A FortiMail administrator is investigating a sudden increase in DSNs being delivered to their protected domain. After searching the logs, the administrator identifies that the DSNs werenotgenerated because of any outbound email sent from their organization.
Which FortiMail antispam technique can the administrator use to prevent this scenario?
A FortiMail is configured with the protected domain example.com.
On this FortiMail, which two envelope addresses are considered incoming? (Choose two.)
A FortiMail administrator is concerned about cyber criminals attempting to get sensitive information from employees using whaling phishing attacks. What option can the administrator configure to prevent these types of attacks?
Refer to the exhibit which displays a topology diagram.
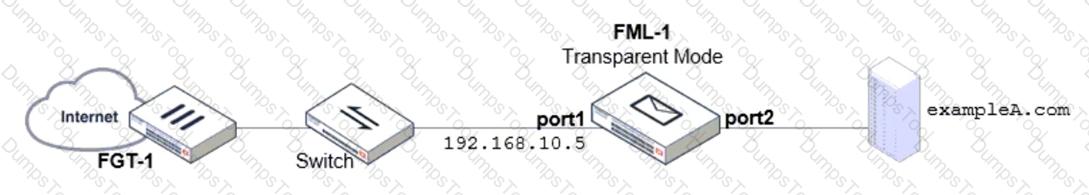
Which two statements describe the built-in bridge functionality on a transparent mode FortiMail? (Choose two.)
Refer to the exhibits, which display a topology diagram (Topology) and two FortiMail device configurations (FML1 ConfigurationandFML2 Configuration).
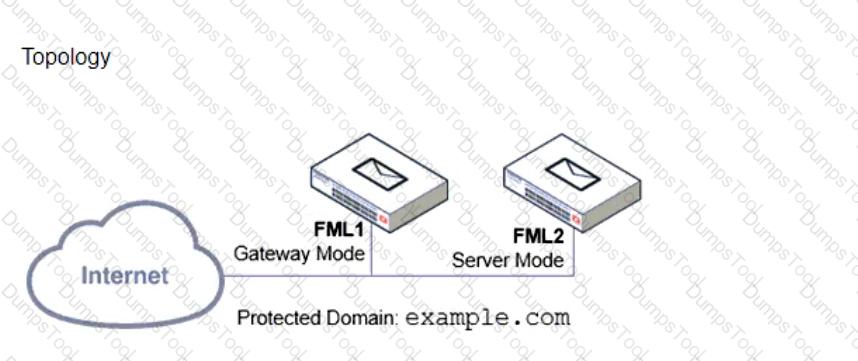
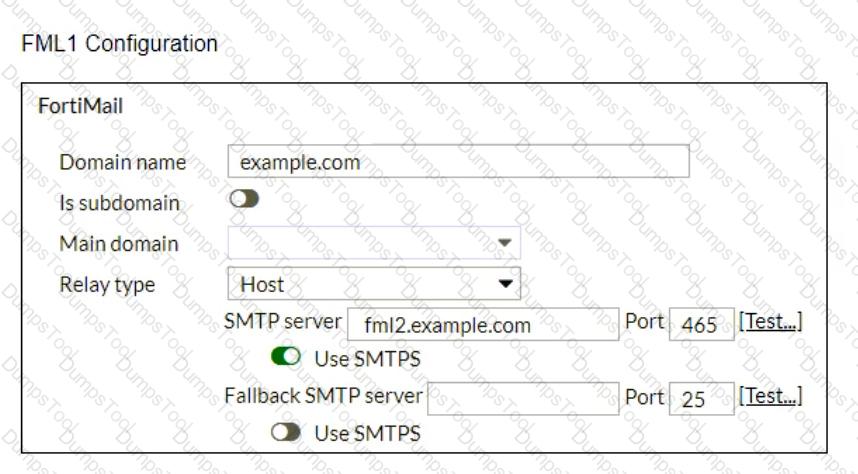
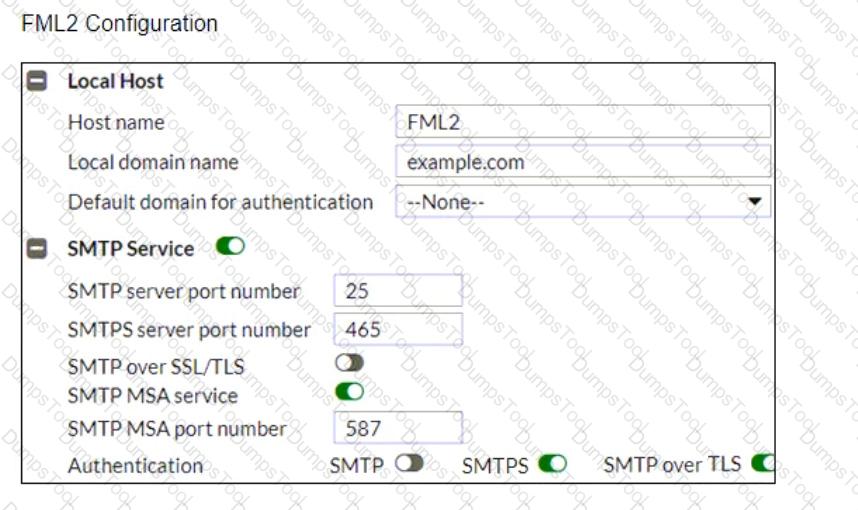
What is the expected outcome of SMTP sessions sourced from FML1 and destined for FML2?
