, the HPE Aruba Networking CPSec Deployment Guide notes:
"CPSec secures the control plane by encrypting management traffic between APs and MCs, ensuring that attackers cannot eavesdrop on or tamper with this communication. It does not protect client data traffic, which is secured by wireless encryption protocols like WPA3." (Page 8, CPSec Benefits Section)
The monitoring admin has asked you to set up an AOS-CX switch to meet these criteria:
Send logs to a SIEM Syslog server at 10.4.13.15 at the standard TCP port (514)
Send a log for all events at the "warning" level or above; do not send logs with a lower level than "warning"The switch did not have any "logging" configuration on it. You then entered this command:AOS-CX(config)# logging 10.4.13.15 tcp vrf defaultWhat should you do to finish configuring to the requirements?
Specify the "warning" severity level for the logging server.
Add logging categories at the global level.
Ask for the Syslog password and configure it on the switch.
Configure logging as a debug destination.
The task is to configure an AOS-CX switch to send logs to a SIEM Syslog server at IP address 10.4.13.15 using TCP port 514, with logs for events at the "warning" severity level or above (i.e., warning, error, critical, alert, emergency). The initial command entered is:
AOS-CX(config)# logging 10.4.13.15 tcp vrf default
This command configures the switch to send logs to the Syslog server at 10.4.13.15 using TCP (port 514 is the default for TCP Syslog unless specified otherwise) and the default VRF. However, this command alone does not specify the severity level of the logs to be sent, which is a requirement of the task.
Severity Level Configuration: AOS-CX switches allow you to specify the severity level for logs sent to a Syslog server. The severity levels, in increasing order of severity, are: debug, informational, notice, warning, error, critical, alert, and emergency. The requirement is to send logs at the "warning" level or above, meaning warning, error, critical, alert, and emergency logs should be sent, but debug, informational, and notice logs should not.
Option A, "Specify the ‘warning’ severity level for the logging server," is correct. To meet the requirement, you need to add the severity level to the logging configuration for the specific Syslog server. The command to do this is:
AOS-CX(config)# logging 10.4.13.15 severity warning
This command ensures that only logs with a severity of warning or higher are sent to the Syslog server at 10.4.13.15. Since the initial command already specified TCP and the default VRF, this additional command completes the configuration.
Option B, "Add logging categories at the global level," is incorrect. Logging categories (e.g., system, security, network) are used to filter logs based on the type of event, not the severity level. The requirement is about severity ("warning" or above), not specific categories, so this step is not necessary to meet the stated criteria.
Option C, "Ask for the Syslog password and configure it on the switch," is incorrect. Syslog servers typically do not require a password for receiving logs, and AOS-CX switches do not have a configuration option to specify a Syslog password. Authentication or encryption for Syslog (e.g., using TLS) is not mentioned in the requirements.
Option D, "Configure logging as a debug destination," is incorrect. Configuring a debug destination (e.g., using the debug command) is used to send debug-level logs to a destination (e.g., console, buffer, or Syslog), but the requirement is to send logs at the "warning" level or above, not debug-level logs. Additionally, the logging command already specifies the Syslog server as the destination.
The HPE Aruba Networking AOS-CX 10.12 System Management Guide states:
"To configure a Syslog server on an AOS-CX switch, use the logging
Additionally, the guide notes:
"Severity levels for logging on AOS-CX switches are, in increasing order: debug, informational, notice, warning, error, critical, alert, emergency. Specifying a severity level of ‘warning’ ensures that only logs at that level or higher are sent to the configured destination." (Page 90, Logging Severity Levels Section)
What is a correct use case for using the specified certificate file format?
using a PKCS7 file to install a certificate plus and its private key on a device
using a PKCS12 file to install a certificate plus its private key on a device
using a PEM file to install a binary encoded certificate on a device
using a PKCS7 file to install a binary encoded private key on a device
The correct use case for using the specified certificate file format is option B, using a PKCS12 file to install a certificate along with its private key on a device. PKCS12 is a binary format for storing a certificate chain and private key in a single encrypted file. PEM files are Base64 encoded certificate files and are typically used for storing certificates, not private keys, and PKCS7 is used for certificate chains without the private key.
These answers are based on general networking and security practices, specifically within the context of Aruba network device configurations. If you have questions specific to Oracle Database 12c SQL, please provide the relevant details or ask separate questions related to that topic.
What is a correct guideline for the management protocols that you should use on AOS-CX switches?
Make sure that SSH is disabled and use HTTPS instead.
Make sure that Telnet is disabled and use SSH instead.
Make sure that Telnet is disabled and use TFTP instead.
Make sure that HTTPS is disabled and use SSH instead.
AOS-CX switches support various management protocols for administrative access, such as SSH, Telnet, HTTPS, and TFTP. Security best practices for managing network devices, including AOS-CX switches, emphasize using secure protocols to protect management traffic from eavesdropping and unauthorized access.
Option B, "Make sure that Telnet is disabled and use SSH instead," is correct. Telnet is an insecure protocol because it sends all data, including credentials, in plaintext, making it vulnerable to eavesdropping. SSH (Secure Shell) provides encrypted communication for remote management, ensuring that credentials and commands are protected. HPE Aruba Networking recommends disabling Telnet and enabling SSH for secure management access on AOS-CX switches.
Option A, "Make sure that SSH is disabled and use HTTPS instead," is incorrect. SSH and HTTPS serve different purposes: SSH is for CLI access, while HTTPS is for web-based management. Disabling SSH would prevent secure CLI access, which is not a recommended practice. Both SSH and HTTPS should be enabled for secure management.
Option C, "Make sure that Telnet is disabled and use TFTP instead," is incorrect. TFTP (Trivial File Transfer Protocol) is used for file transfers (e.g., firmware updates), not for management access like Telnet or SSH. TFTP is also insecure (no encryption), so it’s not a suitable replacement for Telnet.
Option D, "Make sure that HTTPS is disabled and use SSH instead," is incorrect. HTTPS is used for secure web-based management and should not be disabled. Both HTTPS and SSH are secure protocols and should be used together for different management interfaces (web and CLI, respectively).
