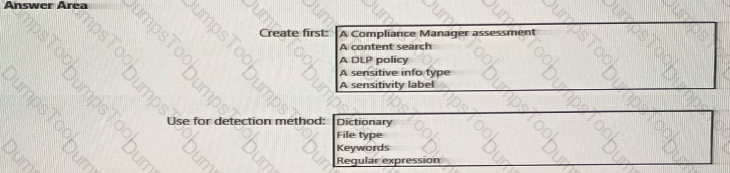
You need to meet the technical requirements for the confidential documents.
What should you created first, and what should you use for the detection method? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
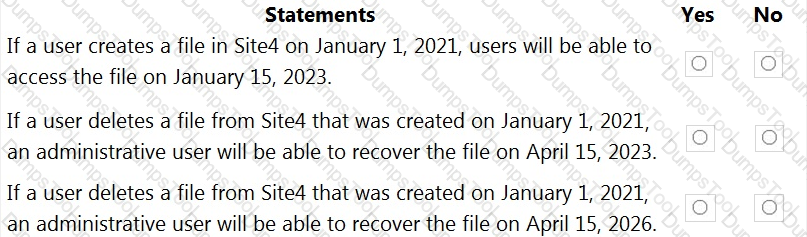
You are reviewing policies for the SharePoint Online environment.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the user viewed them.
When you search the audit log in the Microsoft Purview compliance portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
YOU run the Set-Mailbox -Identity "User1" -AuditEnabled $true command.
Does that meet the goal?
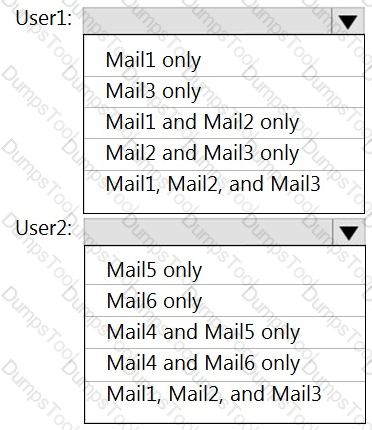
You have a Microsoft 365 tenant named contoso.com that contains two users named User1 and User2. The tenant uses Microsoft Office 365 Message Encryption (OME).
User1 plans to send emails that contain attachments as shown in the following table.
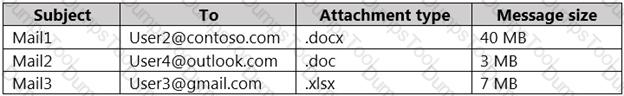
User2 plans to send emails that contain attachments as shown in the following table.
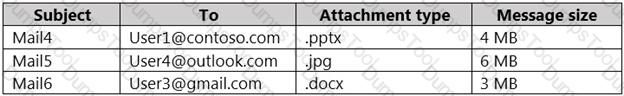
For which emails will the attachments be protected? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that contains the data loss prevention (DLP) policies shown in the following table.
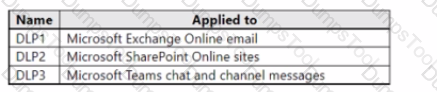
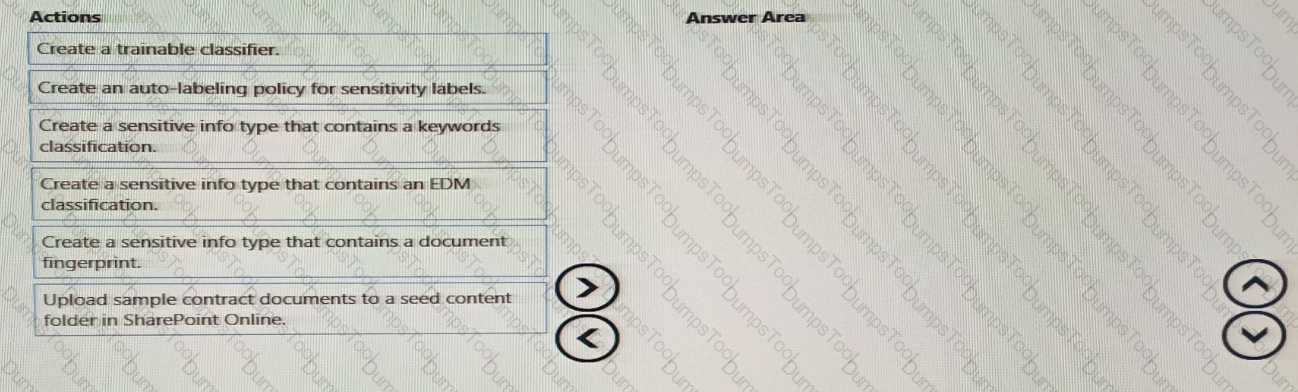
You have a custom employee information form named Template l.docx.
