Company XYZ wants to implement an IPS device to detect and block well-known attacks against their network They want a design solution where all packets that are forwarded to the network are checked against a signature database before being allowed through This check must be done with the minimum effect on performance Which design is recommended?
A communication network failure is usually defined as a situation where the network is unable to deliver communication services Thus a failure can be viewed as a disruption of service rather than degradation due to congestion One of the survivability techniques for improving network resilience is traffic management Which network-level traffic management and restoration technique can be used to achieve this?
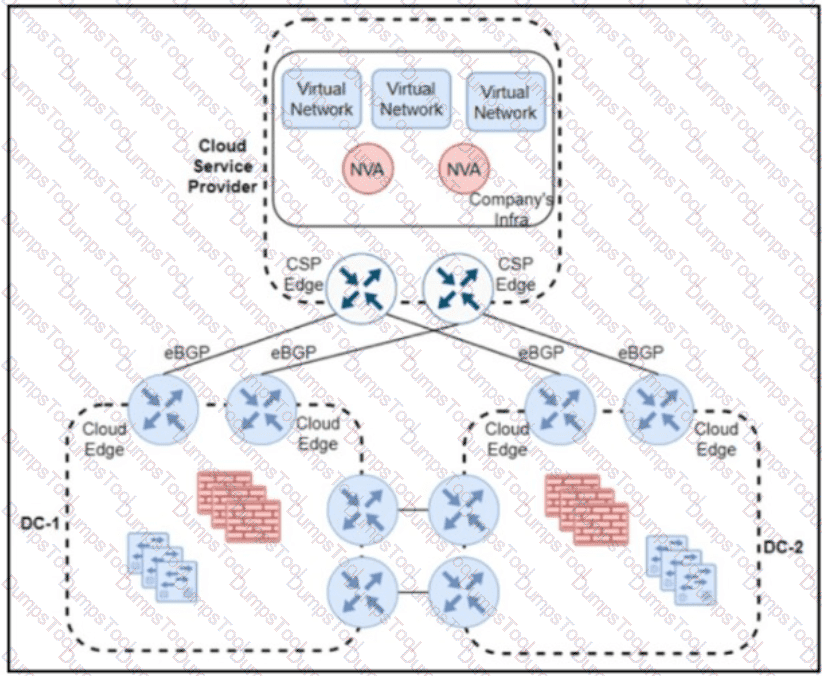
Refer to the exhibit A company has a hybrid cloud architecture with two on-premises data centers that connect to a public cloud service provider by using direct connect and eBGP routing. Encryption is unsupported by the cloud service provider, so the company plans to use an IPsec overlay network over its direct connects. Two virtual network appliances will be installed in the cloud infrastructure to establish tunnels and perform routing The company chose OSPF as the overlay routing protocol because the operations team is familiar with the protocol and because OSPF is the IGP on the on-premises network. The cloud network must be as isolated as possible from the on-premises network. What must be used for the OSPF overlay connectivity ?
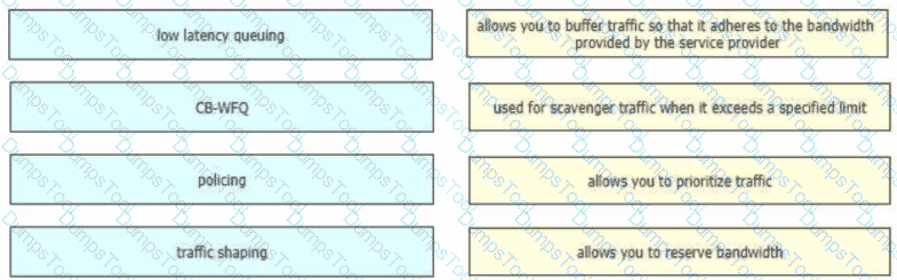
Drag and drop the QoS technologies from the left onto the correct capabilities on the right
When constraint-based routing is under consideration to be added to a network design, what are two inherent characteristics or impacts that must be considered? (Choose two)
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of ISAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
risk is a major determining factor in whether a company chooses to go with a public cloud, a private, or a hybrid of both. what are two factors that impact the decision on which cloud service placement model to use? (choose two)
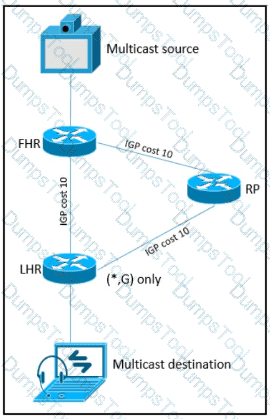
Refer to the exhibit. As part of a redesign project, you must predict multicast behavior . What happens to the multicast traffic received on the shared tree (*,G), if it is received on the LHR interface indicated*?
