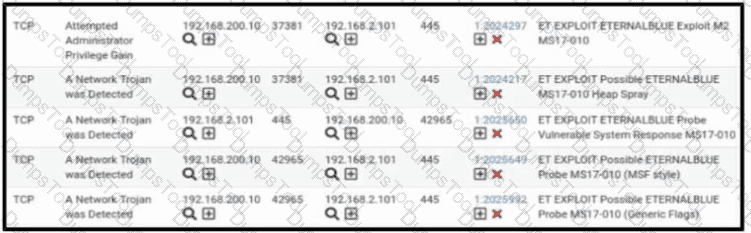
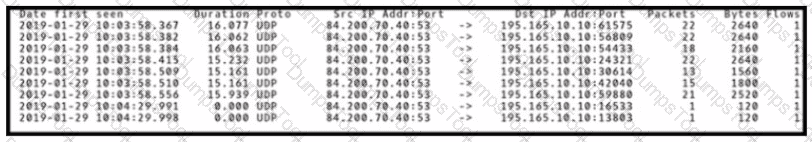
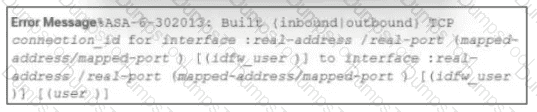
Refer to the exhibit. A security engineer receives several alerts from the SNORT IPS/IDS reporting malicious traffic. What should the engineer understand by examining the SNORT logs?
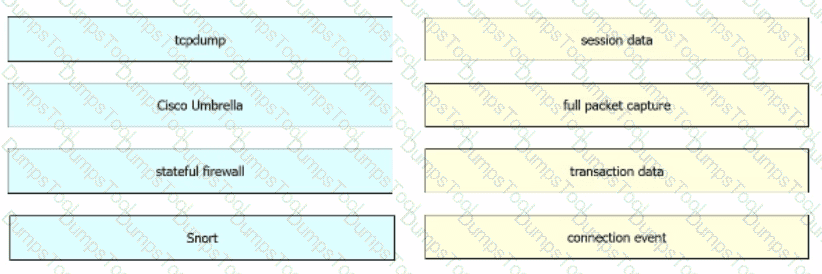
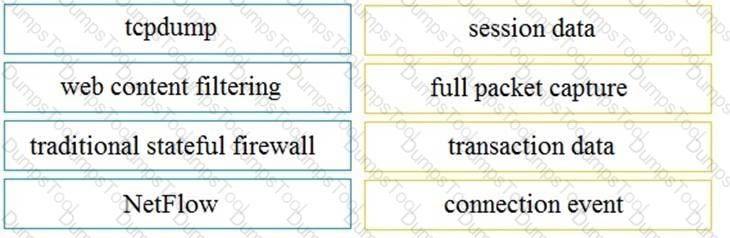
Drag and drop the technologies from the left onto the data types the technologies provide on the right.
A malicious file has been identified in a sandbox analysis tool.
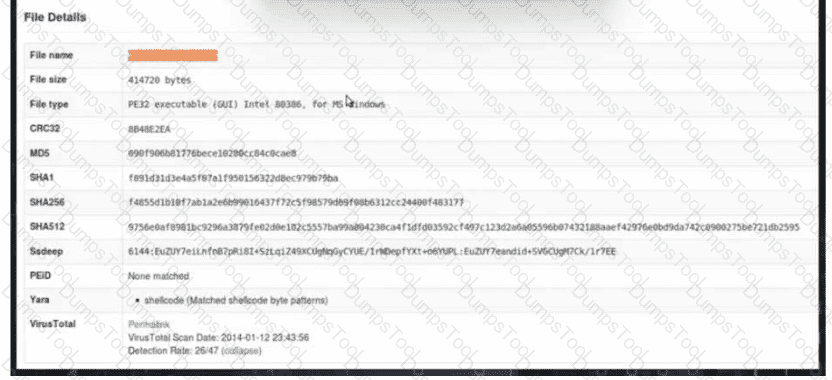
Which piece of information is needed to search for additional downloads of this file by other hosts?