You plan to create a sensitive info type named Sensitive1 that will use the document fingerprint from Template!.docx.
What should you use to create Sensitive1. and in which DIP policies can you use Sensitive1? To answer, select the appropriate options in the answer area.
You need to protect documents that contain credit card numbers from being opened by users outside your company. The solution must ensure that users at your company can open the documents.
What should you use?
Task 4
You need to block users from sending emails containing information that is subject to Payment Card Industry Data Security Standard (PCI OSS). The solution must affect only emails.
Task 9
You are investigating a data breach.
You need to retain all Microsoft Exchange items in the mailbox of Alex Wilber that contain the word Falcon and were created in the year 2021.
Task 7
You need to create a retention policy that meets the following requirements:
• Applies to Microsoft Teams chat and Teams channel messages of users that have a department attribute of Sales.
• Retains item for five years from the date they are created, and then deletes them.
You are evaluating the technical requirements for the DLP reports.
Which user can currently view the DLP reports?
You need to meet the technical requirements for the creation of the sensitivity labels.
To which user or users must you grant the Sensitivity label administrator role?
Each product group at your company must show a distinct product logo in encrypted emails instead of the
standard Microsoft Office 365 logo.
What should you do to create the branding templates?
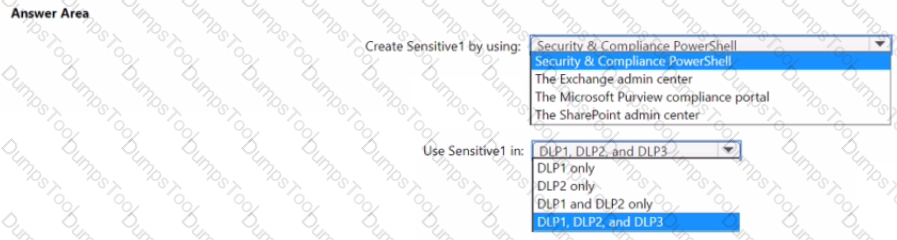
You plan to implement Microsoft 365 Endpoint data loss prevention (Endpoint DLP).
You need to identify which end user activities can be audited on the endpoints, and which activities can be restricted on the endpoints.
What should you identify for each activity? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You receive an email that contains a list of words that will be used few a sensitive information type.
You need to create a file that can be used as the source of a keyword dictionary.
In which format should you save the list?
You have a data loss prevention (DLP) policy that has the advanced DLP rules shown in the following table.
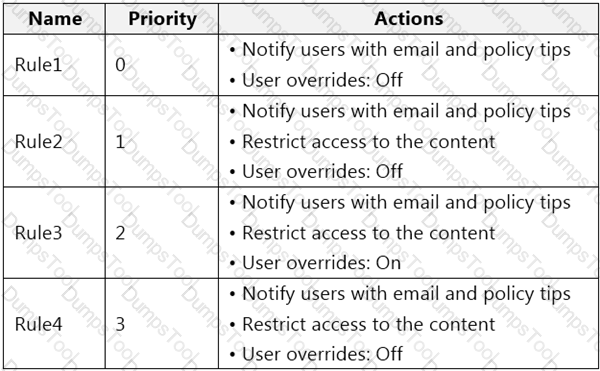
You need to identify which rules will apply when content matches multiple advanced DLP rules.
Which rules should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
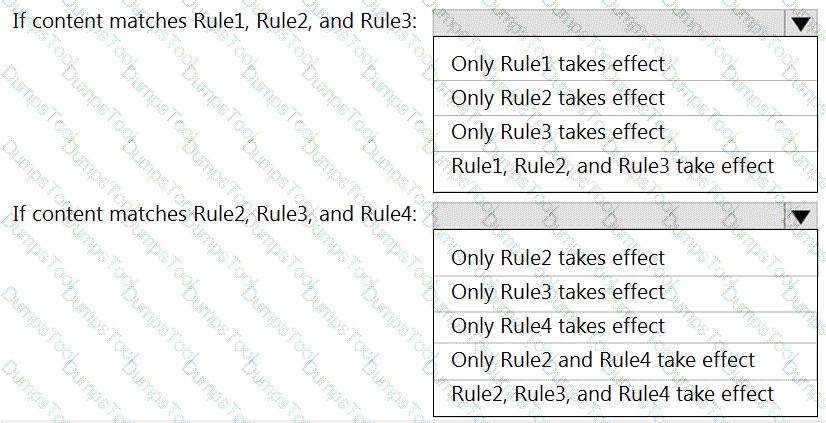
You need to implement a solution to encrypt email. The solution must meet the compliance requirements.
