Which two Cisco ESA features are used to control email delivery based on the sender? (Choose two.)
An engineer must configure Directory Harvest Attack Prevention for SMTP in Cisco Secure Email Gateway. This error message must be sent when the listener receives more than 50 invalid
recipients per hour.
•500 - Too many requests
•Max. Invalid Recipients Per Hour was set to 50 already.
Which two actions must be taken next to set maximum invalid recipients per hour to meet the requirement? (Choose two.)
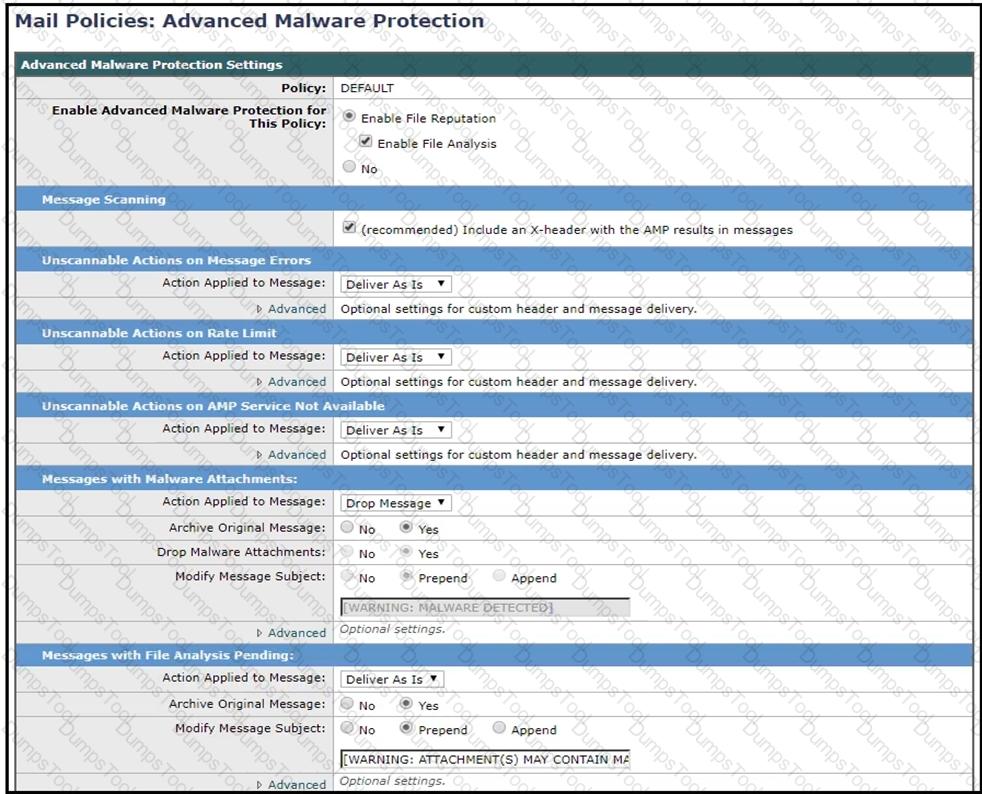
Refer to the exhibit. How should this configuration be modified to stop delivering Zero Day malware attacks?
Refer to the exhibit.
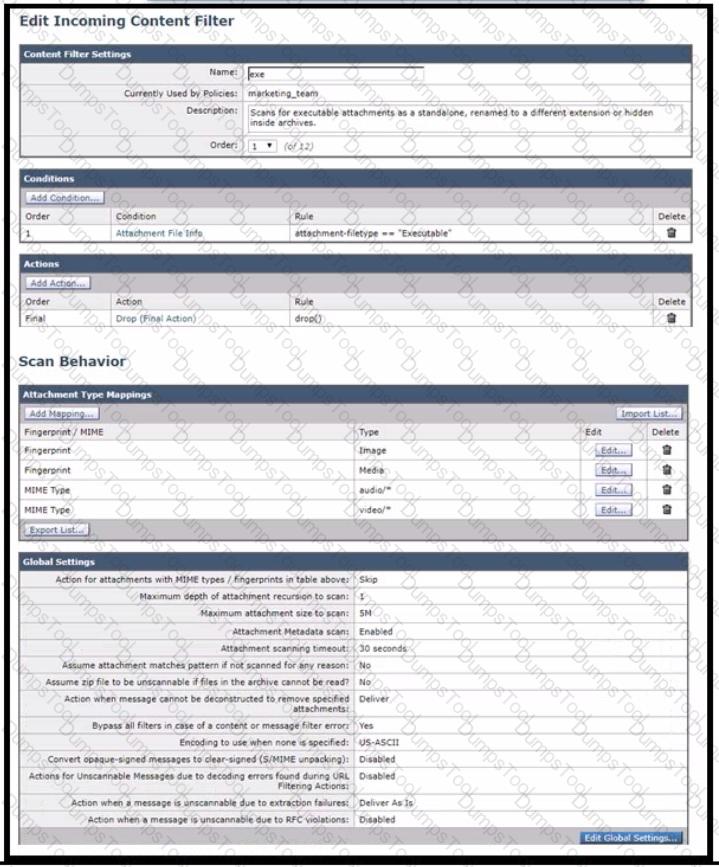
Which configuration allows the Cisco Secure Email Gateway to scan for executables inside the archive file and apply the action as per the content filter?