A security engineer has a video of a suspect entering a data center that was captured on the same day that files in the same data center were transferred to a competitor.
Which type of evidence is this?
STION NO: 102
Refer to the exhibit.
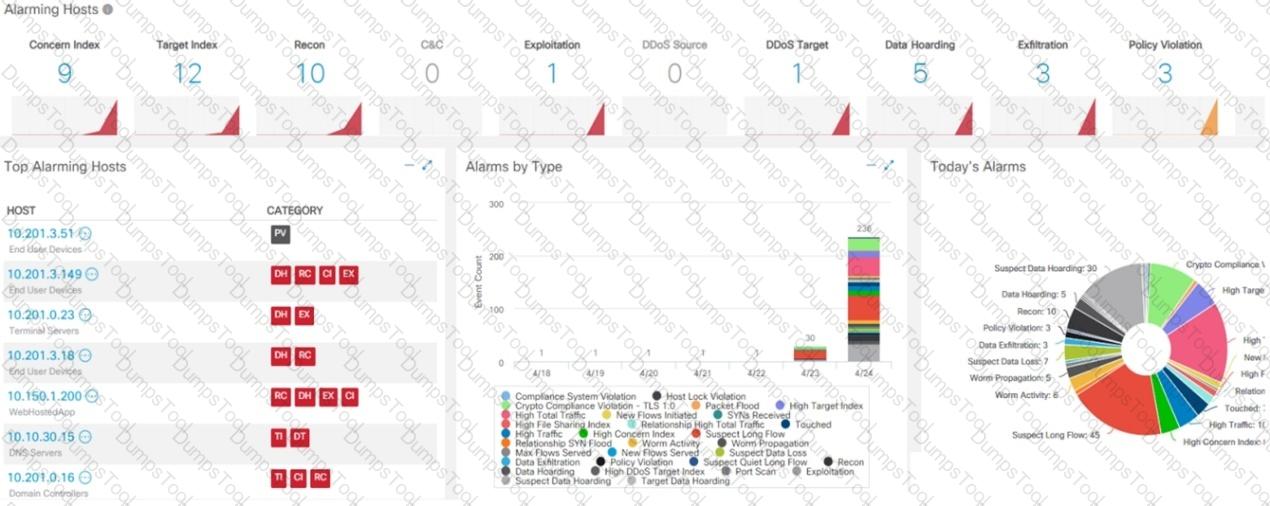
What is the potential threat identified in this Stealthwatch dashboard?
A user received an email attachment named "Hr405-report2609-empl094.exe" but did not run it. Which category of the cyber kill chain should be assigned to this type of event?
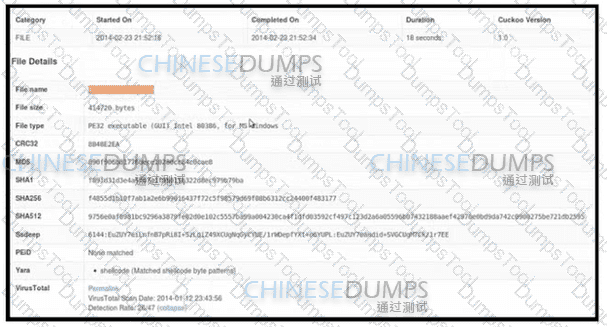
Refer to the exhibit. An employee received an email from an unknown sender with an attachment and reported it as a phishing attempt. An engineer uploaded the file to Cuckoo for further analysis. What should an engineer interpret from the provided Cuckoo report?
What are the two differences between vulnerability and exploit? (Choose two.)
Refer to the exhibit
An engineer is analyzing DNS response packets that are larger than expected The engineer looks closer and notices a lack of appropriate DNS queries What is occurring?
A vulnerability analyst is performing the monthly scan data review Output data is very big and getting bigger each month The analyst decides to create a more efficient process to complete the task on time All false positives and true positives are excluded from the results The remaining findings will be assigned to a technical team for further remediation What is the result of such activity?
An engineer received an alert affecting the degraded performance of a critical server. Analysis showed a heavy CPU and memory load. What is the next step the engineer should take to investigate this resource usage?