The HPE Aruba Networking AOS-CX 10.12 Security Guide states:
"For secure management of AOS-CX switches, disable insecure protocols like Telnet, which sends data in plaintext, and use SSH instead. SSH provides encrypted communication for CLI access, protecting credentials and commands from eavesdropping. Use the command no telnet-server to disable Telnet and ssh-server to enable SSH. Additionally, enable HTTPS for web-based management with https-server to ensure all management traffic is encrypted." (Page 195, Secure Management Protocols Section)
Additionally, the HPE Aruba Networking Security Best Practices Guide notes:
"A key guideline for managing AOS-CX switches is to disable Telnet and enable SSH for CLI access. Telnet is insecure and should not be used in production environments, as it transmits credentials in plaintext. SSH ensures secure remote management, and HTTPS should also be enabled for web access." (Page 25, Management Security Section)
Which attack is an example or social engineering?
An email Is used to impersonate a Dank and trick users into entering their bank login information on a fake website page.
A hacker eavesdrops on insecure communications, such as Remote Desktop Program (RDP). and discovers login credentials.
A user visits a website and downloads a file that contains a worm, which sell-replicates throughout the network.
An attack exploits an operating system vulnerability and locks out users until they pay the ransom.
An example of a social engineering attack is described in option A, where an email is used to impersonate a bank and deceive users into entering their bank login information on a counterfeit website. Social engineering attacks exploit human psychology rather than technical hacking techniques to gain access to systems, data, or personal information. These attacks often involve tricking people into breaking normal security procedures. The other options describe different types of technical attacks that do not primarily rely on manipulating individuals through deceptive personal interactions.
A company has a WLAN that uses Tunnel forwarding mode and WPA3-Enterprise security, supported by an Aruba Mobility Controller (MC) and campus APs (CAPs). You have been asked to capture packets from a wireless client connected to this WLAN and submit the packets to the security team.
What is a guideline for this capture?
You should use an Air Monitor (AM) to capture the packets in the air.
You should capture the traffic on the MC dataplane to obtain unencrypted traffic.
You should mirror traffic from the switch port that connects to the AP out on a port connected to a packet analyzer.
You should capture the traffic on the AP, so that the capture is as close to the source as possible.
The correct approach for capturing packets from a wireless client in a WLAN that uses Tunnel forwarding mode and WPA3-Enterprise, managed by an Aruba Mobility Controller and Campus APs, is to use an Air Monitor (AM). An AM is specifically designed to capture wireless traffic "in the air," which means it listens to the wireless signals transmitted between devices and the access points. This method ensures that the capture includes all the necessary details while maintaining the integrity and security of the data as it is transmitted over the air. Using an Air Monitor helps in analyzing the raw wireless traffic before it gets encrypted or tunneled to the Mobility Controller, providing a clear view of the wireless client's activity and interactions. The information regarding the use of Air Monitors for packet capture in such environments can be found in the Aruba Network's official documentation and configuration guides for WLAN setups and security analysis.
What is a guideline for managing local certificates on AOS-CX switches?
Understand that the switch must use the same certificate for all usages, such as its HTTPS server and RadSec client.
Create a self-signed certificate online on the switch because AOS-CX switches do not support CA-signed certificates.
Before installing the local certificate, create a trust anchor (TA) profile with the root CA certificate for the certificate that you will install.
Install an Online Certificate Status Protocol (OCSP) certificate to simplify the process of enrolling and re-enrolling for certificates.
AOS-CX switches use certificates for various purposes, such as securing HTTPS access to the switch’s web interface, authenticating the switch as a RadSec client, or securing other communications. Managing local certificates on AOS-CX switches involves ensuring that the switch trusts the certificate authority (CA) that issued the certificate, which is critical for proper operation.
Option C, "Before installing the local certificate, create a trust anchor (TA) profile with the root CA certificate for the certificate that you will install," is correct. A trust anchor (TA) profile on AOS-CX switches contains the root CA certificate (or intermediate CA certificate) that issued the local certificate. This TA profile allows the switch to validate the certificate chain when the local certificate is installed. For example, if you install a CA-signed certificate for the HTTPS server, the switch needs the root CA certificate in a TA profile to trust the certificate. This is a standard guideline for certificate management on AOS-CX switches to ensure secure and proper operation.
Option A, "Understand that the switch must use the same certificate for all usages, such as its HTTPS server and RadSec client," is incorrect. AOS-CX switches support using different certificates for different purposes. For example, you can have one certificate for the HTTPS server and another for RadSec client authentication, as long as each certificate is associated with the appropriate service and trusted by the switch.
Option B, "Create a self-signed certificate online on the switch because AOS-CX switches do not support CA-signed certificates," is incorrect. AOS-CX switches fully support CA-signed certificates, and using CA-signed certificates is recommended for production environments to ensure trust and security. Self-signed certificates can be used for testing but are not a guideline for general certificate management.
Option D, "Install an Online Certificate Status Protocol (OCSP) certificate to simplify the process of enrolling and re-enrolling for certificates," is incorrect. OCSP is a protocol used to check the revocation status of certificates, not to simplify certificate enrollment. AOS-CX switches support OCSP for certificate validation, but installing an "OCSP certificate" is not a concept in certificate management, and it’s not a guideline for managing local certificates.
The HPE Aruba Networking AOS-CX 10.12 Security Guide states:
"Before installing a CA-signed local certificate on the switch, you must create a trust anchor (TA) profile that includes the root CA certificate (or intermediate CA certificate) that issued the local certificate. This ensures that the switch can validate the certificate chain. For example, to install a CA-signed certificate for the HTTPS server, use the command crypto pki ta-profile
Additionally, the guide notes:
"AOS-CX switches support both self-signed and CA-signed certificates. For production environments, it is recommended to use CA-signed certificates and ensure that the appropriate trust anchor profiles are configured to validate the certificate chain." (Page 202, Best Practices Section)
What is a difference between radius and TACACS+?
RADIUS combines the authentication and authorization process while TACACS+ separates them.
RADIUS uses TCP for Its connection protocol, while TACACS+ uses UDP tor its connection protocol.
RADIUS encrypts the complete packet, white TACACS+ only offers partial encryption.
RADIUS uses Attribute Value Pairs (AVPs) in its messages, while TACACS+ does not use them.
RADIUS and TACACS+ are both protocols used for networking authentication, but they handle the processes of authentication and authorization differently. RADIUS (Remote Authentication Dial-In User Service) combines authentication and authorization into a single process, whereas TACACS+ (Terminal Access Controller Access-Control System Plus) separates these processes. This separation in TACACS+ allows more flexible policy enforcement and better control over commands a user can execute. This difference is well-documented in various network security resources, including Cisco's technical documentation and security protocol manuals.
