An administrator is investigating a technical outage. The management team wants information that includes the summary of the outage and actions taken. Which of the following documentation should the administrator provide?
An employee receives a message urging them to scan an image with their company-owned smartphone that will access the account management portal in order to reset their password. Which of the following describes this type of social engineering attack?
A technician is deploying a public-facing kiosk that will be used for a library directory. Which of the following account types should the IT team activate?
A project team needs special access on a shared repository to add new content, edit existing content, and prevent content deletion. Which of the following should an administrator do to configure this setup with the least amount of effort?
An administrator received an email stating that the OS they are currently supporting will no longer be issued security updates and patches. Which of the following is most likely the reason the administrator received this message?
A technician is working on a complex, large-scale software deployment. In which of the following places would the technician most likely reference deployment instructions?
A user requires a temporary computer to perform duties. Which of the following is a way to leave minimal user data on the computer?
A support specialist must apply a new application update to an entire organization. Which of the following is the first step in this process?
A company ' s IT department discovers that unauthorized software has been installed on several workstations. The IT manager requests a review and an update of the workstation security posture, focusing on preventing future unauthorized software installations. Which of the following should the company do?
Which of the following authentication methods is the best way to prevent users from frequently entering their credentials?
An organization is experiencing an increased number of issues. A technician notices applications that are not installed by default. Users are reporting an increased number of system prompts for software licensing. Which of the following would the security team most likely do to remediate the root cause?