A large enterprise cloud design team is evaluating different cloud consumption models What is an example of typical PaaS limitations or concerns that should be considered during service design?
A legacy enterprise is using a Service Provider MPLS network to connect its head office and branches. Recently, they added a new branch to their network. Due to physical security concerns, they want to extend their existing IP CCTV network of the head office to the new branch, without any routing changes in the network. They are also under some time constraints. What is the best approach to extend the existing IP CCTV network to the new branch, without incurring any IP address changes?
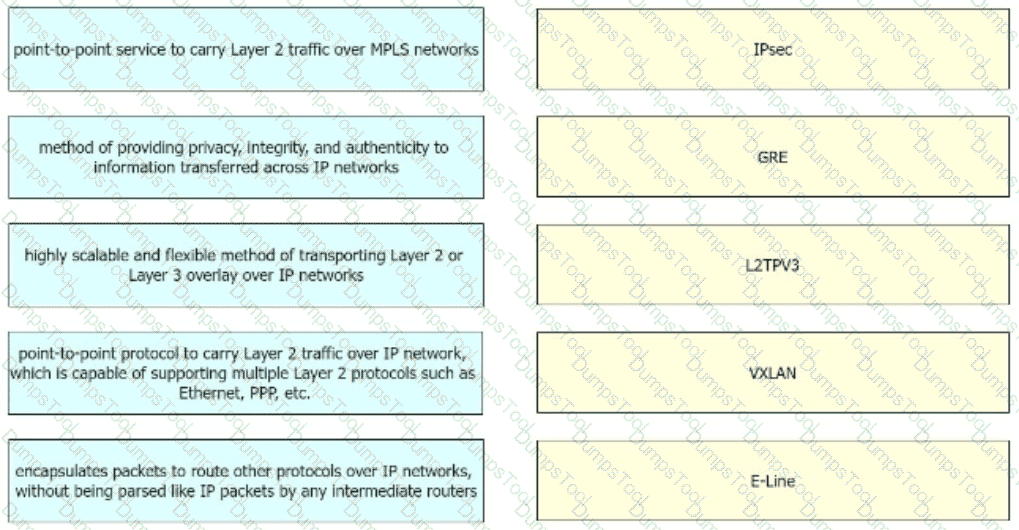
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.
What are two advantages of the Agile project management methodology? (Choose two)
which two actions must be taken when assessing an existing wireless network implementation for its readliness to support voice traffic? (choose two)
Which hybrid cloud environment enables businesses to more readily stage data-intensive and time-sensitive tasks closer to the source, which reduces latency, eases networking requirements, and improves data protection?
Which two statements describe the functionality of OSPF packet-pacing timers? (Choose two )
SDN is still maturing Throughout the evolution of SDN which two things will play a key role in enabling a successful deployment and avoiding performance visibility gaps in the infrastructure’ (Choose two.)
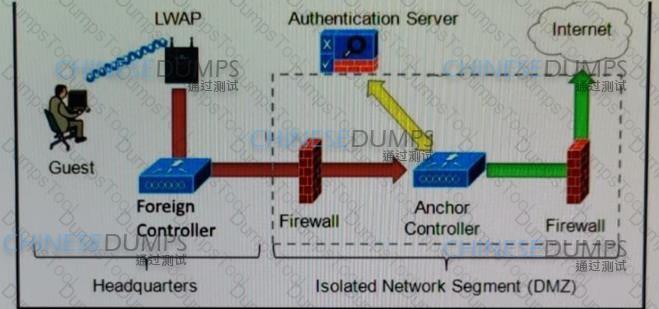
Refer to the diagram. Which solution must be used to send traffic from the foreign wireless LAN controller to the anchor wireless LAN controller?