An engineer must configure incoming message verification using DM ARC in Cisco Secure Email Gateway. Emails from VP@cisco.com must skip the verification Drag and drop the actions from the left into the sequence on the right to meet the requirement.

Users have been complaining of a higher volume of emails containing profanity. The network administrator will need to leverage dictionaries and create specific conditions to reduce the number of inappropriate emails.
Which two filters should be configured to a ddress this? (Choose two.)
An engineer is configuring a Cisco Secure Email Gateway and needs to reject email messages to a recipient with email address user0516585210@acme.com . Which list contains the allowed recipient addresses?
An engineer wants to ensure that emails received by company users that contain URLs do not make them susceptible to data loss from accessing malicious or undesired external content sources Which two features must be configured on Cisco Secure Email Gateway to meet this requirement1? (Choose two.)
An administrator notices that incoming emails with certain attachments do not get delivered to all recipients when the emails have multiple recipients in different domains like cisco.com and test.com. The same emails when sent only to recipients in cisco.com are delivered properly. How must the Cisco Secure Email Gateway be configured to avoid this behavior?
An engineer must modify the altsrchost table on a Cisco Secure Email Gateway Messages destined for a domain named @cisco.com must be mapped to Newlnterface with an IP address of 10.10.10.1. What must be added to the table?
What is needed to sign outbound emails using Domain Keys Identified Mail after a signing profile is created in the Cisco Secure Email Gateway?
A company has deployed a new mandate that requires all emails sent externally from the Sales Department to be scanned by DLP for PCI-DSS compliance. A new DLP policy has been created on the Cisco ESA and needs to be assigned to a mail policy named ‘Sales’ that has yet to be create d.
Which mail policy should be created to accomplish this task?
An engineer must share threat reporting information from Cisco Secure Email Gateway to Cisco SecureX. Which setting must be enabled in Secure Email Gateway?
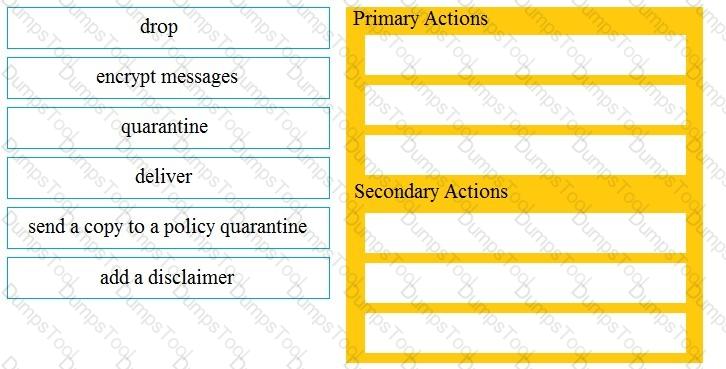
Drag and drop the Cisco ESA reactions to a possible DLP from the left onto the correct action types on the right.
Which feature utilizes sensor information obtained from Talos intelligence to filter email servers connecting into the Cisco ESA?
When outbreak filters are configured, which two actions are used to protect users from outbreaks? (Choose two.)
An organization wants to prevent proprietary patent documents from being shared externally via email. The network administrator reviewed the DLP policies on the Cisco Secure Email Gateway and could not find an existing policy with the appropriate matching patterns. Which type of DLP policy template must be used to create a policy that meets this requirement?
An engineer must configure a mail policy for all incoming email that contains a Microsoft Excel attachment. All such email must be quarantined without any exception. After the incoming mail policy is created, which action must be taken next to meet the requirement?
A Cisco Secure Email Gateway administrator is creating a Mail Flow Policy to receive outbound email from Microsoft Exchange. Which Connection Behavior must be selected to properly process the messages?