A user reports that their corporate mobile phone is lost. Which of the following protects the data locally on the phone from unauthorized access?
A customer’s computer does not have an active connection to the network. A technician goes through a few troubleshooting steps but is unable to resolve the issue. The technician has exhausted their knowledge. The customer expresses frustration at the time taken to resolve this issue. Which of the following should the technician do?
A Windows 11 Home device is receiving constant pop-ups about an urgent need to update antivirus software in order to remove a detected threat. The user has been clicking the " X " button but the window keeps reappearing. The pop-up includes an " OK " button to install the update. What should the user do next?
A technician needs to map a shared drive from a command-line interface. Which of the following commands should the technician use?
An end user ' s laptop is having network drive connectivity issues in the office. The end user submits a help desk ticket, and a support technician is able to establish a remote connection and fix the issue. The following day, however, the network drive is disconnected again. Which of the following should the technician do next?
A user frequently misplaces their Windows laptop and is concerned about it being stolen. The user would like additional security controls on their laptop. Which of the following is a built-in technology that a technician can use to enable full drive encryption?
A utility failure causes a workstation to immediately shut down. Which of the following would help prevent this from reoccurring?
A user wants to dispose of a failed hard drive in a way that ensures the data is unrecoverable. Which of the following is the best at-home method?
A company wants to perform an in-place upgrade of operating systems on all workstations. All types of removable storage are disabled for security reasons. Which of the following is the best way to upgrade while keeping security settings in place?