A system administrator is ensuring that specific registry information is accurate.
Which type of configuration information does the HKEY_LOCAL_MACHINE hive contain?
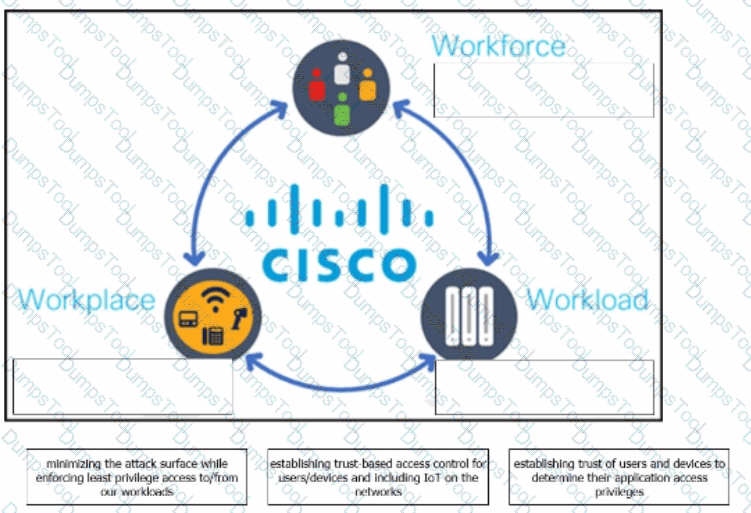
The Cisco Zero Trust Architecture simplifies the zero trust journey into three critical areas. Drag and drop the definitions onto the graphic to describe zero trust from the Cisco perspective.
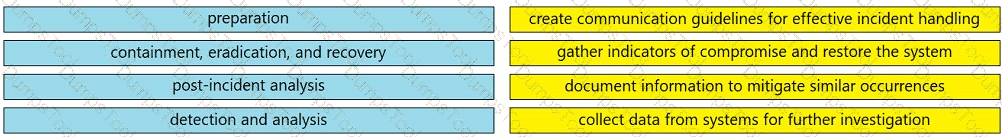
Drag and drop the elements from the left into the correct order for incident handling on the right.
The SOC team has confirmed a potential indicator of compromise on an endpoint. The team has narrowed the executable file's type to a new trojan family. According to the NIST Computer Security Incident Handling Guide, what is the next step in handling this event?
A compliance analyst receives a complaint from a customer regarding personal data being unlawfully retained despite a deletion request. The company is based in Europe and must comply with GDPR. The only data collected is the email address 0524l9i75@gmail.com. How should the compliance analyst act?
Which action should be taken if the system is overwhelmed with alerts when false positives and false negatives are compared?
A security engineer notices confidential data being exfiltrated to a domain "Ranso4134-mware31-895" address that is attributed to a known advanced persistent threat group The engineer discovers that the activity is part of a real attack and not a network misconfiguration. Which category does this event fall under as defined in the Cyber Kill Chain?
Which HTTP header field is used in forensics to identify the type of browser used?
A security consultant must change the identity access management model fof their organization The new approach will put responsibility on the owner, who will decide whichusers will have access to which resources Which low-cost model must be used for this purpose?
An organization has recently adjusted its security stance in response to online threats made by a known hacktivist group.
What is the initial event called in the NIST SP800-61?
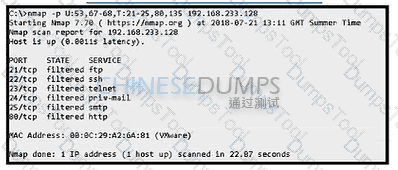
Refer to the exhibit.
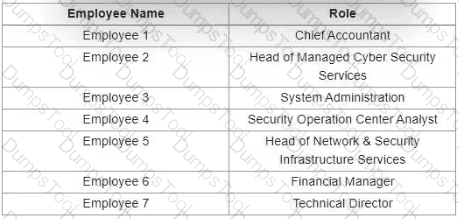
Which stakeholders must be involved when a company workstation is compromised?
An organization's security team has detected network spikes coming from the internal network. An investigation has concluded that the spike in traffic was from intensive network scanning How should the analyst collect the traffic to isolate the suspicious host?
