An organization is deploying a new data lake that will centralize records from several applications. During the design phase, the security architect identifies the following requirements:
• The sensitivity levels of the data is different.
• The data must be accessed through stateless API calls after authentication.
• Different users will have access to different data sets.
Which of the following should the architect implement to best meet these requirements?
A network engineer must ensure that always-on VPN access is enabled Curt restricted to company assets Which of the following best describes what the engineer needs to do ' '
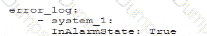
A security analyst is performing a review of a web application. During testing as a standard user, the following error log appears:
Error Message in Database Connection
Connection to host USA-WebApp-Database failed
Database " Prod-DB01 " not found
Table " CustomerInfo " not found
Please retry your request later
Which of the following best describes the analyst’s findings and a potential mitigation technique?
A company wants to improve and automate the compliance of its cloud environments to meet industry standards. Which of the following resources should the company use to best achieve this goal?
A cybersecurity architect is reviewing the detection and monitoring capabilities for a global company that recently made multiple acquisitions. The architect discovers that the acquired companies use different vendors for detection and monitoring The architect ' s goal is to:
• Create a collection of use cases to help detect known threats
• Include those use cases in a centralized library for use across all of the companies
Which of the following is the best way to achieve this goal?
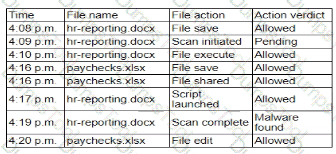
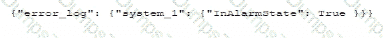
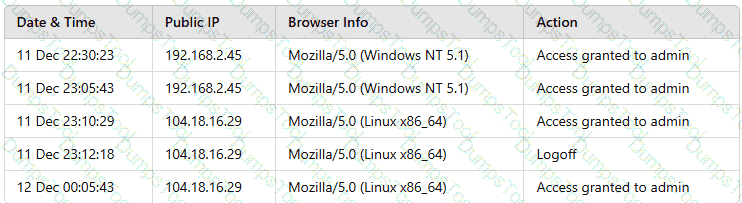
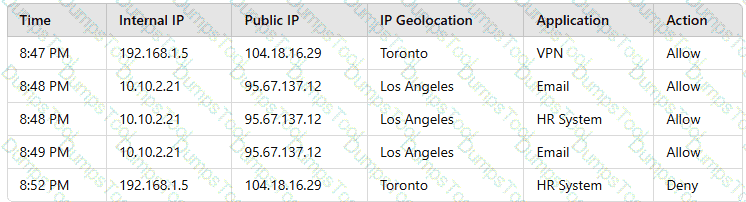
A user reports application access issues to the help desk. The help desk reviews the logs for the user
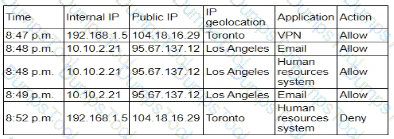
Which of the following is most likely The reason for the issue?
A security analyst is reviewing the following log:
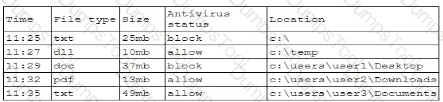
Which of the following possible events should the security analyst investigate further?
A developer receives feedback about code quality and efficiency. The developer needs to identify and resolve the following coding issues before submitting the code changes for peer review:
Indexing beyond arrays
Dereferencing null pointers
Potentially dangerous data type combinations
Unreachable code
Non-portable constructs
Which of the following would be most appropriate for the developer to use in this situation?
A security manager at a local hospital wants to secure patient medical records. The manager needs to:
• Choose an access control model that clearly defines who has access to sensitive information.
• Prevent those who enter new patient information from specifying who has access to this data.
Which of the following access control models is the best way to ensure the lowest risk of granting unintentional access?
Employees use their badges to track the number of hours they work. The badge readers cannot be upgraded due to facility constraints. The software for the badge readers uses a legacy platform and requires connectivity to the enterprise resource planning solution. Which of the following is the best to ensure the security of the badge readers?
