A customer is interested in PCI requirements and needs to ensure that no privilege containers can start in the environment.
Which action needs to be set for “do not use privileged containers”?
What are the two ways to scope a CI policy for image scanning? (Choose two.)
Which ban for DoS protection will enforce a rate limit for users who are unable to post five (5) “. tar.gz" files within five (5) seconds?
Which three fields are mandatory when authenticating the Prisma Cloud plugin in the IntelliJ application? (Choose three.)
What must be created in order to receive notifications about alerts generated when the operator is away from the Prisma Cloud Console?
An administrator has a requirement to ingest all Console and Defender logs to Splunk.
Which option will satisfy this requirement in Prisma Cloud Compute?
Which statement is true about obtaining Console images for Prisma Cloud Compute Edition?
In WAAS Access control file upload controls, which three file types are supported out of the box? (Choose three.)
Prisma Cloud supports which three external systems that allow the import of vulnerabilities and provide additional context on risks in the cloud? (Choose three.)
Which three actions are available for the container image scanning compliance rule? (Choose three.)
Which method should be used to authenticate to Prisma Cloud Enterprise programmatically?
Which three elements are part of SSH Events in Host Observations? (Choose three.)
Which two CI/CD plugins are supported by Prisma Cloud as part of its DevOps Security? (Choose two.).
In Azure, what permissions need to be added to Management Groups to allow Prisma Cloud to calculate net effective permissions?
When would a policy apply if the policy is set under Defend > Vulnerability > Images > Deployed?
A customer has a requirement to automatically protect all Lambda functions with runtime protection. What is the process to automatically protect all the Lambda functions?
What is the function of the external ID when onboarding a new Amazon Web Services (AWS) account in Prisma Cloud?
Which alert deposition severity must be chosen to generate low and high severity alerts in the Anomaly settings when user wants to report on an unknown browser and OS, impossible time travel, or both due to account hijacking attempts?
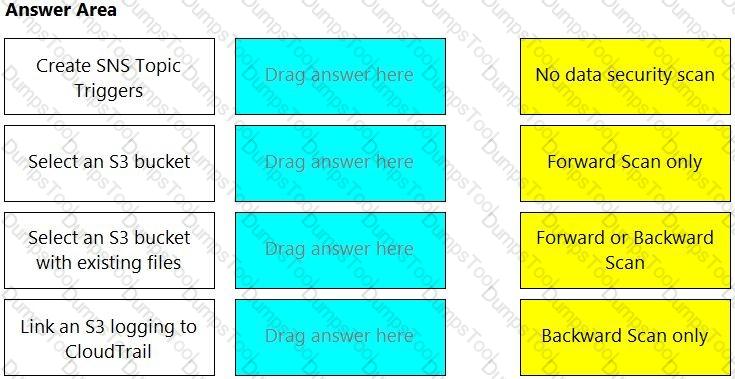
Match the correct scanning mode for each given operation.
(Select your answer from the pull-down list. Answers may be used more than once or not at all.)
An S3 bucket within AWS has generated an alert by violating the Prisma Cloud Default policy “AWS S3 buckets are accessible to public”. The policy definition follows:
config where cloud.type = 'aws' AND api.name='aws-s3api-get-bucket-acl' AND json.rule="((((acl.grants[? (@.grantee=='AllUsers')] size > 0) or policyStatus.isPublic is true) and publicAccessBlockConfiguration does not exist) or ((acl.grants[?(@.grantee=='AllUsers')] size > 0) and publicAccessBlockConfiguration.ignorePublicAcis is false) or (policyStatus.isPublic is true and publicAccessBlockConfiguration.restrictPublicBuckets is false)) and websiteConfiguration does not exist"
Why did this alert get generated?
Under which tactic is “Exploit Public-Facing Application” categorized in the ATT&CK framework?
A security team is deploying Cloud Native Application Firewall (CNAF) on a containerized web application. The application is running an NGINX container. The container is listening on port 8080 and is mapped to host port 80.
Which port should the team specify in the CNAF rule to protect the application?