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load What is the next step the engineer should take to investigate this resource usage7
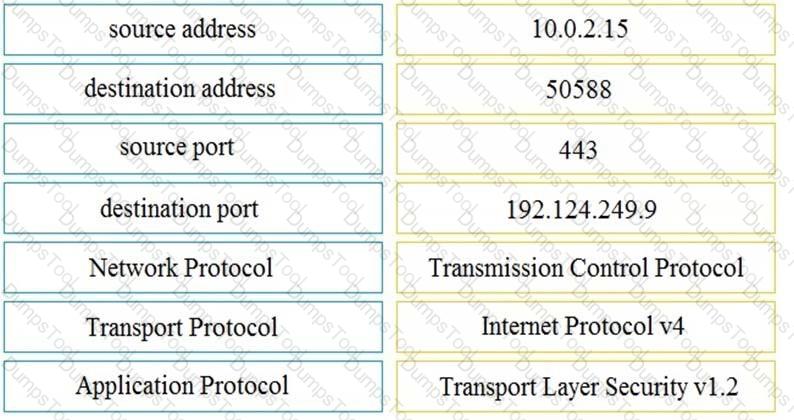
Refer to the exhibit.
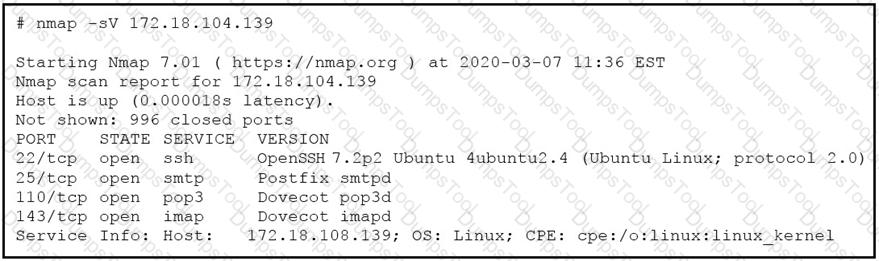
What does the output indicate about the server with the IP address 172.18.104.139?
What is the impact of false positive alerts on business compared to true positive?
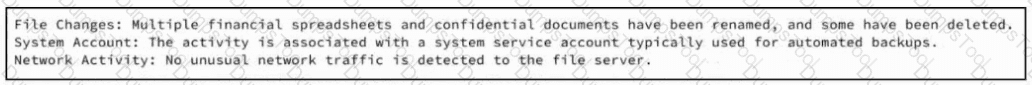
Refer to the exhibit. A SOC team member receives a case from his colleague with notes attached. The artifacts and alerts associated with the case must be analyzed and a conclusion must be provided. What is the cause of the alert?
What are the two characteristics of the full packet captures? (Choose two.)
In digital communications, which method is recommended for securely exchanging public keys between users T0n2262144790 and D4n4126220794?
A SOC analyst is investigating an incident that involves a Linux system that is identifying specific sessions. Which identifier tracks an active program?
What are two differences in how tampered and untampered disk images affect a security incident? (Choose two.)
What is the practice of giving employees only those permissions necessary to perform their specific role within an organization?
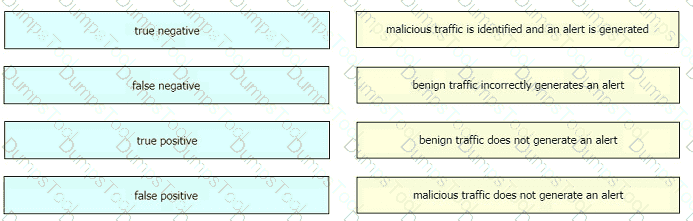
Drag and drop the event term from the left onto the description on the right.
An analyst received a ticket about degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed disabled antivirus software and could not determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
Which security principle requires more than one person is required to perform a critical task?
Which management concept best describes developing, operating, maintaining, upgrading, and disposing of all resources?
What is a difference between rule-based and role-based access control mechanisms?
