Which of the following is a reason multiple password changes on the same day are not allowed?
A Linux administrator tries to install Ansible in a Linux environment. One of the steps is to change the owner and the group of the directory /opt/Ansible and its contents. Which of the following commands will accomplish this task?
A Linux administrator attempts to unmount the local filesystem /data in order to mount a new volume. However, the administrator receives the following error message:
umount: /data: target is busy
Which of the following commands should the administrator run to resolve the issue?
A Linux server is experiencing slowness. A systems administrator obtains the following output:
top - load average: 2.43, 1.80, 2.32
Tasks: ... 154 zombie
%Cpu(s): 6.2 us, 5.1 sy, 0.0 ni, 79.2 id, 9.1 wa, ...
$ iostat -m 2
%user %nice %system %iowait %steal %idle
4.30 2.02 0.29 70.38 4.00 19.01
Which of the following explains the issue?
Which of the following commands would a Linux administrator use to determine the temperature of a motherboard?
A systems administrator needs to check access to all company servers. The administrator uses the following script, which does not complete:
for i in $(cat /home/user1.file)
do
echo $i
ssh $i uptime
Which of the following is missing from the script?
Application owners are reporting that their application stops responding after several days of running, and they need to restart it. A Linux administrator obtains the following details from the dmesg command:
invoked oom-killer
Call Trace:
out_of_memory
oom_kill_process
The application owners mentioned that resources to the system have been increased, and the error takes longer to appear. Which of the following best describes the reason the process is being terminated by OOM?
A systems administrator needs to restore a backup to the /usr/app/data directory. Which of the following commands should the administrator use for this task?
A Linux administrator needs to create and then connect to the app-01-image container. Which of the following commands accomplishes this task?
Which of the following is a protocol for accessing distributed directory services containing a hierarchy of users, groups, machines, and organizational units?
A systems administrator needs to integrate a new storage array into the company ' s existing storage pool. The administrator wants to ensure that the server is able to detect the new storage array. Which of the following commands should the administrator use to ensure that the new storage array is presented to the systems?
On a Kubernetes cluster, which of the following resources should be created in order to expose a port so it is publicly accessible on the internet?
A Linux administrator updates the DNS record for the company using:
cat /etc/bind/db.abc.com
The revised partial zone file is as follows:
ns1 IN A 192.168.40.251
ns2 IN A 192.168.40.252
www IN A 192.168.30.30
When the administrator attempts to resolve www.abc.com to its IP address, the domain name still points to its old IP mapping:
nslookup www.abc.com
Server: 192.168.40.251
Address: 192.168.40.251#53
Non-authoritative answer:
Name: www.abc.com
Address: 199.168.20.81
Which of the following should the administrator execute to retrieve the updated IP mapping?
A systems administrator needs to enable routing of IP packets between network interfaces. Which of the following kernel parameters should the administrator change?
Which of the following is the first step when starting a new Python project on a Linux system?
A systems administrator needs to set the IP address of a new DNS server. Which of the following files should the administrator modify to complete this task?
A Linux user needs to authenticate to a Windows Active Directory domain. Which of the following configuration files contains the domain configuration details?
Which of the following cryptographic functions ensures a hard drive is encrypted when not in use?
A Linux systems administrator needs to extract the contents of a file named /home/dev/web.bkp to the /var/www/html/ directory. Which of the following commands should the administrator use?
An administrator needs to remove the directory /home/user1/data and all of its contents. Which of the following commands should the administrator use?