Which two certificate authority lists are available in Cisco ESA? (Choose two.)
Which Cisco Secure Email Threat Defense visibility and remediation mode is only available when using Cisco Secure Email Gateway as the message source?
When an email is sent with bounce verification enabled, which address is rewritten by the Cisco Secure Email Gateway in the message?
What is the default port to deliver emails from the Cisco ESA to the Cisco SMA using the centralized Spam Quarantine?
When the Cisco ESA is configured to perform antivirus scanning, what is the default timeout value?
Which of the following two statements are correct about the large file attachments (greater than 25MB) feature in Cisco Secure Email Encryption Service? (Choose two.)
An email administrator must configure DLP policies on the Cisco Secure Email Gateway. The DLP policies must be added to the default outgoing mail policy. How is this task accomplished?
To comply with a recent audit, an engineer must configure anti-virus message handling options on the incoming mail policies to attach warnings to the subject of an email.
What should be configured to meet this requirement for known viral emails?
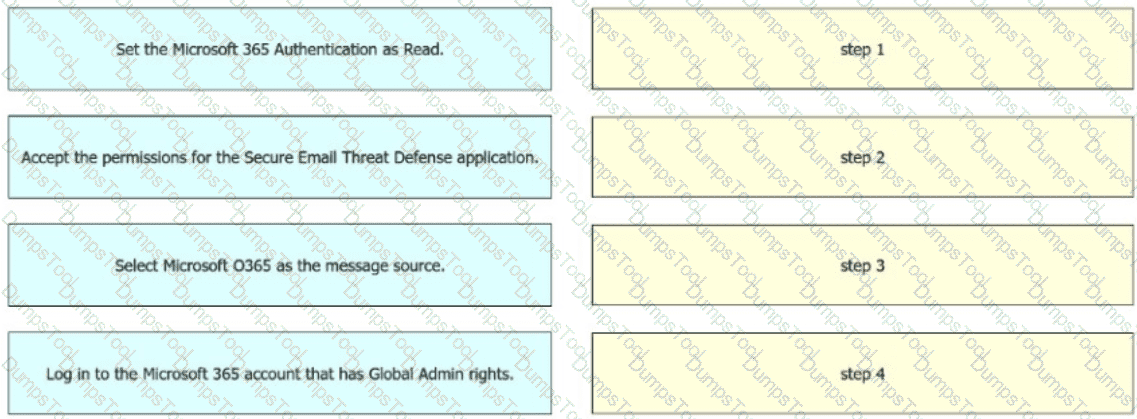
An engineer must configure the message source when integrating Cisco Secure Email Threat Defense with Microsoft 365. The integration must allow visibility but not remediation. Drag and drop the actions from the left into sequence on the right to meet the requirement.
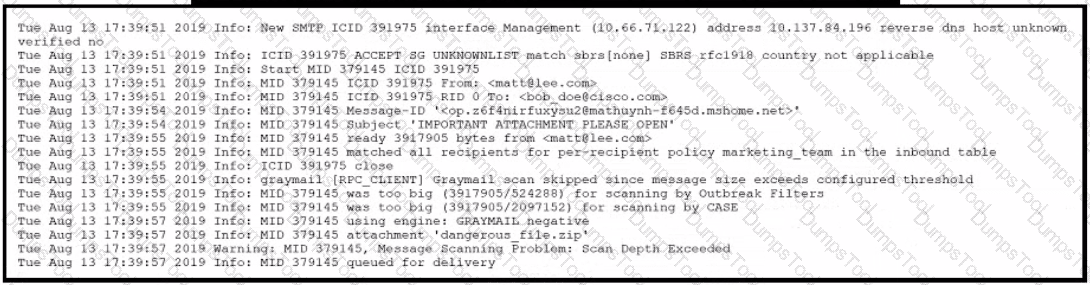
Refer to the exhibit.