A technician is troubleshooting the reason that an application is down. The technician verifies that a service that was running has unexpectedly stopped. The technician tries to manually start the service, but it fails to start. Which of the following is the cause of this issue?
A technician is setting up a computer for a new user. A requirement is that the user ' s documents are stored on a network location and not locally on the computer. Which of the following should the technician configure?
A technician must map a network drive on a piece of legacy equipment running an end-of-life OS. Which of the following is the best script to map the drive using simple Windows commands?
A vendor normally releases security patches for its operating system on a monthly basis. An administrator receives an email from the vendor that says the vendor has published a patch for a zero-day flaw in its operating system outside of the normal patch schedule. Which of the following actions should the administrator take first in order to properly address this issue in a production environment?
What is found in an MSDS (Material Safety Data Sheet) for a battery backup?
A company recently transitioned to a cloud-based productivity suite and wants to secure the environment from external threat actors. Which of the following is the most effective method?
A company wants to use a single operating system for its workstations and servers and avoid licensing fees. Which of the following operating systems would the company most likely select?
A user needs to install and uninstall software on their Windows laptop but does not need to manage user accounts. The company follows least-privilege principles. Which of the following account types meets these requirements?
A user receives a new personal computer but is unable to run an application. An error displays saying that .NET Framework 3.5 is required and not found. Which of the following actions is the best way to resolve this issue?
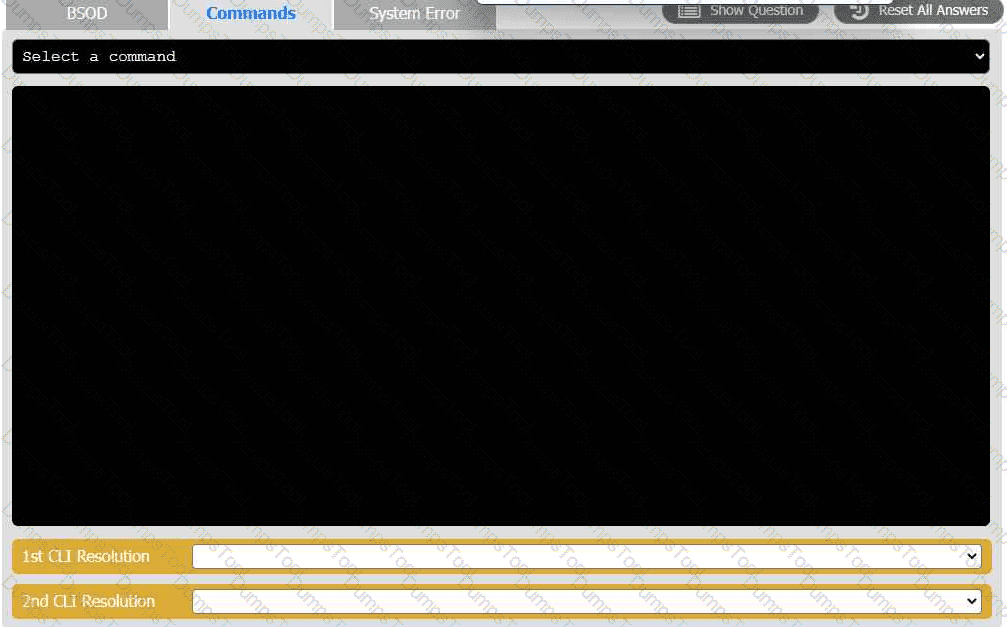
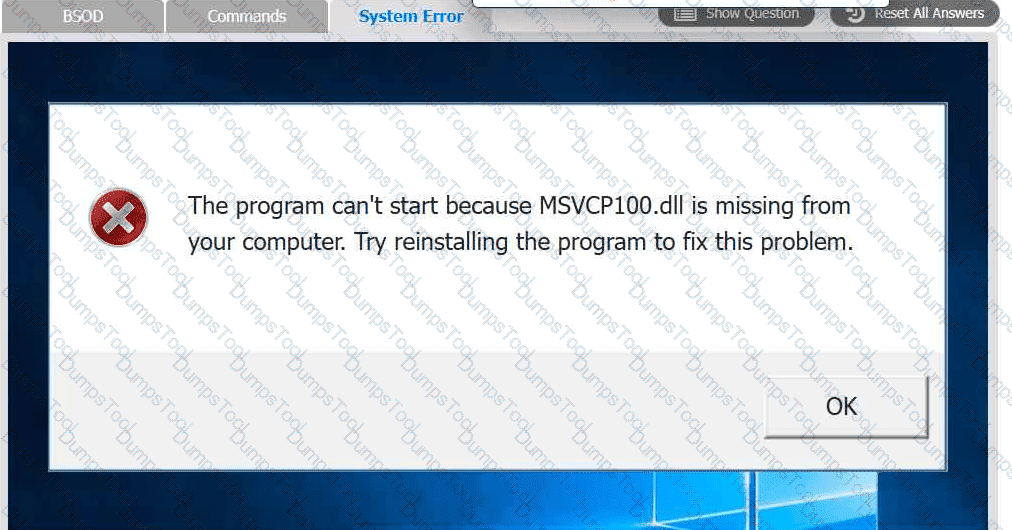
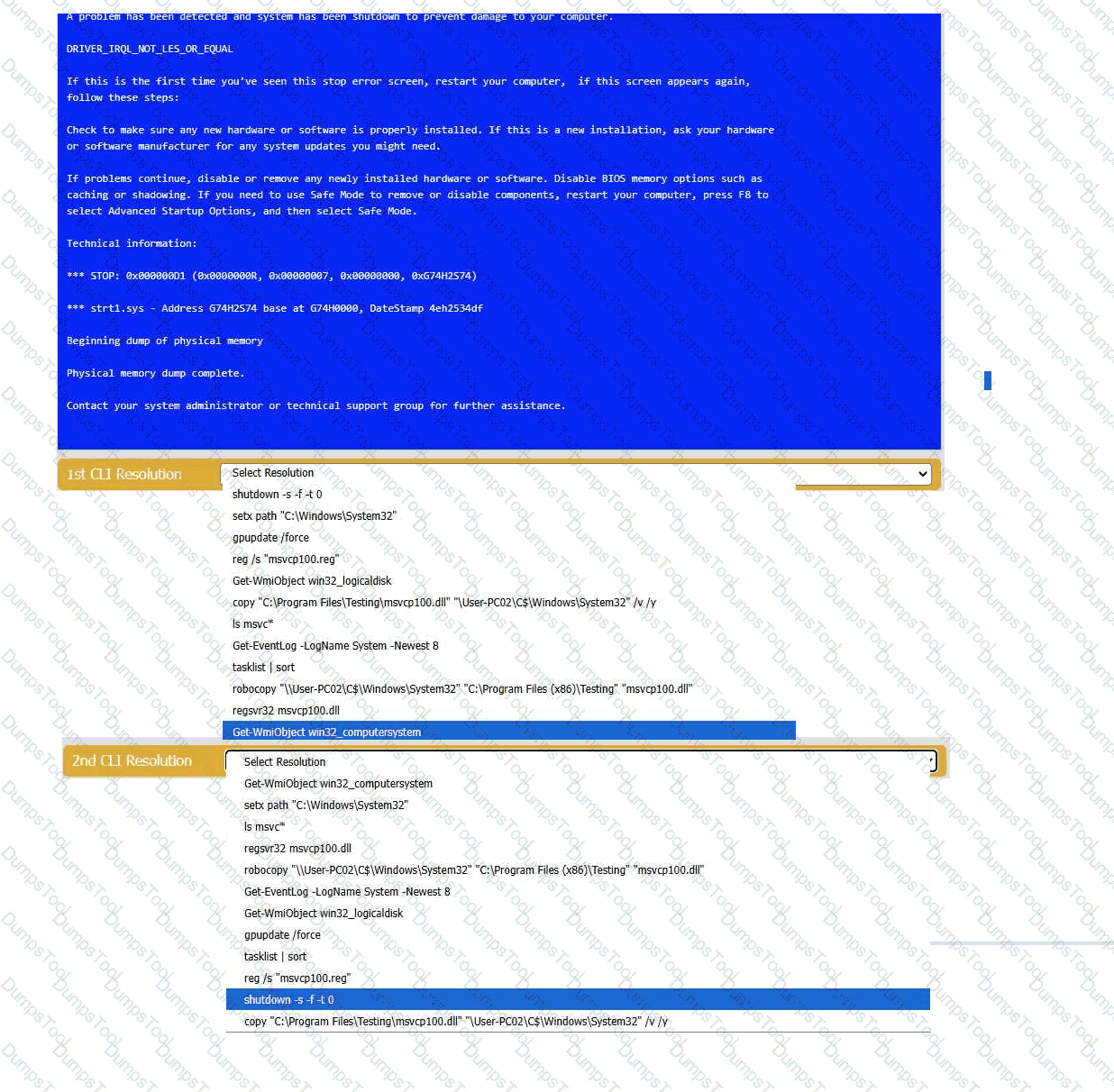