A network security architect for an organization with a highly remote workforce implements an always-on VPN to meet business requirements. Which of the following best explains why the architect is using this approach?
An organization recently implemented a new email DLP solution. Emails sent from company email addresses to matching personal email addresses generated a large number of alerts, but the content of the emails did not include company data. The security team needs to reduce the number of emails sent without blocking all emails to common personal email services. Which of the following should the security team implement first?
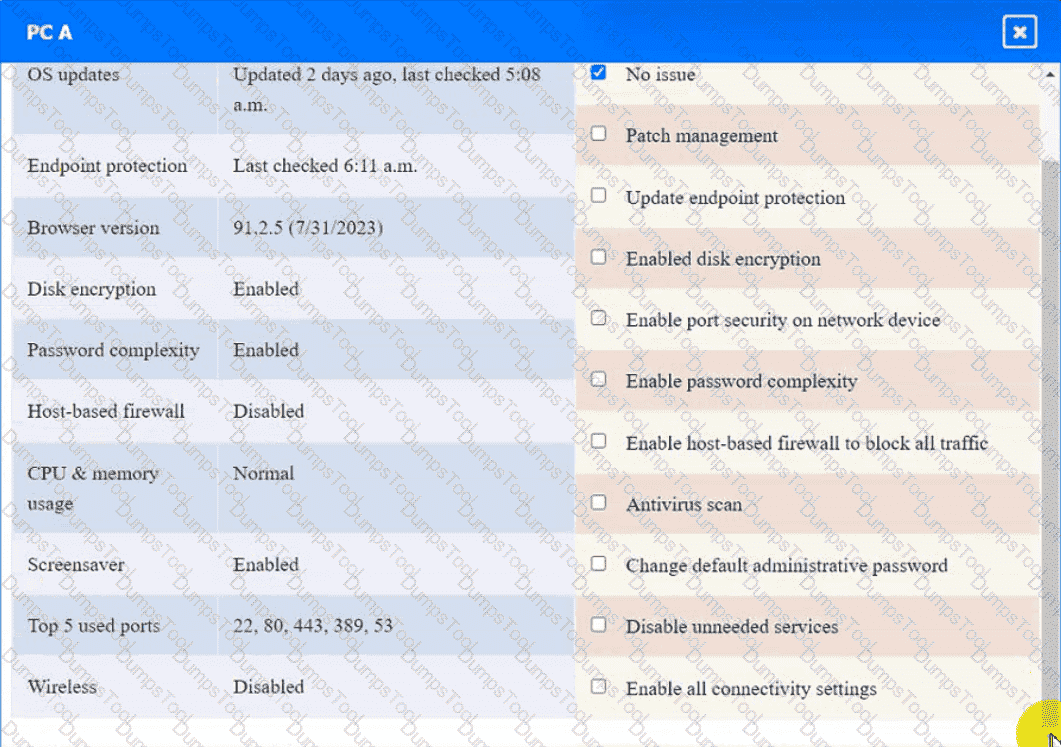
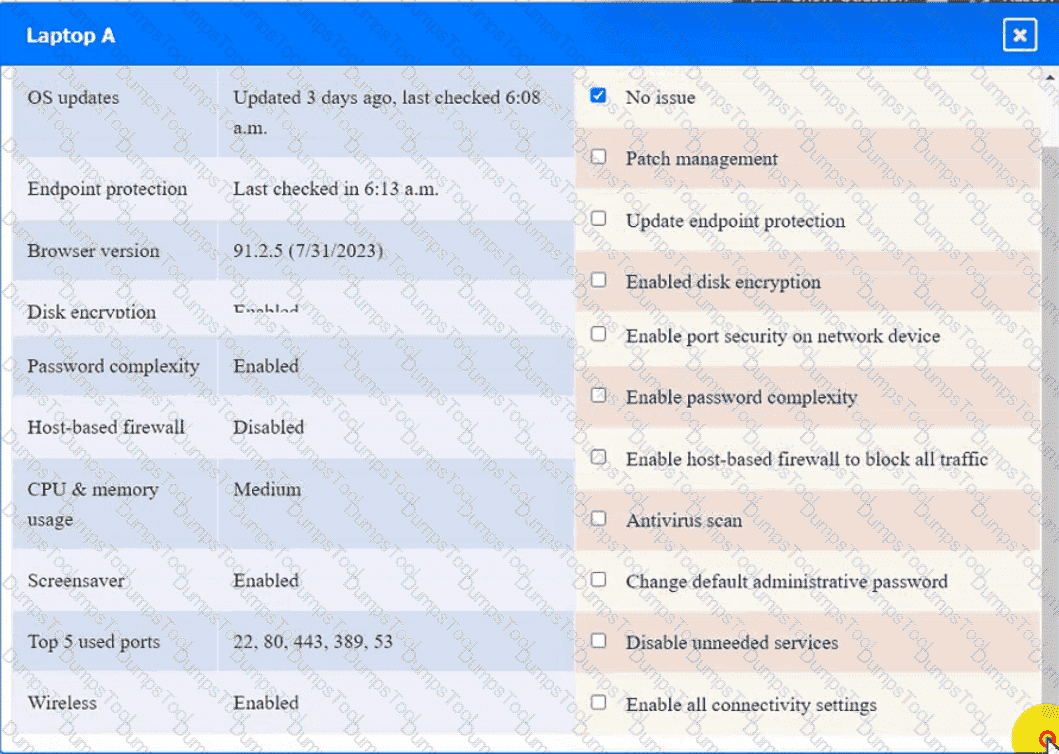
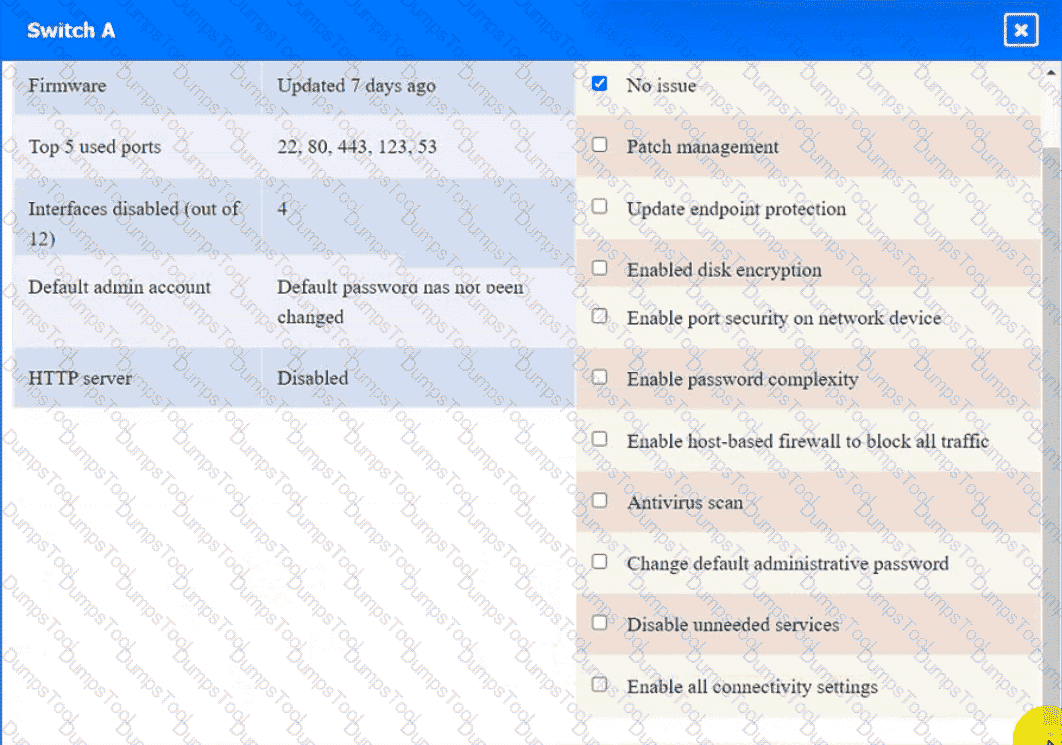
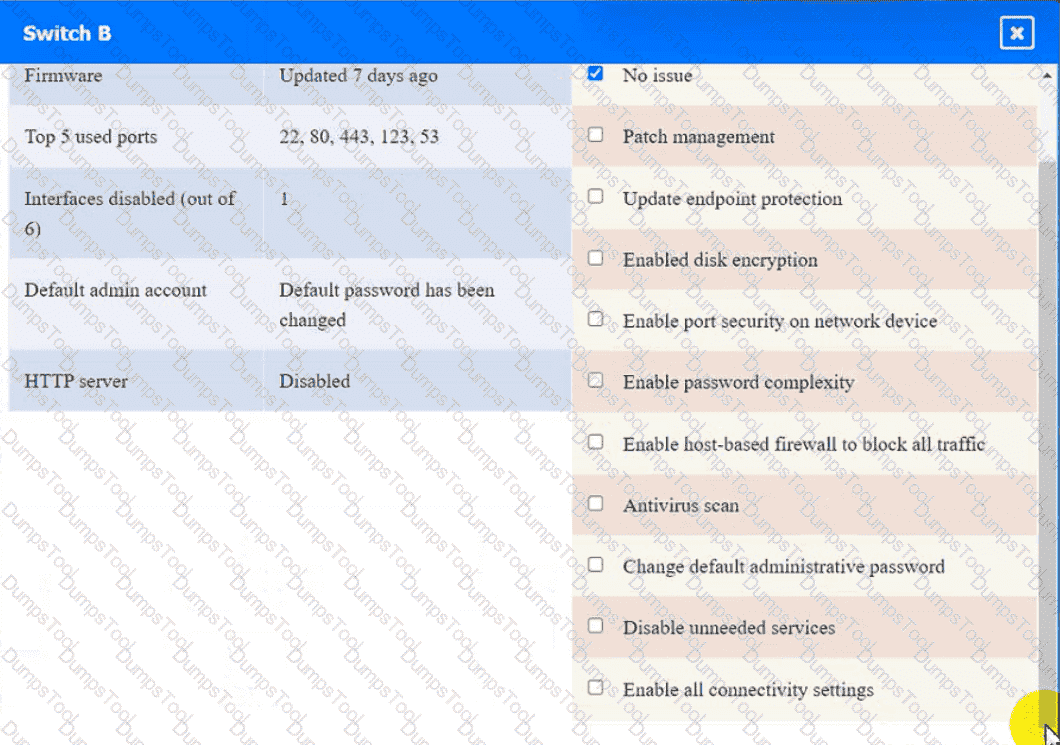
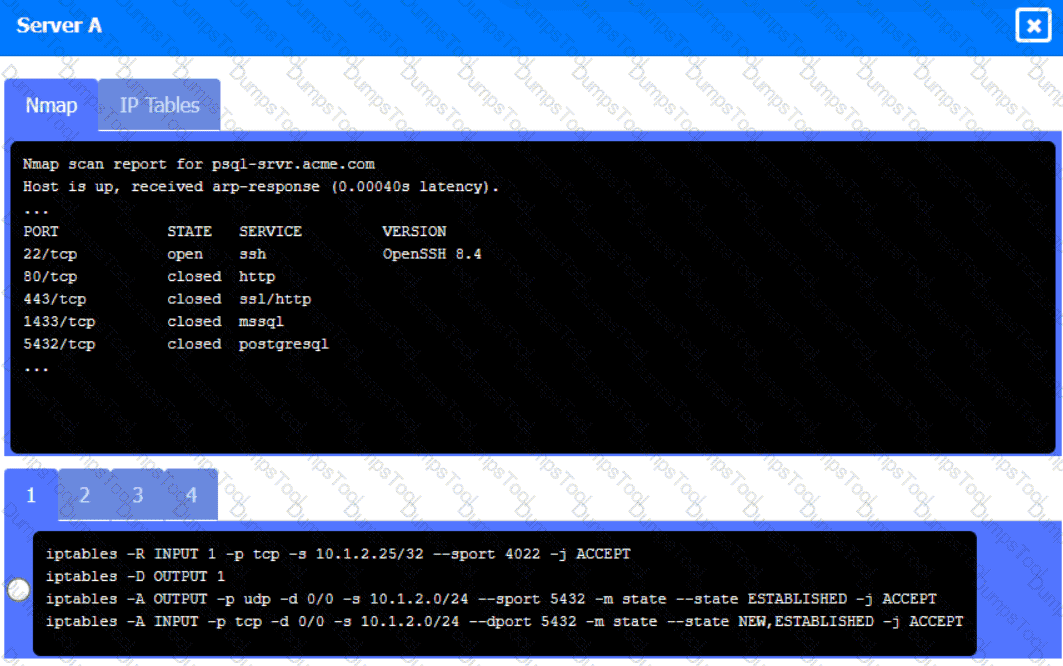
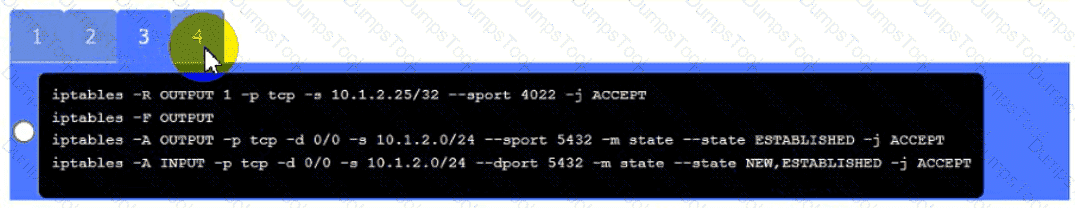
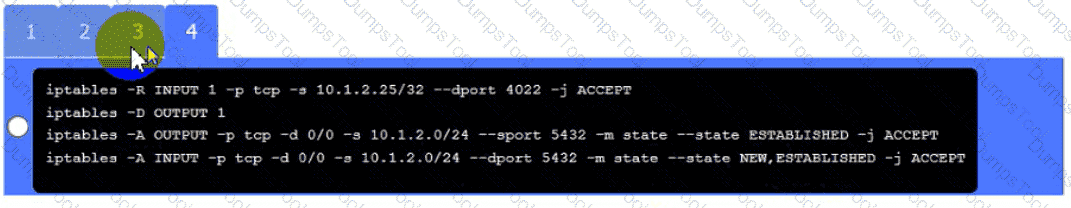
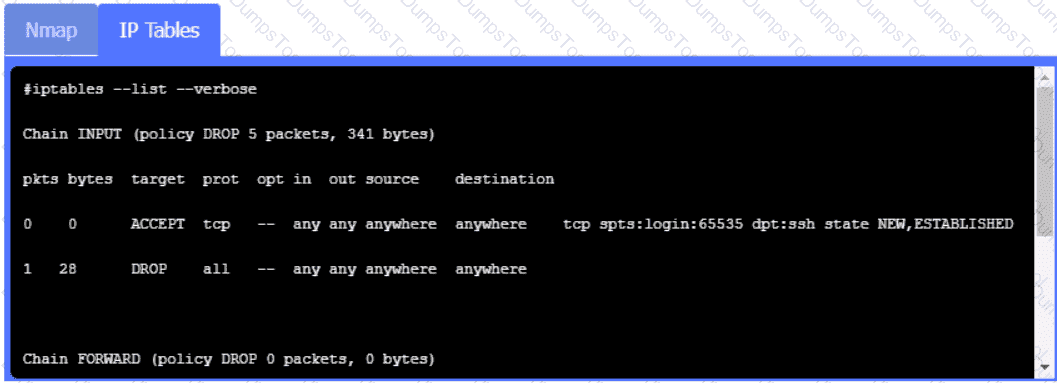
A security engineer needs to review the configurations of several devices on the network to meet the following requirements:
• The PostgreSQL server must only allow connectivity in the 10.1.2.0/24
subnet.
• The SSH daemon on the database server must be configured to listen
to port 4022.
• The SSH daemon must only accept connections from a Single
workstation.
• All host-based firewalls must be disabled on all workstations.
• All devices must have the latest updates from within the past eight
days.
•All HDDs must be configured to secure data at rest.
• Cleartext services are not allowed.
