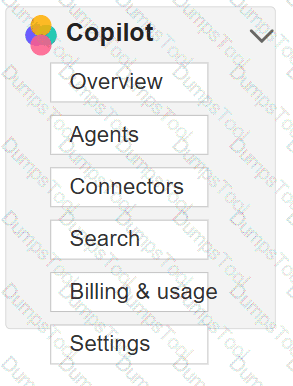
You need to ensure that users can use an external system as a knowledge source for custom Microsoft 365 Copilot agents. What should you configure in the Microsoft 365 admin center? To answer, select the appropriate settings in the answer area.
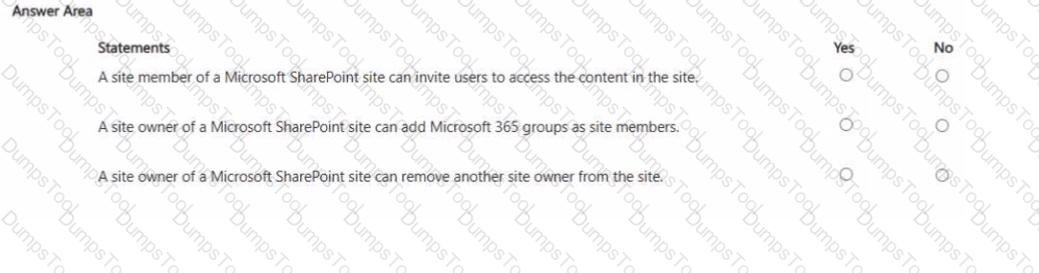
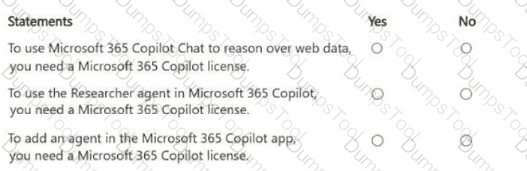
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE Each correct selection is worth one point
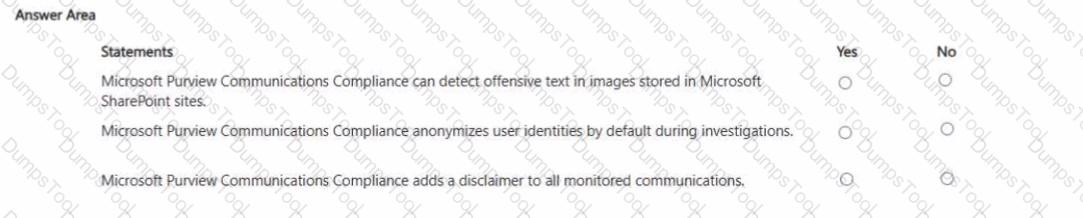
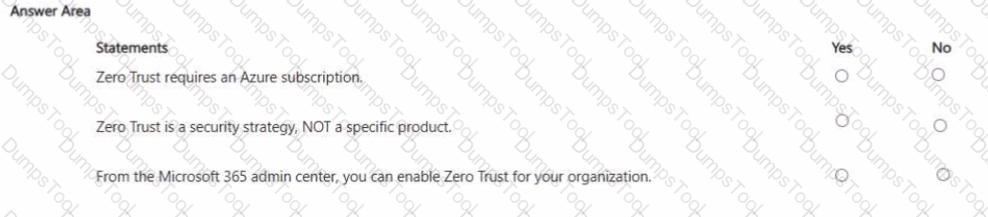
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point
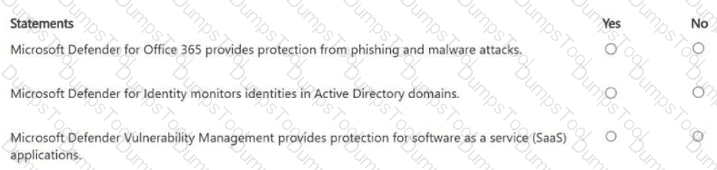
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
What can you use to block a user account automatically when a risky sign-in is detected?
Your organization has a Microsoft 365 subscription.
You need to review the impact of a recent phishing incident that targeted email users.
What should you use?
Your organization has a Microsoft 365 subscription.
All users are assigned a Microsoft 365 Copilot license.
You need to prevent the users from generating images by using Copilot.
What should you use?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
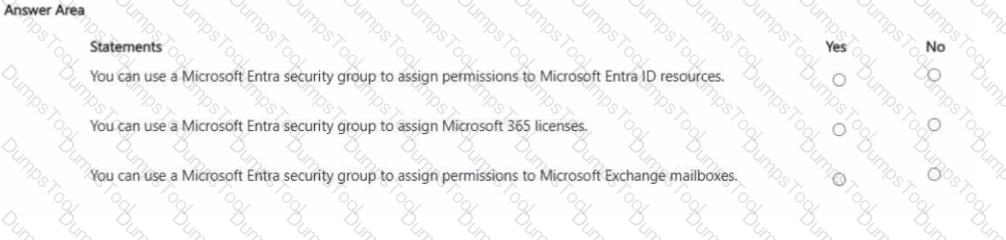
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Your company has a written compliance policy that requires all emails be retained for seven years, and then permanently deleted. Which Microsoft Purview solution should you use?