Which interface between the controller and the networking device enables the two to communicate and allows the controller to program the data plane forwarding tables of the networking device?
As a service provider is implementing Strong Access Control Measures, which two of the following PCI Data Security Standard requirements must be met? (Choose two . )
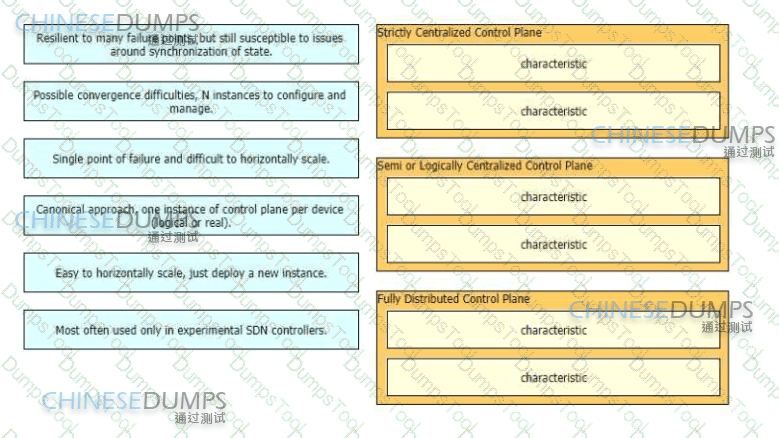
Network operators have many options available from fully centralized to fully distributed control planes and each approach has its own set of characteristics Drag and drop the characteristics from the left onto the corresponding approach on the right
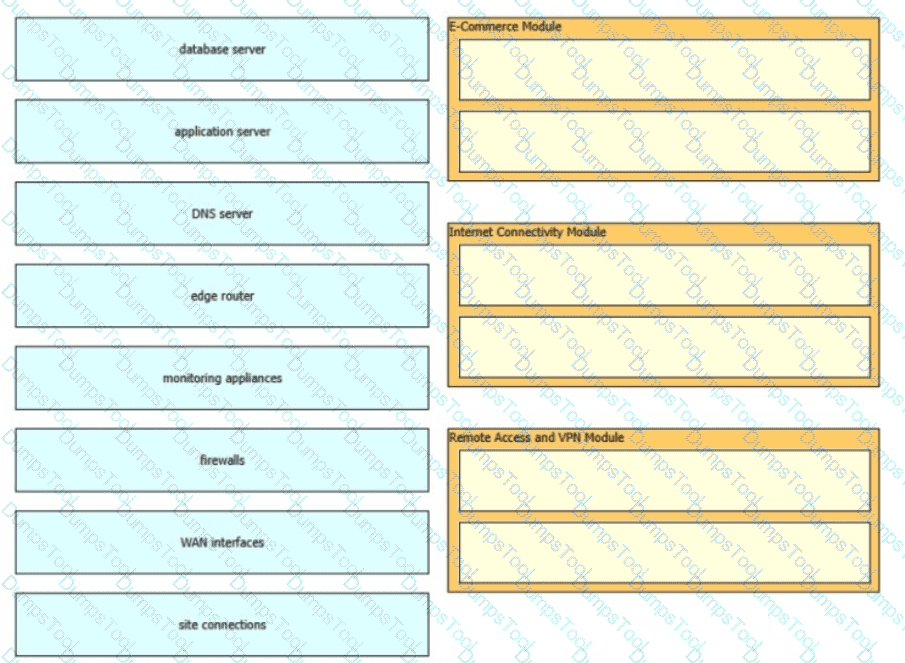
The Enterprise Edge infrastructure modules aggregate the connectivity from the various elements outside the campus—using various services and WAN technologies as needed typicaly provisioned from service providers and route the traffic into the Campus Core layer The Enterprise Edge modules perform security functions when enterprise resources connect across public networks and the internet Drag and drop the network device types from the left onto the corresponding modules on the right Not all options are used
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
Network designers often segment networks by creating modules for various reasons Sometimes however a network can be unintentionally segmented For instance, if the only way to connect a remote site to a headquarters or regional site is to connect them both to the public Internet the corporate network is now unintentionally segmented Which of the following option can be used to desegment the network in this situation?