• All devices must be hardened when possible.
Instructions:
Click on the various workstations and network devices to review the posture assessment results. Remediate any possible issues or indicate that no issue is found.
Click on Server A to review output data. Select commands in the appropriate tab to remediate connectivity problems to the pOSTGREsql DATABASE VIA ssh
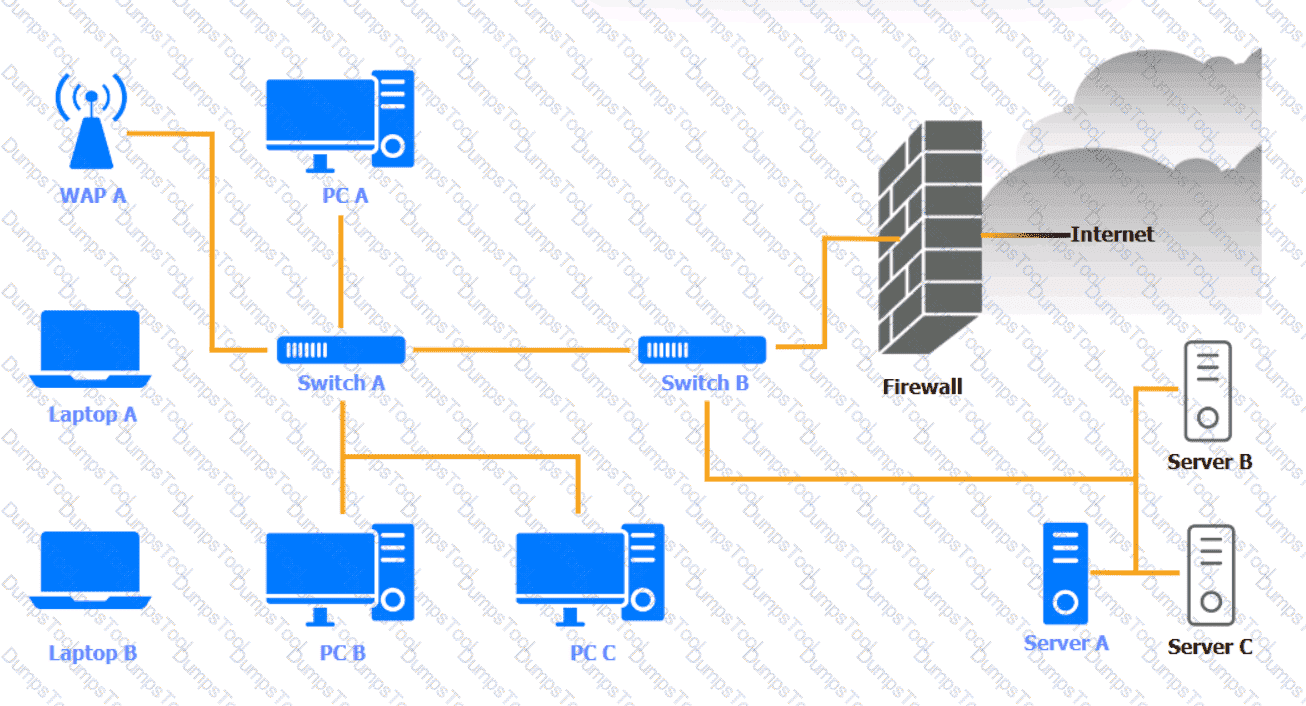
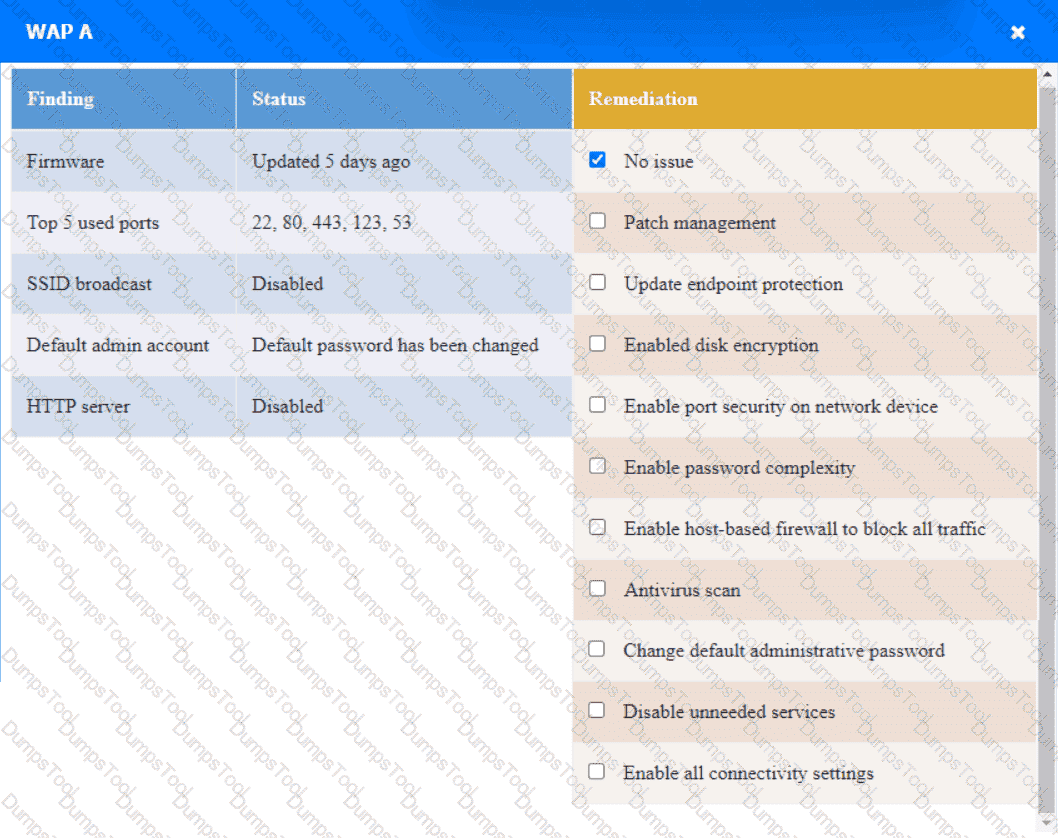
WAP A
PC A
Laptop A
Switch A
Switch B:
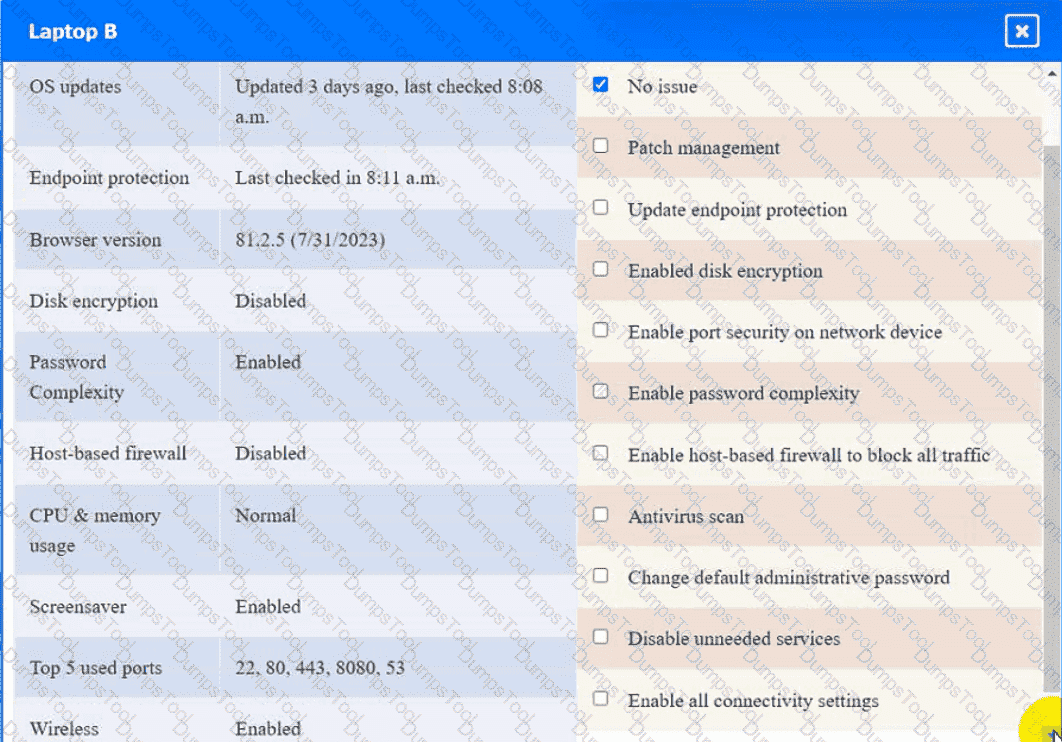
Laptop B
PC B

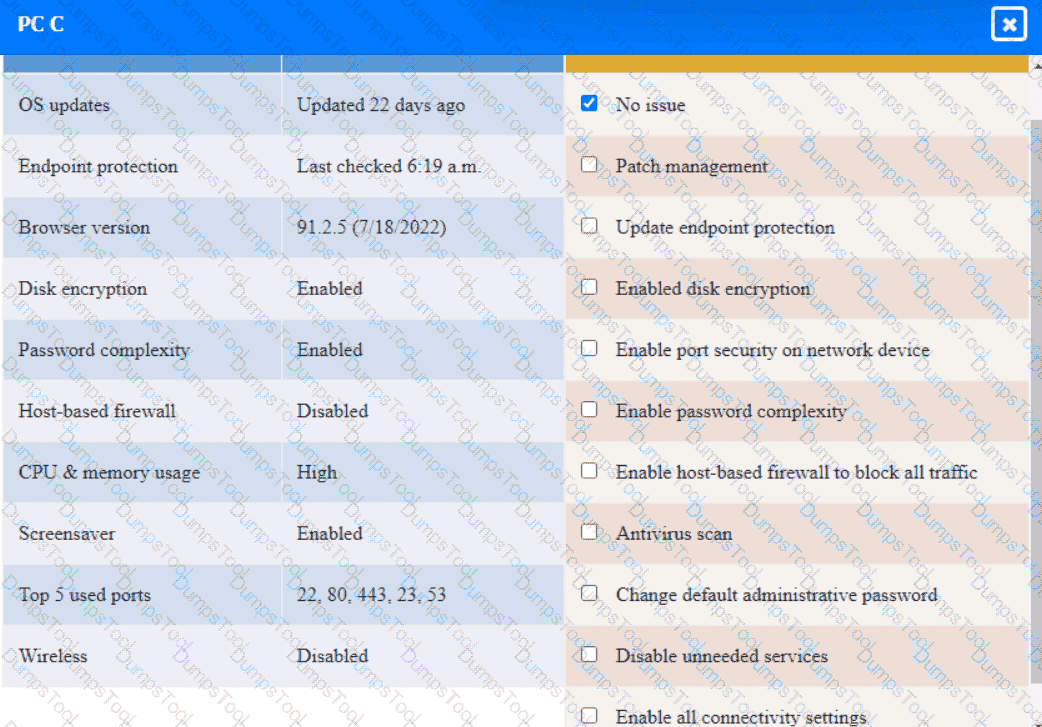
PC C
Server A

A security analyst received anotification from a cloud service provider regarding an attack detected on a web server The cloud service provider shared the following information about the attack:
• The attack came from inside the network.
• The attacking source IP was from the internal vulnerability scanners.
• The scanner is not configured to target the cloud servers.
Which of the following actions should the security analyst take first?
A security architect must make sure that the least number of services as possible is exposed in order to limit an adversary ' s ability to access the systems. Which of the following should the architect do first?
During an incident response activity, the response team collected some artifacts from a compromised server, but the following information is missing:
• Source of the malicious files
• Initial attack vector
• Lateral movement activities
The next step in the playbook is to reconstruct a timeline. Which of the following best supports this effort?