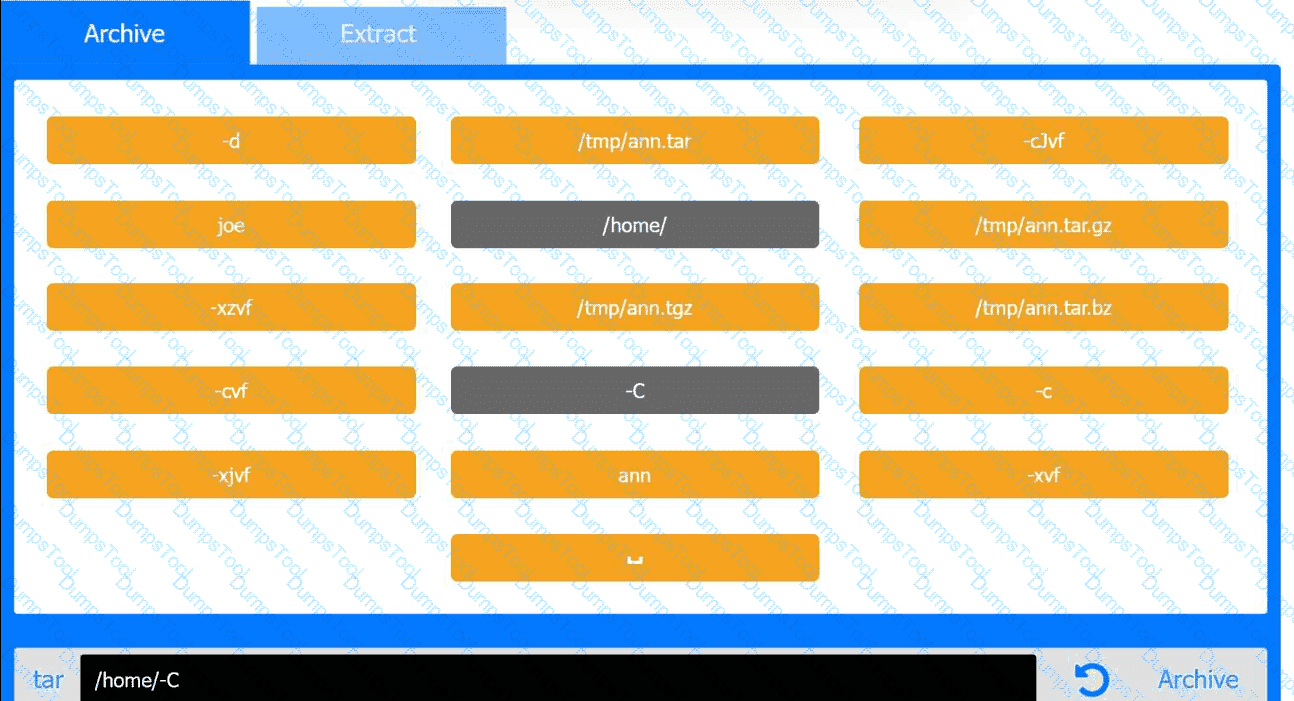
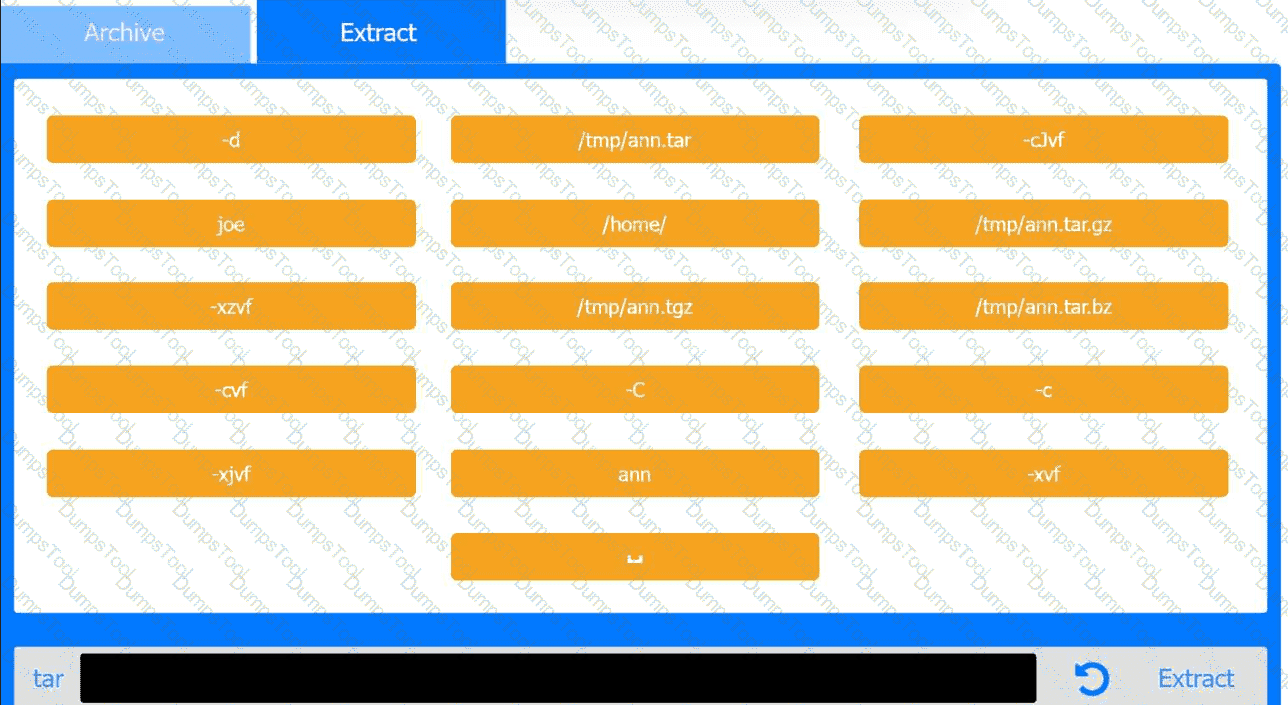
Joe, a user, has taken a position previously held by Ann. As a systems administrator, you
need to archive all the files from Ann ' s home directory and extract them into Joe ' s home
directory.
INSTRUCTIONS
Within each tab, click on an object to form the appropriate commands. Command objects may only be used once, but the spacebar _ object may be used multiple times. Not all objects will be used.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A systems administrator manages multiple Linux servers and needs to set up a reliable and secure way to handle the complexity of