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
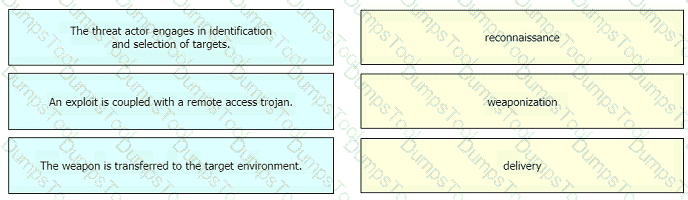
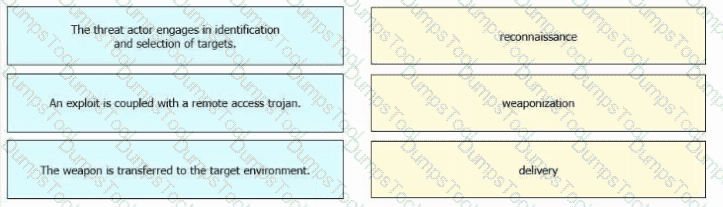
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
Refer to the exhibit.
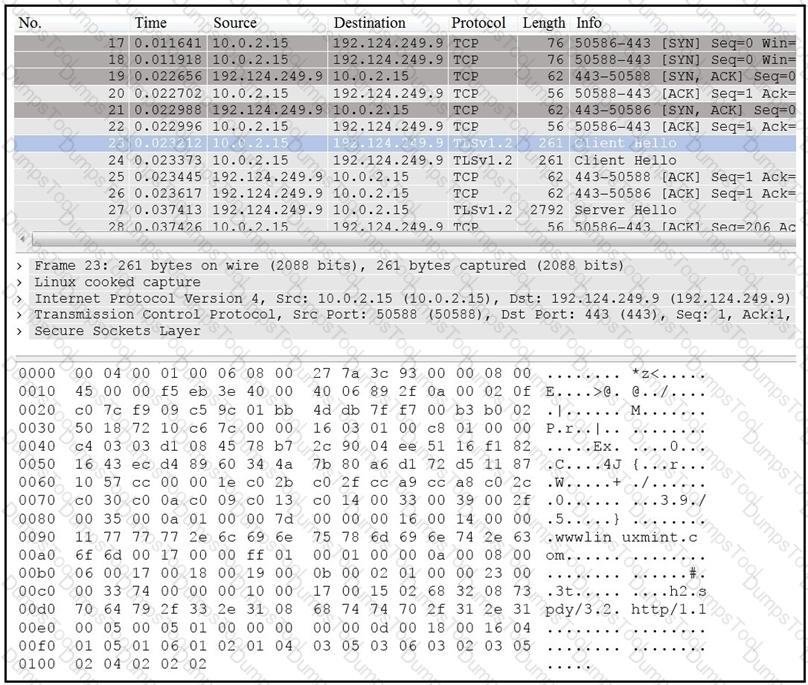
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
Which event artifact is used to identify HTTP GET requests for a specific file?
Which step in the incident response process researches an attacking host through logs in a SIEM?
Refer to the exhibit. An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
Which technique obtains information about how the system works without knowing it's design details?
An analyst discovers that a legitimate security alert has been dismissed. Which signature caused this impact on network traffic?
Which type of data must an engineer capture to analyze payload and header information?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
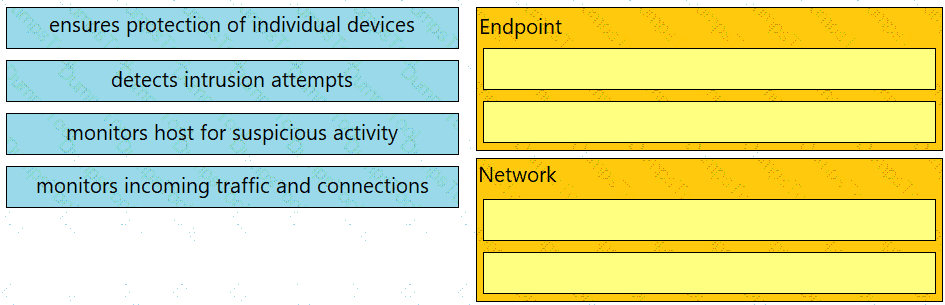
Drag and drop the uses on the left onto the type of security system on the right.