A large organization deployed a generative AI platform for its global user population to use. Based on feedback received during beta testing, engineers have identified issues with user interface latency and page-loading performance for international users. The infrastructure is currently maintained within two separate data centers, which are connected using high-availability networking and load balancers. Which of the following is the best way to address the performance issues?
A company detects suspicious activity associated with inbound connections. Security detection tools are unable to categorize this activity. Which of the following is the best solution to help the company overcome this challenge?
A company is having issues with its vulnerability management program New devices/lPs are added and dropped regularly, making the vulnerability report inconsistent Which of the following actions should the company lake to most likely improve the vulnerability management process '
Company A and Company D ate merging Company A ' s compliance reports indicate branchprotections are not in place A security analyst needs to ensure that potential threats to the software development life cycle are addressed. Which of the following should me analyst cons < der when completing this basic?
An organization is implementing advanced security controls associated with the execution of software applications on corporate endpoints. The organization must implement a deny-all, permit-by-exception approach to software authorization for all systems regardless of OS. Which of the following should be implemented to meet these requirements?
Engineers are unable to control pumps at Site A from Site B when the SCADA controller at Site A experiences an outage. A security analyst must provide a secure solution that ensures Site A pumps can be controlled by a SCADA controller at Site B if a similar outage occurs again. Which of the following represents the most cost-effective solution?
