Which option shows the steps to install the Console in a Kubernetes Cluster?
A customer wants to harden its environment from misconfiguration.
Prisma Cloud Compute Compliance enforcement for hosts covers which three options? (Choose three.)
Which of the following is not a supported external integration for receiving Prisma Cloud Code Security notifications?
Which two frequency options are available to create a compliance report within the console? (Choose two.)
Which two integrations enable ingesting host findings to generate alerts? (Choose two.)
Which two statements are true about the differences between build and run config policies? (Choose two.)
Which IAM Azure RQL query would correctly generate an output to view users who have sufficient permissions to create security groups within Azure AD and create applications?
What is an automatically correlated set of individual events generated by the firewall and runtime sensors to identify unfolding attacks?
A container and image compliance rule has been configured by enabling all checks; however, upon review, the container's compliance view reveals only the entries in the image below.
What is the appropriate action to take next?
An administrator has been tasked with a requirement by your DevSecOps team to write a script to continuously query programmatically the existing users, and the user’s associated permission levels, in a Prisma Cloud Enterprise tenant.
Which public documentation location should be reviewed to help determine the required attributes to carry out this step?
An administrator wants to enforce a rate limit for users not being able to post five (5) .tar.gz files within five (5) seconds.
What does the administrator need to configure?
Which two actions are required in order to use the automated method within Amazon Web Services (AWS) Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose two.)
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
When configuring SSO how many IdP providers can be enabled for all the cloud accounts monitored by Prisma Cloud?
A Systems Engineer is the administrator of a self-hosted Prisma Cloud console. They upgraded the console to the latest version. However, after the upgrade, the console does not show all the policies configured. Before they upgraded the console, they created a backup manually and exported it to a local drive. Now they have to install a Prisma Cloud to restore from the backup that they manually created. Which Prisma Cloud version can they can restore with the backup?
What are two alarm types that are registered after alarms are enabled? (Choose two.)
Which intensity setting for anomaly alerts is used for the measurement of 100 events over 30 days?
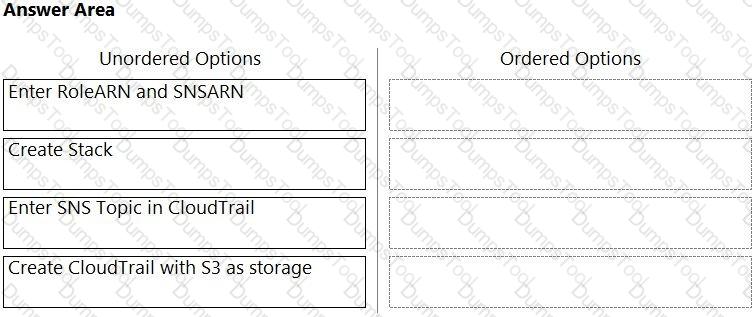
Order the steps involved in onboarding an AWS Account for use with Data Security feature.
A customer has a requirement to scan serverless functions for vulnerabilities.
What is the correct option to configure scanning?
Which three steps are involved in onboarding an account for Data Security? (Choose three.)
An administrator has added a Cloud account on Prisma Cloud and then deleted it.
What will happen if the deleted account is added back on Prisma Cloud within a 24-hour period?
In Prisma Cloud for Azure Net Effective Permissions Calculation, the following Azure permission levels are supported by which three permissions? (Choose three).
A customer's Security Operations Center (SOC) team wants to receive alerts from Prisma Cloud via email once a day about all policies that have a violation, rather than receiving an alert every time a new violation occurs.
Which alert rule configuration meets this requirement?
How many CLI remediation commands can be added in a custom policy sequence?
A customer has Defenders connected to Prisma Cloud Enterprise. The Defenders are deployed as a DaemonSet in OpenShift.
How should the administrator get a report of vulnerabilities on hosts?
Which two statements explain differences between build and run config policies? (Choose two.)
The security team wants to enable the “block” option under compliance checks on the host.
What effect will this option have if it violates the compliance check?
What is the maximum number of access keys a user can generate in Prisma Cloud with a System Admin role?
What are the two ways to scope a CI policy for image scanning? (Choose two.)
A customer wants to scan a serverless function as part of a build process. Which twistcli command can be used to scan serverless functions?
Which type of query is used for scanning Infrastructure as Code (laC) templates?