How does the AOS firewall determine which rules to apply to a specific client's traffic?
The firewall applies the rules in policies associated with the client's user role.
The firewall applies every rule that includes the client's IP address as the source.
The firewall applies the rules in policies associated with the client's WLAN.
The firewall applies every rule that includes the client's IP address as the source or destination.
In an AOS-8 architecture, the Mobility Controller (MC) includes a stateful firewall that enforces policies on client traffic. The firewall uses user roles to apply policies, allowing granular control over traffic based on the client’s identity and context.
User Roles: In AOS-8, each client is assigned a user role after authentication (e.g., via 802.1X, MAC authentication, or captive portal). The user role contains firewall policies (rules) that define what traffic is allowed or denied for clients in that role. For example, a "guest" role might allow only HTTP/HTTPS traffic, while an "employee" role might allow broader access.
Option A, "The firewall applies the rules in policies associated with the client's user role," is correct. The AOS firewall evaluates traffic based on the user role assigned to the client. Each role has a set of policies (rules) that are applied in order, and the first matching rule determines the action (permit or deny). For example, if a client is in the "employee" role, the firewall applies the rules defined in the "employee" role’s policy.
Option B, "The firewall applies every rule that includes the client's IP address as the source," is incorrect. The firewall does not apply rules based solely on the client’s IP address; it uses the user role. Rules within a role may include IP addresses, but the role determines which rules are evaluated.
Option C, "The firewall applies the rules in policies associated with the client's WLAN," is incorrect. While the WLAN configuration defines the initial role for clients (e.g., the default 802.1X role), the firewall applies rules based on the client’s current user role, which may change after authentication (e.g., via a RADIUS VSA like Aruba-User-Role).
Option D, "The firewall applies every rule that includes the client's IP address as the source or destination," is incorrect for the same reason as Option B. The firewall uses the user role to determine which rules to apply, not just the client’s IP address.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"The AOS firewall on the Mobility Controller applies rules based on the user role assigned to a client. Each user role contains a set of firewall policies that define the allowed or denied traffic for clients in that role. For example, a policy in the ‘employee’ role might include a rule like ipv4 user any http permit to allow HTTP traffic. The firewall evaluates the rules in the client’s role in order, and the first matching rule determines the action for the traffic." (Page 325, Firewall Policies Section)
Additionally, the HPE Aruba Networking Security Guide notes:
"User roles in AOS-8 provide a powerful mechanism for firewall policy enforcement. The firewall determines which rules to apply to a client’s traffic by looking at the policies associated with the client’s user role, which is assigned during authentication or via a RADIUS VSA like Aruba-User-Role." (Page 50, Role-Based Access Control Section)
A company has an ArubaOS solution. The company wants to prevent users assigned to the "user_group1" role from using gaming and peer-to-peer applications.
What is the recommended approach for these requirements?
Make sure DPI is enabled, and add application rules that deny gaming and peer-to-peer applications to the "user_groupr role.
Create ALGs for the gaming and peer-to-peer applications, and deny the "user_group1" role on the ALGs.
Add access control rules to the "user_group1" role, which deny HTTP/HTTPS traffic to IP addresses associated with gaming and peer-to-peer applications.
Create service aliases for the TCP ports associated with gaming and peer-to-per applications, and use those aliases in access control rules for the "user_group" rules.
The recommended approach for preventing users in the "user_group1" role from using gaming and peer-to-peer applications in an ArubaOS environment is to enable Deep Packet Inspection (DPI) and add application rules that specifically deny access to these types of applications for the role. DPI allows the network system to analyze the content of network traffic in real time and apply policies based on what it detects, including blocking specific applications like gaming and peer-to-peer sharing. This capability is essential for effectively managing application usage on the network and ensuring compliance with organizational policies. Application-specific rules provide precise control over the network traffic by identifying the application regardless of the network port used, making it a more effective method than blocking based on ports or IP addresses.
You have been instructed to look in the ArubaOS Security Dashboard's client list. Your goal is to find clients that belong to the company and have connected to devices that might belong to hackers.
Which client fits this description?
MAC address: d8:50:e6:f3:70:ab; Client Classification: Interfering; AP Classification: Rogue
MAC address: d8:50:e6:f3:6e:c5; Client Classification: Interfering; AP Classification: Neighbor
MAC address: d8:50:e6:f3:6e:60; Client Classification: Interfering; AP Classification: Authorized
MAC address: d8:50:e6:f3:6d:a4; Client Classification: Authorized; AP Classification: Rogue
The ArubaOS Security Dashboard, part of the AOS-8 architecture (Mobility Controllers or Mobility Master), provides visibility into wireless clients and access points (APs) through its Wireless Intrusion Prevention (WIP) system. The goal is to identify clients that belong to the company (i.e., authorized clients) and have connected to devices that might belong to hackers (i.e., rogue APs).
Client Classification:
Authorized: A client that has successfully authenticated to an authorized AP and is recognized as part of the company’s network (e.g., an employee device).
Interfering: A client that is not authenticated to the company’s network and is considered external or potentially malicious.
AP Classification:
Authorized: An AP that is part of the company’s network and managed by the MC/MM.
Rogue: An AP that is not authorized and is suspected of being malicious (e.g., connected to the company’s wired network without permission).
Neighbor: An AP that is not part of the company’s network but is not connected to the wired network (e.g., a nearby AP from another organization).
The requirement is to find a client that is authorized (belongs to the company) and connected to a rogue AP (might belong to hackers).
Option A: MAC address: d8:50:e6:f3:70:ab; Client Classification: Interfering; AP Classification: RogueThis client is classified as "Interfering," meaning it does not belong to the company. Although it is connected to a rogue AP, it does not meet the requirement of being a company client.
Option B: MAC address: d8:50:e6:f3:6e:c5; Client Classification: Interfering; AP Classification: NeighborThis client is "Interfering" (not a company client) and connected to a "Neighbor" AP, which is not considered a hacker’s device (it’s just a nearby AP).
Option C: MAC address: d8:50:e6:f3:6e:60; Client Classification: Interfering; AP Classification: AuthorizedThis client is "Interfering" (not a company client) and connected to an "Authorized" AP, which is part of the company’s network, not a hacker’s device.