Refer to the exhibit, which shows the Authentication Reputation list on a FortiMail device running in gateway mode.
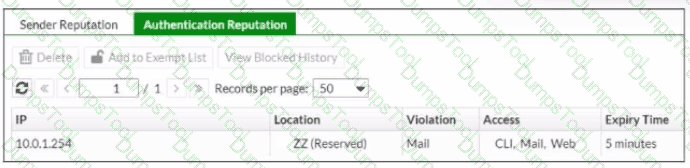
Why was the IP address blocked?
Refer to the exhibit, which displays a history log entry.
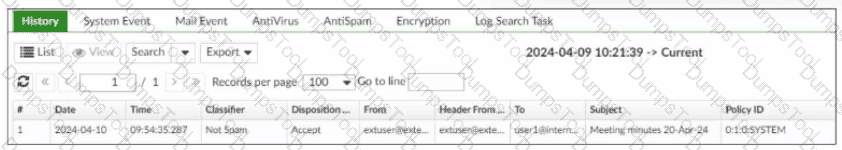
In the Policy ID column, why isthe last policy ID value SYSTEM?
Exhibit.
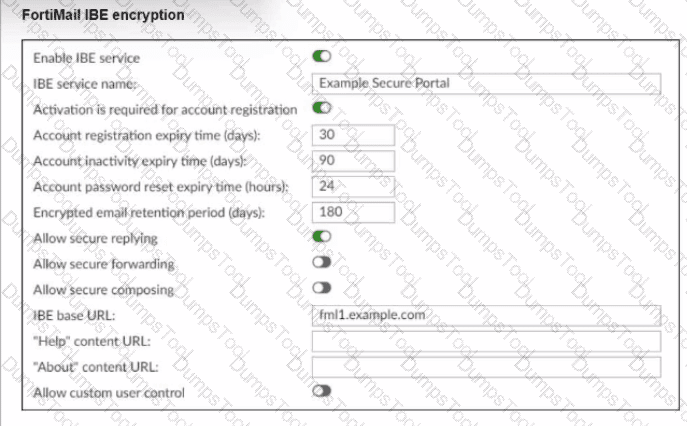
Reter to the exhibit, which shows the IBE Encryption page of a FortiMail device. Which user account behavior can you expect from these IBE settings?
In which two ways does a transparent mode FortiMail use the build-it MTA to process email? (Choose two.)
Refer to the exhibit which shows annslookupoutput of MX records of theexample.comdomain.
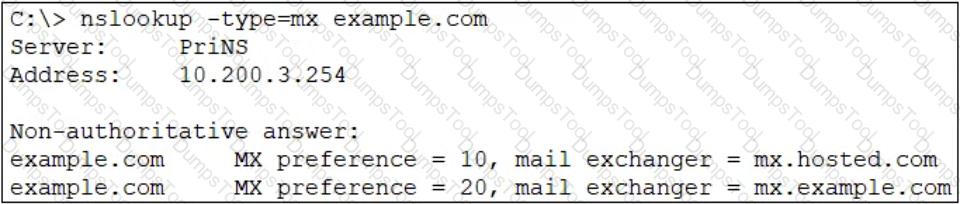
Which two MTA selection behaviors for theexample.comdomain are correct? (Choose two.)