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
A European government passport agency considers upgrading its IT systems to increase performance and workload flexibility in response to constantly changing requirements. The budget manager wants to reduce capital expenses and IT staff and must adopt the lowest-cost technology. Which technology choice is suitable?
In implementing the CIA triad, an organization must follow a general set of best practices. Which best practice is applicable for availability?
Scalability is a desirable attribute of a network, system, or process Poor scalability can result in poor system performance, necessitating the reengineering or duplication of systems Load scalability is the ability of a system to perform gracefully as traffic increases Which two problems can occur due to poor load scalability design? (Choose two )
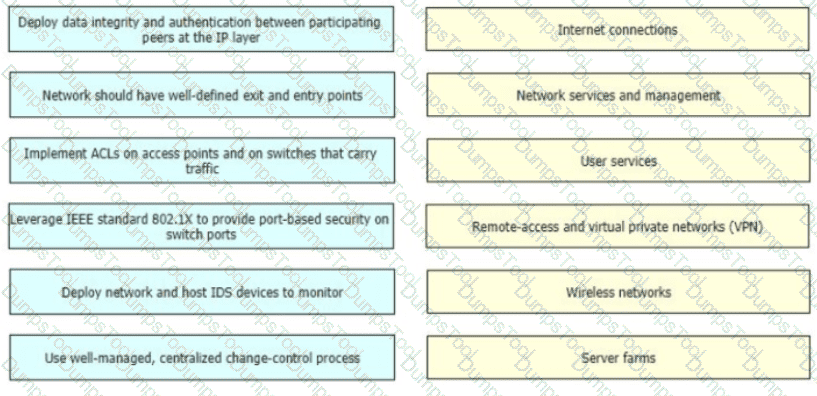
Security experts promote the security defense-m-depth principle which states that network security should be multilayered and modular and multiple methods should be designed and applied to different parts of the network Drag and drop the characteristics on the left to the matching enterprise network components on the right.
Virtualization pose a special challenges for NAC because virtual servers can move around a data center, and the VLAN can change as the servers move. What is an option that can be used to improve security in this condition?
The controller has a global view of the network, and it can easily ensure that the network is in a consistent and optimal configuration Which two statements describe a centralized SDN control path? (Choose two.)
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
In traditional network design, the network and data center are confined within a single building In this configuration, a router connects the internal and external networks Basic configuration of an access control list within the router controls the traffic that can pass through Which security technique defines the boundary between an internal/trusted network and an external/untrusted network?
In the wake of a security compromise incident where the internal networks were breached by an outside attacker at the perimeter of the infrastructure, an enterprise is now evaluating potential measures that can help protect against the same type of incident in the future. What are two design options that can be employed? (Choose two)
A business wants to centralize servies via VDI technology and to replace remote WAN desktop PCs with thin client-type machines to reduce operating costs Which consideration supports the new business requirement?
A customer has a functional requirement that states HR systems within a data center must be segmented from other systems that reside in the same data center and same VLAN The systems run legacy applications by using hard-coded IP addresses with all HR systems dedicated to 129 to 254 of the 10 20.20 0/24 prefix Which segmentation method is optimal for the customer?
The PaaS model provides customers with a virtualized application development platform without the need for them to furnish hardware or system administration using in-house resources All necessary infrastructure components and application development services are provided and managed by the cloud service provider. Which limitation should be considered when selecting PaaS model?
Over the years, many solutions diveloped to limit control plane state which reduces the scope or the speed of control plane information propagation Which solution removes more specific information about a particular destination as topological distance is covered in the network?
Two companies need to implement an extranet overlay network solution by using a VPN tunnel over the internet to use each other ' s HTTP REST APIs. The solution must only provide data integrity because data confidentiality will be covered at the application layer The existing firewall devices will be used as VPN endpoints for the tunnel but they have limited available resources Which type of VPN tunnel must be deployed for the extranet service?
The modular design model approach allows companies to have a network infrastructure that is better suited for scalable applications What is the benefit for companies that use this model?