managing event records on the OS and application levels. Which of the following should the administrator do?
To perform a live migration, which of the following must match on both host servers? (Choose two)
An administrator wants to see all logs for the app.service systemd process. Which of the following commands should the administrator use to complete this task?
A Linux administrator just finished setting up passwordless SSH authentication between two nodes. However, upon test validation, the remote host prompts for a password. Given the following logs:
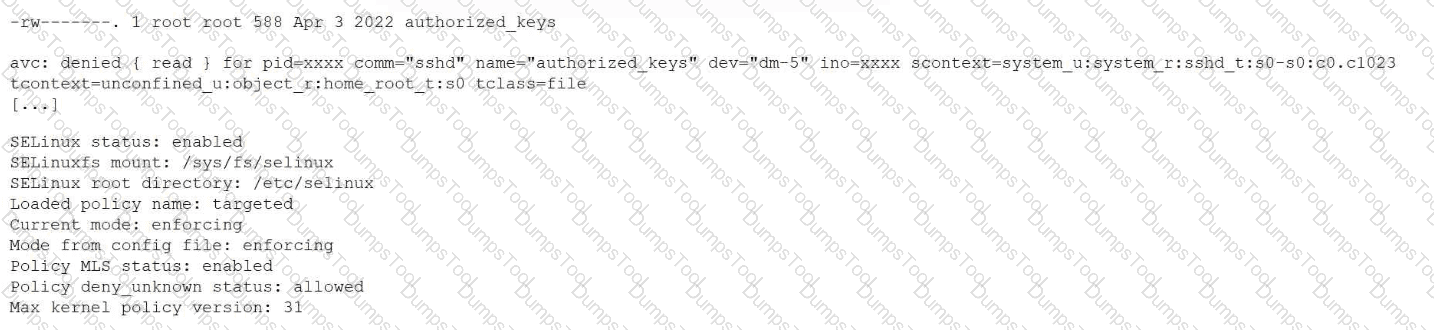
Which of the following is the most likely cause of the issue?
