A threat hunter is performing a structured hunt usingCisco Secure Endpoint (AMP)telemetry to identify credential harvesting activity. Which data source is MOST critical during thedata collection and processing phaseof the hunt?
A SOC team using Cisco security technologies wants to improve its ability to detect threats that bypass traditional security controls by abusing valid user credentials. Which hunting focus MOST effectively addresses this challenge?
While analyzing telemetry from Cisco Secure Endpoint and Secure Network Analytics, analysts observe that an adversary consistently avoids deploying malware and instead abuses built-in administrative tools. Why does this observation matter for attribution?
A SOC analyst using Cisco security tools wants to differentiatethreat huntingfromtraditional detection engineering. Which activity BEST represents threat hunting rather than detection engineering?
A SOC repeatedly discovers similar attacker behaviors during separate hunts, indicating recurring detection gaps. What process change MOST effectively prevents rediscovery of the same threats?
Refer to the exhibit.
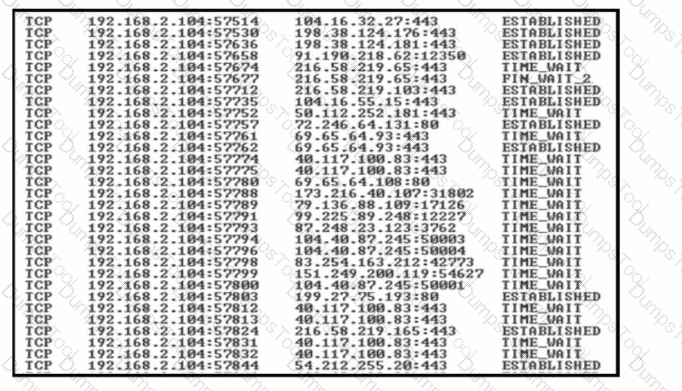
A security team detects a spike in traffic from the company web server. After further investigation, the team discovered that multiple connections have been established from the server to different IP addresses, but the web server logs contain both expected traffic and DDoS traffic. Which attribute must the team use to further filter the logs?
A SOC team must prepare for a new phishing campaign that tricks users into clicking a malicious URL to download a file. When the file executes, it creates a Windows process that harvests user credentials. The team must configure the SIEM tool to receive an alert if a suspicious process is detected. Which two rules must the team create in the SIEM tool? (Choose two.)
The SOC team receives an alert about a user sign-in from an unusual country. After investigating the SIEM logs, the team confirms the user never signed in from that country. The incident is reported to the IT administrator who resets the user's password. Which threat hunting phase was initially used?
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
A security team is performing threat modeling for a hybrid environment consisting of on-prem Active Directory and Azure AD. The team wants to identify how an attacker could move from a compromised cloud identity to full on-prem domain dominance. Which modeling focus is MOST appropriate?
Refer to the exhibit.
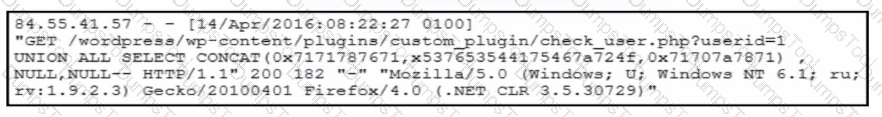
A forensic team must investigate how the company website was defaced. The team isolates the web server, clones the disk, and analyzes the logs. Which technique was used by the attacker initially to access the website?
A threat hunting team is attempting to attribute a series of intrusions across multiple organizations to a known threat actor. The malware binaries differ across incidents, infrastructure changes frequently, and IP addresses rotate daily. Which evidence provides the STRONGEST basis for confident attribution?