A network architect is working on the baseline policies dealing with the use of Infrastructure-as-Code within an IT department, and has been requested to present the plan at the monthly management board meeting. What are two examples of operational aspects of Infrastructure-as-Code that can be highlighted during the presentation? (Choose two.)
Company XYZ is running SNMPvl in their network and understands that it has some flaws They want to change the security design to implement SNMPv3 in the network Which network threat is SNMPv3 effective against?
When planning their cloud migration journey what is crucial for virtually all organizations to perform?
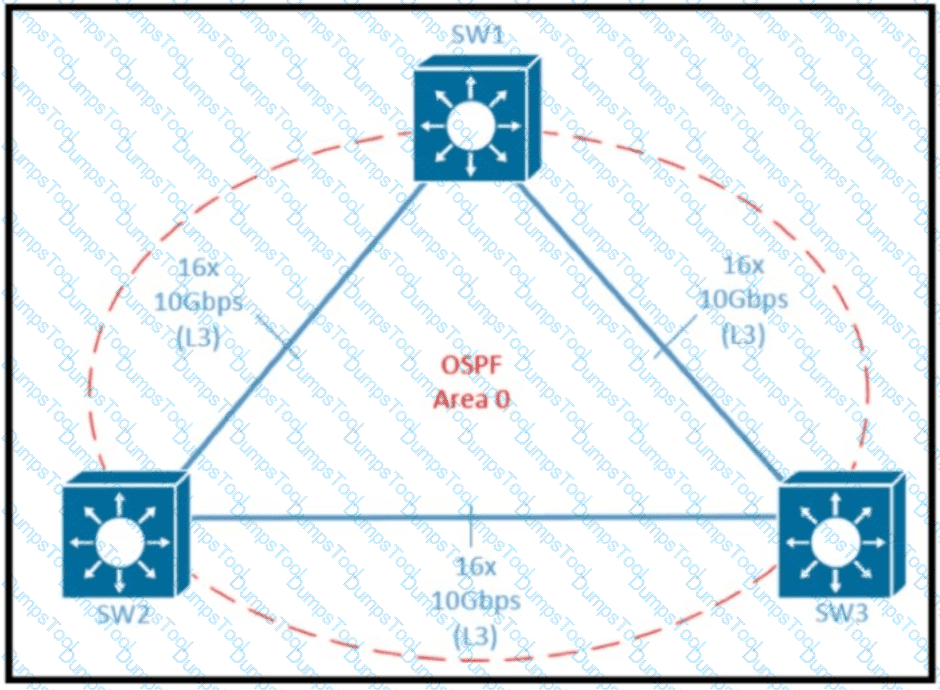
Refer to the exhibit Which two design options reduce the size of OSPF database in the shown topology? (Choose two.)
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
Which design method is achieved by layering the network control plane above a redundant physical infrastructure?
Company XYZ has 30 sites using MPLS L3 VPN and the company is now concerned about data integrity. The company wants to redesign the security aspect of their network based on these requirements:
Securely transfer the corporate data over the private WAN
Use a centralized configuration model.
Minimize overhead on the tunneled traffic.
Which technology can be used in the new design to meet the company’s requirements?
When a traditional network is transformed to a hierarchical network, the state information in the control plane is reduced so that changes in one area of the network do not result in changes in the routing table on devices half-way around the globe What is a potential trade off in these cases?
A customer migrates from a traditional Layer 2 data center network Into a new SDN- based, spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. Which activity should be completed each time a legacy network is migrated?
Which undesired effect of increasing the jitter compensation buffer is true?
With virtualization being applied in many parts of the network, every physical link is likely to carry one or more virtual links, but what is a drawback in cases like this?
A network uses an SDN architecture with switches and a centralized controller What should be on the switches but not on the controller?
Implementing a network automation architecture usually follows a phased approach that increases automation as the new technology and processes in the preceding phases are integrated and adopted. What provides a model that greatly simplifies the interaction with network devices?
As part of workspace digitization, a large enterprise has migrated all their users to Desktop as a Sen/ice (DaaS), by hosting the backend system in their on-premises data center. Some of the branches have started to experience disconnections to the DaaS at periodic intervals, however, local users in the data center and head office do not experience this behavior. Which technology can be used to mitigate this issue?
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?