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
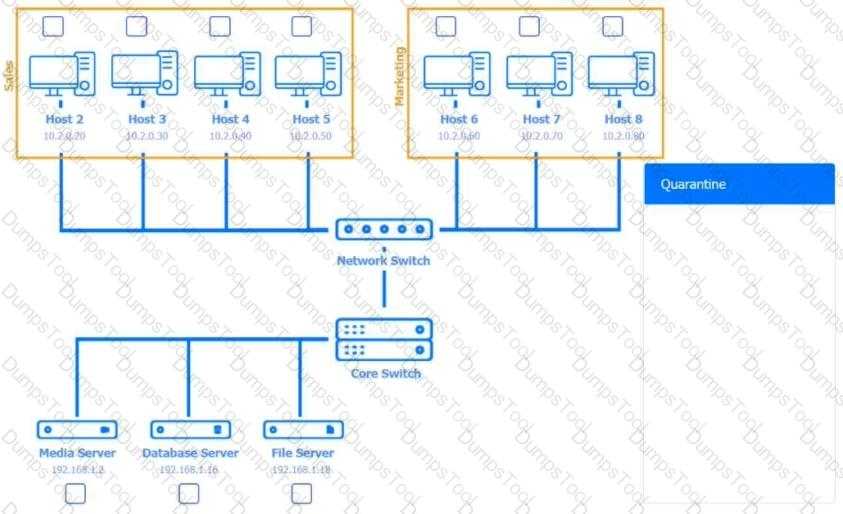
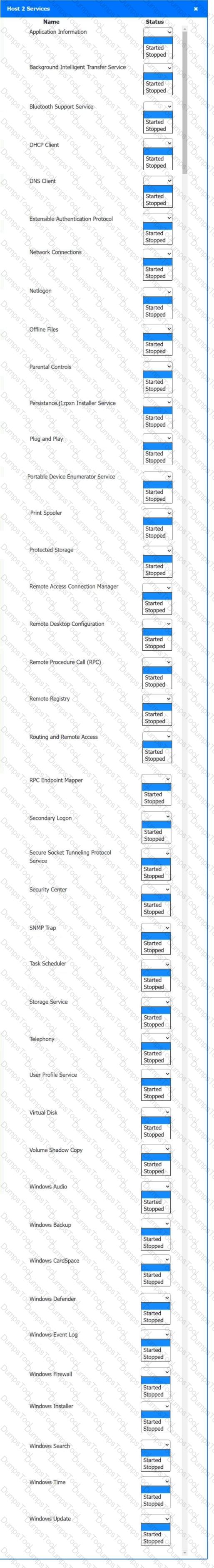
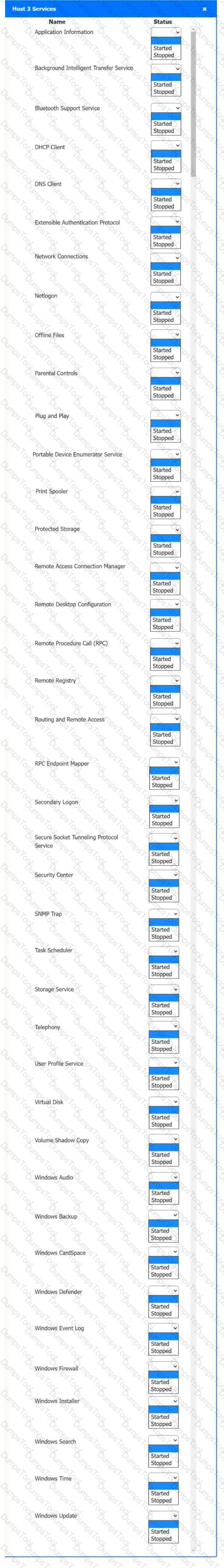
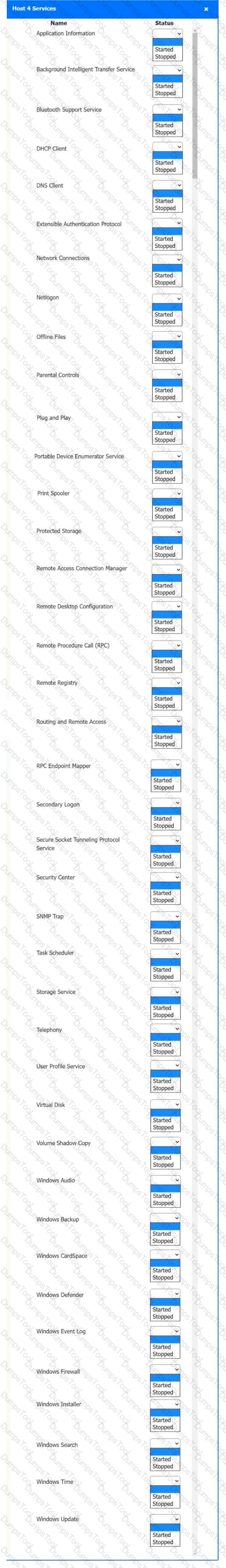
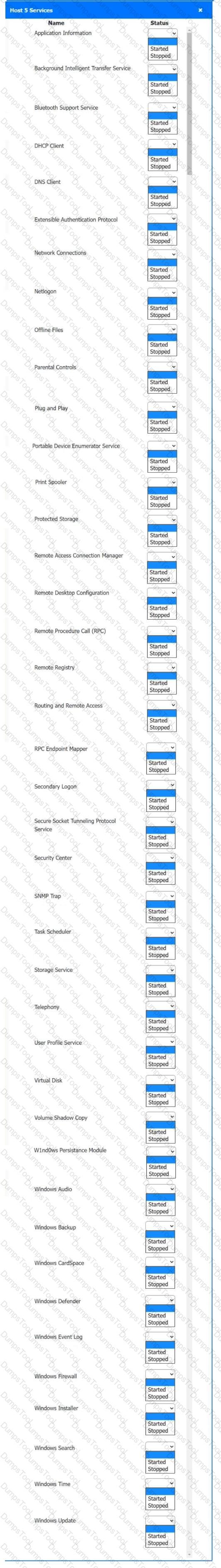
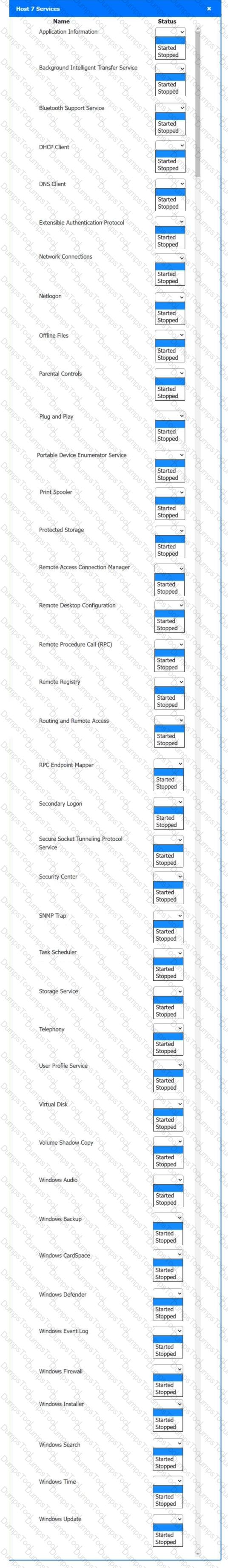
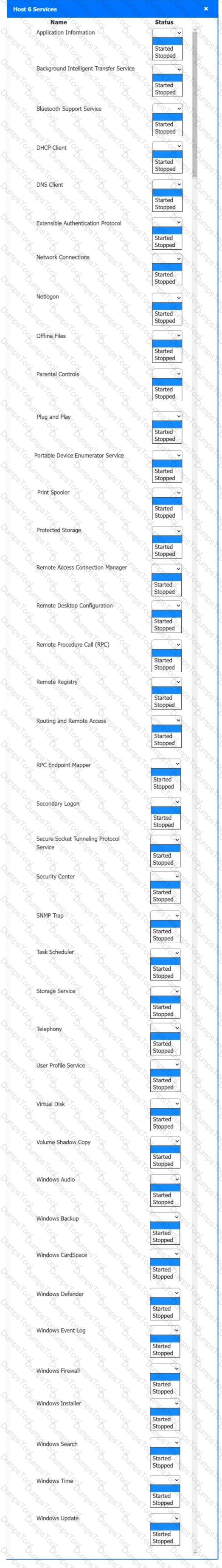
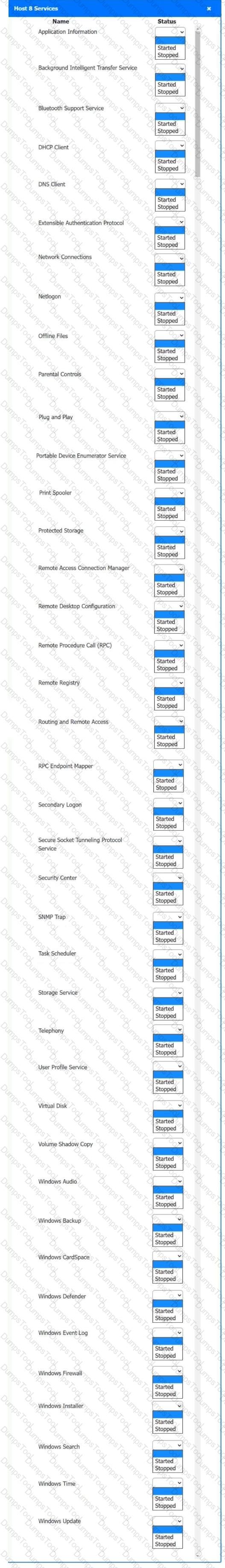
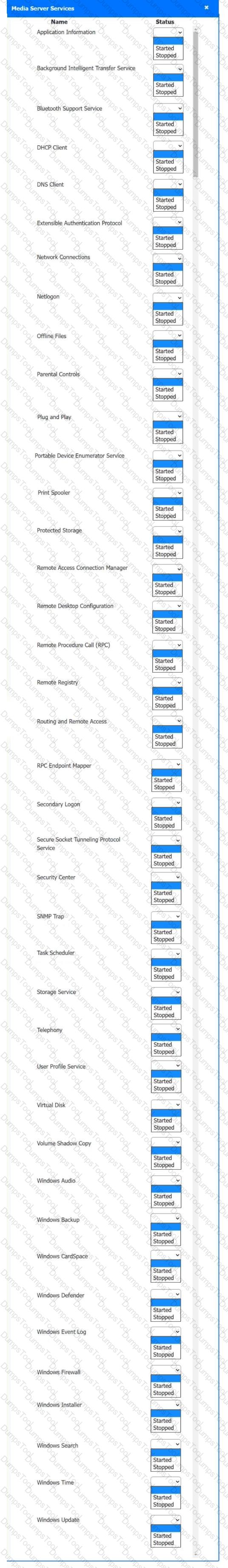
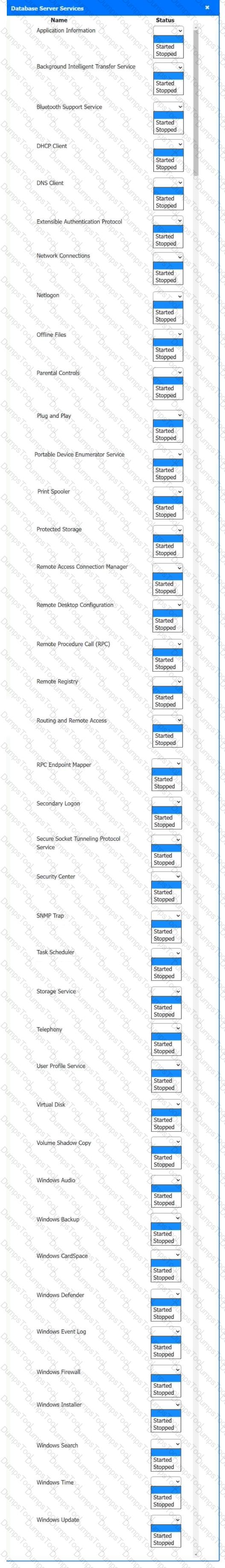
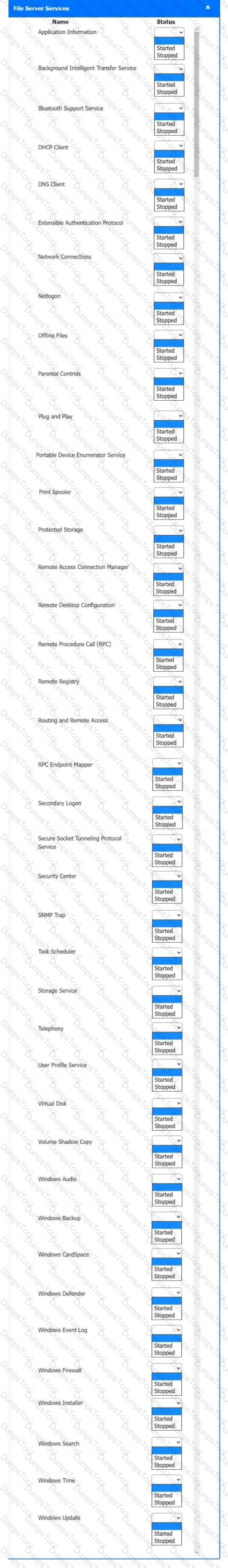
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
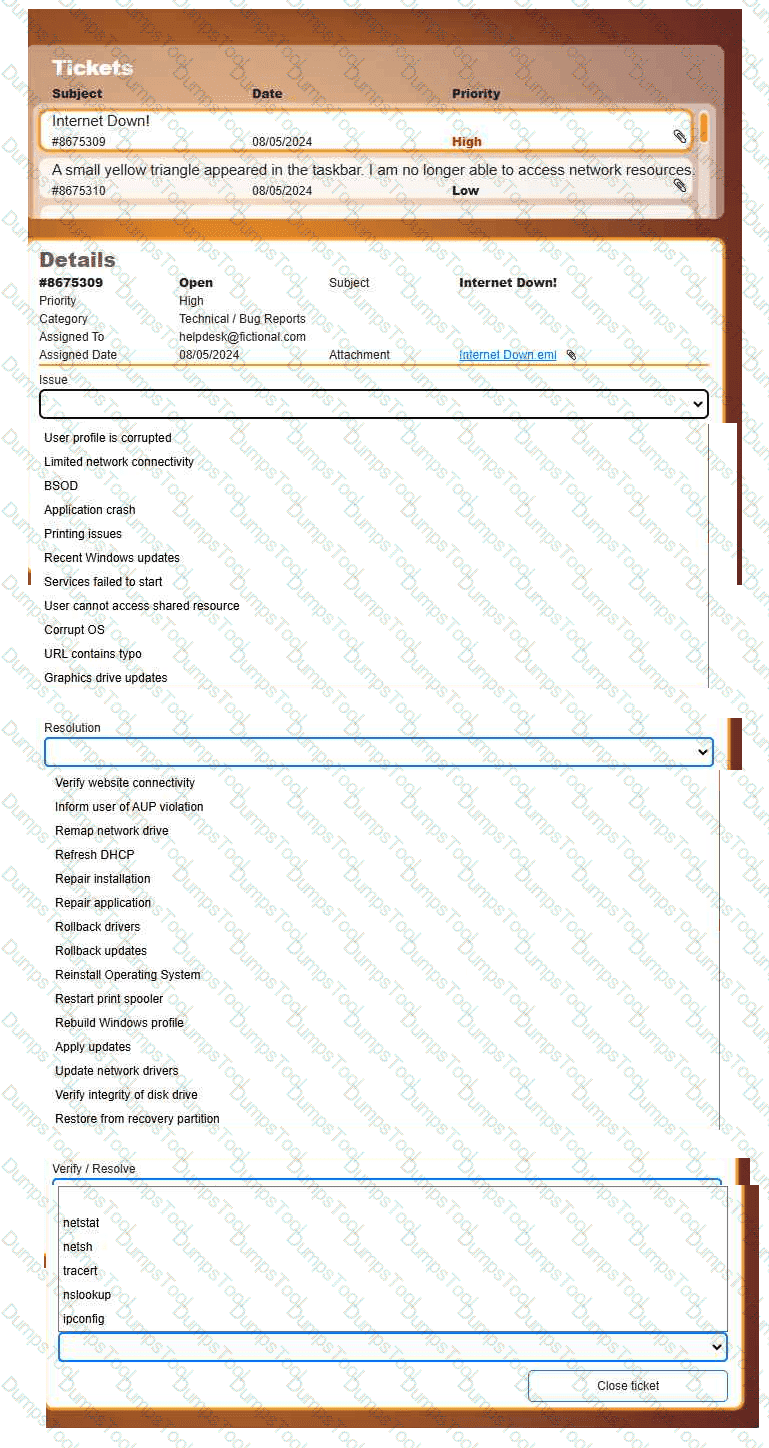
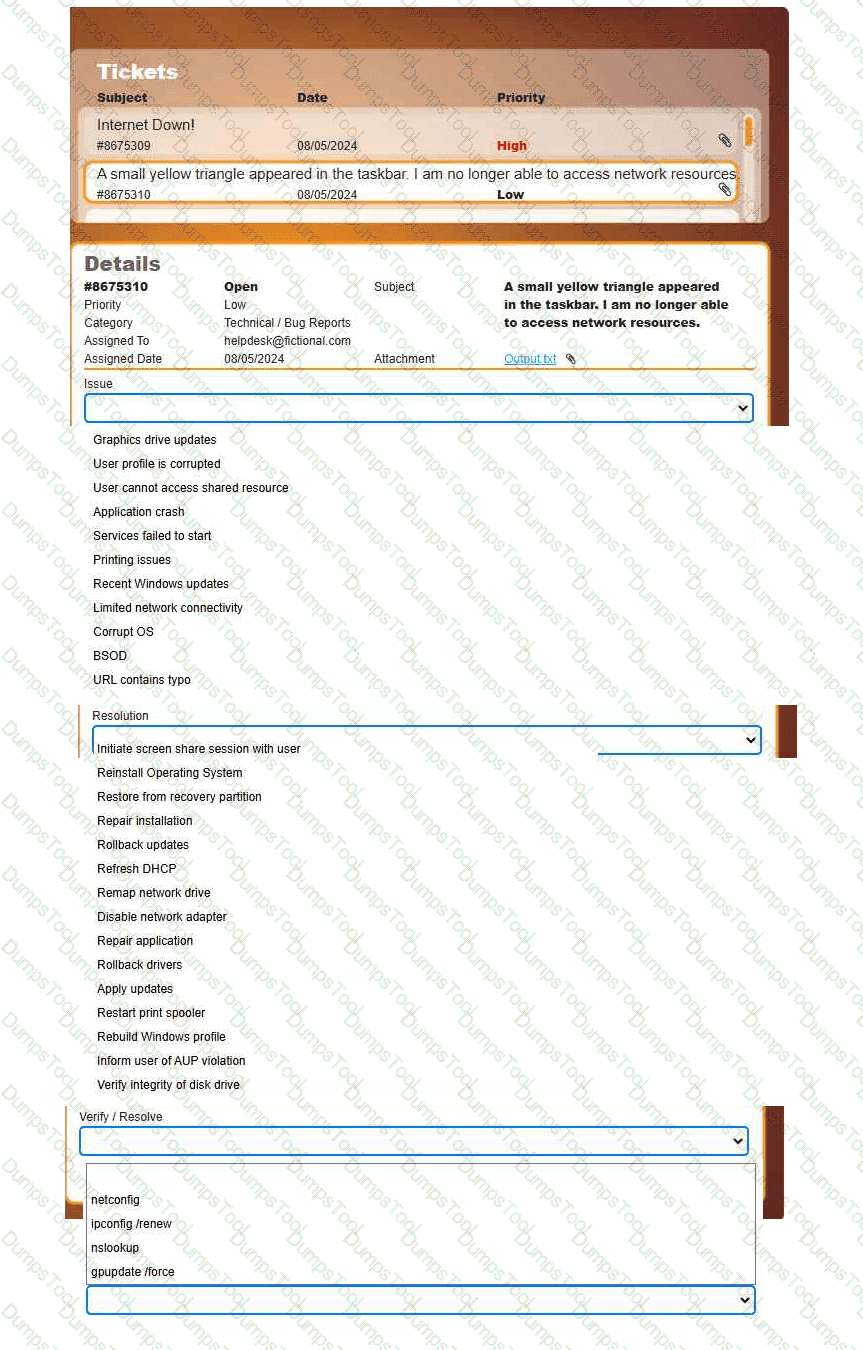
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
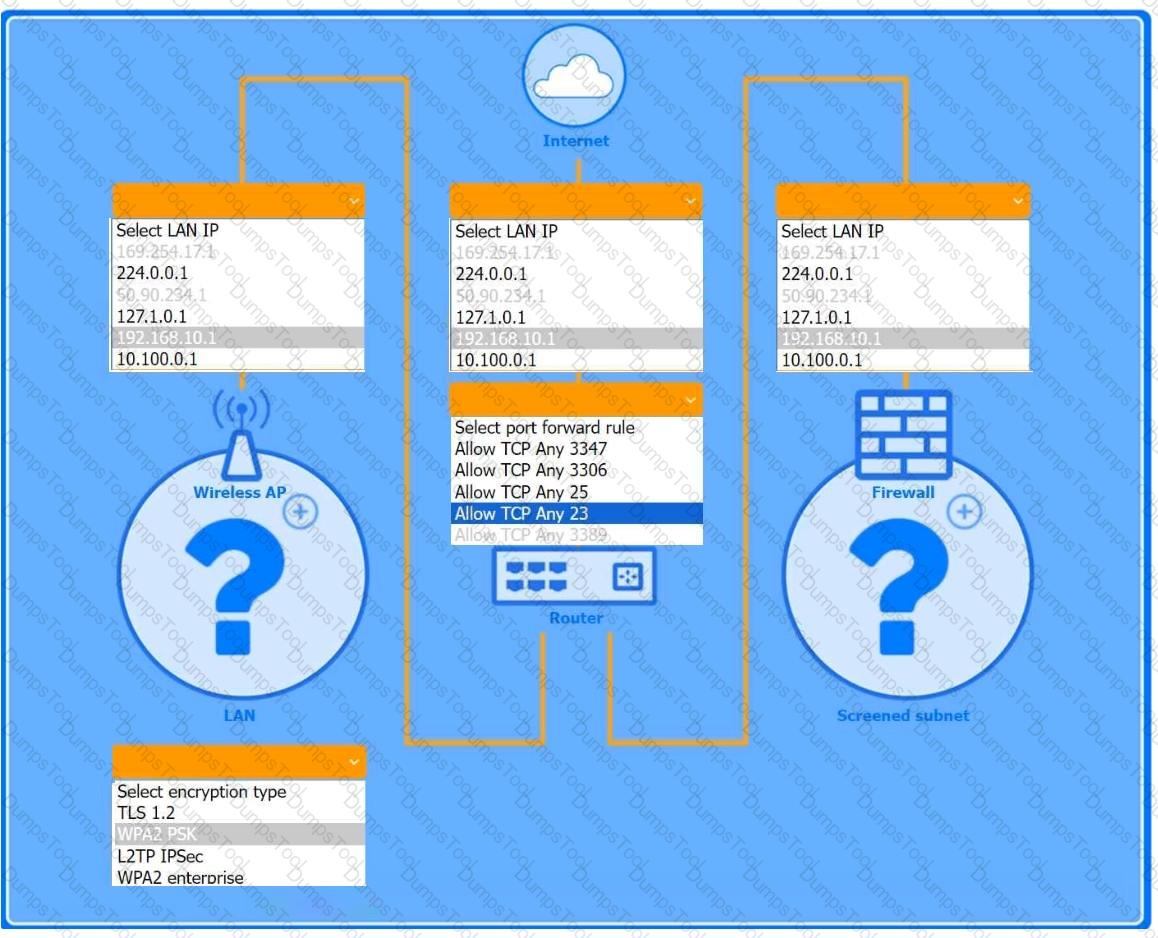
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
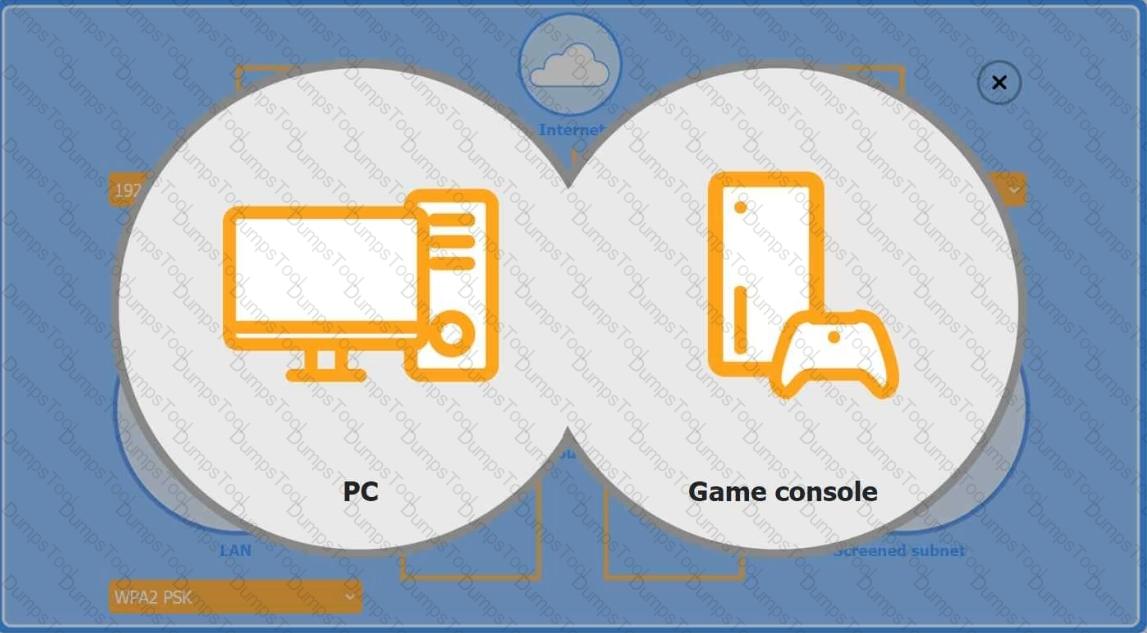
Firewall Screened Subnet
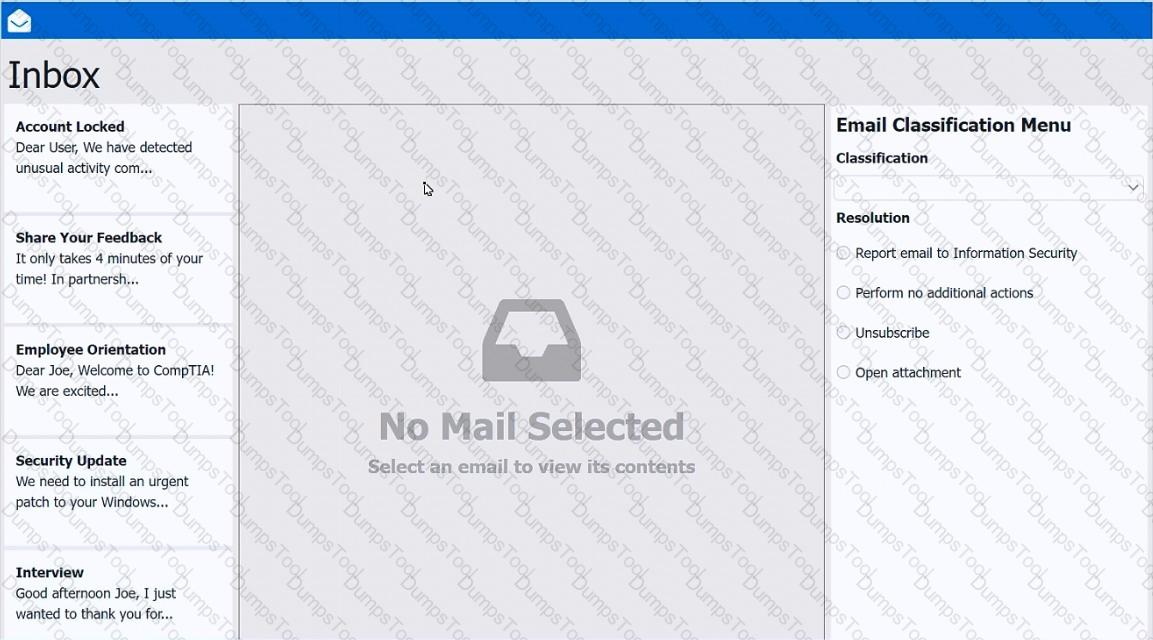
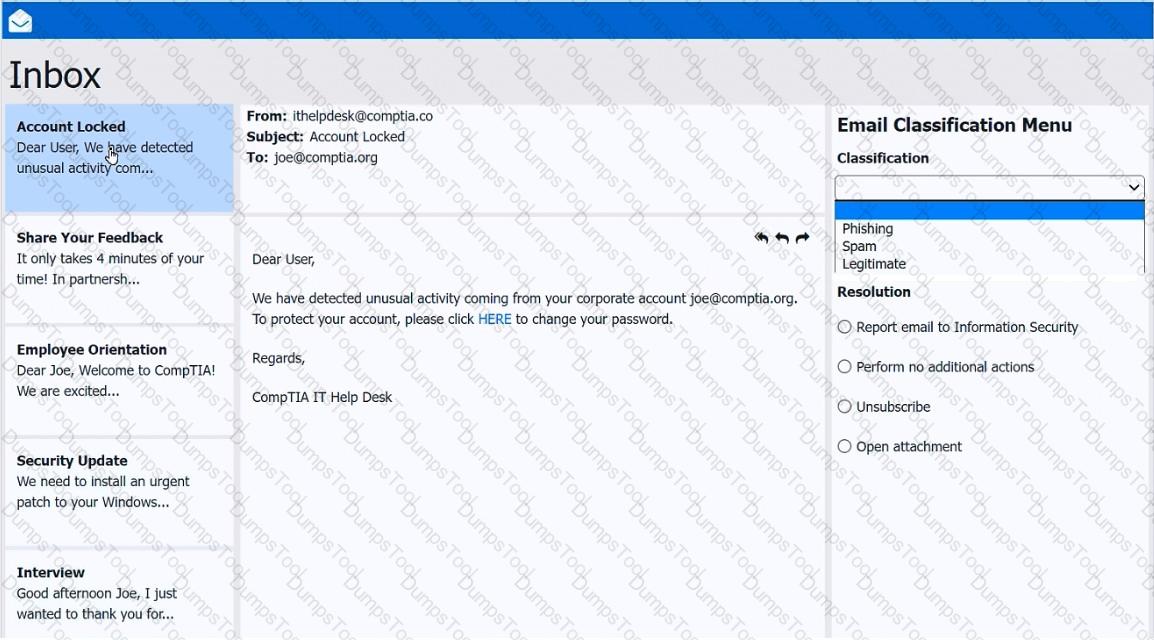
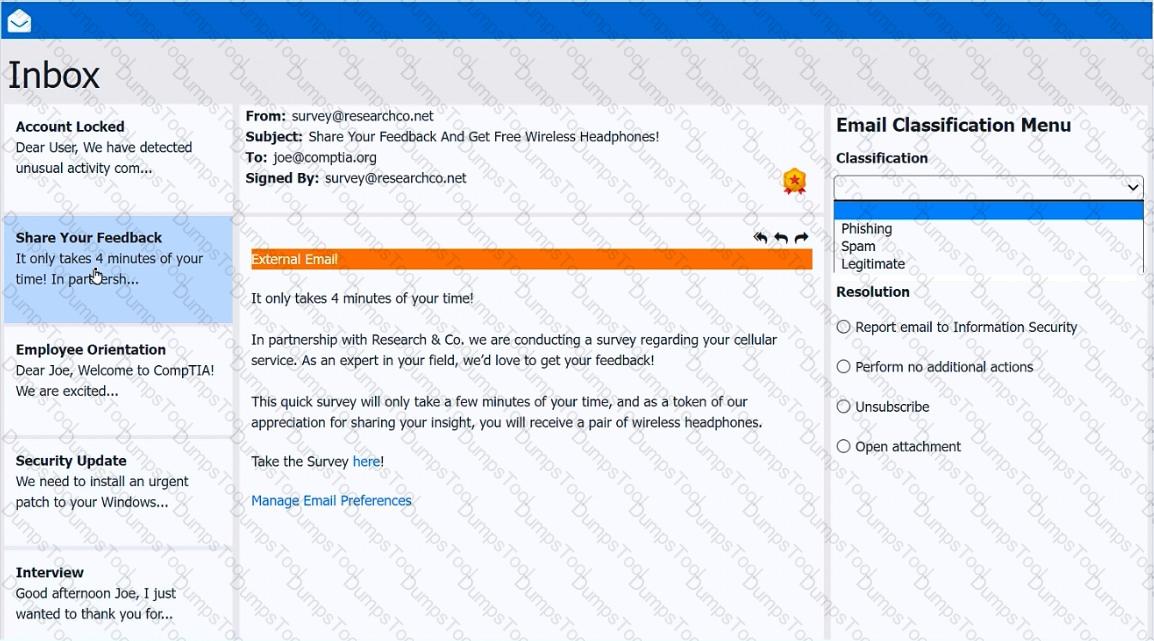
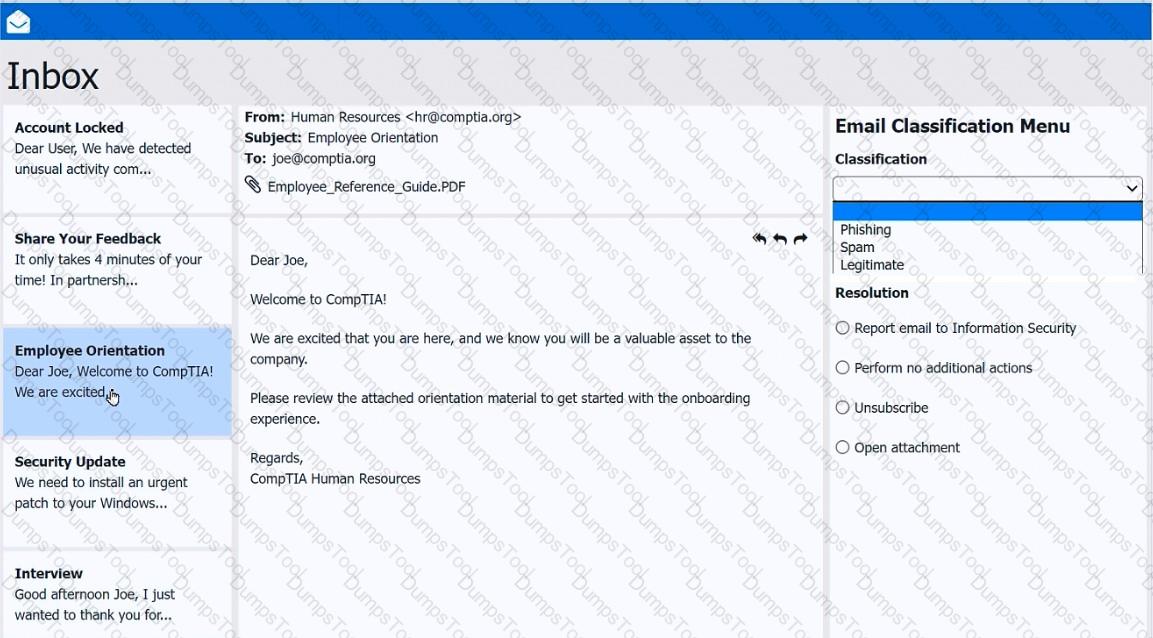
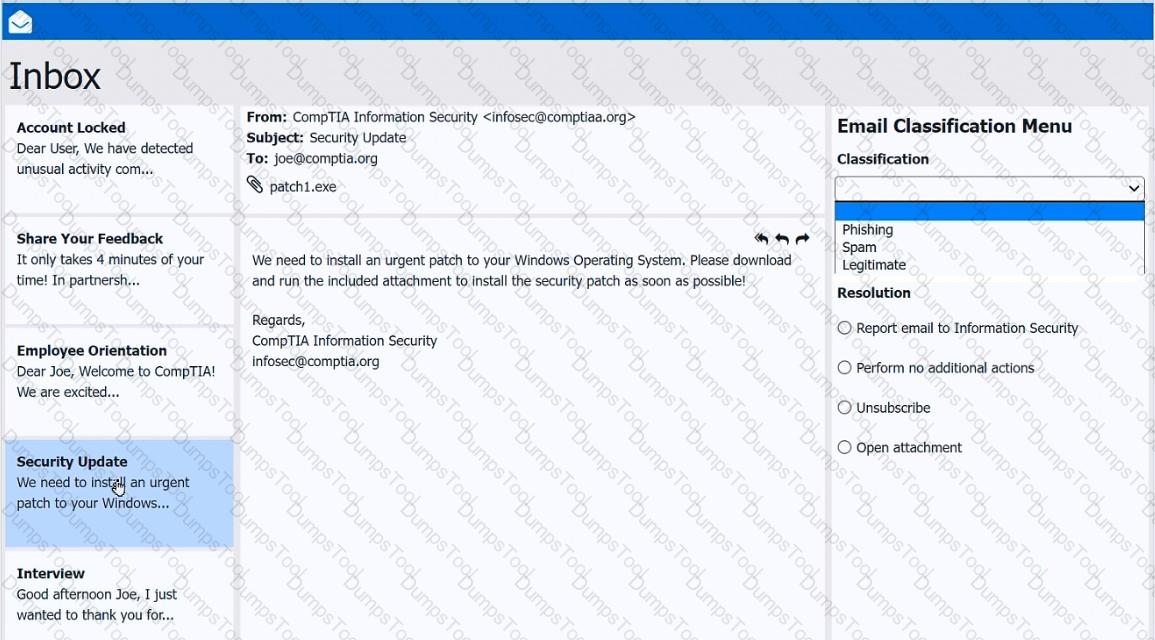