What should you create in the Exchange admin center and the Microsoft 36.S compliance center? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
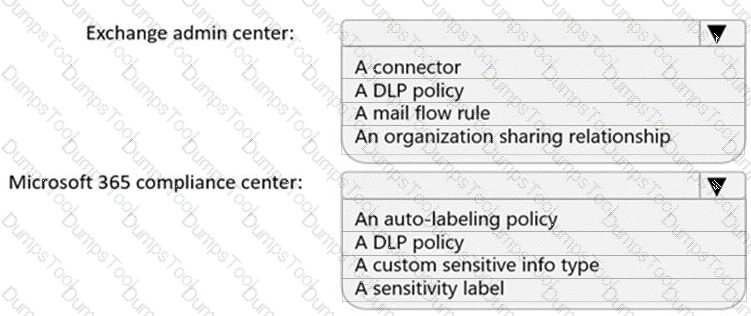
You need to recommend a solution that meets the sales requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to recommend a solution that meets the compliance requirements for protecting the documents in the Data shared folder. What should you recommend?
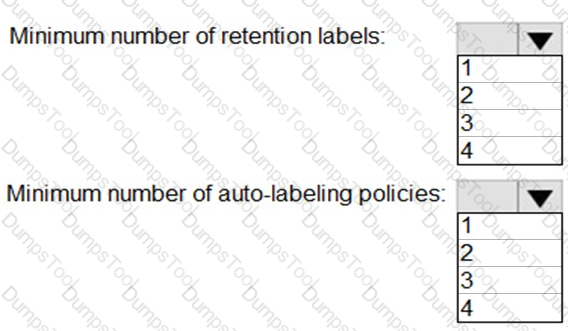
You need to recommend an information governance solution that meets the HR requirements for handling employment applications and resumes.
What is the minimum number of information governance solution components that you should create? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement a solution that meets the compliance requirements for the Windows 10 computers.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each coned selection is worth one point.
You need to recommend a solution that meets the compliance requirements for Dropbox.
What should you recommend?
You need to recommend a solution that meets the executive requirements. What should you recommend?
You need to recommend a solution that meets the compliance requirements for viewing DLP tooltip
justifications.
What should you recommend?
You need to recommend a solution that meets the compliance requirements for Dropbox.
What should you recommend?
You need to recommend a solution that meets the Data Loss Prevention requirements for the HR department.
Which three actions should you perform? Each correct answer presents part of the solution. (Choose three.)
NOTE: Each correct selection is worth one point.
You need to recommend a solution to configuration the Microsoft 365 Records management settings by using the CSV file must meet the compliance requirements.
What should you recommend?
You need to recommend a solution that meets the compliance requirements for protecting the documents in the Data shared folder.
What should you configure in the Microsoft Purview compliance portal?
Task 1
You need to provide users with the ability to manually classify files that contain product information that are stored in SharePoint Online sites. The solution must meet the following requirements:
• The users must be able to apply a classification of Product1 to the files.
• Any authenticated user must be able to open files classified as Product1.
• files classified as Product1 must be encrypted.
Task 6
You plan to implement Endpoint data loss prevention (Endpoint DLP) policies for computers that run Windows.
Users have an application named App1 that stores data locally in a folder named C:\app1\data.
You need to prevent the folder from being monitored by Endpoint DLP.
Task 5
You need to ensure that a group named U.S. Sales can store files containing information subject to General Data Protection Regulation (GDPR) in their OneDrive accounts. All other current GDPR restrictions must remain in effect.
Task 3
You plan to automatically apply a watermark to the document1 of a project named Falcon.
You need to create a label that will add a watermark of "Project falcon' in red. size-12 font diagonally across the documents.
Task 10
You plan to create a data loss prevention (DLP) policy that will apply to content containing the following keywords:
• Tailspin
• litware
• Falcon
You need to create a keyword list that can be used in the DLP policy. You do NOT need to create the DLP policy at this time.
Task 8
You need to retain Microsoft SharePoint files that contain the word Falcon for two years from the date they were created, and then delete them.
Task 2
You discover that all users can apply the Confidential - Finance label.
You need to ensure that the Confidential - Finance label is available only to the members of the Finance Team group.