312-50v12 Question Includes: Single Choice Questions: 561, Multiple Choice Questions: 11,
Bella, a security professional working at an it firm, finds that a security breach has occurred while transferring important files. Sensitive data, employee usernames. and passwords are shared In plaintext, paving the way for hackers 10 perform successful session hijacking. To address this situation. Bella Implemented a protocol that sends data using encryption and digital certificates. Which of the following protocols Is used by Bella?
Why containers are less secure that virtual machines?
Elliot is in the process of exploiting a web application that uses SQL as a back-end database. He’s determined that the application is vulnerable to SQL injection, and has introduced conditional timing delays into injected queries to determine whether they are successful. What type of SQL injection is Elliot most likely performing?
Consider the following Nmap output:
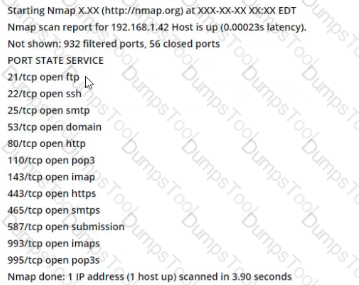
what command-line parameter could you use to determine the type and version number of the web server?
what is the correct way of using MSFvenom to generate a reverse TCP shellcode for windows?
Customers Passed
ECCouncil 312-50v12
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump
DumpsTool Practice Questions provide you with the ultimate pathway to achieve your targeted ECCouncil Exam 312-50v12 IT certification. The innovative questions with their interactive and to the point content make your learning of the syllabus far easier than you could ever imagine.
DumpsTool Practice Questions are information-packed and prove to be the best supportive study material for all exam candidates. They have been designed especially keeping in view your actual exam requirements. Hence they prove to be the best individual support and guidance to ace exam in first go!
ECCouncil CEH v12 312-50v12 PDF file of Practice Questions is easily downloadable on all devices and systems. This you can continue your studies as per your convenience and preferred schedule. Where as testing engine can be downloaded and install to any windows based machine.
DumpsTool Practice Questions ensure your exam success with 100% money back guarantee. There virtually no possibility of losing ECCouncil CEH v12 312-50v12 Exam, if you grasp the information contained in the questions.
DumpsTool professional guidance is always available to its worthy clients on all issues related to exam and DumpsTool products. Feel free to contact us at your own preferred time. Your queries will be responded with prompt response.
DumpsTool tires its level best to entertain its clients with the most affordable products. They are never a burden on your budget. The prices are far less than the vendor tutorials, online coaching and study material. With their lower price, the advantage of DumpsTool 312-50v12 Certified Ethical Hacker Exam (CEHv12) Practice Questions is enormous and unmatched!
The ECCouncil 312-50v12 Exam, also known as the Certified Ethical Hacker (CEH) exam, is a globally recognized certification for aspiring cybersecurity professionals. It validates your knowledge and skills in ethical hacking, penetration testing, and securing computer systems.
The ECCouncil 312-50v12 exam is ideal for individuals interested in ethical hacking, network security, and vulnerability assessment. It’s suitable for security professionals, network administrators, and anyone seeking to enhance their cybersecurity expertise.
The 312-50v12 exam covers various domains, including ethical hacking, network security, reconnaissance, scanning, gaining access, maintaining access, and covering tracks. It tests your understanding of tools, techniques, and methodologies used by ethical hackers.
Earning your CEH v12 certification demonstrates your proficiency in ethical hacking, making you a valuable asset in today's cybersecurity landscape. It can boost your career prospects, increase your earning potential, and enhance your credibility in the field.
The ECCouncil 312-50v12 exam consists of 125 multiple-choice questions.
The ECCouncil 312-50v12 exam has a duration of 4 hours.
The EC-Council 312-50v12 certification is valid for three years from the date of passing the exam. After this period, you’ll need to renew it by demonstrating continued professional development or retaking the exam.
To prepare for the CEH v12 Practice Test, you can utilize Dumpstool's comprehensive 312-50v12 question sets with explanations to help you understand the concepts better. Additionally, you can use our 312-50v12 PDF study guide and testing engine for thorough preparation.
Yes, you can access Dumpstool 312-50v12 PDF exam questions on multiple devices, including computers, tablets, and smartphones. This flexibility allows you to study and review materials at your convenience, ensuring that you are well-prepared for the 312-50v12 exam.
Dumpstool offers a money-back guarantee if you do not pass the CEHv12 certification exam after using our 312-50v12 study materials. To be eligible, you must provide proof of your 312-50v12 exam attempt and failure. Our guarantee is designed to ensure that you get the most value out of your preparation materials.