After a cybersecurity incident, a security analyst was able to collect a binary that the attacker used on the compromised server. Then the analyst ran the following command:
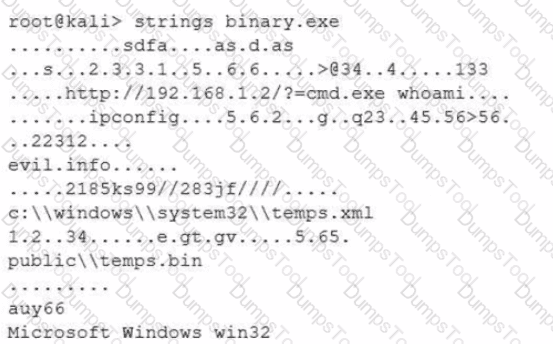
Which of the following options describes what the analyst is trying to do?
While investigating an email server that crashed, an analyst reviews the following log files:
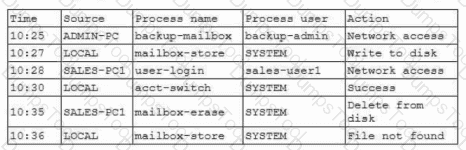
Which of the following is most likely the root cause?
A Chief Information Security Officer is concerned about the operational impact of ransomware. In the event of a ransomware attack, the business requires the integrity of the data to remain intact and an RPO of less than one hour. Which of the following storage strategies best satisfies the business requirements?
During a gap assessment, an organization notes that OYOD usage is asignificant risk. The organization implemented administrative policies prohibiting BYOD usage However, the organization has not implemented technical controls to prevent the unauthorized use of BYOD assets when accessing the organization ' s resources. Which of the following solutions should the organization implement to b»« reduce the risk of OYOD devices? (Select two).
A security architect for a global organization with a distributed workforce recently received funding lo deploy a CASB solution Which of the following most likely explains the choice to use a proxy-based CASB?
A security analyst isreviewing the following event timeline from an COR solution:
Which of the following most likely has occurred and needs to be fixed?
A systems administrator needs to identify new attacks that could be carried out against the environment. The administrator plans to proactively seek out and observe new attacks. Which of the following is the best way to accomplish this goal?
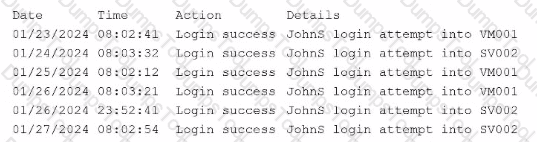
A security administrator needs to automate alerting. The server generates structured log files that need to be parsed to determine whether an alarm has been triggered Given the following code function:
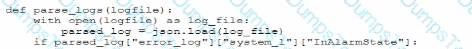
Which of the following is most likely the log input that the code will parse?
A)
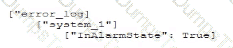
B)
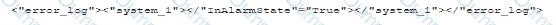
C)
D)
A security configure isbuilding a solution to disable weak CBC configuration for remote access connections lo Linux systems. Which of the following should the security engineer modify?
John Doe ' s email account was compromised. The attacker ' s access to John Doe ' s account was removed and MFA was implemented. The attacker convinced Joe Roe in the accounting department to pay a fraudulent invoice through email exchanges. A security analyst is reviewing the headers from the initial email that Joe Roe received:
Received: from 221.15.11.103 (221.15.11.103.mta.com [221.15.11.103])
by with esmtps (TLS 1.2)
Received-SPF: pass
Received: from 18.132.124.10 (18.132.124.10-internal.com [18.132.124.10])
by mx7sgwt-3S (Postfix) with ESMTPS id zRhQ22fmNnQCdys
DKIM-Signature: v=1; c=relaxed/relaxed; d=example.com;
s=default; t=1672873468;
h=To: Message-ID: Date: Content-Type: Subject: From: From: To: Cc: Subject;
To: jroe@example.com
Message-ID: _73/A4-32616-C36L8ZbYC4p
Date: Mon, 07 Apr 2025 +0000
Content-Type: multipart/alternative; boundary=
MIME-Version: 1.0
Reply-To: jdoe@exampl.com
Subject: FW: Invoice
From: jdoe@exampl.com
X-SpamProbability: 0.095349
Which of the following best explains how the attacker was able to get the invoice paid?
A company notices that cloud environment costs increased after using a new serverless solution based on API requests. Many invalid requests from unknown IPs were found, often within a short time. Which of the following solutions would most likely solve this issue, reduce cost, and improve security?
A security engineer receives an alert from the SIEM platform indicating a possible malicious action on the internal network. The engineer generates a report that outputs the logs associated with the incident:
Which of the following actions best enables the engineer to investigate further?
An organization determines existing business continuity practices are inadequate to support critical internal process dependencies during a contingency event. A compliance analyst wants the Chief Information Officer (CIO) to identify the level of residual risk that is acceptable to guide remediation activities. Which of the following does the CIO need to clarify?
A senior security engineer flags the following log file snippet as having likely facilitated an attacker’s lateral movement in a recent breach:
qry_source: 19.27.214.22 TCP/53
qry_dest: 199.105.22.13 TCP/53
qry_type: AXFR
| in comptia.org
------------ directoryserver1 A 10.80.8.10
------------directoryserver2 A 10.80.8.11
------------ directoryserver3 A 10.80.8.12
------------ internal-dns A 10.80.9.1
----------- www-int A 10.80.9.3
------------ fshare A 10.80.9.4
------------ sip A 10.80.9.5
------------ msn-crit-apcs A 10.81.22.33
Which of the following solutions, if implemented, would mitigate the risk of this issue reoccurring?
A user submits a help desk ticket stating then account does not authenticatesometimes. An analyst reviews the following logs for the user:
Which of the following best explains the reason the user ' s access is being denied?
PKI can be used to support security requirements in the change management process. Which of the following capabilities does PKI provide for messages?
A senior security engineer flags me following log file snippet as hawing likely facilitated an attacker ' s lateral movement in a recent breach:
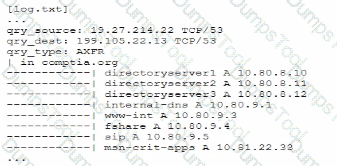
Which of the following solutions, if implemented, would mitigate the nsk of this issue reoccurnnp?
After several companies in the financial industry were affected by a similar incident, they shared information about threat intelligence and the malware used for exploitation. Which of the following should the companies do to best indicate whether the attacks are being conducted by the same actor?
A software vendor provides routine functionality and security updates to its global customer base. The vendor would like to ensure distributed updates are authorized, originate from only the company, and have not been modified by others. Which of the following solutions best supports these objectives?
In order to follow new regulations, the Chief Information Security Officer plans to use a defense-in-depth approach for a perimeter network. Which of the following protections would best achieve this goal?
Consultants for a company learn that customs agents at foreign border crossings are demanding device inspections. The company wants to:
• Minimize the risk to its data by storing its most sensitive data inside of a security container.
• Obfuscate containerized data on command.