Option D: MAC address: d8:50:e6:f3:6d:a4; Client Classification: Authorized; AP Classification: RogueThis client is "Authorized," meaning it belongs to the company, and it is connected to a "Rogue" AP, which might belong to hackers. This matches the requirement perfectly.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"The Security Dashboard in ArubaOS provides a client list that includes the client classification and the AP classification for each client. A client classified as ‘Authorized’ has successfully authenticated to an authorized AP and is part of the company’s network. A ‘Rogue’ AP is an unauthorized AP that is suspected of being malicious, often because it is connected to the company’s wired network (e.g., detected via Eth-Wired-Mac-Table match). To identify potential security risks, look for authorized clients connected to rogue APs, as this may indicate that a company device has connected to a hacker’s AP." (Page 415, Security Dashboard Section)
Additionally, the HPE Aruba Networking Security Guide notes:
"An ‘Authorized’ client is one that has authenticated to an AP managed by the controller, typically an employee or corporate device. A ‘Rogue’ AP is classified as such if it is not authorized and poses a potential threat, such as being connected to the corporate LAN. Identifying authorized clients connected to rogue APs is critical for detecting potential man-in-the-middle attacks." (Page 78, WIP Classifications Section)
A company is deploying ArubaOS-CX switches to support 135 employees, which will tunnel client traffic to an Aruba Mobility Controller (MC) for the MC to apply firewall policies and deep packet inspection (DPI). This MC will be dedicated to receiving traffic from the ArubaOS-CX switches.
What are the licensing requirements for the MC?
one AP license per-switch
one PEF license per-switch
one PEF license per-switch. and one WCC license per-switch
one AP license per-switch. and one PEF license per-switch
When deploying ArubaOS-CX switches that tunnel client traffic to an Aruba Mobility Controller (MC), the licensing requirements typically involve Policy Enforcement Firewall (PEF) licenses. These licenses enable the MC to enforce firewall policies and perform deep packet inspection (DPI). Therefore, for each switch tunneling traffic to the MC, a PEF license would be necessary.
What purpose does an initialization vector (IV) serve for encryption?
It helps parties to negotiate the keys and algorithms used to secure data before data transmission.
It makes encryption algorithms more secure by ensuring that same plaintext and key can produce different ciphertext.
It enables programs to convert easily-remembered passphrases to keys of a correct length.
It enables the conversion of asymmetric keys into keys that are suitable for symmetric encryption.
The primary purpose of an Initialization Vector (IV) in encryption is to ensure that the same plaintext encrypted with the same encryption key will produce different ciphertext each time it is encrypted. This variability is crucial for securing repetitive data patterns and preventing certain types of cryptographic attacks, such as replay or pattern analysis attacks. The IV adds randomness to the encryption process, making it more secure by ensuring that encrypted messages are unique, even if the plaintext and key remain unchanged. This prevents attackers from deducing patterns or inferring any useful information from repeated ciphertext.
A company with 382 employees wants to deploy an open WLAN for guests. The company wants the experience to be as follows:
The company also wants to provide encryption for the network for devices mat are capable, you implement Tor the WLAN?
Which security options should
WPA3-Personal and MAC-Auth
Captive portal and WPA3-Personai
Captive portal and Opportunistic Wireless Encryption (OWE) in transition mode
Opportunistic Wireless Encryption (OWE) and WPA3-Personal
For a company that wants to deploy an open WLAN for guests with the ease of access and encryption for capable devices, using a captive portal with Opportunistic Wireless Encryption (OWE) in transition mode would be suitable. The captive portal allows for a user-friendly login page for authentication without a pre-shared key, and OWE provides encryption to protect user data without the complexities of traditional WPA or WPA2 encryption, which is ideal for guest networks. Transition mode allows devices that support OWE to use it while still allowing older or unsupported devices to connect.
You are deploying an Aruba Mobility Controller (MC). What is a best practice for setting up secure management access to the ArubaOS Web UP
Avoid using external manager authentication tor the Web UI.
Change the default 4343 port tor the web UI to TCP 443.
Install a CA-signed certificate to use for the Web UI server certificate.
Make sure to enable HTTPS for the Web UI and select the self-signed certificate Installed in the factory.
For securing management access to the ArubaOS Web UI of an Aruba Mobility Controller (MC), it is a best practice to install a certificate signed by a Certificate Authority (CA). This ensures that communications between administrators and the MC are secured with trusted encryption, which greatly reduces the risk of man-in-the-middle attacks. Using a CA-signed certificate enhances the trustworthiness of the connection over self-signed certificates, which do not offer the same level of assurance.
Refer to the exhibit, which shows the settings on the company’s MCs.
— Mobility Controller
Dashboard General Admin AirWave CPSec Certificates
Configuration
WLANsv Control Plane Security
Roles & PoliciesEnable CP Sec
Access PointsEnable auto cert provisioning:
You have deployed about 100 new Aruba 335-APs. What is required for the APs to become managed?
installing CA-signed certificates on the APs
installing self-signed certificates on the APs
approving the APs as authorized APs on the AP whitelist
configuring a PAPI key that matches on the APs and MCs
Based on the exhibit, which shows the settings on the company's Mobility Controllers (MCs), with 'Control Plane Security' enabled and 'Enable auto cert provisioning' available, new Aruba 335-APs require approval on the MC to become managed. This is commonly done by adding the APs to an authorized AP whitelist, after which they can be automatically provisioned with certificates generated by the MC.
Which is a correct description of a stage in the Lockheed Martin kill chain?
In the weaponization stage, which occurs after malware has been delivered to a system, the malware executes its function.
In the exploitation and installation phases, malware creates a backdoor into the infected system for the hacker.
In the reconnaissance stage, the hacker assesses the impact of the attack and how much information was exfiltrated.
In the delivery stage, malware collects valuable data and delivers or exfiltrates it to the hacker.
The Lockheed Martin Cyber Kill Chain is a framework that outlines the stages of a cyber attack, from initial reconnaissance to achieving the attacker’s objective. It is often referenced in HPE Aruba Networking security documentation to help organizations understand and mitigate threats. The stages are: Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control (C2), and Actions on Objectives.