An analyst performs traffic analysis to detect data exfiltration and identifies a high frequency of DNS requests in a small period of time Which technology makes this behavior feasible?
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
An engineer must investigate suspicious connections. Data has been gathered using a tcpdump command on a Linux device and saved as sandboxmatware2022-12-22.pcaps file.The engineer is trying to open the tcpdump in the Wireshark tool. What is the expected result?
Which information must an organization use to understand the threats currently targeting the organization?
Exhibit.
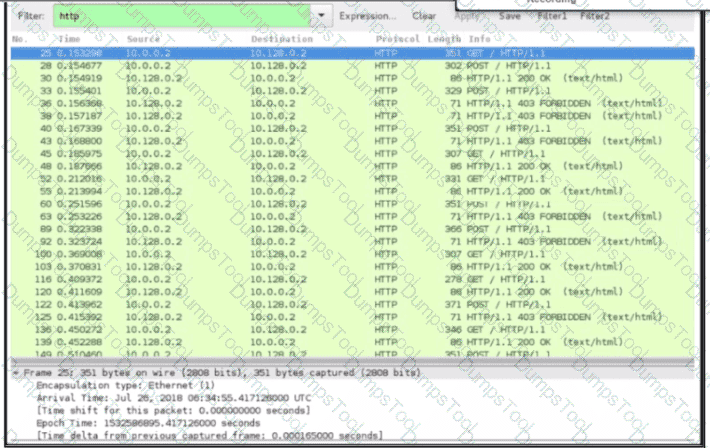
An engineer received a ticket about a slowdown of a web application, Drug analysis of traffic, the engineer suspects a possible attack on a web server. How should the engineer interpret the Wiresharat traffic capture?
A user reports difficulties accessing certain external web pages. When an engineer examines traffic to and from the external domain in full packet captures, they notice that many SYNs have the same sequence number, source, and destination IP address, but they have different payloads. What is causing this situation?
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?
How does the approach of a behavioral detection system to identifying security threats compare to that of a rule-based detection system?
Which action matches the weaponization step of the Cyber Kill Chain model?
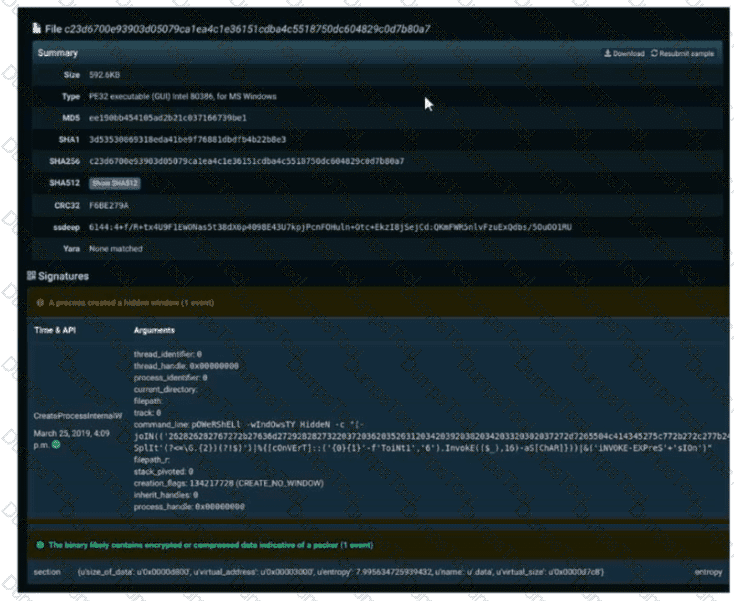
Refer to the exhibit. A SOC engineer is analyzing Cuckoo Sandbox report for a file that has been identified as suspicious by the endpoint security system. What is the state of the file?
Which two protocols are used for DDoS amplification attacks? (Choose two.)
A user received a targeted spear-phishing email and identified it as suspicious before opening the content. To which category of the Cyber Kill Chain model does to this type of event belong?