Which of the following technologies is the best way to accomplish this goal?
A compliance officer isfacilitating abusiness impact analysis (BIA)and wantsbusiness unit leadersto collect meaningful data. Several business unit leaders want more information about the types of data the officer needs.
Which of the following data types would be the most beneficial for the compliance officer?(Select two)
A company has the following requirements for a cloud-based web application:
• Must authenticate customers
• Must prevent data exposure
• Must allow customer access to data throughout the cloud environment
• Must restrict access by specific regions
Which of the following solutions best addresses these security requirements?
A company updates itscloud-based services by saving infrastructure code in a remote repository. The code is automatically deployed into the development environment every time the code is saved lo the repository The developers express concern that the deployment often fails, citing minor code issues and occasional security control check failures in the development environment Which of the following should a security engineer recommend to reduce the deployment failures? (Select two).
Which of the following best describes a common use case for homomorphic encryption?
Which of the following are risks associated with vendor lock-in? (Select two).
During a forensic review of a cybersecurity incident, a security engineer collected a portion of the payload used by an attacker on a comprised web server Given the following portion of the code:
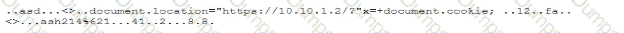
Which of the following best describes this incident?
An organization is implementing Zero Trust architecture A systems administrator must increase the effectiveness of the organization ' s context-aware access system. Which of the following is the best way to improve the effectiveness of the system?
A company recently acquired a manufacturing plant. The acquiring company plans to create a unified network that does not impact its security posture. The manufacturing plant has been in operation for more than 30 years and has not followed an equipment replacement life cycle. Which of the following is the best way to meet this objective?
An analyst wants to conduct a risk assessment on a new application that is being deployed. Given the following information:
• Total budget allocation for the new application is unavailable.
• Recovery time objectives have not been set.
• Downtime loss calculations cannot be provided.
Which of the following statements describes the reason a qualitative assessment is the best option?
A user tried to access a web page at http://10.1.1.1. Previously the web page did not require authentication, and now the browser is prompting for credentials. Which of the following actions would best prevent the issue from reoccurring and reduce the likelihood of credential exposure?
A company discovers intellectual property data on commonly known collaboration web applications that allow the use of slide templates. The systems administrator is reviewing the configurations of each tool to determine how to prevent this issue. The following security solutions are deployed:
CASB
SASE
WAF
EDR
Firewall
IDS
SIEM
DLP endpoints
Which of the following should the administrator do to address the issue?
A news organization wants to implement workflows that allow users to request that untruthful data be retraced and scrubbed from online publications to comply with the right to be forgotten Which of the following regulations is the organization most likely trying to address '
Within a SCADA a business needs access to the historian server in order together metric about the functionality of the environment. Which of the following actions should be taken to address this requirement?
A company wants to use loT devices to manage and monitor thermostats at all facilities The thermostats must receive vendor security updates and limit access to other devices within the organization Which of the following best addresses the company ' s requirements ' '
An organization wants to manage specialized endpoints and needs a solution that provides the ability to
* Centrally manage configurations
* Push policies.
• Remotely wipe devices
• Maintain asset inventory
Which of the following should the organization do to best meet these requirements?
An organization recently migrated data to a new file management system. The architect decides to use a discretionary authorization model on the new system. Which of the following best explains the architect ' s choice?
A company reduced its staff 60 days ago, and applications are now starting to fail. The security analyst is investigating to determine if there is malicious intent for the application failures. The security analyst reviews the following logs:
22:03:50 sshd[21502]: Success login for user01 from 192.168.2.5
22:10:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:11:40 sshd[21502]: Success login for user07 from 192.168.2.58
22:12:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:13:00 sshd[21502]: Failed login for user10 from 192.168.2.5
22:13:00 sshd[21502]: Success login for user03 from 192.168.2.27
22:13:00 sshd[21502]: Failed login for user10 from 192.168.2.5
Which of the following is the most likely reason for the application failures?
A threat intelligence company ' s business objective is to allow customers to integrate data directly to different TIPs through an API. The company would like to address as many of the following objectives as possible:
• Reduce compute spend as much as possible.
• Ensure availability for all users.
• Reduce the potential attack surface.
• Ensure the integrity of the data provided.
Which of the following should the company consider to best meet the objectives?
A game developer wants to reach new markets and is advised by legal counsel to include specific age-related sign-up requirements. Which of the following best describes the legal counsel ' s concerns?
A security engineer is given the following requirements:
• An endpoint must only execute Internally signed applications
• Administrator accounts cannot install unauthorized software.
• Attempts to run unauthorized software must be logged
Which of the following best meets these requirements?
During a recentsecurity event, access from thenon-production environment to the production environmentenabledunauthorized usersto:
Installunapproved software
Makeunplanned configuration changes
During theinvestigation, the following findings were identified:
Several new users were added in bulkby theIAM team
Additionalfirewalls and routerswere recently added
Vulnerability assessmentshave been disabled formore than 30 days
Theapplication allow listhas not been modified intwo weeks
Logs were unavailablefor various types of traffic
Endpoints have not been patchedinover ten days
Which of the following actions would most likely need to be taken toensure proper monitoring?(Select two)
A technician is reviewing the logs and notices a large number of files were transferred to remote sites over the course of three months. This activity then stopped. The files were transferred via TLS-protected HTTP sessions from systems that do not normally send traffic to those sites. The technician will define this threat as:
A security engineer is implementing a code signing requirement for all code developed by the organization. Currently, the PKI only generates website certificates. Which of the following steps should the engineer perform first?
A company that uses several cloud applications wants to properly identify:
All the devices potentially affected by a given vulnerability.
All the internal servers utilizing the same physical switch.
The number of endpoints using a particular operating system.Which of the following is the best way to meet the requirements?
An organization is looking for gaps in its detection capabilities based on the APTs that may target the industry Which of the following should the security analyst use to perform threatmodeling?
A company is adopting microservice architecture in order to quickly remediate vulnerabilities and deploy to production. All of the microservices run on the same Linux platform. Significant time was spent updating the base OS before deploying code. Which of the following should the company do to make the process efficient?
After an incident response exercise, a security administrator reviews the following table:
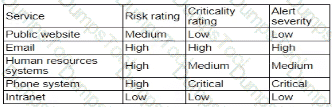
Which of the following should the administrator do to beat support rapid incident response in the future?
A subcontractor develops safety critical avionics software for a major aircraft manufacturer. After an incident, a third-party investigator recommends the company begin to employ formal methods in the development life cycle. Which of the following findings from the investigation most directly supports the investigator ' s recommendation?
A company is migrating from a Windows Server to Linux-based servers. A security engineer must deploy a configuration management solution that maintains security software across all the Linux servers. Which of the following configuration file snippets is the most appropriate to use?