Option A, "In the weaponization stage, which occurs after malware has been delivered to a system, the malware executes its function," is incorrect. The weaponization stage occurs before delivery, not after. In this stage, the attacker creates a deliverable payload (e.g., combining malware with an exploit). The execution of the malware happens in the exploitation stage, not weaponization.
Option B, "In the exploitation and installation phases, malware creates a backdoor into the infected system for the hacker," is correct. The exploitation phase involves the attacker exploiting a vulnerability (e.g., a software flaw) to execute the malware on the target system. The installation phase follows, where the malware installs itself to establish persistence, often by creating a backdoor (e.g., a remote access tool) to allow the hacker to maintain access to the system. These two phases are often linked in the kill chain as the malware gains a foothold and ensures continued access.
Option C, "In the reconnaissance stage, the hacker assesses the impact of the attack and how much information was exfiltrated," is incorrect. The reconnaissance stage occurs at the beginning of the kill chain, where the attacker gathers information about the target (e.g., network topology, vulnerabilities). Assessing the impact and exfiltration occurs in the Actions on Objectives stage, the final stage of the kill chain.
Option D, "In the delivery stage, malware collects valuable data and delivers or exfiltrates it to the hacker," is incorrect. The delivery stage involves the attacker transmitting the weaponized payload to the target (e.g., via a phishing email). Data collection and exfiltration occur later, in the Actions on Objectives stage, not during delivery.
The HPE Aruba Networking Security Guide states:
"The Lockheed Martin Cyber Kill Chain outlines the stages of a cyber attack. In the exploitation phase, the attacker exploits a vulnerability to execute the malware on the target system. In the installation phase, the malware creates a backdoor or other persistence mechanism, such as a remote access tool, to allow the hacker to maintain access to the infected system for future actions." (Page 18, Cyber Kill Chain Overview Section)
Additionally, the HPE Aruba Networking AOS-8 8.11 User Guide notes:
"The exploitation and installation phases of the Lockheed Martin kill chain involve the malware gaining a foothold on the target system. During exploitation, the malware is executed by exploiting a vulnerability, and during installation, it creates a backdoor to ensure persistent access for the hacker, enabling further stages like command and control." (Page 420, Threat Mitigation Section)
Refer to the exhibits.
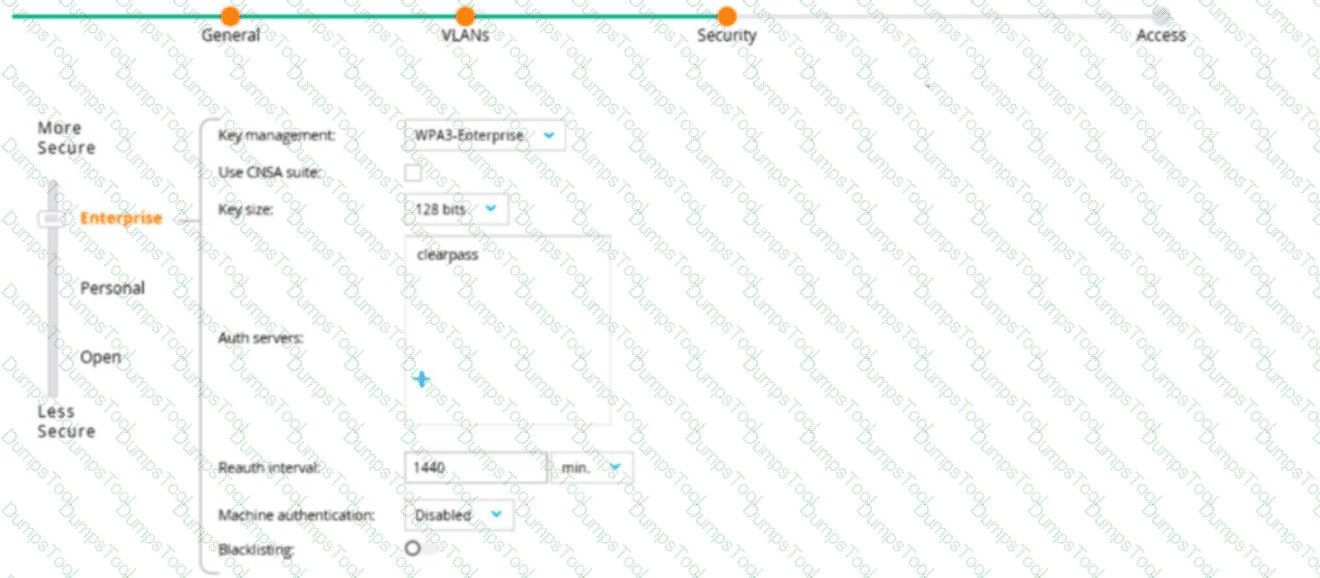
An admin has created a WLAN that uses the settings shown in the exhibits (and has not otherwise adjusted the settings in the AAA profile). A client connects to the WLAN. Under which circumstances will a client receive the default role assignment?
The client has attempted 802.1X authentication, but the MC could not contact the authentication server.
The client has passed 802.1X authentication, and the authentication server did not send an Aruba-User-Role VSA.
The client has attempted 802.1X authentication, but failed to maintain a reliable connection, leading to a timeout error.
The client has passed 802.1X authentication, and the value in the Aruba-User-Role VSA matches a role on the MC.
The exhibit shows the configuration of a WLAN on an AOS-8 Mobility Controller (MC) with the following settings:
Key management: WPA3-Enterprise (indicating 802.1X authentication).
Use CNSA suite: Unchecked (using standard encryption, not the Commercial National Security Algorithm suite).
Key size: 128 bits (standard for AES-GCMP in WPA3).
Reauth interval: 1440 minutes (24 hours, the interval for re-authentication).
Machine authentication: Disabled (only user authentication is required).
Blacklisting: Disabled (clients are not blacklisted after failed attempts).
The question states that the AAA profile settings have not been adjusted, meaning the default roles (e.g., initial role, logon role, 802.1X default role) are not specified in the exhibit and are assumed to be the system defaults (e.g., "logon" for the initial and logon roles, and a default role like "guest" for the 802.1X default role). The question asks under which circumstances a client will receive the "default role assignment," which refers to the 802.1X default role configured in the AAA profile for the WLAN.
802.1X Authentication Process in AOS-8:
When a client connects to a WPA3-Enterprise WLAN, it starts in the initial role (typically "logon") to allow basic connectivity (e.g., DHCP, DNS).