An administrator has been tasked with a requirement by your DevSecOps team to write a script to continuously query programmatically the existing users, and the user’s associated permission levels, in a Prisma Cloud Enterprise tenant.
Which public documentation location should be reviewed to help determine the required attributes to carry out this step?
When configuring SSO how many IdP providers can be enabled for all the cloud accounts monitored by Prisma Cloud?
The compliance team needs to associate Prisma Cloud policies with compliance frameworks. Which option should the team select to perform this task?
A customer has Defenders connected to Prisma Cloud Enterprise. The Defenders are deployed as a DaemonSet in OpenShift.
How should the administrator get a report of vulnerabilities on hosts?
What factor is not used in calculating the net effective permissions for a resource in AWS?
Prisma Cloud Compute has been installed on Onebox. After Prisma Cloud Console has been accessed. Defender is disconnected and keeps returning the error "No console connectivity" in the logs.
What could be causing the disconnection between Console and Defender in this scenario?
Which two options may be used to upgrade the Defenders with a Console v20.04 and Kubernetes deployment? (Choose two.)
An administrator of Prisma Cloud wants to enable role-based access control for Docker engine.
Which configuration step is needed first to accomplish this task?
Which two fields are required to configure SSO in Prisma Cloud? (Choose two.)
What is required for Prisma Cloud to successfully execute auto-remediation commands?
In which Console menu would an administrator verify whether a custom compliance check is failing or passing?
Which two statements explain differences between build and run config policies? (Choose two.)
During the Learning phase of the Container Runtime Model, Prisma Cloud enters a “dry run” period for how many hours?
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
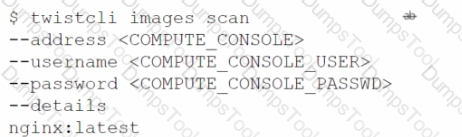
C)
D)
The Compute Console has recently been upgraded, and the administrator plans to delay upgrading the Defenders and the Twistcli tool until some of the team’s resources have been rescaled. The Console is currently one major release ahead.
What will happen as a result of the Console upgrade?
An administrator has deployed Console into a Kubernetes cluster running in AWS. The administrator also has configured a load balancer in TCP passthrough mode to listen on the same ports as the default Prisma Compute Console configuration.
In the build pipeline, the administrator wants twistcli to talk to Console over HTTPS. Which port will twistcli need to use to access the Prisma Compute APIs?
Which two services require external notifications to be enabled for policy violations in the Prisma Cloud environment? (Choose two.)
Which two integrations enable ingesting host findings to generate alerts? (Choose two.)
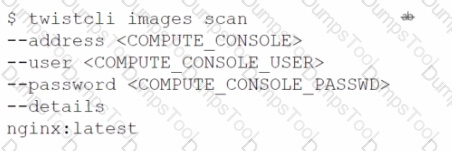
Put the steps of integrating Okta with Prisma Cloud in the right order in relation to CIEM or SSO okra integration.
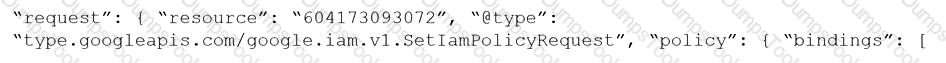
Given the following JSON query:
$.resource[*].aws_s3_bucket exists
Which tab is the correct place to add the JSON query when creating a Config policy?
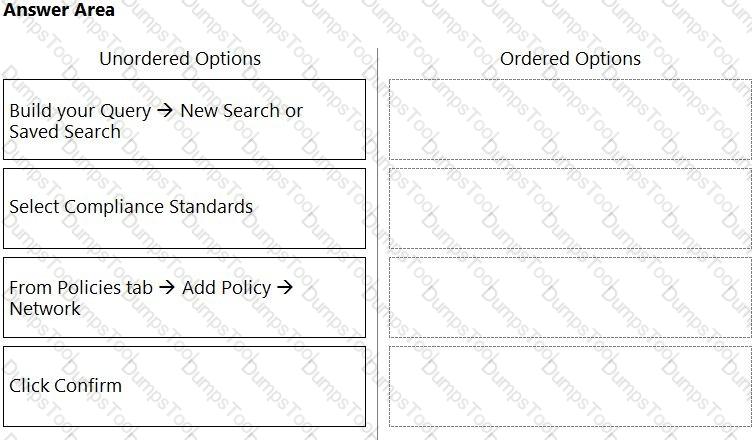
What is the order of steps to create a custom network policy?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
An administrator for Prisma Cloud needs to obtain a graphical view to monitor all connections, including connections across hosts and connections to any configured network objects.