A security engineer wants to enhance the security posture of end-user systems in a Zero Trust environment. Given the following requirements:
. Reduce the ability for potentially compromised endpoints to contact command-and-control infrastructure.
. Track the requests that the malware makes to the IPs.
. Avoid the download of additional payloads.
Which of the following should the engineer deploy to meet these requirements?
A global company with a remote workforce implemented a new VPN solution. After deploying the VPN solution to several hundred users, the help desk starts receiving reports of slow access to both internally and externally available applications. A security analyst reviews the following:
VPN client routing: 0.0.0.0/0 → eth1
Which of the following solutions should the analyst use to fix this issue?
The material finding from a recent compliance audit indicate a company has an issue with excessive permissions. The findings show that employees changing roles or departments results in privilege creep. Which of the following solutions are the best ways to mitigate this issue? (Select two).
Setting different access controls defined by business area
A user from the sales department opened a suspicious file attachment. The sales department then contacted the SOC to investigate a number of unresponsive systems, and the team successfully identified the file and the origin of the attack. Which of the following is the next step of the incident response plan?
Recent repents indicate that a software tool is being exploited Attackers were able to bypass user access controls and load a database. A security analyst needs to find the vulnerability and recommend a mitigation. The analyst generates the following output:
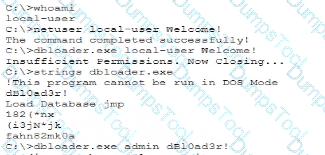
Which of the following would the analyst most likely recommend?
A company is preparing to move a new version of a web application to production. No issues were reported during security scanning or quality assurance in the CI/CD pipeline. Which of the following actions should thecompany take next?
A global organization wants to manage all endpoint and user telemetry. The organization also needs to differentiate this data based on which office it is correlated to. Which of the following strategies best aligns with this goal?
The ISAC for the retail industry recently released a report regarding social engineering tactics in which small groups create distractions for employees while other malicious individuals install advanced card skimmers on the payment systems. The Chief Information Security Officer (CISO) thinks that security awareness training, technical control implementations, and governance already in place is adequate to protect from this threat. The board would like to test these controls. Which of the following should the CISO recommend?
After a vendor identified a recent vulnerability, a severity score was assigned to the vulnerability. A notification was also publicly distributed. Which of the following would most likely include information regarding the vulnerability and the recommended remediation steps?
An engineer wants to automate several tasks by running commands daily on a UNIX server. The engineer has only built-in, default tools available. Which of the following should the engineer use to best assist with this effort? (Select Two).
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
Which of the following actions should the analyst take to best mitigate the threat?
Third partiesnotified a company ' s security team about vulnerabilities in the company ' s application. The security team determined these vulnerabilities were previously disclosed in third-party libraries. Which of the following solutions best addresses the reported vulnerabilities?
An incident response team is analyzing malware and observes the following:
• Does not execute in a sandbox
• No network loCs
• No publicly known hash match
• No process injection method detected
Which of thefollowing should the team do next to proceed with further analysis?
A user reports application access issues to the help desk. The help desk reviews the logs for the user:
Which of the following is most likely the reason for the issue?
A security engineer performed a code scan that resulted in many false positives. The security engineer must find asolution that improves the quality of scanning results before application deployment. Which of the following is the best solution?
Acompany must build and deploy security standards for all servers in its on-premises and cloud environments based on hardening guidelines. Which of the following solutions most likely meets the requirements?
A company that uses containers to run its applications is required to identify vulnerabilities on every container image in a private repository The security team needs to be able to quickly evaluate whether to respond to a given vulnerability Which of the following, will allow the security team to achieve the objective with the last effort?
During a vulnerability assessment, a scan reveals the following finding:
Windows Server 2016 Missing hotfix KB87728 - CVSS 3.1 Score: 8.1 [High] - Affected host 172.16.15.2
Later in the review process, the remediation team marks the finding as a false positive. Which of the following is the best way toavoid this issue on future scans?
A security engineer receives the following findings from a recent security audit:
• Data should be protected based on user permissions and roles.
• User action tracking should be implemented across the network.
• Digital identities should be validated across the data access workflow.
Which of the following is the first action the engineer should take to address the findings?
An organization has been using self-managed encryption keys rather than the free keys managed by the cloud provider. The Chief Information Security Officer (CISO) reviews the monthly bill and realizes the self-managed keys are more costly than anticipated. Which of the following should the CISO recommend to reduce costs while maintaining a strong security posture?
During DAST scanning, applications are consistently reporting code defects in open-source libraries that were used to build web applications. Most of the code defects are from using libraries with known vulnerabilities. The code defects are causing product deployment delays. Which of the following is the best way to uncover these issues earlier in the life cycle?
The device event logs sourced from MDM software are as follows:
Device | Date/Time | Location | Event | Description
ANDROID_102 | 01JAN21 0255 | 38.9072N, 77.0369W | PUSH | APPLICATION 1220 INSTALL QUEUED
ANDROID_102 | 01JAN21 0301 | 38.9072N, 77.0369W | INVENTORY | APPLICATION 1220 ADDED
ANDROID_1022 | 01JAN21 0701 | 39.0067N, 77.4291W | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 0701 | 25.2854N, 51.5310E | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 0900 | 39.0067N, 77.4291W | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 1030 | 39.0067N, 77.4291W | STATUS | LOCAL STORAGE REPORTING 85% FULL
Which of the following security concerns and response actions would best address the risks posed by the device in the logs?
To prevent data breaches, security leaders at a company decide to expand user education to:
• Create a healthy security culture.
• Comply with regulatory requirements.
• Improve incident reporting.
Which of the following would best meet their objective?
A security engineer must resolve a vulnerability in a deprecated version of Python for a custom-developed flight simul-ation application that is monitored and controlled remotely. The source code is proprietary and built with Python functions running on the Ubuntu operating system. Version control is not enabled for the application in development or production. However, the application must remain online in the production environment using built-in features. Which of the following solutions best reduces theattack surface of these issues and meets the outlined requirements?
An organization plans to deploy new software. The project manager compiles a list of roles that will be involved in different phases of the deployment life cycle. Which of the following should the project manager use to track these roles?
A hospital provides tablets to its medical staff to enable them to more quickly access and edit patients ' charts. The hospital wants to ensure that if a tablet is identified as lost or stolen and a remote command is issued, the risk of data loss can be mitigated within seconds. The tablets are configured as follows:
• Full disk encryption is enabled.
• " Always On " corporate VPN is enabled.
• eFuse-backed keystore is enabled.
• Wi-Fi 6 is configured with SAE.
• Location services is disabled.
• Application allow list is unconfigured.
Assuming the hospital policy cannot be changed, which of the following is the best way to meet the hospital ' s objective?