During 802.1X authentication, the client is placed in the logon role to allow communication with the authentication server (e.g., ClearPass Policy Manager, CPPM).
If authentication succeeds, the client is assigned a role:
If the authentication server (e.g., CPPM) sends an Aruba-User-Role VSA with a role that exists on the MC, the client is assigned that role.
If no Aruba-User-Role VSA is sent, the client is assigned the 802.1X default role configured in the AAA profile for the WLAN.
If authentication fails or the server is unreachable, the client may be assigned a different role (e.g., a critical role, if configured) or denied access.
Option A, "The client has attempted 802.1X authentication, but the MC could not contact the authentication server," is incorrect. If the MC cannot contact the authentication server (e.g., due to a timeout), the client does not receive the 802.1X default role. Instead, the MC may apply a critical role (if configured) or deny access, depending on the configuration. The 802.1X default role is applied only after successful authentication.
Option B, "The client has passed 802.1X authentication, and the authentication server did not send an Aruba-User-Role VSA," is correct. If the client successfully authenticates via 802.1X and the authentication server (e.g., CPPM) does not send an Aruba-User-Role VSA, the MC assigns the client the 802.1X default role configured in the AAA profile for the WLAN. This is the "default role assignment" referred to in the question.
Option C, "The client has attempted 802.1X authentication, but failed to maintain a reliable connection, leading to a timeout error," is incorrect. A timeout error during authentication (e.g., the client fails to respond to EAP messages) typically results in an authentication failure, not a successful authentication. The client would not receive the 802.1X default role; it might be denied access or placed in a different role (e.g., a pre-authentication role).
Option D, "The client has passed 802.1X authentication, and the value in the Aruba-User-Role VSA matches a role on the MC," is incorrect. If the authentication server sends an Aruba-User-Role VSA with a role that exists on the MC, the client is assigned that specific role, not the 802.1X default role.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"After a client successfully authenticates via 802.1X, the Mobility Controller assigns a role to the client. If the authentication server (e.g., a RADIUS server) sends an Aruba-User-Role VSA with a role that exists on the controller, the client is assigned that role. If no Aruba-User-Role VSA is sent in the Access-Accept message, the client is assigned the 802.1X default role configured in the AAA profile for the WLAN. For example, if the AAA profile specifies ‘guest’ as the 802.1X default role, the client will be assigned the ‘guest’ role." (Page 305, Role Assignment Section)
Additionally, the HPE Aruba Networking Wireless Security Guide notes:
"In WPA3-Enterprise with 802.1X authentication, the default role assignment occurs when a client successfully authenticates but the authentication server does not specify a role via the Aruba-User-Role VSA. In this case, the client receives the 802.1X default role defined in the AAA profile, such as ‘guest’ or another role configured by the administrator." (Page 42, 802.1X Role Assignment Section)
What is one benefit of a Trusted Platform Module (TPM) on an Aruba AP?
It enables secure boot, which detects if hackers corrupt the OS with malware.
It deploys the AP with enhanced security, which includes disabling the password recovery mechanism.
It allows the AP to run in secure mode, which automatically enables CPsec and disables the console port.
It enables the AP to encrypt and decrypt 802.11 traffic locally, rather than at the MC.
The TPM (Trusted Platform Module) is a hardware-based security feature that can provide various security functions, one of which includes secure boot. Secure boot is a process where the TPM ensures that the device boots using only software that is trusted by the manufacturer. If the OS has been tampered with or infected with malware, the secure boot process can detect this and prevent the system from loading the compromised OS.
You are deploying a new wireless solution with an Aruba Mobility Master (MM). Aruba Mobility Controllers (MCs), and campus APs (CAPs). The solution will include a WLAN that uses Tunnel for the forwarding mode and WPA3-Enterprise for the security option.
You have decided to assign the WLAN to VLAN 301, a new VLAN. A pair of core routing switches will act as the default router for wireless user traffic.
Which links need to carry VLAN 301?
only links in the campus LAN to ensure seamless roaming
only links between MC ports and the core routing switches
only links on the path between APs and the core routing switches
only links on the path between APs and the MC
In a wireless network deployment with Aruba Mobility Master (MM), Mobility Controllers (MCs), and Campus APs (CAPs), where a WLAN is configured to use Tunnel mode for forwarding, the user traffic is tunneled from the APs to the MCs. VLAN 301, which is assigned to the WLAN, must be present on the links from the MCs to the core routing switches because these switches act as the default router for the wireless user traffic. It is not necessary for the VLAN to be present on all campus LAN links or AP links, only between the MCs and the core routing switches where the routing for VLAN 301 will occur.
What is one of the policies that a company should define for digital forensics?
which data should be routinely logged, where logs should be forwarded, and which logs should be archived
what are the first steps that a company can take to implement micro-segmentation in their environment
to which resources should various users be allowed access, based on their identity and the identity of their clients
which type of EAP method is most secure for authenticating wired and wireless users with 802.1
In the context of digital forensics, policy A is the most relevant. It defines which data should be logged, where logs should be forwarded for analysis or storage, and which logs should be archived for future forensic analysis or audit purposes. This ensures that evidence is preserved in a way that supports forensic activities.
Why might devices use a Diffie-Hellman exchange?
to agree on a shared secret in a secure manner over an insecure network
to obtain a digital certificate signed by a trusted Certification Authority
to prove knowledge of a passphrase without transmitting the passphrase
to signal that they want to use asymmetric encryption for future communications
Devices use the Diffie-Hellman exchange to agree on a shared secret in a secure manner over an insecure network. The main purpose of this cryptographic protocol is to enable two parties to establish a shared secret over an unsecured communication channel. This shared secret can then be used to encrypt subsequent communications using a symmetric key cipher. The Diffie-Hellman exchange is particularly valuable because it allows the secure exchange of cryptographic keys over a public channel without the need for a prior shared secret. This protocol is a foundational element for many secure communications protocols, including SSL/TLS, which is used to secure connections on the internet. References to the Diffie-Hellman protocol and its uses can be found in standard cryptographic textbooks and documentation such as those from the Internet Engineering Task Force (IETF) and security protocol specifications.
What is a benefit of Protected Management Frames (PMF). sometimes called Management Frame Protection (MFP)?