A systems administrator wants to update and apply changes in an existing file in a remote Git repository. Which of the following is the last Git command the administrator should execute to complete this process?
An administrator is investigating the reason a Linux workstation is not resolving the website http://www.comptia.org. The administrator executes some commands and receives the following output:
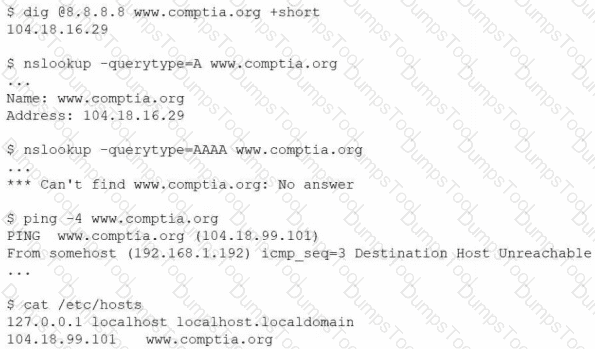
Which of the following is the most likely cause?
A systems administrator is decommissioning a service. Which of the following commands should the administrator use to make sure users cannot start the service again?
In the echo " profile-$num-$name " line of a shell script, the variable $num seems to not be expanding during execution. Which of the following notations ensures the value is expanded?
A Linux user runs the following command:
nohup ping comptia.com &
Which of the following commands should the user execute to attach the process to the current terminal?
A Linux administrator needs to securely erase the contents of a hard disk. Which of the following commands is the best for this task?
A user states that an NFS share Is reporting random disconnections. The systems administrator obtains the following information
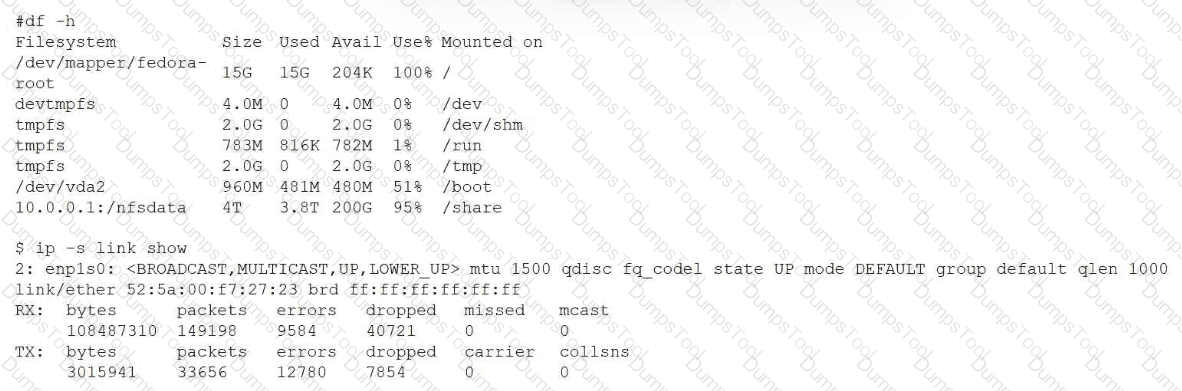
Which of the following best explains the symptoms that are being reported?
A user reports recurrent issues with an application, which is currently operational. The systems administrator gathers the following outputs to diagnose the issue:
Out of memory: Kill process (mariadb)
Killed process (mariadb)
mariadb invoked oom-killer
egrep ' Out of memory ' /var/log/messages
Multiple entries showing mariadb being killed by OOM killer
free -m
Mem: total 15819, used 10026, free 5174, available 5134
Swap: 0 0 0
sar -r
kbmemused ~67%, no swap usage
Which of the following is a possible cause of this issue?
Which of the following describes the method of consolidating system events to a single location?