A network engineer noticed in the NetFlow report that internal hosts are sending many DNS requests to external DNS servers A SOC analyst checked the endpoints and discovered that they are infected and became part of the botnet Endpoints are sending multiple DNS requests but with spoofed IP addresses of valid external sources What kind of attack are infected endpoints involved in1?
Which principle reduces the risk of attackers gaining access to sensitive data by compromising a low-level user account?
What is a difference between inline traffic interrogation and traffic mirroring?
An engineer discovered a breach, identified the threat’s entry point, and removed access. The engineer was able to identify the host, the IP address of the threat actor, and the application the threat actor targeted. What is the next step the engineer should take according to the NIST SP 800-61 Incident handling guide?
Refer to the exhibit.
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
Which security model assumes an attacker within and outside of the network and enforces strict verification before connecting to any system or resource within the organization?
What describes the concept of data consistently and readily being accessible for legitimate users?
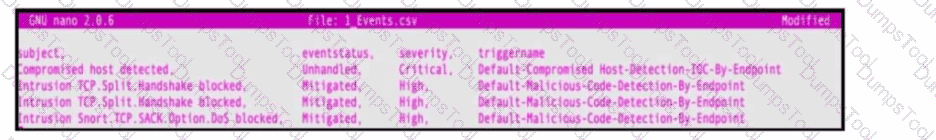
Refer to the exhibit. An engineer must map these events to the source technology that generated the event logs. To which technology do the generated logs belong?
Which difficulty occurs when log messages are compared from two devices separated by a Layer 3 device that performs Network Address Translation?
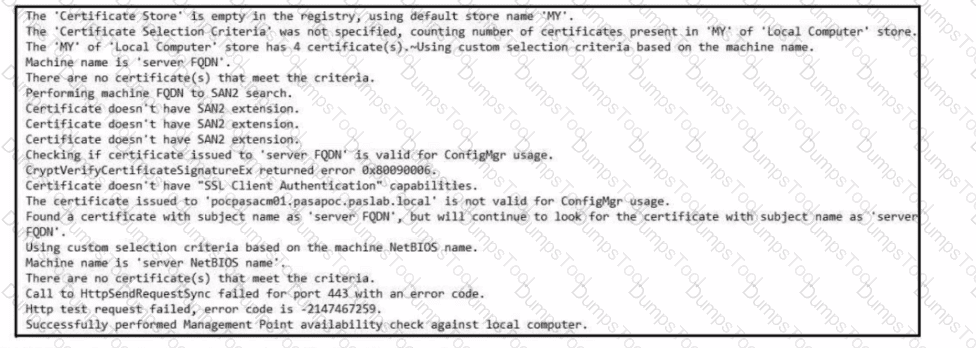
Refer to the exhibit. Which set of actions must an engineer perform to identify and fix this issue?
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
What are two differences between tampered disk images and untampered disk images'? (Choose two.)
A data privacy officer at a marketing firm has received a request from a former client to delete all personally sensitive information held by the company. The firm operates globally and follows international data protection standards. The only information retained about the client is a unique customer ID, "051473912", which is not directly tied to the name, address, or any other identifiable details. Which action should the data privacy officer take?
When an event is investigated, which type of data provides the investigate capability to determine if data exfiltration has occurred?
Drag and drop the technology on the left onto the data type the technology provides on the right.
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
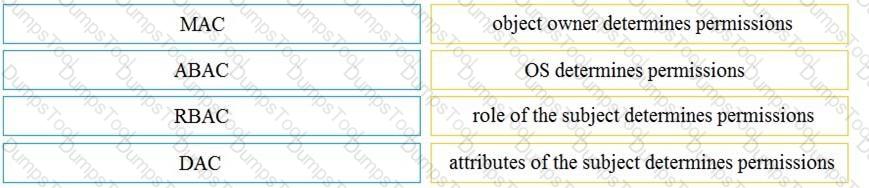
Drag and drop the access control models from the left onto the correct descriptions on the right.
An engineer receives a security alert that traffic with a known TOR exit node has occurred on the network. What is the impact of this traffic?
Which metric is used to capture the level of access needed to launch a successful attack?