PMF helps to protect APs and MCs from unauthorized management access by hackers.
PMF ensures trial traffic between APs and Mobility Controllers (MCs) is encrypted.
PMF prevents hackers from capturing the traffic between APs and Mobility Controllers.
PMF protects clients from DoS attacks based on forged de-authentication frames
Protected Management Frames (PMF), also known as Management Frame Protection (MFP), is designed to protect clients from denial-of-service (DoS) attacks that involve forged de-authentication and disassociation frames. These attacks can disconnect legitimate clients from the network. PMF provides a way to authenticate these management frames, ensuring that they are not forged, thus enhancing the security of the wireless network.
You have an Aruba Mobility Controller (MC) that is locked in a closet. What is another step that Aruba recommends to protect the MC from unauthorized access?
Use local authentication rather than external authentication to authenticate admins.
Change the password recovery password.
Set the local admin password to a long random value that is unknown or locked up securely.
Disable local authentication of administrators entirely.
Protecting an Aruba Mobility Controller from unauthorized access involves several layers of security. One recommendation is to change the password recovery password, which is a special type of password used to recover access to the device in the event the admin password is lost. Changing this to something complex and unique adds an additional layer of security in the event the physical security of the device is compromised.
You configure an ArubaOS-Switch to enforce 802.1X authentication with ClearPass Policy Manager (CPPM) denned as the RADIUS server Clients cannot authenticate You check Aruba ClearPass Access Tracker and cannot find a record of the authentication attempt.
What are two possible problems that have this symptom? (Select two)
users are logging in with the wrong usernames and passwords or invalid certificates.
Clients are configured to use a mismatched EAP method from the one In the CPPM service.
The RADIUS shared secret does not match between the switch and CPPM.
CPPM does not have a network device defined for the switch's IP address.
Clients are not configured to trust the root CA certificate for CPPM's RADIUS/EAP certificate.
If clients cannot authenticate and there is no record of the authentication attempt in Aruba ClearPass Access Tracker, two possible problems that could cause this symptom are:
The RADIUS shared secret does not match between the switch and CPPM. This mismatch would prevent the switch and CPPM from successfully communicating, so authentication attempts would fail, and no record would appear in Access Tracker.
CPPM does not have a network device profile defined for the switch's IP address. Without a network device profile, CPPM would not recognize authentication attempts coming from the switch and would not process them, resulting in no logs in Access Tracker.
The other options are incorrect because:
Users logging in with the wrong credentials would still generate an attempt record in Access Tracker.
Clients configured to use a mismatched EAP method would also generate an attempt record in Access Tracker.
Clients not configured to trust the root CA certificate for CPPM's RADIUS/EAP certificate might fail authentication, but the attempt would still be logged in Access Tracker.
What is one difference between EAP-Tunneled Layer Security (EAP-TLS) and Protected EAP (PEAP)?
EAP-TLS begins with the establishment of a TLS tunnel, but PEAP does not use a TLS tunnel as part of its process.
EAP-TLS requires the supplicant to authenticate with a certificate, but PEAP allows the supplicant to use a username and password.
EAP-TLS creates a TLS tunnel for transmitting user credentials, while PEAP authenticates the server and supplicant during a TLS handshake.
EAP-TLS creates a TLS tunnel for transmitting user credentials securely, while PEAP protects user credentials with TKIP encryption.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security) and PEAP (Protected EAP) are two EAP methods used for 802.1X authentication in wireless networks, such as those configured with WPA3-Enterprise on HPE Aruba Networking solutions. Both methods are commonly used with ClearPass Policy Manager (CPPM) for secure authentication.
EAP-TLS:
Requires both the supplicant (client) and the server (e.g., CPPM) to present a valid certificate during authentication.
Establishes a TLS tunnel to secure the authentication process, but the primary authentication mechanism is the mutual certificate exchange. The client’s certificate is used to authenticate the client, and the server’s certificate authenticates the server.
PEAP:
Requires only the server to present a certificate to authenticate itself to the client.
Establishes a TLS tunnel to secure the authentication process, within which the client authenticates using a secondary method, typically a username and password (e.g., via MS-CHAPv2 or EAP-GTC).
Option A, "EAP-TLS begins with the establishment of a TLS tunnel, but PEAP does not use a TLS tunnel as part of its process," is incorrect. Both EAP-TLS and PEAP establish a TLS tunnel. In EAP-TLS, the TLS tunnel is used for the mutual certificate exchange, while in PEAP, the TLS tunnel protects the inner authentication (e.g., username/password).
Option B, "EAP-TLS requires the supplicant to authenticate with a certificate, but PEAP allows the supplicant to use a username and password," is correct. This is a key difference: EAP-TLS mandates certificate-based authentication for the client, while PEAP allows the client to authenticate with a username and password inside the TLS tunnel, making PEAP more flexible for environments where client certificates are not deployed.
Option C, "EAP-TLS creates a TLS tunnel for transmitting user credentials, while PEAP authenticates the server and supplicant during a TLS handshake," is incorrect. Both methods use a TLS tunnel, and both authenticate the server during the TLS handshake (using the server’s certificate). In EAP-TLS, the client’s certificate is also part of the TLS handshake, while in PEAP, the client’s credentials (username/password) are sent inside the tunnel after the handshake.
Option D, "EAP-TLS creates a TLS tunnel for transmitting user credentials securely, while PEAP protects user credentials with TKIP encryption," is incorrect. PEAP does not use TKIP (Temporal Key Integrity Protocol) for protecting credentials; TKIP is a legacy encryption method used in WPA/WPA2 for wireless data encryption, not for EAP authentication. PEAP uses the TLS tunnel to protect the inner authentication credentials.
The HPE Aruba Networking ClearPass Policy Manager 6.11 User Guide states:
"EAP-TLS requires both the supplicant and the server to present a valid certificate for mutual authentication. The supplicant authenticates using its certificate, and the process is secured within a TLS tunnel. In contrast, PEAP requires only the server to present a certificate to establish a TLS tunnel, within which the supplicant can authenticate using a username and password (e.g., via MS-CHAPv2 or EAP-GTC). This makes PEAP more suitable for environments where client certificates are not deployed." (Page 292, EAP Methods Section)
Additionally, the HPE Aruba Networking Wireless Security Guide notes:
"A key difference between EAP-TLS and PEAP is the client authentication method. EAP-TLS mandates that the client authenticate with a certificate, requiring certificate deployment on all clients. PEAP allows the client to authenticate with a username and password inside a TLS tunnel, making it easier to deploy in environments without client certificates." (Page 40, 802.1X Authentication Methods Section)
What is a reason to set up a packet capture on an Aruba Mobility Controller (MC)?