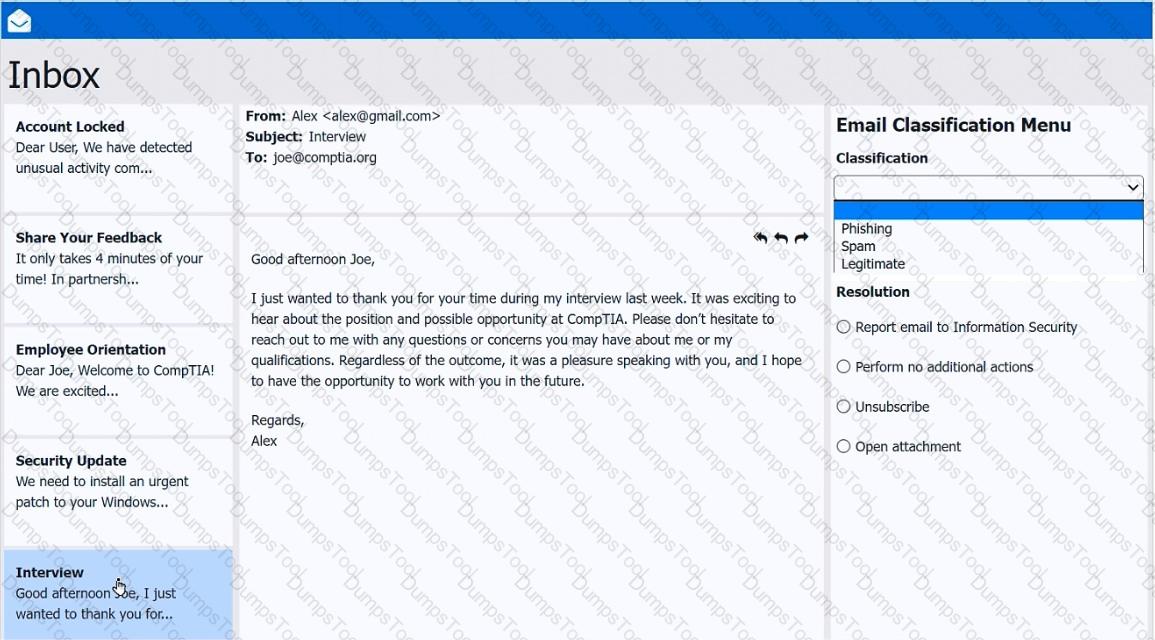
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
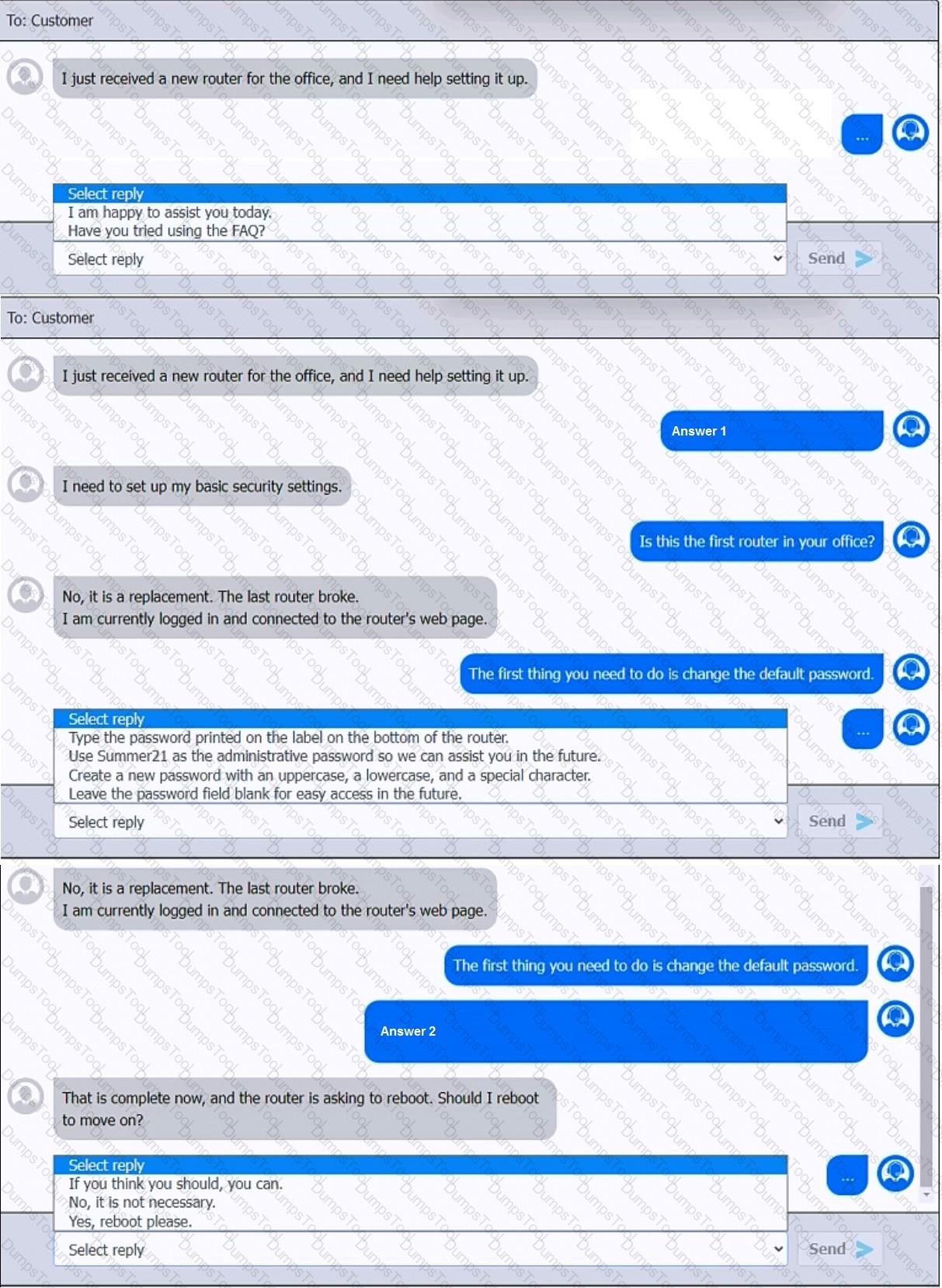
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A Windows 11 Home device is receiving constant pop-ups about an urgent need to update antivirus software to remove a detected threat. The user has been clicking the " X " button in the window frame but it always reappears. The pop-up includes an " OK " button to install the update and remove the threat. Which of the following should the user do next?
When a corporate laptop is connected to the company network, it can reach external websites. However, it cannot reach any internal websites, displaying the error message “Cannot reach this page.” Which of the following should a technician configure?
A new software installation requires administrative privileges for deployment. Which of the following is the best way to provide the necessary permissions to install the software?
Which of the following Linux commands is used to read another command ' s documentation?