Which setting does the administrator enable or configure to accomplish this task?
Which API calls can scan an image named myimage: latest with twistcli and then retrieve the results from Console?
What will happen when a Prisma Cloud Administrator has configured agentless scanning in an environment that also has Host and Container Defenders deployed?
The security auditors need to ensure that given compliance checks are being run on the host. Which option is a valid host compliance policy?
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
The security team wants to target a CNAF policy for specific running Containers. How should the administrator scope the policy to target the Containers?
A customer finds that an open alert from the previous day has been resolved. No auto-remediation was configured.
Which two reasons explain this change in alert status? (Choose two.)
Console is running in a Kubernetes cluster, and Defenders need to be deployed on nodes within this cluster.
How should the Defenders in Kubernetes be deployed using the default Console service name?
A Prisma Cloud administrator is onboarding a single GCP project to Prisma Cloud. Which two steps can be performed by the Terraform script? (Choose two.)
A customer has a development environment with 50 connected Defenders. A maintenance window is set for Monday to upgrade 30 stand-alone Defenders in the development environment, but there is no maintenance window available until Sunday to upgrade the remaining 20 stand-alone Defenders.
Which recommended action manages this situation?
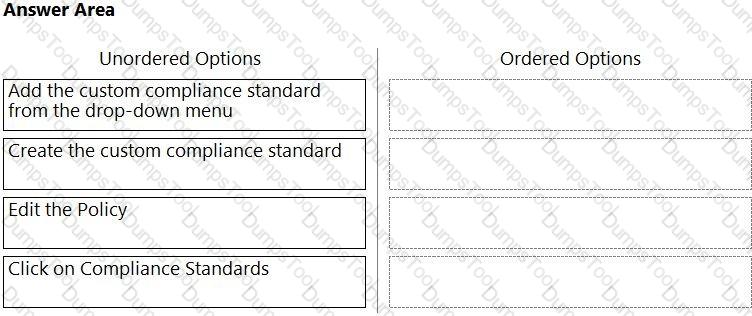
Which order of steps map a policy to a custom compliance standard?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
While writing a custom RQL with array objects in the investigate page, which type of auto-suggestion a user can leverage?
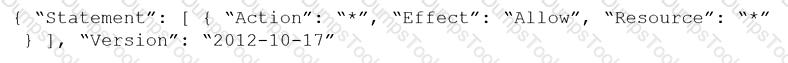
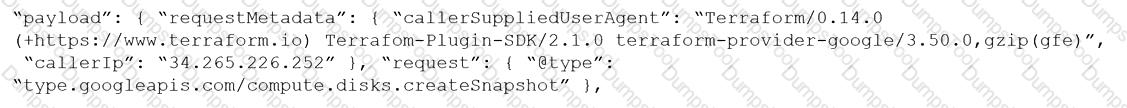
Given the following RQL:
event from cloud.audit_logs where operation IN (‘CreateCryptoKey’, ‘DestroyCryptoKeyVersion’, ‘v1.compute.disks.createSnapshot’)
Which audit event snippet is identified?
A)
B)
C)
D)
What is the correct method for ensuring key-sensitive data related to SSNs and credit card numbers cannot be viewed in Dashboard > Data view during investigations?
An administrator has added a Cloud account on Prisma Cloud and then deleted it.
What will happen if the deleted account is added back on Prisma Cloud within a 24-hour period?
Which policy type provides information about connections from suspicious IPs in a customer database?
Which report includes an executive summary and a list of policy violations, including a page with details for each policy?