The administrator wants to review the Console audit logs from within the Console.
Which page in the Console should the administrator use to review this data, if it can be reviewed at all?
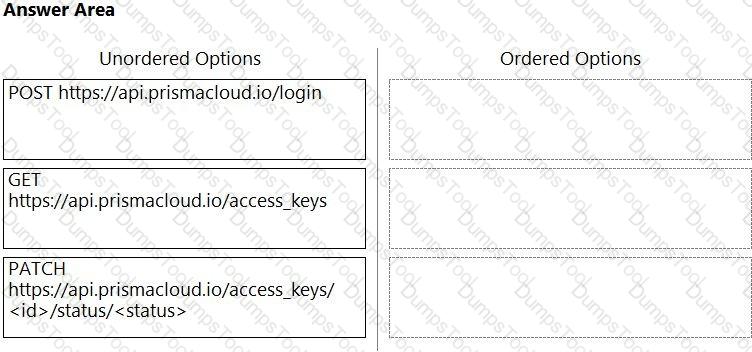
An administrator needs to write a script that automatically deactivates access keys that have not been used for 30 days.
In which order should the API calls be used to accomplish this task? (Drag the steps into the correct order from the first step to the last.) Select and Place:
The development team is building pods to host a web front end, and they want to protect these pods with an application firewall.
Which type of policy should be created to protect this pod from Layer7 attacks?
Which serverless cloud provider is covered by the "overly permissive service access" compliance check?
When an alert notification from the alarm center is deleted, how many hours will a similar alarm be suppressed by default?
During an initial deployment of Prisma Cloud Compute, the customer sees vulnerabilities in their environment.
Which statement correctly describes the default vulnerability policy?
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
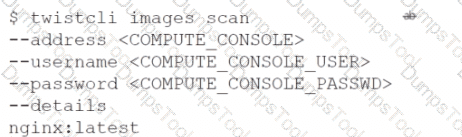
C)
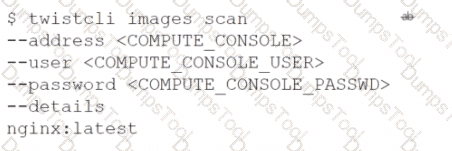
D)
A customer is reviewing Container audits, and an audit has identified a cryptominer attack. Which three options could have generated this audit? (Choose three.)
Which two information types cannot be seen in the data security dashboard? (Choose two).
In which Console menu would an administrator verify whether a custom compliance check is failing or passing?
Per security requirements, an administrator needs to provide a list of people who are receiving e-mails for Prisma Cloud alerts.
Where can the administrator locate this list of e-mail recipients?
Which two roles have access to view the Prisma Cloud policies? (Choose two.)
Which three actions are available for the container image scanning compliance rule? (Choose three.)
An organization wants to be notified immediately to any “High Severity” alerts for the account group “Clinical Trials” via Slack.
Which option shows the steps the organization can use to achieve this goal?
How does assigning an account group to an administrative user on Prisma Cloud help restrict access to resources?
A customer has multiple violations in the environment including:
User namespace is enabled
An LDAP server is enabled
SSH root is enabled
Which section of Console should the administrator use to review these findings?
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose three.)
An administrator needs to detect and alert on any activities performed by a root account.
Which policy type should be used?
A business unit has acquired a company that has a very large AWS account footprint. The plan is to immediately start onboarding the new company’s AWS accounts into Prisma Cloud Enterprise tenant immediately. The current company is currently not using AWS Organizations and will require each account to be onboarded individually.
The business unit has decided to cover the scope of this action and determined that a script should be written to onboard each of these accounts with general settings to gain immediate posture visibility across the accounts.
Which API endpoint will specifically add these accounts into the Prisma Cloud Enterprise tenant?
If you are required to run in an air-gapped environment, which product should you install?
A customer does not want alerts to be generated from network traffic that originates from trusted internal networks.
Which setting should you use to meet this customer’s request?
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
Which method should be used to authenticate to Prisma Cloud Enterprise programmatically?
Which two options may be used to upgrade the Defenders with a Console v20.04 and Kubernetes deployment? (Choose two.)
A customer has a requirement to terminate any Container from image topSecret:latest when a process named ransomWare is executed.
How should the administrator configure Prisma Cloud Compute to satisfy this requirement?