The company wants to use ClearPass Policy Manager (CPPM) to profile devices and needs to receive HTTP User-Agent strings from the MC.
The security team believes that a wireless endpoint connected to the MC is launching an attack and wants to examine the traffic more closely.
You want the MC to analyze wireless clients' traffic at a lower level, so that the ArubaOS firewall can control the traffic I based on application.
You want the MC to analyze wireless clients' traffic at a lower level, so that the ArubaOS firewall can control Web traffic based on the destination URL.
Setting up a packet capture on an Aruba Mobility Controller (MC) is particularly useful in scenarios where detailed analysis of network traffic is necessary to identify and address security concerns. Option B is the correct answer because it directly addresses the need to closely examine the traffic of a potentially malicious wireless endpoint. Packet capture on the MC allows the security team to collect and analyze traffic to/from specific endpoints in real-time, providing valuable insights into the nature of the traffic and potentially identifying harmful activities. This capability is essential for forensics and troubleshooting security incidents, enabling administrators to respond effectively to threats.
Which correctly describes a way to deploy certificates to end-user devices?
ClearPass Onboard can help to deploy certificates to end-user devices, whether or not they are members of a Windows domain
ClearPass Device Insight can automatically discover end-user devices and deploy the proper certificates to them
ClearPass OnGuard can help to deploy certificates to end-user devices, whether or not they are members of a Windows domain
in a Windows domain, domain group policy objects (GPOs) can automatically install computer, but not user certificates
ClearPass Onboard is part of the Aruba ClearPass suite and it provides a mechanism to deploy certificates to end-user devices, regardless of whether or not they are members of a Windows domain. ClearPass Onboard facilitates the configuration and provisioning of network settings and security, including the delivery and installation of certificates to ensure secure network access. This capability enables a bring-your-own-device (BYOD) environment where devices can be securely managed and provided with the necessary certificates for network authentication.
What is one of the roles of the network access server (NAS) in the AAA framewonx?
It authenticates legitimate users and uses policies to determine which resources each user is allowed to access.
It negotiates with each user's device to determine which EAP method is used for authentication
It enforces access to network services and sends accounting information to the AAA server
It determines which resources authenticated users are allowed to access and monitors each users session
In the AAA (Authentication, Authorization, and Accounting) framework, the role of the Network Access Server (NAS) is to act as a gateway that enforces access to network services and sends accounting information to the AAA server. The NAS initially requests authentication information from the user and then passes that information to the AAA server. It also enforces the access policies as provided by the AAA server after authentication and provides accounting data to the AAA server based on user activity.
A user attempts to connect to an SSID configured on an AOS-8 mobility architecture with Mobility Controllers (MCs) and APs. The SSID enforces WPA3-Enterprise security and uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as the authentication server. The WLAN has initial role, logon, and 802.1X default role, guest.
A user attempts to connect to the SSID, and CPPM sends an Access-Accept with an Aruba-User-Role VSA of "contractor," which exists on the MC.
What does the MC do?
Applies the rules in the logon role, then guest role, and the contractor role
Applies the rules in the contractor role
Applies the rules in the contractor role and the logon role
Applies the rules in the contractor role and guest role
In an AOS-8 mobility architecture, the Mobility Controller (MC) manages user roles and policies for wireless clients connecting to SSIDs. When a user connects to an SSID with WPA3-Enterprise security, the MC uses 802.1X authentication to validate the user against an authentication server, in this case, HPE Aruba Networking ClearPass Policy Manager (CPPM). The SSID is configured with specific roles:
Initial role: Applied before authentication begins (not specified in the question, but typically used for pre-authentication access).
Logon role: Applied during the authentication process to allow access to authentication services (e.g., DNS, DHCP, or RADIUS traffic).
802.1X default role (guest): Applied if 802.1X authentication fails or if no specific role is assigned by the RADIUS server after successful authentication.
In this scenario, the user successfully authenticates, and CPPM sends an Access-Accept message with an Aruba-User-Role Vendor-Specific Attribute (VSA) set to "contractor." The "contractor" role exists on the MC, meaning it is a predefined role in the MC’s configuration.
When the MC receives the Aruba-User-Role VSA, it applies the specified role ("contractor") to the user session, overriding the default 802.1X role ("guest"). The MC does not combine the contractor role with other roles like logon or guest; it applies only the role specified by the RADIUS server (CPPM) in the Aruba-User-Role VSA. This is the standard behavior in AOS-8 for role assignment after successful authentication when a VSA specifies a role.
Option A, "Applies the rules in the logon role, then guest role, and the contractor role," is incorrect because the MC does not apply multiple roles in sequence. The logon role is used only during authentication, and the guest role (default 802.1X role) is overridden by the contractor role specified in the VSA.
Option C, "Applies the rules in the contractor role and the logon role," is incorrect because the logon role is no longer applied once authentication is complete; only the contractor role is applied.
Option D, "Applies the rules in the contractor role and guest role," is incorrect because the guest role (default 802.1X role) is not applied when a specific role is assigned via the Aruba-User-Role VSA.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
"When a user authenticates successfully via 802.1X, the Mobility Controller applies the role specified in the Aruba-User-Role VSA returned by the RADIUS server in the Access-Accept message. If the role specified in the VSA exists on the controller, it is applied to the user session, overriding any default 802.1X role configured for the WLAN. The controller does not combine the VSA-specified role with other roles, such as the initial, logon, or default roles." (Page 305, Role Assignment Section)
Additionally, the HPE Aruba Networking ClearPass Policy Manager 6.11 User Guide notes:
"ClearPass can send the Aruba-User-Role VSA in a RADIUS Access-Accept message to assign a specific role to the user on Aruba Mobility Controllers. The role specified in the VSA takes precedence over any default roles configured on the WLAN, ensuring that the user is placed in the intended role." (Page 289, RADIUS Enforcement Section)

TESTED 11 May 2026
Copyright © 2014-2026 DumpsTool. All Rights Reserved