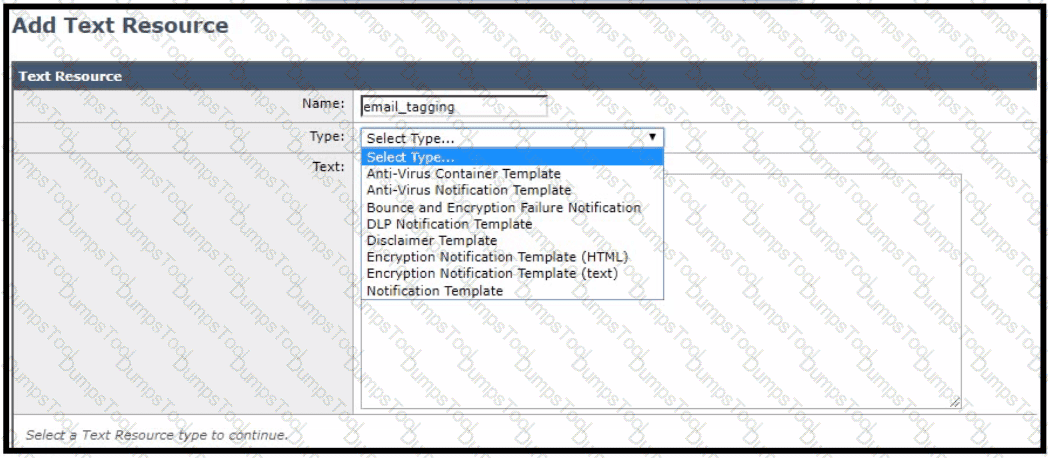
For improved security, an administrator wants to warn users about opening any links or attachments within an email How must the administrator configure an HTML-coded message at the top of an email body to create this warning?
Which two factors must be considered when message filter processing is configured? (Choose two.)
A Cisco ESA administrator has several mail policies configured. While testing policy match using a specific sender, the email was not matching the expected policy.
What is the reason of this?
Which Cisco ESA security service is configured only through an outgoing mail policy?
Spreadsheets containing credit card numbers are being allowed to bypass the Cisco ESA.
Which outgoing mail policy feature should be configured to catch this content before it leaves the network?
Which of the following two steps are required to enable Cisco SecureX integration on a Cisco Secure Email Gateway appliance? (Choose two.)
Which feature must be configured before an administrator can use the outbreak filter for nonviral threats?
When URL logging is configured on a Cisco ESA, which feature must be enabled first?
What is the default method of remotely accessing a newly deployed Cisco Secure Email Virtual Gateway when a DHCP server is not available?
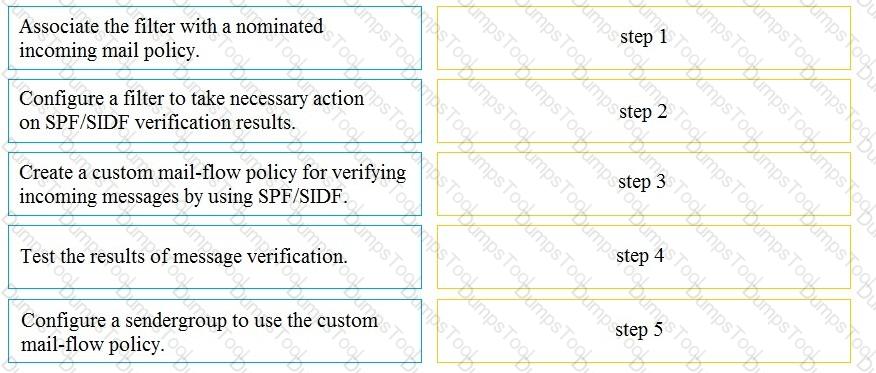
Drag and drop the steps to configure Cisco ESA to use SPF/SIDF verification from the left into the correct order on the right.
Which two features of Cisco Email Security are added to a Sender Group to protect an organization against email threats? (Choose two.)
An engineer must add the user1@cisco.co m with an IP address of 10.1.1.13 to a safelist in Cisco Secure Email Gateway. Which two safelist syntaxes must be configured to meet the requirement? (Choose two.)
Which scenario prevents a message from being sent to the quarantine as an action in the scan behavior on Cisco ESA?
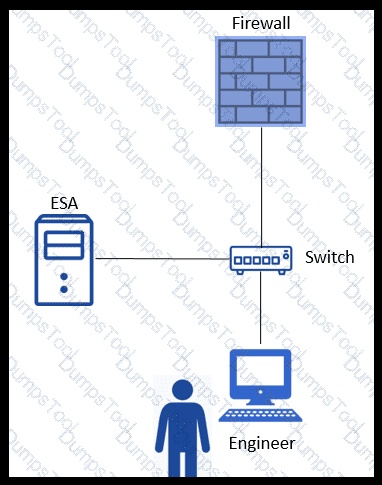
Refer to the exhibit. An engineer is trying to connect to a Cisco E SA using SSH and has been unsuccessful. Upon further inspection, the engineer notices that there is a loss of connectivity to the neighboring switch.
Which connection method should be used to determine the configuration issue?
Which action is allowed while managing list of certificate authorities on Cisco Secure Email Gateway?